The 12 Elements of an Information Security Policy
- 6 minutes to read
Table of Contents
What is an information security policy?
Security threats are constantly evolving, and compliance requirements are becoming increasingly complex. Organizations must create a comprehensive information security policy to cover both challenges. An information security policy makes it possible to coordinate and enforce a security program and communicate security measures to third parties and external auditors.
To be effective, an information security policy should:
- Cover end-to-end security processes across the organization
- Be enforceable and practical
- Be regularly updated in response to business needs and evolving threats
- Be focused on the business goals of your organization
This content is part of a series about information security.
Recommended Reading: 4 Types of Cyber Threat Intelligence and Using Them Effectively.
The importance of an information security policy
Information security policies can have the following benefits for an organization:
- Facilitates data integrity, availability, and confidentiality – Effective information security policies standardize rules and processes that protect against vectors threatening data integrity, availability, and confidentiality.
- Protects sensitive data – Information security policies prioritize the protection of intellectual property and sensitive data such as personally identifiable information (PII).
- Minimizes the risk of security incidents – An information security policy helps organizations define procedures for identifying and mitigating vulnerabilities and risks. It also details quick responses to minimize damage during a security incident.
- Executes security programs across the organization – Information security policies provide the framework for operationalizing procedures.
- Provides a clear security statement to third parties – Information security policies summarize the organization’s security posture and explain how the organization protects IT resources and assets. They facilitate quick response to third-party requests for information by customers, partners, and auditors.
- Helps comply with regulatory requirements – Creating an information security policy can help organizations identify security gaps related to regulatory requirements and address them.
12 Elements of an Information Security Policy
A security policy can be as broad as you want it to be, from everything related to IT security and the security of related physical assets, but enforceable in its full scope. The following list offers some important considerations when developing an information security policy.
1. Purpose
First state the purpose of the policy, which may be to:
- Create an overall approach to information security., especially as touches standards, security requirements, and best practices adopted by the organization.
- Detect and preempt information security breaches such as misuse of networks, data, applications, and computer systems.
- Maintain the reputation of the organization, and uphold ethical and legal responsibilities and applicable governance.
- Respect employee and customer rights, including how to react to inquiries and complaints about non-compliance.
2. Audience
Define the audience to whom the information security policy applies. You may also specify which audiences are out of the scope of the policy (for example, staff in another business unit which manages security separately may not be in the scope of the policy).
3. Information security objectives
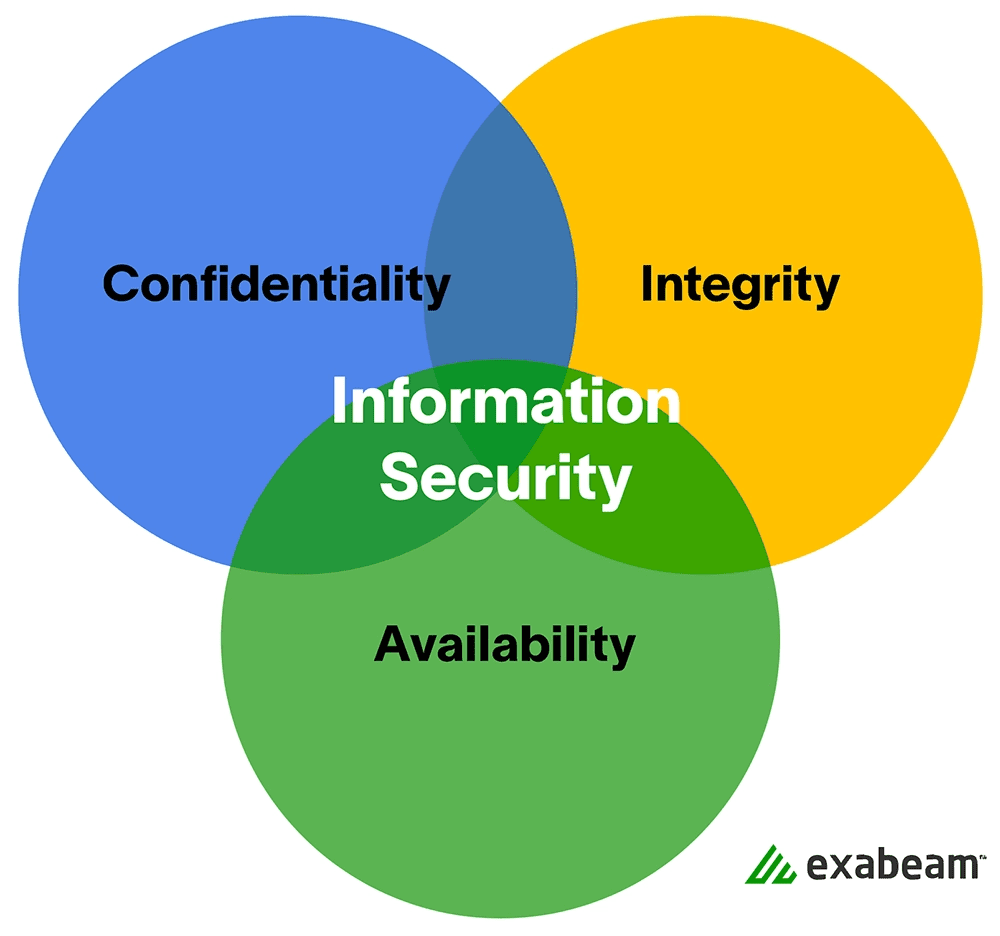
Guide your management team to agree on well-defined objectives for strategy and security. Information security focuses on three main objectives:
- Confidentiality — Only authenticated and authorized individuals can access data and information assets.
- Integrity — Data should be intact, accurate and complete, and IT systems must be kept operational.
- Availability — Users should be able to access information or systems when needed.
4. Authority and access control policy
- Hierarchical pattern – A senior manager may have the authority to decide what data can be shared and with whom. The security policy may have different terms for a senior manager vs. a junior employee or contractor. The policy should outline the level of authority over data and IT systems for each organizational role.
- Network security policy – Critical patching and other threat mitigation policies are approved and enforced. Users are only able to access company networks and servers via unique logins that demand authentication, including passwords, biometrics, ID cards, or tokens. You should monitor all systems and record all login attempts.
5. Data classification
The policy should classify data into categories, which may include “top secret,” “secret,” “confidential,” and “public.” The objectives for classifying data are:
- To understand which systems and which operations and applications touch on the most sensitive and controlled data, to properly design security controls for that hardware and software (see 6.)
- To ensure that sensitive data cannot be accessed by individuals with lower clearance levels
- To protect highly important data, and avoid needless security measures for unimportant data
6. Data support and operations
- Data protection regulations – systems that store personal data, or other sensitive data — must be protected according to organizational standards, best practices, industry compliance standards, and relevant regulations. Most security standards require, at a minimum, encryption, a firewall, and anti-malware protection.
- Data backup – Encrypt data backup according to industry best practices, both in motion and at rest. Securely store backup media, or move backup to secure cloud storage.
- Movement of data – Only transfer data via secure protocols. Encrypt any information copied to portable devices or transmitted across a public network.
7. Security awareness and behavior
Share IT security policies with your staff. Conduct training sessions to inform employees of your security procedures and mechanisms, including data protection measures, access protection measures, and sensitive data classification.
- Social engineering – Place a special emphasis on the dangers of social engineering attacks (such as phishing emails or informational requests via phone calls). Make all employees responsible for noticing, preventing, and reporting such attacks.
- Clean desk policy – Secure laptops with a cable lock. Shred sensitive documents that are no longer needed. Keep printer areas clean so documents do not fall into the wrong hands.
- Work with HR to define how the internet should be restricted both on work premises and for remote employees using organizational assets. Do you allow YouTube, social media websites, etc.? Block unwanted websites using a proxy.
8. Encryption policy
Encryption involves encoding data to keep it inaccessible to or hidden from unauthorized parties. It helps protect data stored at rest and in transit between locations and ensure that sensitive, private, and proprietary data remains private. It can also improve the security of client-server communication. An encryption policy helps organizations define:
- The devices and media the organization must encrypt
- When encryption is mandatory
- The minimum standards applicable to the chosen encryption software
9. Data backup policy
A data backup policy defines rules and procedures for making backup copies of data. It is an integral component of overall data protection, business continuity, and disaster recovery strategy. Here are key functions of a data backup policy:
- Identifies all information the organization needs to back up
- Determines the frequency of backups, for example, when to perform an initial full backup and when to run incremental backups
- Defines a storage location holding backup data
- Lists all roles in charge of backup processes, for example, a backup administrator and members of the IT team
10. Responsibilities, rights, and duties of personnel
Appoint staff to carry out user access reviews, education, change management, incident management, implementation, and periodic updates of the security policy. Responsibilities should be clearly defined as part of the security policy.
11. System hardening benchmarks
The information security policy should reference security benchmarks the organization will use to harden mission-critical systems, such as the Center for Information Security (CIS) benchmarks for Linux, Windows Server, AWS, and Kubernetes.
12. References to regulations and compliance standards
The information security policy should reference regulations and compliance standards that impact the organization, such as the General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), Payment Card Industry Data Security Standard (PCI DSS), the Sarbanes-Oxley Act (SOX), and the Health Insurance Portability and Accountability Act (HIPAA).
9 best practices for successful information security policies
- Information and data classification – helps an organization understand the value of its data, determine whether the data is at risk, and implement controls to mitigate risks
- Developers, security, and IT operations – should work together to meet compliance and security requirements. Lack of cooperation between departments may lead to configuration errors. Teams that work together in a DevSecOps model can coordinate risk assessment and identification throughout the software development lifecycle to reduce risks.
- Security incident response plan – helps initiate appropriate remediation actions during security incidents. A security incident strategy provides a guideline, which includes initial threat response, priorities identification, and appropriate fixes.
- SaaS and cloud policy – provides the organization with clear cloud and SaaS adoption guidelines, which can provide the foundation for a unified cloud ecosystem and standards of configuration, especially for development environments. This policy can help mitigate ineffective complications and poor use of cloud resources.
- Acceptable use policies (AUPs) – helps prevent data breaches that occur through misuse of company resources. Transparent AUPs help keep all personnel in line with the proper use of company technology resources.
- Identity and access management (IAM) regulations – let IT administrators authorize systems and applications to the right individuals and let employees know how to use and create passwords in a secure way. A simple password policy can reduce identity and access risks.
- Data security policy – outlines the technical operations of the organization and acceptable use standards in accordance with all applicable governance and compliance regulations.
- Privacy regulations – government-enforced regulations such as GDPR and CCPA protect the privacy of end users. Organizations that don’t protect the privacy of their users risk fines and penalties, and in some cases court action.
- Personal and mobile devices – Nowadays, most organizations have moved business processes to the cloud. Companies that permit employees to access company software assets from any location from any device risk introducing vulnerabilities through personal devices such as laptops and smartphones. Creating a policy for proper security of personal devices can help prevent exposure to threats via employee-owned assets.
Learn more about information security:
- Information security (InfoSec): The Complete Guide
- The 8 Elements of an Information Security Policy
- PCI Security: 7 Steps to Becoming PCI Compliant
- Cloud Security 101
- Threat Hunting: Tips and Tools
- IT Security: What You Should Know
- Machine Learning for Cybersecurity: Next-Gen Protection Against Cyber Threats
- Penetration Testing: Process and Tools
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.