In a recent Exabeam survey conducted by IDC, organizations were asked if they’ve had to invest additional resources to remediate a serious security incident in the past year — and over half said yes. That’s despite the fact that cybersecurity spending exceeded $92 billion in 2022 and is expected to surpass $170 billion by 2027.
Threat detection, investigation, and response (TDIR) workflows are fundamental for security operations centers (SOCs) to protect their organizations from attacks. It’s that third component — response and remediation — that often matters most, because it comes into play once an investigation has confirmed that an incident has indeed occurred.
In this article:
Protecting the present and future
While response may be the “R” in TDIR, this stage comprises response, remediation, and lessons learned. That means its aim is to not only identify the scope of the events, but to also contain the damage, mitigate or eradicate the root cause of the incident, and operationalize learnings for the future.
Defined in the context of TDIR, an “incident” represents a change in security posture that could be in breach of law or policy, or pose a threat to information assets such as networks, identities, or devices, which may or may not be materially reportable.
You need to be ready to respond
When an incident isn’t effectively managed, it can be catastrophic. Huge costs can be incurred — whether from data loss, system crashes, expensive recovery, or fines and penalties for negligence or noncompliance. And it becomes even costlier if it sullies an organization’s reputation with partners and customers.
The opposite is true when the response is rapid and effective. Losses can be reduced, processes and services can be restored, the scope and effects of the incident can be contained, and exploited vulnerabilities can be mitigated.
Consistency is key. Organizations with incident response plans are prepared for both known and unknown risks. They are equipped with best practices to manage incidents when they occur and block further intrusion after a threat is detected, while also preventing breaches before they happen.
However, certain factors hold many SOCs back from achieving this ideal state. Chief among them is a lack of automation across the TDIR workflow; remediation automation is one of the top functions organizations want for their TDIR platforms. There’s also a shortage of skilled talent, as exemplified in the aforementioned survey, in which 39% of respondents worried their teams lacked knowledge on how to respond to incidents. Another challenge is the ability to turn post-incident learnings into actionable and applicable new processes.
How to excel in incident response
Exabeam recommends the following six steps for incident response:
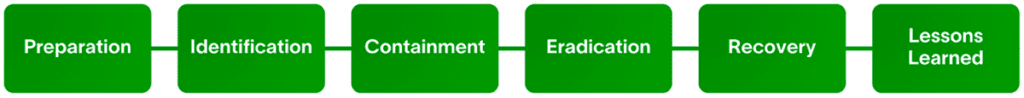
Proper incident response isn’t just kicked off once an investigation reveals a legitimate threat. Rather, it’s a six-step process that’s constantly engaged, even when there’s no evidence of an attack — remember, long-term prevention is one of the biggest benefits of a consistent response plan.
1. Preparation forms the foundation for cyberdefense, while also establishing a structure that can be continuously built and reinforced by developing and reviewing policies, conducting risk assessments, identifying known security issues and vulnerabilities, and outlining the roles, responsibilities, procedures, and protocols in the event an incident takes place.
2. Identification is deeply tied to the investigation stage of the TDIR workflow. It involves knowing the questions to ask and factors to consider in order to conduct basic triage and isolate an incident. As soon as it’s been assessed and evidence has been gathered, analysts need to diagnose the type and severity of the incident, and escalate if necessary.
3. Containment takes place once the incident is isolated to stop further damage. Some of these processes are short term, such as taking down production servers that have been hacked, while some are long term, such as rebuilding clean systems, installing patches, altering firewall rules, and changing routes. This is also the stage where the SOC should create a forensic image of their affected systems before they’re wiped.
4. Eradication follows after the emergency measures of containment have been carried out and the SOC can focus on isolating the root cause of the attack, removing threats and malware, and identifying and mitigating vulnerabilities. This can be disruptive to an organization, so communication and cooperation with architecture, operations, and engineering teams may be required.
5. Recovery involves carefully reintroducing the affected systems into the production environment after restoring them from clean backups. It then entails calculating the costs of the incident in terms of lost productivity and the human hours required to troubleshoot, repair, replace, and rebuild fully. The SOC also must determine how long the affected network and endpoint systems should be monitored to ensure they’re functioning normally.
6. Lessons learned is the final stage of the incident response workflow, where a post-incident analysis allows teams to debrief on what happened, what went well — and what didn’t — and explore options for improving the organization’s defense processes moving forward. By reporting on this, the security team has benchmarks for comparison and training materials for future team members.
Facilitating an effective, efficient incident response plan necessitates both humans and technology to work in tandem. A dedicated centralized security incident response team (CSIRT) should be appointed so that people have well-defined roles to play when an incident occurs. And a cloud-native, next-gen security information and event management (SIEM) solution that aggregates the data and powers the automation necessary to identify, contain, and eradicate threats at speed and scale should be implemented.
It’s crucial for security operations teams to connect every stage of the TDIR workflow — and every stage of the six-step incident response process — and there are many technicalities to consider. For a complete overview of how to do this, check out The Ultimate Guide to TDIR.
Unlock Advanced TDIR Strategies
Discover the critical insights and advanced strategies needed to enhance your TDIR capabilities. Read The Ultimate Guide to TDIR — a comprehensive resource with essential practices to understand and master the TDIR workflow. Leverage the latest in security information and event management (SIEM) technologies, optimize your log management, and achieve excellence in incident response.
Elevate your cybersecurity strategy and improve your security team’s efficiency and effectiveness. Download your guide now.
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!











