When I started at Exabeam two years ago, we had a primarily on-premises product that had just moved to a SaaS offering. I recognized that we had a strong, unique position in the market with user and entity behavior analytics (UEBA) and a differentiated offering — a great foundation for any technology provider. As I considered the future, where we needed to evolve our products, we did what every good product organization should do: we talked to customers to make sure we truly understood their challenges.
In having those conversations, we realized that there was an opportunity to help security operations teams get a more complete picture of what’s happening in their environments so they can more effectively detect, investigate, and respond to threats.
We heard customers say that they’re overwhelmed with data. “What data is useful? How do I collect it? How do I leverage it? How long should I keep it?” At the same time, cyberattacks are becoming more and more sophisticated and just about impossible to detect using traditional rule-based solutions alone. Security analysts are doing the best they can to respond to incidents using the tools they have, but they’re dealing with a plethora of alerts without the ability to quickly pick out the ones that are helpful for detecting and responding to real threats.
We saw that this was a moment for Exabeam to disrupt the market in the truest sense, by combining the power of cloud with the strength we had in UEBA to bring together a new offering. The three things we considered were:
- How can we make it easier to ingest security data at scale, help store petabytes of it, and deliver a powerful, yet simple, search functionality that anyone can learn?
- How can we get a baseline of normal user and entity activity to identify anomalous behavior that warrants further investigation?
- How can we simplify and automate the investigation experience to make teams more productive and accurate?
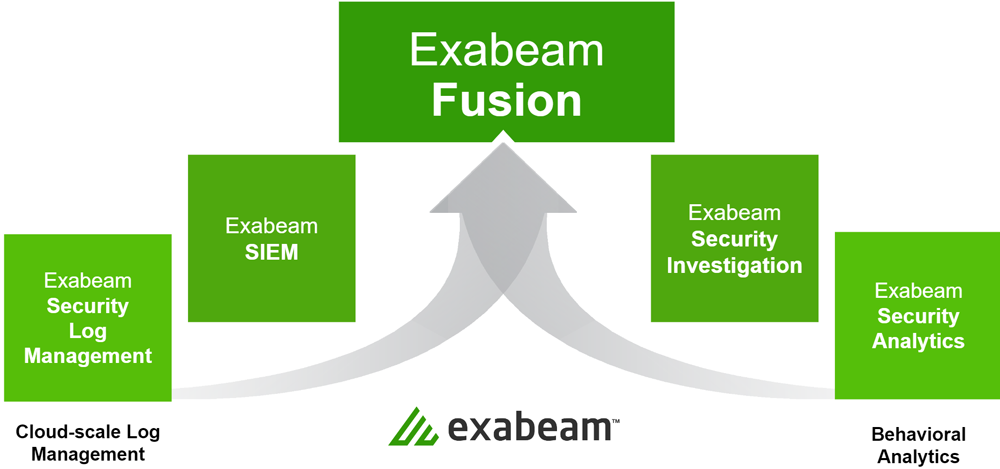
All of this culminates in what Exabeam announces today: a new security operations platform with five products designed to solve the problems we’ve heard about time and again:
- Security teams need to collect more of the right data.
- Teams must know what they are looking for.
- Threats are buried in a sea of noise.
- Manual investigations lead to incomplete outcomes.
In this blog post:
- A new approach for security operations: New-Scale SIEM™
- Exabeam Security Log Management™
- Exabeam SIEM™
- Exabeam Security Analytics™
- Exabeam Security Investigation™
- Exabeam Fusion™
- Purpose-built for security
A new approach for security operations: New-Scale SIEM™
Overall, what we’ve seen is that security operations teams are struggling with the limitations of legacy SIEMs, and a new approach is needed. We call it New-Scale SIEM. It includes a breakthrough set of capabilities security operations teams need in products and want to use.
What does New-Scale SIEM really mean?
- Cloud-scale security log management — Pull data from all sources, including context; easily ingest, parse, store, search, and present more of the right data from everywhere. Get instant results over petabytes (PB) and years of data. This is foundational. Then, more capabilities can be integrated.
- Powerful behavioral analytics — Establish a baseline of normal behavior with histograms, and detect and prioritize unusual events. Stay ahead of threats by detecting insiders as they move throughout the organization with built-in awareness of adversary tactics, such as aligning with the MITRE ATT&CK® framework.
- Automated investigation — Get a full picture and resolve incidents faster by automating investigations and response actions. Exabeam Smart Timelines™ reconstruct the chain of incidents to find out what really happened. Analysts can recapture two-thirds of their time on detection, triage, and investigation.
We realize that there are multiple ways that organizations want to get started, depending on their needs. There are two clear paths customers can take to solve for security operations with Exabeam: leverage Exabeam as their security data lake and SIEM, or get more value from their existing SIEM or data lake by leveraging Exabeam’s threat detection, investigation, and response (TDIR) capabilities. Whatever their needs, we have designed solutions to meet them at the right stage of their security operations journey.
And we understand that the journey may align differently for everyone. There may be a very small organization with a one- or two-person security operations team that is super advanced and ready for the most sophisticated security technology that exists. Or there could be a global company with dozens of security personnel around the world that is struggling to collect logs and get them into a system that can complete basic search tasks.
Below, I’ll introduce each product and explain which solutions are best suited for organizations at different entry points.
Exabeam Security Log Management™
I’ll begin with Exabeam Security Log Management, which is cloud-scale log management, fast and modern search, powerful dashboarding and correlation capabilities, built in a solution that is easy to use and easy to deploy. It scales to meet the ever-growing need organizations have in terms of data. The performance is incredible — delivering rapid log ingestion processing at a sustained rate of more than 1M EPS per tenant on a platform that scales to PB of data.
This is our cost-effective entry point to ingest, parse, store, and search security data all in one place, with a fast, sophisticated dashboarding experience across multi-year data. Write, test, and monitor custom correlation rules — no advanced programming or query-building skills required. Our Threat Intelligence Service (available at no cost in all products) adds deeper context to rules, to deliver more accurate and efficient threat management.
Exabeam Security Log Management is best suited for an organization with any of these needs:
- A cloud-native security data lake — a place to collect all of your data
- An easy and intuitive way to collect data from all the sources and locations that matter to them
- A need for a simplified search experience with fast query and instant results over PB-scale and/or years of data — search hot and cold data at the same speed
- View, print, or export data, dashboards, and pre-built reports produce logs for a compliance audit
- A solution that provides cost effective and cloud-scale log management where a full SIEM is not a requirement
- Write, test, publish, and monitor their own correlation rules for their critical systems and assets
Learn more: See Exabeam Security Log Management in action.
Exabeam SIEM™
Building on Exabeam Security Log Management, Exabeam SIEM includes all of that product’s features, plus more than 100 pre-built correlation rules and alert and case management. Similar to Exabeam Security Log Management, integrated threat intelligence improves the fidelity of detections, and adds deeper context for correlation rule building and enhancement. This is way more than just a log management solution — this is a real SIEM. Turn log data into actionable events that support security use cases. Create a dashboard in literally a minute. With automated alert triage workflows, know how to look at an alert, respond to it, and build a case around it. All of this sets the stage for a more advanced TDIR workflow or investigation experience.
Exabeam SIEM is best suited for an organization with any of these needs:
- A first-time SIEM — a great starting point for correlation building and alert and case management along with security log management
- To transition from an on-premises solution to a cloud-native SIEM
- To replace a current SIEM with a SIEM that includes more advanced threat detection, investigation, and response (TDIR) capabilities
- More than 100 pre-built correlation rules matching some of the most common use cases and threat types
Learn more: Read more about Exabeam SIEM.
Exabeam Security Analytics™
Exabeam Security Analytics provides automated threat detection powered by UEBA with correlation and threat intelligence to detect and respond to complex and anomalous threat types like compromised credentials. This product is designed to operate on and enhance a third-party SIEM or data lake. Examine patterns of behaviors to understand what is normal in an organization’s environment, so it can detect anomalies. Automated risk score assignment and machine learning prioritizes triage, investigation, and response for key incidents. Stitch together multiple events and alerts into a time horizon to unlock the story of what happened in an incident.
Exabeam Security Analytics is best suited for an organization that:
- Already has a SIEM or data lake but struggles to get value from that investment
- Wants deeper detection that cannot be derived from existing correlation rules or just looking at alerts — along with improved triage
- Needs visualization of event timelines, stitching together related events by user, entity, and device — wants to create watchlists for critical users or assets
- Is interested in insider threat programs and/or use cases that focus on specific threat types, e.g., compromised insiders, malicious insiders, and external threats
Learn more: Read more about Exabeam Security Analytics.
Exabeam Security Investigation™
When we designed Exabeam Security Investigation, we wanted to make the investigation experience more meaningful, so that people could investigate and find out what is really happening, versus just closing a ticket and moving on to the next one. We wanted to figure out how we could make that workflow more efficient. Exabeam Security Investigation is also designed to operate on and extend an existing third-party SIEM or data lake.
Exabeam Security Investigation builds on the UEBA capabilities of Exabeam Security Analytics with content, workflows, and automation to provide an intelligent triage capability for the TDIR workflow or investigation process. The automation of the alert triage process with machine learning-powered Dynamic Alert Prioritization, infuses third-party security alerts with context from UEBA and dynamic sorting to help identify, prioritize, and escalate the most meaningful alerts. Exabeam Security Investigation accelerates investigations, reduces response times, and ensures repeatable results with hundreds of security orchestration, automation, and response (SOAR) actions.
Exabeam Security Investigation is best suited for an organization that:
- Already has a SIEM or data lake but wants improved automation for investigation and response actions
- Is inundated with alerts and needs intelligent, dynamic prioritization to figure out what’s important to chase, and what can safely be ignored
- Wants turnkey playbooks for automating repeated workflows for investigation into compromised credentials, external attacks, or malicious insider use cases with guided checklists for resolution
- Is ready for the option to customize their responses to events and integrate more tightly into their security stack
Learn more: Read more about Exabeam Security Investigation.
Exabeam Fusion™
Exabeam Fusion brings it all together, uniting Exabeam Security Log Management and Exabeam SIEM with Exabeam Security Analytics and Exabeam Security Investigation to create the most powerful and advanced cloud-native SIEM on the market today. The combined capabilities include:
- Cloud-scale security log management
- Rapid data ingestion
- Simplified search experience with faster query and instant results over petabyte-scale and/or years of data
- Powerful behavioral analytics to uncover weak signals that other tools miss
- Automation that changes the way analysts do their jobs
- Automated investigation experience
Exabeam Fusion helps accelerate investigations, reduce response times, and ensure consistent, repeatable results – replacing any SIEM or security operations tool.
Exabeam Fusion is best suited for an organization that:
- Is looking for a combination of cloud-scale SIEM with the most advanced security investigation capabilities
- Has a security-focused mindset and a level of expertise that understands TDIR, wants to align with the ATT&CK framework, and has specific use case requirements, e.g., insider threat program — needs far greater than a traditional SIEM can provide
- Is recovering from a breach or compromise and needs to invest in deeper detection, investigation, and response capabilities; and want to focus on security use-case outcomes for discovering compromised accounts, identifying malicious insider threats, identifying privileged account abuse, cloud security monitoring, and entity monitoring
Learn more: See Exabeam Fusion in action.
Purpose-built for security
There are a number of security practitioners and experts at Exabeam, and we use our extensive knowledge to build products that are security-centric. I’ve been in security for a long time — more than 20 years — and I have a deep understanding of this space. Everyone on our product team has a background in cybersecurity, and many are former practitioners. I can confidently say that Exabeam products are built for security people by security people.
There’s more to accomplish, but this is a compelling evolution and a clear execution milestone of our expertise and vision. We want to be the holistic security operations platform by providing and coordinating timely automated visibility, detection, analytics, investigation, and response across organizations’ key operating environments — including on-prem, SaaS, and cloud infrastructure.
Launching New-Scale SIEM was a tremendous undertaking, and represents the most significant innovation in our history. Many customers have already transitioned to the new platform, and the early reports are very positive. We appreciate all of the customers, partners, analysts and Exabeamers who helped make this achievement possible.
Learn more: Discover New-Scale SIEM.
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!











