
-
- Home
>
-
- Blog
>
-
- InfoSec Trends
Revolution or Evolution? The Old Origins of Today’s New AI
- Jan 10, 2024
- Steve Wilson
- 3 minutes to read
Table of Contents
The first thing that comes to mind for many people when they think of artificial intelligence (AI) is generative AI — those user-friendly applications like ChatGPT and Bard, which made their public debut in 2022 to much fanfare.
Indeed, these sophisticated technologies broke new ground by utilizing large language models (LLMs) to create systems that could work from plain language prompts and directives, adapt to feedback to refine output, and yield brand-new, original text and images.
People may not realize that they’ve been using AI constantly for the past decade — from the autocorrects and suggestions in their Google Docs and Gmail to the virtual assistants in their homes. And that many of the same technologies that make these possible — such as the neural networks that support machine learning (ML) and natural language processing (NLP) — continue to play a fundamental role in new AI.
Generative AI indeed has the potential to be both a blessing and curse for the security operations center (SOC), but to assess its implications properly, it’s essential to place it in context.
What’s different about the latest AI?
Let’s start by asking, “What sets generative AI apart?” It really begins with the LLMs. Like the AI models that precede them, LLMs are trained on massive datasets so that they’re able to recognize patterns and make normative connections amid a vast volume of information, but they differ because of how they’ve been modified.
Data scientists have fine-tuned generative AI models to produce specific results, then further honed them so that they can follow instructions and iterate on outputs. This is made possible by a type of deep learning architecture called a transformer — “GPT” stands for “generative pre-trained transformer” — that leverages a powerful mechanism called “attention” to weight different inputs differently in order to produce the results with the greatest likely relevance.
But while these capabilities are certainly advanced, they should be understood as an alternative way to use AI rather than an upheaval that necessarily renders past approaches obsolete.
The fact is that ML and neural networks — the technologies that underlie LLMs — have been around for a long time. And while the latest innovations in AI may have made programs more responsive to plain language prompts, and more novel and flexible in what they produce, they often serve different purposes than the deep learning technologies already in play, and should be viewed as a valuable complement rather than a competitive replacement.
What else can machine learning do?
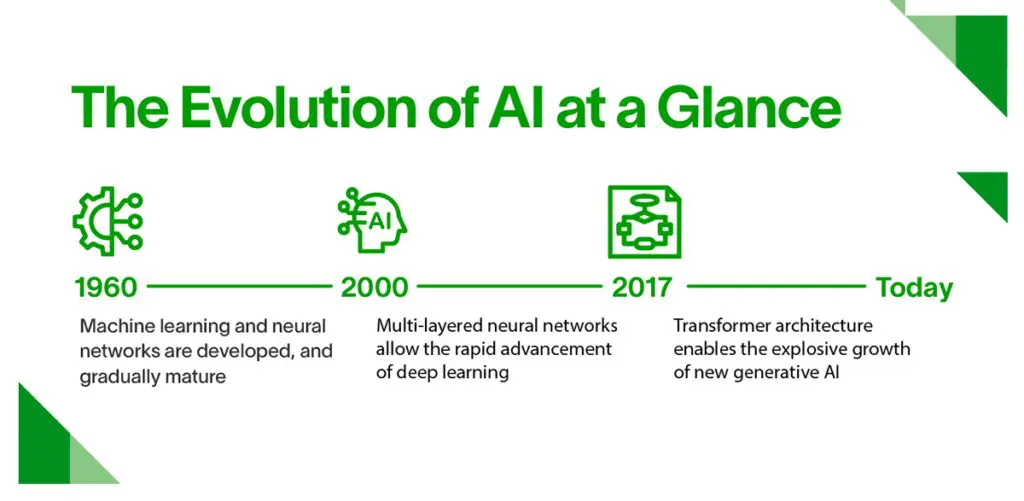
Machine learning was invented back in the 1960s and is driven by algorithms that ingest, interpret, and identify information within large datasets. This led to neural networks, in which layered nodes can analyze unstructured data, and deep learning, which uses multiple neural networks to mimic the human brain and automate machine learning capabilities at speed and scale.
This forms the foundation of the NLP and computer vision advances generative AI brings with it. They’re also responsible for vulnerability identification, network traffic identification, false-positive tuning, and basic forensics behind the best SOC solutions.
For example, the AI-driven Exabeam Security Operations Platform processes some 700 to 900 petabytes of data per month (and growing), and it’s ML that enables the categorization of security events and assigning of risk scores. By modeling normal user behavior, deviations and anomalies can be immediately identified and investigated — and that’s not going away just because generative AI has arrived.
Generative AI is an exciting new evolutionary pathway in the development of AI — one that has seen explosive, even exponential improvements since transformer architectures were introduced in 2017. And while it hasn’t yet eclipsed its ML and deep learning predecessors when it comes to cyber defense processes such as threat detection, investigation, and response (TDIR), new use cases and productivity enhancements are being exposed and introduced seemingly every day.
As a result, security leaders need to understand how to harness old and new AI tools for an effective, dynamic SOC; reading the CISO’s Guide to the AI Opportunity in Security Operations is an excellent place to start.
Read our white paper: CISO’s Guide to the AI Opportunity in Security Operations. This guide is your key to understanding the opportunity AI presents for security operations. In it, we provide:
- Clear AI definitions: We break down different types of AI technologies currently relevant to security operations.
- Positive and negative implications: Learn how AI can impact the SOC, including threat detection, investigation, and response (TDIR).
- Foundational systems and solutions: Gain insights into the technologies laying the groundwork for AI-augmented security operations.

Steve Wilson
Chief AI and Product Officer | Exabeam | Steve Wilson is Chief AI and Product Officer at Exabeam. Wilson leads product strategy, product management, product marketing, and research at Exabeam. He is a leader and innovator in AI, cybersecurity, and cloud computing, with over 20 years of experience leading high-performance teams to build mission-critical enterprise software and high-leverage platforms. Before joining Exabeam, he served as CPO at Contrast Security leading all aspects of product development, including strategy, product management, product marketing, product design, and engineering. Wilson has a proven track record of driving product transformation from on-premises legacy software to subscription-based SaaS business models including at Citrix, accounting for over $1 billion in ARR. He also has experience building software platforms at multi-billion dollar technology companies including Oracle and Sun Microsystems.
More posts by Steve WilsonLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
