
-
- Home
>
-
- Blog
>
-
- SIEM Trends
Understand Your Detection Gaps and How to Close Them
- Jun 10, 2025
- Heidi Willbanks
- 3 minutes to read
Table of Contents
Without a direct line of sight into detection logic, use cases, and data sources, even mature security teams can miss critical gaps. Most security information and event management (SIEM) platforms track ingestion and alert volumes, but they rarely show whether your detections align with actual threats or frameworks like MITRE ATT&CK®.
That’s where the Outcomes Navigator app within the New-Scale Security Operations Platform makes a difference.
It provides full visibility into your current detection coverage, mapped to both Exabeam-supported use cases and the ATT&CK framework. More than just a view, it delivers specific, actionable recommendations to help you strengthen detection, optimize data collection, and improve outcomes over time.
Know What Your Data is Really Collecting
Security teams often collect a wide range of logs, but that doesn’t always translate to effective detection. Without clear traceability, it’s hard to tell:
- Which use cases are fully supported
- Where ATT&CK techniques are partially or not at all covered
- Which detection rules are enabled but not actively firing
- Whether logs are parsed in a way that supports detection logic
Outcomes Navigator connects these dots. It maps detections back to their underlying log sources and parsing quality, so you can see what’s working, what’s underperforming, and what needs attention. For example, you may be collecting endpoint logs, but if key fields are missing or no correlation rules are firing, you’re not effectively detecting lateral movement.
Align to Both Strategic Use Cases and MITRE ATT&CK
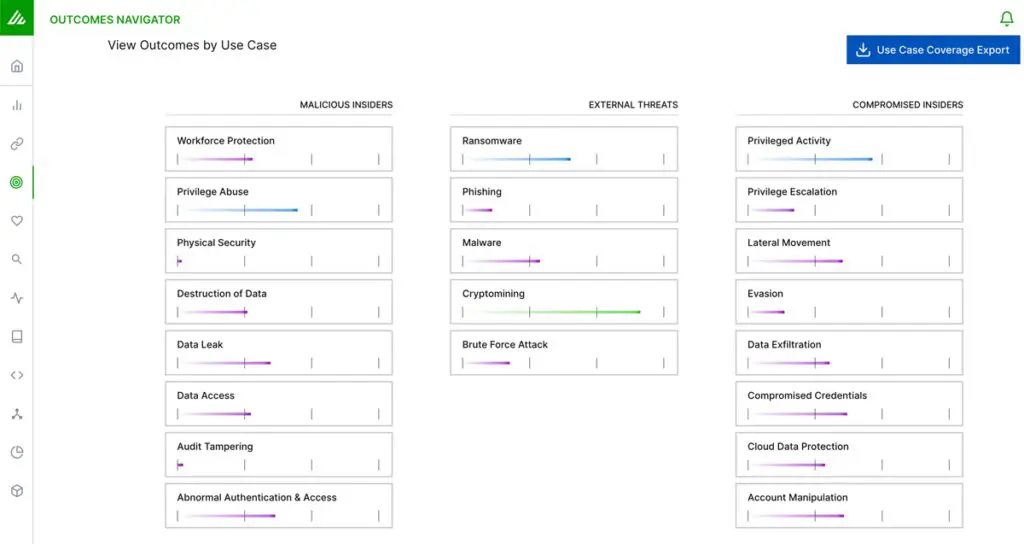
Outcomes Navigator supports multiple perspectives on detection:
- Use cases provide a broader, strategic lens for security operations center (SOC) managers and compliance teams—things like detecting compromised insiders or privilege escalation.
- ATT&CK coverage offers deeper alignment for technical teams tracking detection against specific adversary behaviors and regulatory expectations.
By offering both views in one app, Outcomes Navigator supports detection maturity across a range of SOC structures, from emerging teams to advanced programs.
See What’s Working and What’s Not
Outcomes Navigator gives you the ability to:
- View current detection coverage across 21 supported use cases and 236 ATT&CK techniques.
- Identify rules that are enabled but not triggered, highlighting potential configuration issues or data gaps.
- Pinpoint missing fields in log sources that prevent detections from firing.
- Prioritize improvements with specific, actionable recommendations.
For each use case, Outcomes Navigator shows:
- Other use cases in the same detection category
- Your current posture by category (None, Good, Better, Best)
- Which log sources support the use case and which ones you’re actively collecting and parsing
- Which rules are receiving the right data to trigger (satisfied) versus rules that are enabled but inactive
- How well each source is parsed in support of specific detections
It also recommends ways to improve coverage, including:
- Which additional data sources could strengthen visibility
- Which sources would benefit from improved field parsing
- Whether critical data might be excluded due to filters or configuration
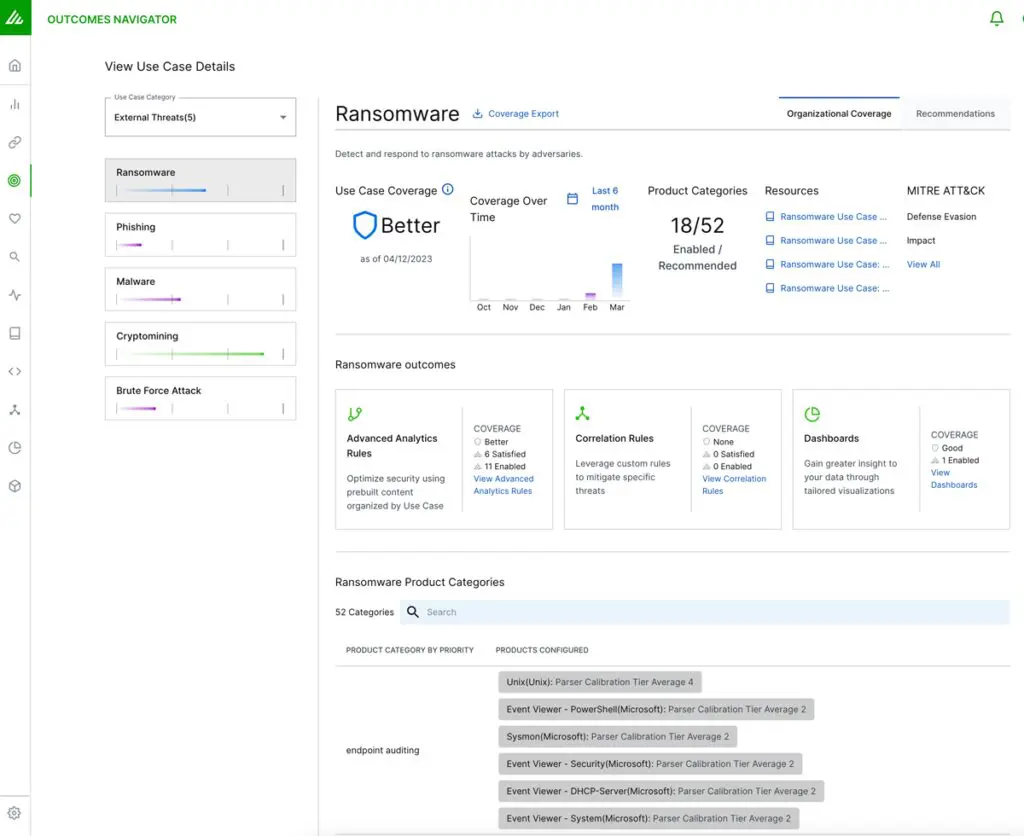
This level of detail helps analysts, engineers, and architects move beyond dashboards to fine-tune content and collection with precision.
Improve Over Time With Agentic AI-Powered Guidance
Security coverage isn’t static. Detection priorities evolve, log volumes grow, and frameworks like ATT&CK are frequently updated. To support continuous improvement, Exabeam Nova, our built-in, security-specific AI agent, works within Outcomes Navigator to provide:
- Real-time posture summaries across ATT&CK and key use cases
- Trend tracking to show how your coverage changes over time
- Step-by-step guidance on how to improve use case and technique-level coverage
- Leadership-ready reporting that communicates progress in clear terms
You can compare your current scored coverage—including prebuilt and custom dashboards and rules—to the full detection content available in the New-Scale Platform. This helps teams identify what’s missing, understand how to close any gaps, and track progress toward specific security goals.
With Exabeam Nova, teams can identify gaps and understand what to do about them. To move from simply spotting gaps to closing them, you need a repeatable way to measure coverage, prioritize improvements, and track progress over time.
Your Roadmap to Closing Detection Gaps
Read the White Paper: Operationalizing Continuous Improvement in the Age of Advanced Threats
Discover how to turn coverage assessments into an ongoing improvement process, benchmark against ATT&CK, and strengthen SOC performance. Read the white paper
Additional Resources
- Feature Brief: Outcomes Navigator – Understand your current use case coverage and get prioritized guidance to strengthen detection.
- Video: Outcomes Navigator With Exabeam Nova – See how Outcomes Navigator, enhanced by the Exabeam Nova Advisor Agent, delivers deeper insights and recommendations to improve threat detection.

Heidi Willbanks
Senior Product Marketing Manager, Content | Exabeam | Heidi Willbanks is the Senior Product Marketing Manager, Content at Exabeam. She manages content strategy and production for product marketing and supports strategic partners, sales and channel enablement, and competitive content, leveraging her product marketing certification, content expertise, and industry knowledge. She has 19 years of experience in content marketing, with nearly a decade in the cybersecurity field. Heidi received a BA in Journalism with a minor in Graphic Design from Cal Poly Humboldt and was awarded Outstanding Graduating Senior in Public Relations Emphasis. She enjoys reading, writing, gardening, hiking, yoga, music, and art.
More posts by Heidi WillbanksLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
-
 Blog
Blog
Five Reasons Security Operations Teams Augment Microsoft Sentinel With New-Scale Analytics
- Show More



