
-
- Home
>
-
- Explainers
>
-
- UEBA
UEBA (User and Entity Behavior Analytics): Complete 2025 Guide
- 14 minutes to read
Table of Contents
What is User and Entity Behavior Analytics (UEBA)?
UEBA, which stands for User and Entity Behavior Analytics, is a cybersecurity technology that analyzes user and entity behavior to detect anomalous and potentially malicious activities. It goes beyond traditional security measures by focusing on patterns of behavior, not just known threats, using machine learning and advanced analytics to identify deviations from normal activity. This helps organizations detect insider threats, compromised credentials, and other sophisticated attacks. (Related content: Read our guide to security analytics)
The core function of UEBA includes:
- Behavioral analysis: UEBA systems analyze user and entity behavior, including actions like login attempts, file access, network traffic, and application usage.
- Anomaly detection: It establishes a baseline of normal behavior for each user and entity and then flags deviations from that baseline as potential threats.
- Machine learning: UEBA leverages machine learning algorithms to identify subtle patterns and anomalies that might be missed by traditional security methods.
Key benefits include:
- Enhanced threat detection: UEBA can detect a wider range of threats, including insider threats, compromised accounts, and advanced persistent threats (APTs).
- Improved security posture: By proactively identifying suspicious activity, UEBA helps organizations improve their overall security posture and reduce the risk of data breaches.
- Reduced false positives: UEBA’s ability to analyze context and behavior helps minimize false alarms, allowing security teams to focus on genuine threats.
- Faster incident response: By quickly identifying and alerting on anomalous behavior, UEBA enables faster incident response and containment.
- Comprehensive visibility: UEBA provides a comprehensive view of user and entity activity, helping organizations understand how their systems are being used and identify potential security weaknesses.
UEBA tools use innovative algorithms, based on traditional machine learning and deep learning, to discover abnormal and risky behavior by users, machines and other entities on the corporate network often in conjunction with a Security Incident and Event Management (SIEM) solution.
This is part of an extensive series of guides about cybersecurity.
The Growing Need for UEBA: Insider Risks Surpass External Threats
According to our recent report, From Human to Hybrid: How AI and the Analytics Gap Are Fueling Insider Risk, insider risks have now surpassed external threats as the leading concern for security teams. In our survey, 64% of cybersecurity professionals identified malicious or compromised insiders as a greater danger than outside attackers, compared to 36% who pointed to external actors.
Within that 64%, 42% saw malicious insiders as the primary concern, and 22% cited compromised insiders. Over half (53%) reported insider incidents had increased in the past year, and 54% expect them to rise further in the next 12 months.
Detection capabilities remain underdeveloped. Only 44% of organizations are using user and entity behavior analytics (UEBA), which are critical for detecting abnormal activity. Although 88% say they have an insider threat program, many are informal, underfunded, or lack visibility across systems. Leadership alignment is also a gap: 74% of security professionals believe executives underestimate insider risk.
Generative AI is accelerating the problem. 76% of organizations have seen unauthorized use of GenAI tools by employees. AI-enhanced phishing and social engineering (27%) and unauthorized GenAI usage (22%) rank among the top insider threat vectors, alongside privilege misuse (18%).
Security leaders acknowledge the need for better behavioral insight, but face technical and organizational roadblocks. Privacy resistance (20%), lack of visibility (16%), and fragmented tools (10%) create blind spots in detection efforts.
How UEBA works
User and entity behavior analytics (UEBA) is a category of cybersecurity solutions or capabilities that analyze user and entity behavior and apply advanced analytics and behavioral modeling to determine anomalous behavior. UEBA is used to discover advanced security threats like malicious insiders and privileged account compromises, which traditional, rule-based security tools cannot see. UEBA solutions ingest operational data from many sources and determine what is the normal behavior of any user or non-human entity. Entities may include IT assets such as hosts, applications, network traffic, service accounts, and data repositories. Over time, the solution builds standard profiles of behavior for users and entities across peer groups to create a baseline for what is normal in an organization. When anomalous activity is identified, it is assigned a risk score. The score rises with increasing amounts of anomalous behavior until it crosses a predefined threshold triggering an alert to security analysts. Some solutions can automate response actions.
Here’s a more detailed look at UEBA’s core function:
- Machine learning: UEBA applies supervised and unsupervised machine learning techniques to detect subtle anomalies that static rules cannot catch. Algorithms can adapt as user behavior evolves, reducing the need for constant manual updates. This allows the system to uncover hidden attack patterns, such as low-and-slow data exfiltration or privilege abuse, that unfold gradually and might otherwise evade detection.
- Behavioral analysis: UEBA collects and correlates data from multiple sources such as authentication logs, file systems, email, and cloud applications to build a comprehensive view of activity. It tracks not just isolated events but also sequences of actions over time, making it possible to identify unusual workflows, access attempts, or usage patterns that may indicate misuse or compromise.
- Anomaly detection: Once normal behavior profiles are established, UEBA continuously compares new activity against these baselines. Deviations such as login attempts from unusual locations, excessive file downloads, or unexpected access to sensitive resources are flagged. The system assigns context to these anomalies, helping analysts distinguish between benign deviations and genuine threats.
Related content: Read our guide to behavioral profiling.
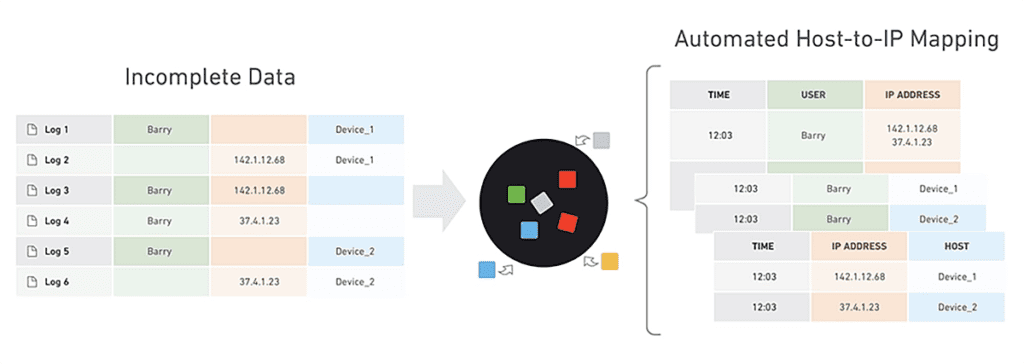
Holistic analysis across multiple data sources
The true power of a UEBA solution is in its ability to cut across organizational boundaries, IT systems and data sources and analyze all the data available for a specific user or entity.
A UEBA solution should analyze as many data sources as possible, some example data sources include:
- Authentication systems like Active Directory
- Access systems like VPN and proxies
- Configuration Management Databases
- Human resources data–new employees, departed employees, and any data that provides additional context on users
- Firewall, Intrusion Detection and Prevention Systems (IDPS)
- Anti-malware and antivirus systems
- Endpoint Detection and Response systems
- Network Traffic Analytics
- Threat Intelligence feeds
For example, a UEBA solution should be able to identify unusual login via Active Directory, cross reference it with the criticality of the device being logged onto, the sensitiveness of the files accessed, and recent unusual network or malware activity which may have enabled a compromise.
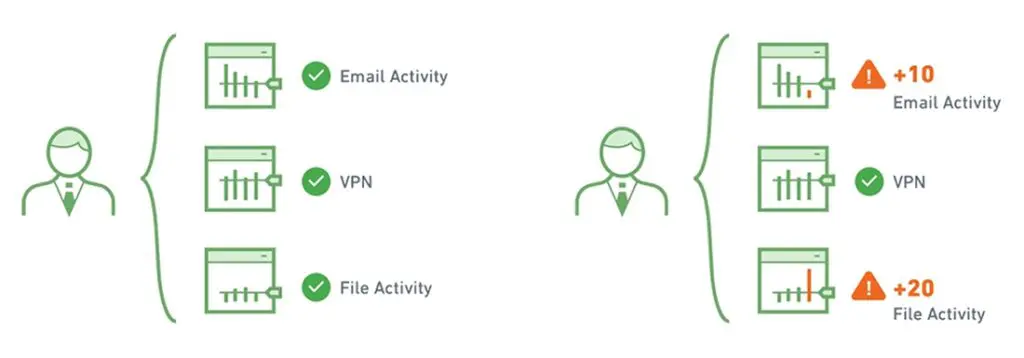
Behavioral baselining and risk scores
A UEBA solution learns normal behavior to identify abnormal behavior. It examines a broad set of data to determine a user’s baseline or behavioral profile.
For example, the system monitors a user and sees how they use a VPN, at what time they arrive to work and which systems they log into, what printer they use, how often and what size of files they send by email or load to a USB drive, and many other data points that define the user’s “normal behavior”. The same is done for servers, databases or any significant IT system.
When there is deviation from the baseline, the system adds to the risk score of that user or machine. The more unusual the behavior, the higher the risk score. As more and more suspicious behavior accumulates, the risk score increases until it hits a threshold, causing it to be escalated to an analyst for investigation.
This analytical approach has several advantages:
- Aggregation – the risk score is made up of numerous events, so there is no need for analysts to manually review large numbers of individual alerts and mentally combine them to detect a threat.
- Reduced false positives–one slightly abnormal event on its own will not result in a security alert. The system requires multiple signs of abnormal behavior to create an alert, reducing the number of false positives and saving time for analysts.
More context — traditional correlation rules defined by security administrators may have been correct for one set of users or systems, but not for others. For example, if a department starts employing shift workers or offshore workers, they will start logging in at unusual times, which would trigger a rule-based alert all the time. UEBA is smarter because it establishes a context-sensitive baseline for each user group. An offshore worker logging in at 3am local time would not be considered an abnormal event.
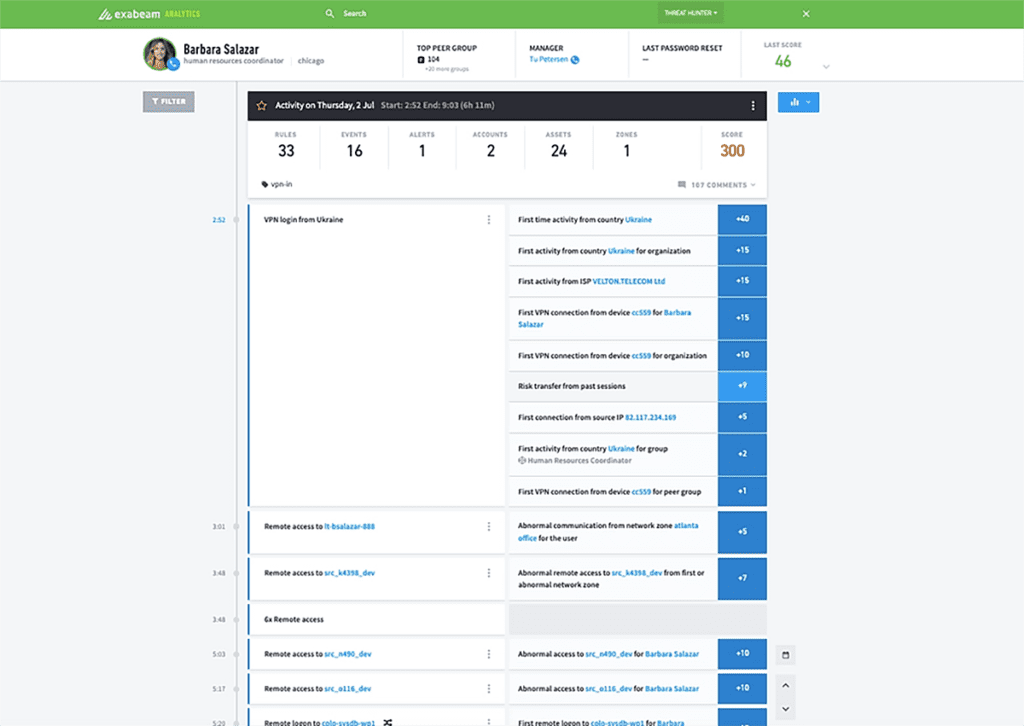
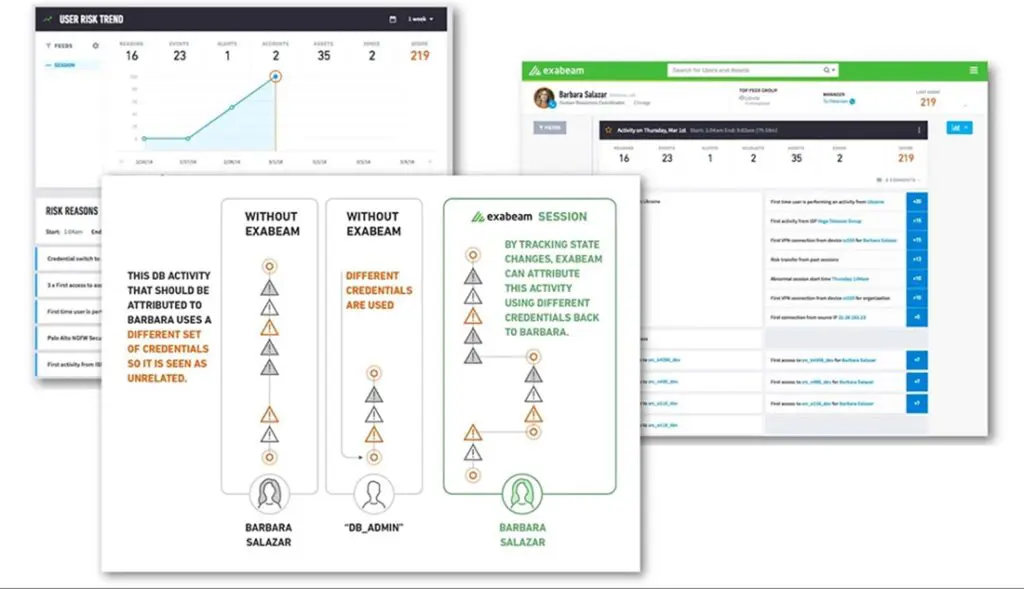
Timeline analysis and session stitching
When analyzing security incidents, the timeline is a critical concept which can tie together seemingly unrelated activities. Modern attacks are processes, not isolated events.
For example, consider a user who logged in, performed suspicious activity and then disappeared from the logs. Was the same IP used to connect to other organizational systems shortly afterwards? If so, this could be part of the same incident, with the same user continuing their attempt to penetrate the system. An additional example could be an attacker logging in to the same machine multiple times using different credentials. This also requires “stitching” together data about the various login attempts and flagging them as a single incident.
UEBA use cases and examples
Insider threats
There are three types of insider threats:
- Negligent insider – A negligent insider is an employee or contractor with privileged access to IT systems, who unintentionally puts their organization at risk because they do not follow proper IT procedures. For example, someone who leaves their computer without logging out, or an administrator who did not change a default password or failed to apply a security patch. Identifying normal vs abnormal activity for a user is key to detecting a user that has been compromised by negligence.
- Malicious insider – A malicious insider is an employee or contractor with privileged access to IT systems, who intends to perform a cyber attack against the organization. It is difficult to measure malicious intent or discover it through log files or regular security events. UEBA solutions help by establishing a baseline of a user’s typical behavior and detect abnormal activity.
- Compromised insider – It’s common for attackers to infiltrate an organization and compromise a privileged user account or trusted host on the network, and continue the attack from there. UEBA solutions can help rapidly detect and analyze malicious activity that the attacker carries on via the compromised account.
Traditional security tools find it difficult to detect a compromised insider if the attack pattern or kill chain is not currently known (such as in a zero day attack), or if the attack moves laterally through an organization by changing credentials, IP addresses, or machines. UEBA technology, however, can detect these types of attacks, because they will almost always force assets to behave differently from established baselines.
Incident prioritization
A SIEM collects events and logs from multiple security tools and critical systems, and generates a large number of alerts that must be investigated by security staff. This leads to alert fatigue, a common challenge of Security Operations Centers (SOC).
UEBA solutions can help understand which incidents are particularly abnormal, suspicious or potentially dangerous in the context of your organization. UEBA can go beyond baselines and threat models by adding data about organizational structure–for example, the criticality of assets and the roles and access levels of specific organizational functions. A small deviation from norm for a critical protected system or a top-level administrator, might be worth a look for an investigator; for a run-of-the-mill employee only a major deviation would receive high priority.
Data loss prevention (DLP) and data leak prevention
Data Loss Prevention (DLP) tools are used to prevent data exfiltration, or the illicit transfer of data outside organizational boundaries. Traditional DLP tools report on any unusual activity carried out on sensitive data–they create a high volume of alerts which can be difficult for security teams to handle.
UEBA solutions can take DLP alerts, prioritize and consolidate them by understanding which events represent anomalous behavior compared to known baselines. This saves time for investigators and helps them discover real security incidents faster.
Entity analytics (IoT)
UEBA can be especially important in dealing with Internet of Things (IoT) security risks. Organizations deploy large fleets of connected devices, often with minimal or no security measures. Attackers can compromise IoT devices, use them to steal data or gain access to other IT systems, or worse–leverage them in DDoS or other attacks against third parties.
Two sensitive categories of IoT are medical devices and manufacturing equipment. Connected medical devices may contain critical data, and may be life threatening if used directly for patient care. Manufacturing equipment can cause large financial losses if disrupted, and in some cases may threaten employee safety.
UEBA can track connected devices, establish a behavioral baseline for each device or group of similar devices, and immediately detect if a device is behaving outside its regular boundaries. For example:
- Connections to or from unusual addresses or devices
- Activity at unusual times
- Device features activated which are typically not used
Convergence of UEBA and SIEM
There is a close relation between UEBA and SIEM technologies, because UEBA relies on cross-organizational security data to perform its analyses, and this data is typically collected and stored by a SIEM.
Gartner views UEBA as a feature incorporated into a SIEM. Behavior analysis is one of the capabilities by which Gartner evaluates the vendors in the Magic Quadrant for Security Information and Event Management. Gartner outlines the following capabilities for a SIEM:
- Aggregate event data produced by security devices, network infrastructure, systems and applications
- Combine event data with contextual information about users, assets, threats, and vulnerabilities for the purpose of scoring, prioritization and expediting investigations
- Normalize the data to analyze more efficiently
- Offer real-time analysis of events for security monitoring, advanced analysis of user and entity behaviors, querying analytics, supporting incident investigation and management, and reporting.
UEBA vs. Similar Technologies
UEBA vs. NTA
Network traffic analysis (NTA) focuses on monitoring and analyzing network communications to detect anomalies or signs of compromise. While both UEBA and NTA identify abnormal behavior, their scopes differ.
UEBA examines user and entity behavior across diverse systems—including endpoints, applications, and directories—not just network activity. NTA is limited to network data and excels at identifying threats like lateral movement and data exfiltration. In contrast, UEBA can detect threats that involve privileged access abuse, unusual login behavior, or changes in file access patterns. NTA typically supports real-time traffic analysis, whereas UEBA works with both real-time and historical data for long-term behavior modeling.
Together, UEBA and NTA can complement each other: NTA highlights suspicious network paths, while UEBA provides behavioral context about who or what is involved.
UBA vs. UEBA
User behavior analytics (UBA) is an earlier generation of technology focused solely on human users. It analyzes user behavior to detect risks such as credential misuse, insider threats, or suspicious access patterns.
UEBA (user and entity behavior analytics) expands this concept by including non-human entities like servers, applications, and IoT devices. This broader scope is critical as many attacks target or originate from entities beyond human users. UEBA also typically incorporates more advanced analytics, such as machine learning models capable of identifying complex behavioral anomalies across hybrid environments.
In short, UEBA builds on UBA by providing a more comprehensive view of all entities in an IT environment and the relationships between them.
UEBA analytics methods
Some UEBA solutions rely on traditional methods to identify suspicious activity. These can include manually-defined rules, correlations between security events and known attack patterns. The limitation of traditional techniques is that they are only as good as the rules defined by security administrators, and cannot adapt to new types of threats or system behavior.
Advanced analytics involves several modern technologies that can help identify abnormal behavior even in the absence of known patterns:
- Supervised machine learning–sets of known good behavior and known bad behavior are fed into the system. The tool learns to analyze new behavior and determine if it is “similar to” the known good or known bad behavior set.
- Bayesian networks–can combine supervised machine learning and rules to create behavioral profiles.
- Unsupervised learning–the system learns normal behavior, and is able to detect and alert on abnormal behavior. It will not be able to tell if the abnormal behavior is good or bad, only that it deviates from normal.
- Reinforced / semi-supervised machine learning–a hybrid model where the basis is unsupervised learning, and actual alert resolutions are fed back into the system to allow fine tuning of the model and reduce the signal-to-noise ratio.
- Deep learning–enables virtual alert triage and investigation. The system trains on data sets representing security alerts and their triage outcomes, performs self-identification of features, and is able to predict triage outcomes for new sets of security alerts.
Traditional analytics techniques are deterministic, in the sense that if certain conditions were true, an alert was generated, and if not the system assumed “all is fine”. The advanced analytics methods listed above are different in that they are heuristic. They compute a risk score which is a probability that an event represents an anomaly or security incident. When the risk score exceeds a certain threshold, the system creates a security alert.
Challenges in UEBA Deployment
Data Integration and Scaling
One of the major challenges in UEBA deployment is the integration of diverse data sources. UEBA systems rely on comprehensive, high-quality data from identity management systems, application logs, network traffic, endpoint telemetry, and more. Integrating these sources—often in different formats and volumes—can be complex and time-consuming.
Scalability is another issue. As organizations grow and add more devices, applications, and users, the volume of data increases exponentially. UEBA solutions must process this data in near real-time while maintaining performance. Without proper planning, performance bottlenecks and increased latency can degrade detection capabilities and analyst workflows.
False Positives
Despite advanced analytics, false positives remain a significant concern in UEBA deployments. If the system generates too many alerts for benign anomalies—such as a legitimate user working from a new location—security analysts may become overwhelmed or desensitized.
This problem is often linked to immature baselining or insufficient context in behavior models. Over time, as the system learns and fine-tunes risk scoring, false positives can decrease. However, in the early stages of deployment or in dynamic environments, maintaining acceptable alert quality can be difficult.
Skill and Resource Requirements
UEBA platforms require skilled personnel for configuration, tuning, and maintenance. Organizations need analysts with knowledge of behavioral analytics, threat detection, and incident response. Additionally, data engineers may be needed to ensure proper data ingestion and normalization.
Smaller organizations may lack the expertise or headcount to support a full-scale UEBA implementation. Even for larger enterprises, integrating UEBA into existing security operations can require a significant time investment and ongoing effort to keep models accurate and effective.
Key Best Practices for UEBA Implementation
1. Ensure Comprehensive, High‑Quality Data Integration
UEBA systems rely on rich, diverse data to accurately model behavior. Start by identifying key data sources across identity providers (e.g., Active Directory, LDAP), endpoint logs, cloud applications, VPNs, proxies, and network traffic. Ingest both structured and unstructured data to build complete behavioral profiles.
Use connectors, APIs, or log shippers to automate data collection, and ensure that time synchronization across sources is consistent—time discrepancies can prevent accurate timeline analysis. Invest in data normalization and enrichment processes to standardize formats, resolve ambiguities, and tag relevant metadata such as user roles or asset classifications.
High-quality data is not just a technical requirement—it’s foundational to UEBA’s ability to generate meaningful, actionable insights. Poor data quality results in skewed baselines, ineffective anomaly detection, and increased false positives.
2. Establish Robust Behavior Baselines
UEBA effectiveness depends on the strength of its behavioral models. Begin by allowing the system an observation period—typically several weeks—during which it monitors activity without alerting. During this period, the system establishes baselines for users and entities by learning usage patterns, access times, network interactions, and system behavior.
For greater accuracy, baselines should be peer-aware, incorporating behavior comparisons among users in similar roles or systems in the same operational category. Incorporating organizational context, such as department or location, helps tailor baselines and prevent misclassifications.
Regularly review and refine these baselines. If business operations shift—such as the addition of remote teams or a seasonal spike in activity—ensure the system adapts. Static baselines in dynamic environments lead to blind spots or alert fatigue.
3. Configure Thresholds and Risk Scoring Thoughtfully
Not all anomalies warrant equal concern. UEBA systems use risk scores to assess the severity of deviations, but these must be calibrated carefully. Start with conservative thresholds to avoid overwhelming analysts, and adjust based on operational feedback and incident analysis.
Risk scoring should account for anomaly frequency, severity, and the criticality of the affected system or user. For example, an unusual login on a high-value server by an administrator should carry more weight than the same action on a generic workstation.
Use dynamic thresholds where possible—adaptive systems that learn acceptable variance over time can provide more nuanced alerting. Also, define escalation paths and automate response actions for high-confidence, high-risk events to speed up mitigation.
4. Enrich Alerts with Context and Threat Intelligence
Context is essential to reduce time-to-triage and improve decision-making. Enrich alerts with metadata from HR systems (e.g., employment status, department), asset inventories (e.g., system criticality), and historical behavior patterns. Include details such as login times, device IDs, geolocation, and data access logs.
Integrate threat intelligence feeds to match anomalies against known indicators of compromise (IOCs) or attacker tactics, techniques, and procedures (TTPs). This helps distinguish between random anomalies and targeted threats.
Present enriched alerts in an analyst-friendly format, linking them to related events in the attack chain. This minimizes manual investigation time and improves the quality of response actions.
5. Integrate In-Line with Security Stack and Workflows
To maximize value, UEBA must operate within the broader security ecosystem. Integrate with SIEM platforms to leverage existing log collection and correlation capabilities. Feed risk scores and alerts into SOAR systems to enable automated playbook execution, such as isolating devices or resetting credentials.
Ensure UEBA output maps to your existing incident response workflows, ticketing systems, and reporting dashboards. This allows seamless handoff between detection and investigation teams, and avoids duplication of effort.
Test integrations thoroughly—UEBA systems must not only deliver accurate alerts but also fit operational realities. Alert volume, response time, and usability are just as important as detection fidelity. Aim for a tightly coupled architecture where behavioral analytics become a natural part of your security operations lifecycle.
Exabeam: An integrated SIEM and UEBA solution
Several systems are deployed in the field which combine the breadth of data in a SIEM with the deep analytics made possible by cutting-edge UEBA engines.
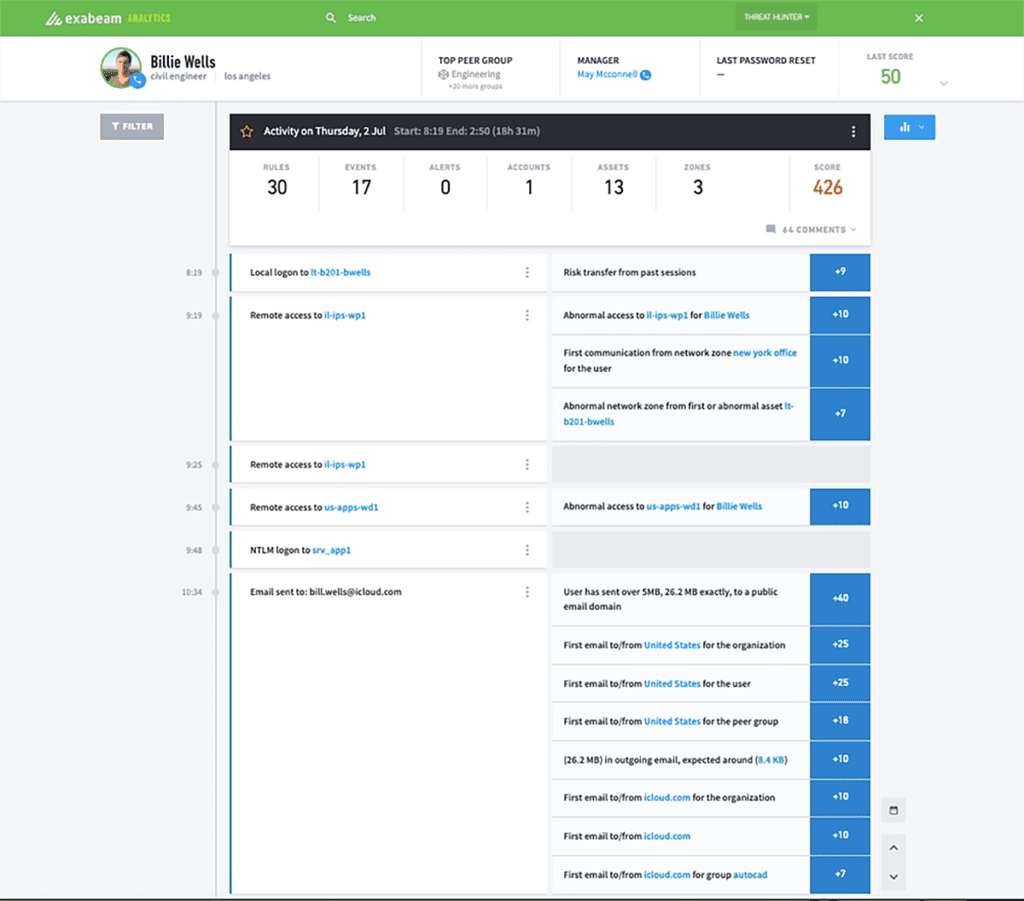
One example of an integrated system is the Exabeam SOC Platform. Exabeam is a full SIEM solution based on modern data lake technology. In addition, it provides the following UEBA capabilities:
- Rule and signature-free incident detection — Exabeam uses advanced analytics to identify abnormal and risky activity without predefined correlation rules or threat patterns. It provides meaningful alerts without requiring heavy setup and fine tuning, and with lower false positives.
- Automatic timelines for security incidents — Exabeam can stitch together related security events into a timeline that shows a security incident, spanning multiple users, IP addresses and IT systems.
- Dynamic peer groupings — Exabeam not only performs behavioral baselining of individual entities, it also dynamically groups similar entities (such as users from the same department, or IoT devices of the same class), to analyze normal collective behavior across the entire group and detect individuals who exhibit risky behavior.
- Lateral movement detection — Exabeam detects attackers as they move through a network using different IP addresses, credentials and machines, in search of sensitive data or key assets. It ties together data from multiple sources to connect the dots and view the attacker’s journey through the network.
See Additional Guides on Key Cybersecurity Topics
Together with our content partners, we have authored in-depth guides on several other topics that can also be useful as you explore the world of cybersecurity.
Authored by Cloudian
- [Guide] What Is Disaster Recovery? – Features and Best Practices
- [Guide] The Easy Way to Create Your Own IT Disaster Recovery Plan
- [Blog] Cloudian Ransomware Survey
- [Product] Cloudian | Enterprise-Class, S3-Compatible Object Storage Software
Authored by Imperva
- [Guide[ What Is Next Generation Firewalls (NGFW) | Important Features
- [Guide] Financial Services Cybersecurity | Threats & Solutions
- [Blog] Imperva Detects Undocumented 8220 Gang Activities
- [Product] Imperva | Comprehensive Application and Data Security
Authored by Exabeam
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.