Businesses invest heavily in battling cybersecurity threats, from installing top-of-the-line malware protection to monitoring their environments for unusual activity. But if your business focuses all its efforts on external threats, you’re missing an important piece of the puzzle.
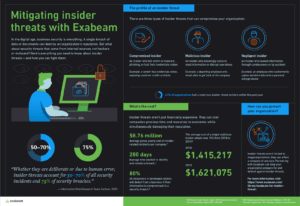
According to the Information Risk Research Team at Gartner, insider threats make up 50-70 percent of all security incidents. When it comes to security breaches, insiders are responsible for a full 75 percent. This statistic highlights the need for taking a very close look at the threats insiders pose for your business. Our infographic, “Mitigating insider threats with Exabeam” provides a high-level view of insider threat and the costs associated with it.
Three types of insider threats
An insider threat is defined as any threat that comes from someone who has been granted access to your systems. They could be employees, contractors, vendors, or even clients, anyone you’ve set up with a login and password. However, an insider threat can also be someone you’ve granted physical access to your premises, such as the cleaning crew or a technician brought in to perform warranty repairs.
But just as there are different roles an insider can have, there are also different motives for these attacks. Each insider threat falls into one of the following categories.
- Compromised insider — Perhaps the most problematic is this type of attack. A compromised insider has done nothing but innocently click on a link or input a password. Often this is done through phishing campaigns, which presents users with a link to an authentic-looking website in order to convince them to input login credentials or other sensitive data.
- Malicious insider — In this type of threat, the insider actually has malicious intent. A vendor could sell the information, for instance, or an angry employee could choose to sabotage you.
- Accidental insider — As much as you train employees to be cautious, mistakes happen. Something as simple as an employee leaving a workstation unlocked in a shared area could result in a data breach. Accidental incidents can also apply to your IT staff. An administrator could forget to apply a security patch, for example.
The cost of insider threats
It only takes one insider threat to put your business on a costly, time-consuming course. You’ll initially have to deal with stopping the damage and figuring out how to protect your network moving forward. But after that come the secondary costs.
The Ponemon Institute estimates that insider threats cost $8.76 million per year per affected company. Most businesses have far better uses for $8.76 million than cleaning up after a breach. Why so expensive?
It takes an average of 280 days to identify and contain each breach.
Unfortunately, the cost is only increasing with each passing year. From 2018 to 2019, the cost of a single malicious insider attack increased 15 percent, from $1.4 million in 2018 to $1.6 million in 2019.
But perhaps the biggest cost to your business is loss of customers. Would you continue to do business with a company after discovering your data had been exposed while on their servers? According to IDC, 80 percent of customers in developed nations will defect from a business after a security breach results in their data being leaked.
Protecting your organization
One of the biggest issues when it comes to insider threats is that they’re hard to predict. If an outsider is trying to get around your firewall, you can use software and security protocols to prevent it. But most traditional cybersecurity protections don’t turn that magnifying glass on what happens within the organization.
Increasing awareness has changed that in recent years. Here are some things your organization can do to protect against insider threats:
- Invest in training. The truth is, some accidental and compromised insider attacks can be prevented by simply training your end users on spotting and avoiding phishing attempts.
- Focus on user behaviors. Your security protocols can benefit from user and entity behavior analytics (UEBA). By understanding typical behaviors, you can more easily detect when an anomaly occurs.
- Use artificial intelligence. The right technology can make all the difference. Exabeam’s solution uses machine learning to send more accurate and timely alerts.
With 41 percent of all organizations experiencing a malicious insider threat incident in the past year, it’s important to put protocols in place to protect your data. For more information on how Exabeam protects against insider threats, or to schedule a free demo, click here.
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!