Our professional services team highlights that customers who are aware of their data locations, adept at data movement, and have clear internal communication and change control processes tend to be the fastest adopters of a new TDIR platform.
It’s time for a new approach
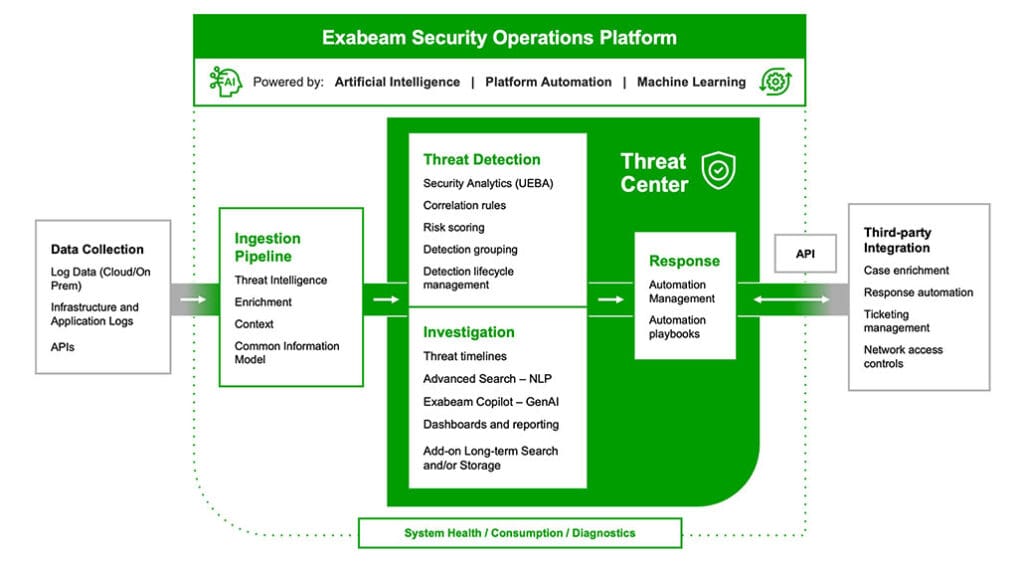
The Exabeam Security Operations Platform architecture allows you to start with the full offering or try base capabilities and add more over time. The platform features shared capabilities across all products. These are delivered as apps that operate with any license entitlement: Collectors (on-prem, cloud, context), Search, Log Stream, Reporting and Dashboards, Correlation Rule Builder, Outcomes Navigator, Service and Health Monitoring, and our Threat Intelligence Service. These shared capabilities are available to every Exabeam user. Additional capabilities such as UEBA, automation, timelines, and advanced triage can be easily provisioned and entitled for any existing cloud-native platform or new user.

MODULAR PLATFORM DESIGN
All capabilities delivered as license entitlements or platform apps
The platform architecture provides shared capabilities, apps that operate with any license entitlement. You can start small and grow your capabilities as you need more sophistication.
CLOUD-SCALE SECURITY LOG MANAGEMENT
Log management built for security use cases
Modern log management forms the foundation and is designed to support security use cases. Ingest, parse, store, and search log data efficiently at scale, with rapid ingestion and high-speed query performance.
- Purpose-built for security
- Scale to meet any data requirements
- Intelligent data retention to manage costs

EXPANSIVE DATA COLLECTION
Supports best-of-breed, multi-vendor strategy
An open platform supporting 200+ on-premises products, 34 cloud-delivered security products, and 21 cloud infrastructure products. It also integrates with 11 SaaS productivity apps and the top three cloud infrastructure vendors.
- Avoid vendor lock-in
- Rapid onboarding of new data sources
- Simplified user experience
RAPID DATA INGESTION AND PARSING
Centralized console for parser management
The platform delivers rapid log ingestion processing, sustaining over 2M EPS. Use the Log Stream app’s central console to visualize, create, deploy, and monitor parsers within a unified ingestion pipeline for all Exabeam products and features.
- Access 9,500+ pre-built log parsers
- Enrich data with context from threat intelligence feeds, location, and user-host-IP mapping
- Get self-service, real-time performance monitoring with Live Tail capabilities
SECURITY-SPECIFIC COMMON INFORMATION MODEL
Transform raw logs into meaningful events
At the core of the platform’s data ingestion is a security-specific Common Information Model (CIM), providing normalized, actionable logs for faster and easier parsing, storage, management, and search.
- Normalizes logs from any vendor for security outcomes
- Prepares data for immediate threat detection
- Organizes data by 10 fields, 76 security subjects, and 395 activities
ALIGNED WITH OUTCOMES
Easily support your most strategic use cases
Automatically visualize your use case and MITRE ATT&CK® coverage against data ingested into the platform. Get recommendations for improving coverage and report easily to stakeholders.
- Measure the value of ingested data
- Spot gaps and improve parsing configurations or data source coverage

EASILY BUILD NEW CORRELATIONS
Build custom correlations for unique requirements
The platform provides a single interface to write, test, publish, and monitor custom correlation rules for your most critical business entities and assets. Define higher-criticality rules for advanced threats sourced from our Threat Intelligence Service.
- Customize correlation rules to meet specific use case requirements
- Identify a broad range of abnormal behavior and events
- Use context from our Threat Intelligence Service or third-party threat intelligence
INDUSTRY-LEADING UEBA
Understand normal user and device behavior
The platform offers powerful UEBA capabilities with more than 1,800 rules and 750+ behavioral models. Automatically learn normal behavior of users and devices and establish baselines, enabling the detection, prioritization, and response to anomalies based on risk.
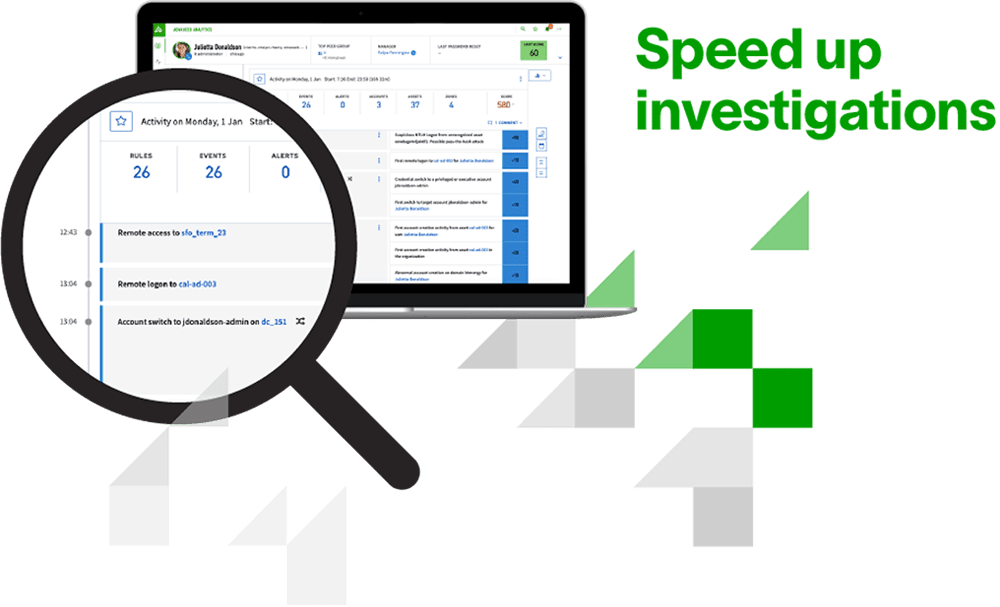
AUTOMATED TIMELINES
Incident history visualization
An automated timeline organizes all anomaly and correlated security events chronologically, conveying a comprehensive incident history. Each event is risk-scored, reducing the need for analysts to write hundreds of queries.
AUTOMATE THE TDIR WORKFLOW
Streamline response actions and complex tasks
Automate the TDIR workflow to gain a comprehensive view of a threat, escalate events to cases quickly, reduce manual routines, and simplify complex tasks.
- Automate alert triage
- View a threat in a timeline
- Sort events into incidents and cases
- Create tasks with assignment options
- Choose from semi- to fully automated actions
PRE-BUILT REPORTING AND DASHBOARDS
Build a dashboard in a minute
Chart types include: bar chart, column chart, line graph, area chart, pie chart, donut chart, bubble chart, funnel, single value, sankey diagram, word cloud, heat map, table, and coverage map
Easy to Get Started
The modular, AI-driven Exabeam Security Operations Platform provides powerful, fully integrated log management, SIEM, UEBA, SOAR, and insider threat capabilities, plus compliance. Unique in its ability to replace a SIEM or augment one with UEBA and automation, Exabeam helps organizations of any size and maturity to achieve security operations excellence.

How can we help? Talk to an expert.
Contact UsFrequently Asked Questions
What are the key considerations before starting an Exabeam engagement?
Can I see the existing data sources configured?
Absolutely! You can find all the current log sources with pre-built parsers here, conveniently organized by vendor for easy reference.
How can I request a cloud services log collector not currently supported by Exabeam?
Please contact your support representative. If the collector hasn’t already been requested and added to the roadmap, you can submit a request. The product team will evaluate these requests and incorporate them into the timeline or roadmap. Early Access for new Collectors, released monthly, is accessible directly within the Exabeam Security Operations Platform, without requiring support assistance.
“Threat Center will save analysts countless hours by enabling SOC analysts to work from one single interface performing investigations and taking actions against identified threats. The Exabeam Copilot AI virtual assistant will be a force multiplier for SOC teams helping to improve cybersecurity across organizations.”
See Exabeam in Action
Request a demo to see how Exabeam helps security operations teams secure the agentic enterprise.
You’ll learn how to:
- Monitor and analyze human & agent behavior to uncover risk
- Investigate threats with machine-built timelines
- Use multi-agent AI to improve detection, investigation, and response workflows
- Apply playbooks to guide decisions
- Support compliance requirements
Award-Winning Leader in Security