Exabeam applies Agent Behavior Analytics (ABA) within New-Scale Analytics to centralize visibility into agent activity. Your team can identify suspicious behavior, investigate agent-driven risk, and understand how agents interact with enterprise data and systems.
AI-DRIVEN DETECTIONS
Identify Threats Other Tools Overlook
New-Scale Fusion uses advanced AI to build behavioral baselines for users and entities while giving you visibility into AI agent activity. It correlates events, applies risk scores, and surfaces credible threats so your team can respond faster.

DETECT ANOMALOUS BEHAVIOR
Pinpoint High-Risk Anomalies
Exabeam identifies meaningful deviations from normal behavior by building behavioral baselines that reveal high-risk anomalies. Agent Behavior Analytics gives your team visibility into AI agent activity to uncover suspicious actions and a new class of insider risk.

PRIORITIZE THREATS
Focus on Credible Threats With Intelligent Prioritization
New-Scale Fusion groups related detections and uses multi-layered risk scoring to surface credible threats. By evaluating event rarity and business context, it keeps your analysts focused on the alerts and cases that carry the most risk.

DETECT LATERAL MOVEMENT
Track the Complete Attack Progression
Trace subtle lateral movement through users, devices, IP addresses, credentials, and automated processes. Patented Exabeam technology reveals the full attack chain, giving analysts an end-to-end view without gaps.

STRENGTHEN DETECTION WITH CONTEXT
Gain a Comprehensive Understanding of Risk
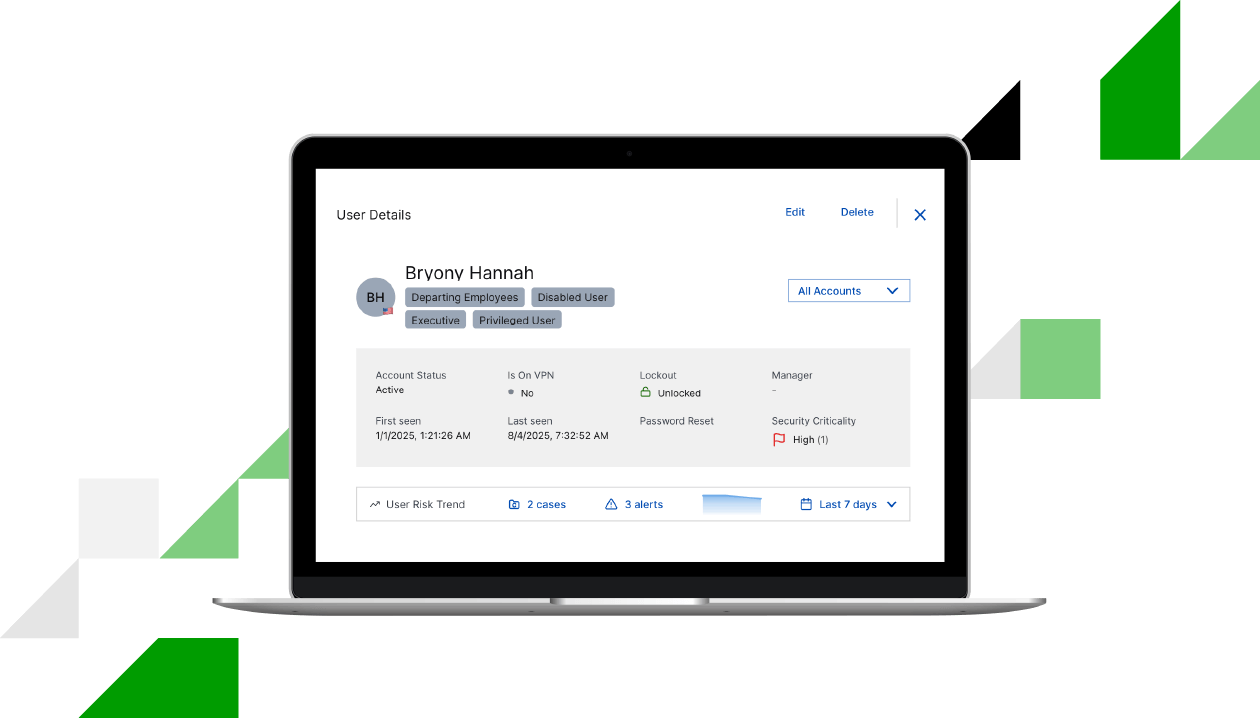
Attack Surface Insights adds detailed entity context to detections by profiling users, devices, applications, and agents. By mapping asset relationships and criticality, New-Scale Fusion give your analysts the context needed to understand risk and gauge business impact.

How can we help? Talk to an expert.
Contact UsFrequently Asked Questions
How does Exabeam detect and secure AI agents?
Can you provide more information about your generative AI guidelines and guardrails?
Exabeam ensures all inputs and outputs processed by foundation models, adapter models, and safety classifiers remain proprietary customer data. This data is retained only long enough to generate Exabeam Nova output and is never added to foundation models.
How does Exabeam provide strong insider threat coverage?
Exabeam addresses insider risk across human and non-human identities. Behavioral analytics establish baselines for human users to reveal subtle deviations, while deep monitoring of AI agents and service accounts helps your team see and investigate high-risk activity among trusted identities.
“Exabeam gives us an initial alarm followed immediately by context information on the alarm’s severity and timelines if more data is required. The SIEM only pushes forward with serious alerts, so we know if we need to switch into incident response mode.”
See Exabeam in Action
Request a demo to see how Exabeam helps security operations teams secure the agentic enterprise.
You’ll learn how to:
- Monitor and analyze human & agent behavior to uncover risk
- Investigate threats with machine-built timelines
- Use multi-agent AI to improve detection, investigation, and response workflows
- Apply playbooks to guide decisions
- Support compliance requirements
Award-Winning Leader in Security

































