Exabeam SIEM
Cloud-native SIEM at hyperscale with fast, modern search and powerful correlation, reporting, dashboarding, and case management.
Finally, a SIEM teams will want to use
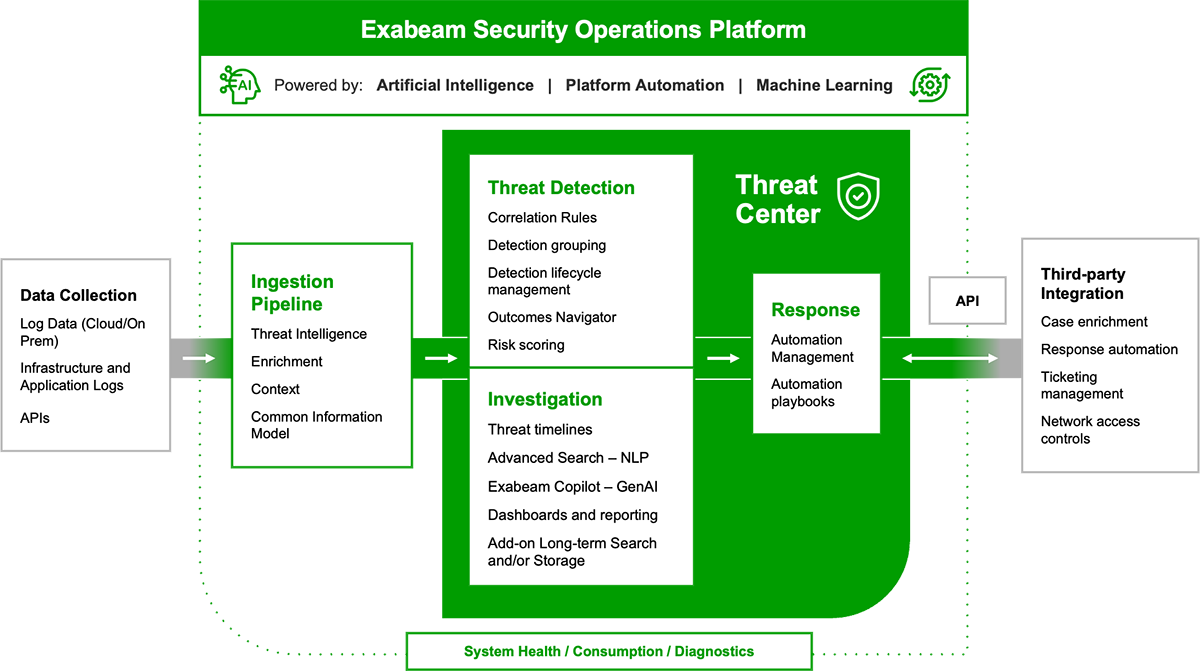
Exabeam extends the cloud-scale capabilities of Exabeam Security Log Management with additional features for threat, detection, investigation, and response (TDIR). Exabeam SIEM includes Threat Center, over 190 pre-built correlation rules, integrated threat intelligence, automation management, and powerful dashboarding capabilities. The solution delivers analysts new speed, processing at over 2 million events per second (EPS) sustained, and natural language search capability for query responses across PB of data in seconds.
Comprehensive log collection
Securely collect data from on-premises or cloud data sources at scale using a single interface. Parse each raw log into a security event, identify named fields, and normalize it using a standard format for accelerated analysis and added security context. A wizard enables custom parser creation from new or templated log sources making it easy to develop, deploy, and manage error-free parsers. Review parser quality against use cases and the MITRE ATT&CKⓇ framework for continuous improvement. Process events at over 2 million per second (EPS) sustained.
- Currently supporting 650+ products from over 340 vendors
- Multiple transport methods: API, agent, syslog, SIEM, data lake
- Over 9,500 pre-built log parsers


Cloud-scale security log management
Security log management on the Exabeam cloud-scale architecture offers end-to-end efficiency to ingest, parse, store, and search data at lightning speed. An essential capability of Exabeam SIEM is our natural language processing enabled Search — a single interface that allows analysts to search using their native language across petabytes of data at speed. And there’s no learning curve; analysts don’t need to learn a proprietary query language. Security Engineers can convert a Search to a Correlation Rule with automatic notifications or a Dashboard visualization in minutes.
Cloud-scale visibility
Drive desired security outcomes to close critical gaps by understanding your data source coverage and configuration. Learn precisely what to do to improve your security posture by seeing recommended information, event streams, and parsing configurations. Finally, there is a powerful and affordable log management solution, purpose-built for security, that your teams will want to use without a massive learning curve.


Advanced correlation capabilities
Turn your searches into powerful threat-hunting rules in one click. Properly designed correlation rules enable you to surface a broad range of behaviors and events. Write, test, publish, and monitor hundreds of custom correlation rules, including defining higher criticality for those that correspond to Threat Intelligence Service-sourced activity.
How it works
Powered by AI, Exabeam SIEM contains the heart of investigation for your teams — Threat Center simplifies security analyst workflows and increases productivity through centralized threat management, pre-built investigative tools, and automation. Threat Center reduces alert fatigue with prioritization, automated evidence collection, and threat timeline creation, providing all analysts with a consistent view of the threat with the ability to add or upload supporting documents, assign cases, and close them out when the investigation is complete. Analysts can save searches for common threats based on ATT&CK framework TTPs or use cases for quick filters.
pre-built log parsers
As it is ingested, data is parsed using over 9,500 pre-built log parsers and enriched using context sources from open source and commercial threat intelligence feeds.
events per second
Rapid log ingestion processing at a sustained rate of over 2M EPS.
pre-built correlation rules
Exabeam SIEM offers over 190 pre-built correlation rules matching some of the most common use cases of malware and compromised credentials.
Exabeam SIEM features
Exabeam SIEM is a breakthrough combination of threat detection, investigation, and response (TDIR) capabilities security operations need in products they will want to use. Exabeam SIEM delivers limitless scale to ingest, parse, store, search, and report on petabytes of data — from everywhere.
Collectors
Collect data from on-premises or cloud data sources from 22 product categories, 292 different vendors, and 549 different products with over 9,500 pre-built log parsers.
Log Stream
Rapid log ingestion processing over 2M events per second using a new CIM and parsing at ingest. A central console enables you to visualize, create, deploy, and monitor parsers within a unified ingestion pipeline for all Exabeam functions.
Common Information Model (CIM)
Exabeam built a CIM to transform raw logs into normalized, security events that are faster and easier to parse, store, and report on.
Search
A simplified search experience with faster natural-language query and instant results over petabyte scale and/or years of data.
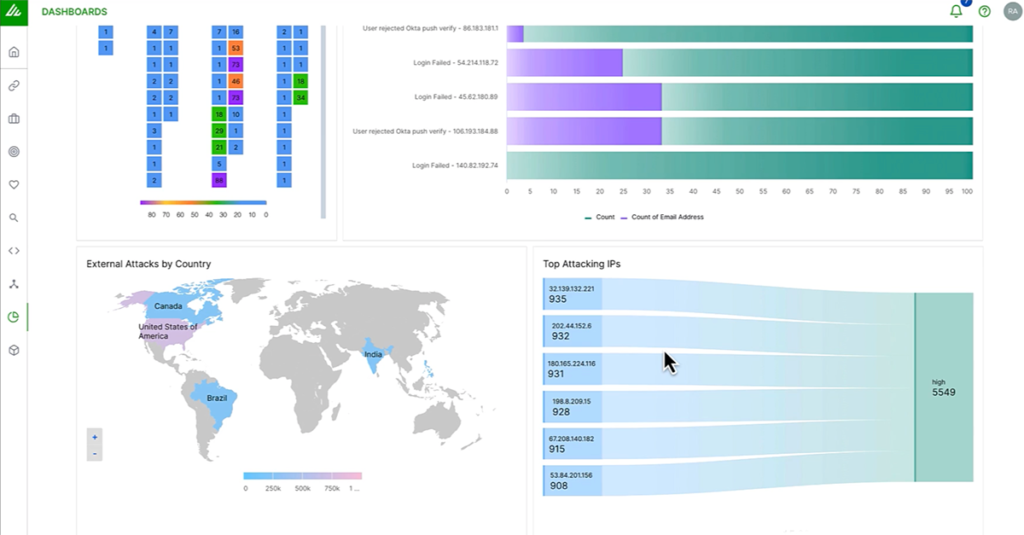
Reporting and Dashboards
Print, export, and view dashboard data with pre-built compliance reports and customize dashboards with 14 different chart types.
Correlation Rules
Write, test, publish, and monitor custom correlation rules for your most critical assets, including defining higher criticality for events that correspond to Threat Intelligence Service-sourced activity.
Pre-built Correlation Rules
Over 190 pre-built correlation rules for detections against the most common threat types such as malware and compromised credentials.
Outcomes Navigator
Outcomes Navigator maps the feeds that come into the platform against the most common security use cases and suggests ways to improve coverage.
Service Health and Consumption
Visualize your service health for every Exabeam service and application, as well as data consumption, while monitoring your connections and sources.
Threat Intelligence Service
Available at no additional cost and refreshed every 24 hours, the Exabeam Threat Intelligence Service ingests commercial and open source feeds, then aggregates, scrubs, and ranks them, using machine learning algorithms to produce a highly accurate stream of IoCs.
Context Enrichment
Exabeam enrichment capabilities provide powerful benefits across several areas of the platform using three methods: threat intelligence, geolocation, and user-host-IP mapping.
MITRE ATT&CK® Coverage
The Exabeam Security Operations Platform uses the ATT&CK framework as a critical lens, spanning all 14 categories, including 199 techniques, and 379 sub-technique in the ATT&CK framework.
Put Your Security Skills to the Test
Challenge yourself and compete with peers in a formidable game of Exabeam CTF. You’ll get a firsthand view into the power of Exabeam behavioral analytics, threat hunting, and automation and their ability to transform your team’s TDIR capabilities.

“After reviewing the market and a number of providers, we chose Exabeam to champion our vision of maximizing what the cloud offers as it relates to our security program. Exabeam’s SaaS-based SIEM means we have no infrastructure or system operations to manage. A cloud-first approach gives our team efficiencies versus operational management tasks; they can now focus on strategic security initiatives that continue to mature our enterprise’s cybersecurity program.
Marc Crudgington
Chief Information Security Officer | Woodforest National Bank

Trusted by organizations
around the world














Frequently Asked Questions
Answer: The Exabeam Security Management Platform is built on Google Cloud Platform (GCP) which has a 99.5% uptime service level agreement (SLA). Uptime is further enhanced with application-level resiliency and redundancy. Lastly, Exabeam has a global team of cloud operations experts who monitor dozens of health signals around the clock to proactively detect and remediate concerns before they become issues.
Customers can access their unique status page at any time to check the availability of Exabeam cloud-delivered services.
Answer: Exabeam SIEM is cloud-native and is delivered from GCP. We leverage GCP to store data securely and leverage many of their data centers across the globe. The exact location and country used in your deployment will be determined at the time of purchase as we continuously keep adding new locations. Customers may choose where their service is hosted from a list of available, global locations.
We use every care to protect our customers’ data. As part of our commitment to making data private, each customer’s data is isolated and not visible to other tenants.
Answer: We use a combination of Collectors, log forwarding, as well as log fetching options directly from other SIEMs like QRadar or Splunk (on-prem or Splunk Cloud) using their APIs, to securely transport customer data to our cloud-native platform. Collectors are virtual machines running Exabeam software on your premises. They are secured behind your firewalls and use SSL to forward encrypted data to Exabeam. Collectors can also bring your data from public clouds such as AWS, Azure, and GCP and SaaS applications, including Microsoft Office 365 and Salesforce.
Explore the many ways Exabeam can work for you
Whether you replace a legacy SIEM, or complement an ineffective SIEM solution by adding UEBA, SOAR, and TDIR content, the modular Exabeam Security Operations Platform can help you achieve security operations success.
- SIEM replacement: Exabeam Fusion
- SIEM augmentation: Exabeam Security Investigation
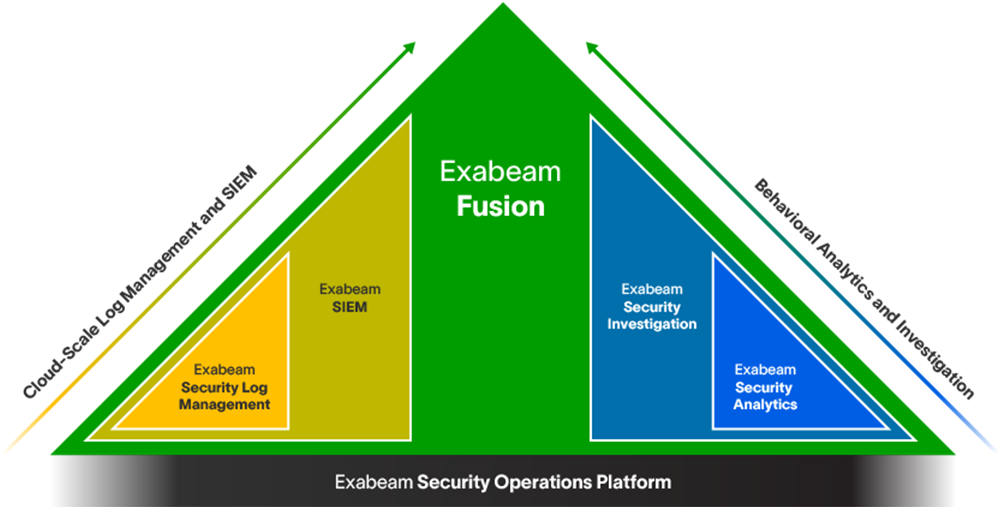
Learn more about the Exabeam Security Operations Platform
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
REPORT
Customers Achieve 245% ROI Using Exabeam Fusion SIEM
In this Forrester Consulting Total Economic Impact™ report, you’ll learn how the Exabeam Fusion SIEM behavioral analytics-driven approach transformed Security Operations by delivering a quantifiable return with ROI as high as 245%, and payback in under six months.
What else can Exabeam do for you?
At Exabeam, we deliver persona-based workflows, purpose-built for security. With support resources, professional services, training opportunities, and business partnerships, Exabeam can usher your organization through deployment and beyond.
See the Exabeam Security Operations Platform in action.
Request a demo of the industry’s most powerful platform for threat detection, investigation, and response (TDIR). See how to:
• Ingest and monitor data at cloud-scale
• Determine abnormal user and device behavior
• Automatically score and profile user activity
• View pre-built incident timelines
• Use playbooks to make the next right decision