
- Home >
- Explainers >
- SIEM Tools
Best SIEM for Threat Detection: Top 5 Options in 2026
- 10 minutes to read
Table of Contents
What Is SIEM?
A SIEM (Security Information and Event Management) system is crucial for threat detection by collecting, analyzing, and correlating vast amounts of security data from across an IT environment (networks, endpoints, clouds, apps). SIEM solutions can identify suspicious activities, insider threats, and complex attacks that individual tools miss, using AI/ML and threat intelligence to find anomalies, prioritize alerts, and enable rapid response.
How SIEM enhances threat detection:
- Centralized data: Gathers logs and events from firewalls, servers, endpoints, cloud services, etc., into one place.
- Correlation: Links seemingly unrelated events to uncover patterns of malicious behavior (e.g., lateral movement, privilege escalation).
- Advanced analytics: Uses AI, machine learning (ML), and behavioral analytics to spot deviations from normal activity, catching sophisticated threats like zero-day exploits or APTs.
- Threat intelligence enrichment: Enriches data with external threat feeds and context (user info, asset criticality) for better detection and risk scoring.
- Real-time monitoring: Provides instant alerts for immediate action, reducing breach impact.
- Automated response: Can trigger automated playbooks to contain threats (e.g., block IPs, isolate devices).
This is part of a series of articles about SIEM tools
How SIEM Enhances Threat Detection
Centralized Data
Centralized data collection is fundamental to SIEM’s ability to detect threats effectively. By gathering logs and security events from multiple sources, such as firewalls, intrusion detection systems, cloud platforms, and endpoints, SIEM creates a consolidated repository of information. This unified view allows security analysts to see relationships and patterns across the organization’s entire infrastructure, eliminating blind spots created by siloed systems.
With all relevant data centralized, cross-system analysis and incident investigation become more efficient. Correlating activities from multiple devices and locations enables identification of complex attack chains that might span network boundaries. This data consolidation supports compliance efforts as well, making it easier to generate reports for regulatory mandates.
Correlation
Correlation is the process through which SIEM systems analyze disparate security events to identify potential threats that individual events alone might not reveal. Using correlation rules, SIEM platforms can link events from different sources (such as an anomalous login from one system followed by unusual file access from another) to flag potential security incidents.
These correlation rules improve signal-to-noise ratios by reducing false positives and surfacing genuinely suspicious behaviors. Effective correlation enables detection of advanced tactics, such as multi-step intrusions or lateral movement, which would be missed if events were analyzed in isolation. SIEM administrators can customize correlation rules to the threat landscape.
Advanced Analytics
SIEM systems leverage analytics, including machine learning and statistical modeling, to enhance threat detection beyond predefined rules. These capabilities allow SIEMs to establish baselines of normal user and system behavior, uncovering subtle deviations that may suggest insider threats, compromised accounts, or novel attack techniques.
Machine learning helps detect unknown threats by identifying anomalies that escape traditional signature-based detection. Integrating analytics within SIEM enables detection of complex attack patterns, such as slow-moving threats or low-and-slow data exfiltration attempts. Security teams benefit from continuous learning algorithms that adjust to new behaviors over time, continually improving the SIEM’s accuracy in flagging real incidents.
Threat Intelligence Enrichment
Threat intelligence enrichment involves augmenting SIEM-collected data with external threat feeds, such as indicators of compromise (IOCs), IP reputation lists, and known malware signatures. This process equips SIEM systems with up-to-date, actionable context that improves event analysis. When an observed event matches intelligence from these feeds, the SIEM can automatically escalate alerts, allowing analysts to prioritize the most credible and dangerous threats.
The integration of external threat intelligence makes detection faster and more accurate, especially for threats that have been identified in the wild but have not yet triggered internal security controls. SIEM platforms often automate enrichment workflows, correlating internal events with global threat data in real time.
Real-Time Monitoring
Real-time monitoring is a defining feature of SIEM platforms. Immediately after events are ingested, SIEM systems scan for signs of possible attacks, compliance violations, or suspicious user actions. By continuously monitoring network, system, and application activity, SIEM can send instant alerts prompting rapid investigation and response, reducing the window of opportunity for adversaries.
This constant vigilance enables identification of threats at their earliest stages, such as credential abuse or abnormal access patterns. Real-time detection empowers organizations to contain and disrupt attacks before they escalate, minimizing the potential for damage. Integration with security orchestration and response tools further accelerates containment and remediation when threats are discovered.
Automated Response
Automated response capabilities allow modern SIEM solutions to execute pre-defined actions when certain threat scenarios are detected. These responses can range from blocking a user account or isolating a device to starting a forensic investigation workflow. By automating containment steps, SIEM systems decrease the time between detection and mitigation, limiting the potential impact of an attack.
Automation also addresses SOC resource constraints, helping security teams keep up with high alert volumes without sacrificing speed or accuracy. Automated playbooks can standardize responses to common incidents, ensuring consistent application of security policies and freeing analysts to focus on more complex threats.
SIEM Use Cases for Proactive Threat Detection
Compromised Credentials and Identity-Based Attacks
SIEM solutions are crucial in detecting compromised credentials and identity-based attacks by analyzing authentication patterns, privilege changes, and access anomalies. For example, a SIEM can flag unusual login activity, such as repeated failed logins, logins from unfamiliar locations, or simultaneous logins across geographies. These anomalies may indicate credential stuffing, brute force attempts, or stolen credentials being used.
Correlating login data with other indicators, such as privilege escalation or unauthorized resource access, increases the confidence of detection. SIEM platforms can integrate with identity and access management (IAM) systems to continuously monitor user account activity and alert on suspicious behavior.
Cloud Control Plane and SaaS Abuse Detections
Modern SIEMs support monitoring of cloud infrastructure and SaaS applications to detect configuration abuses, privilege misuse, and unauthorized API calls. By collecting logs from cloud control planes (like AWS CloudTrail or Azure Activity Logs) and SaaS event streams, SIEM systems can detect suspicious administrative actions, such as the creation of unapproved accounts or changes to access policies.
In hybrid and multi-cloud environments, SIEM correlation helps to uncover activities that might cross cloud or on-premises boundaries. For example, detection of a rare API call in conjunction with unexpected data transfers can indicate abuse of administrative privileges or attempts to exfiltrate sensitive information from cloud resources.
Lateral Movement and Privilege Escalation
Attackers often pivot across systems through lateral movement and privilege escalation after gaining an initial foothold. SIEM platforms can detect these tactics by analyzing east-west traffic, authentication logs, and changes to user permissions. Patterns such as unauthorized remote desktop protocol access or sequences of failed and successful logins to critical servers are strong indicators of lateral movement.
Privilege escalation attempts are identified through correlation of seemingly benign events that, together, represent risk (like a non-administrative account gaining high-level privileges or executing new admin-level commands). SIEM can automate the detection of these behavioral changes, enabling security teams to disrupt attackers before they reach valuable systems.
Insider Threats and Data Exfiltration
Insider threats are difficult to detect because they originate from legitimate accounts. SIEM uses behavior analytics to spot subtle deviations from the norm (such as atypical file access, large-volume data transfers, or unusual working hours) that could signal malicious intent or compromised insiders. Continuous monitoring and correlation of user actions across endpoints and networks help surface potential insider activity.
Data exfiltration attempts, such as uploading sensitive files to unauthorized cloud storage or external FTP services, are tracked through SIEM’s analysis of DNS, proxy, and DLP logs. By correlating access and transfer events, SIEM provides early warnings of illicit data movement so teams can intervene before information leaves the organization’s control.
Ransomware Kill Chain Detection and Disruption
SIEM solutions aid in identifying ransomware activity throughout the attack kill chain. Initial compromise indicators include detection of phishing emails, suspicious file downloads, or the execution of untrusted executables. As the attack progresses, SIEM monitors for malware-related behaviors such as unauthorized process spawning, rapid file encryption, and deletion of backup snapshots.
By correlating these activities in real time, SIEM platforms enable rapid response to stop ransomware before widespread encryption or impact can occur. Automated playbooks can trigger network segmentation, isolate infected endpoints, and initiate disaster recovery plans.
DNS, Proxy, and C2 Beaconing Anomalies
Command-and-control (C2) beaconing detection relies on deep analysis of network logs, DNS queries, and proxy traffic (capabilities native to robust SIEM platforms). Attackers often use regular, low-profile network connections to communicate with external C2 infrastructure. SIEM can baseline normal DNS and web traffic, surfacing unusual, periodic, or rare patterns that suggest C2 activity.
Correlation of DNS anomalies with blocked web requests or outbound connections to known suspicious domains increases detection accuracy. Detecting beaconing early in the kill chain provides an opportunity to sever attacker communications, reduce dwell time, and limit the scope of compromise.
Notable SIEM Solutions for Threat Detection
1. Exabeam
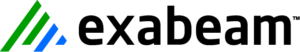
Exabeam offers its New-Scale Security Operations Platform, a cloud-native SIEM meticulously designed to provide comprehensive visibility through advanced behavioral analytics for both human and agentic workers. Moving beyond traditional rules-based approaches, the platform leverages AI to establish and understand the normal behavior of every user and entity—from employees and contractors to AI agents and automated workflows—across an organization’s infrastructure. This behavioral baselining allows Exabeam to identify subtle anomalies and sophisticated threats that would otherwise bypass static, signature-based security tools. The platform aims to reduce the burden on security teams by automating many aspects of the threat detection, investigation, and response (TDIR) workflow.
SIEM features:
- New-Scale Platform: A cloud-native architecture capable of petabyte-scale data ingestion and analysis, supporting hybrid and multi-cloud environments with flexible scalability.
- Behavioral Analytics (UEBA): Utilizes advanced machine learning to establish behavioral baselines for users and entities, enabling the detection of high-risk anomalies, insider threats, and compromised accounts.
- Automated Incident Timelines: Automatically correlates disparate security events into coherent timelines, providing contextual narratives that accelerate investigations and reduce manual effort for analysts.
- Comprehensive Data Collection: Ingests and normalizes data from a broad range of sources, including network devices, endpoints, applications, cloud services, and identity providers.
- Threat Detection and Prioritization: Leverages risk scoring and machine learning to prioritize alerts, directing security teams to the most critical threats and minimizing alert fatigue.
Threat detection features:
- AI-Driven Anomaly Detection: Identifies deviations from established behavioral baselines to detect stealthy threats like lateral movement, privilege escalation, and data exfiltration.
- Automated Response Options: Supports automated or semi-automated response actions to mitigate threats, such as isolating compromised endpoints, revoking user credentials, or initiating password resets for affected accounts.
- Real-time Threat Hunting: Facilitates proactive threat hunting by providing tools to query and analyze historical and real-time data for indicators of compromise or attack.
- Integrated Agent Behavior Analytics (ABA): Extends behavioral analysis to AI agents and other non-human entities, recognizing the unique behavioral patterns and risks associated with these automated workers.
- Contextual Enrichment: Enriches alerts with critical context, including user identity, asset criticality, and threat intelligence, to provide a complete picture for rapid decision-making.
Source: Exabeam
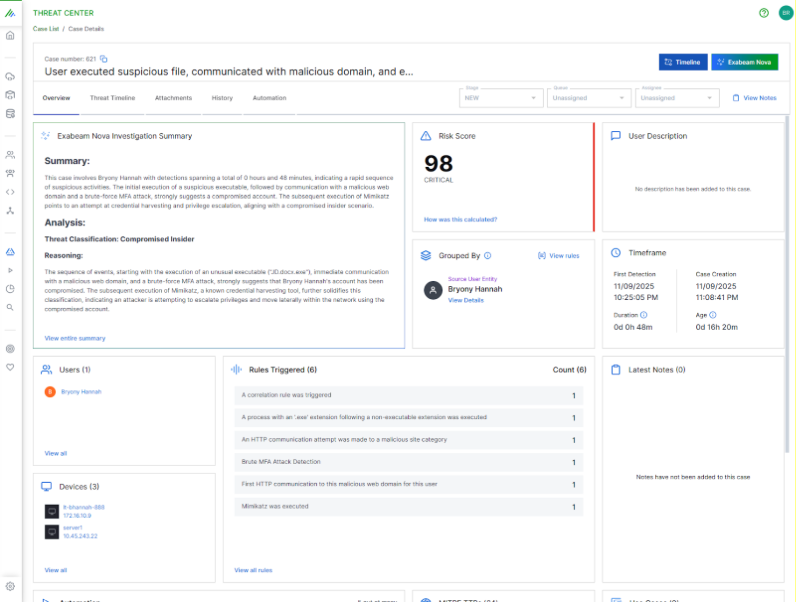
2. Microsoft Sentinel SIEM

Microsoft Sentinel is a cloud-native SIEM solution built on Azure, providing security visibility and threat protection across multi-cloud and hybrid environments. It helps security teams detect, investigate, and respond to threats at scale using analytics, automation, and integrated threat intelligence.
SIEM features:
- Scalable data collection: Ingests data across users, devices, applications, and infrastructure from on-premises and multiple cloud environments using built-in and custom connectors.
- Data normalization: Translates diverse data sources into a consistent format at ingestion or query time using the Advanced Security Information Model (ASIM).
- Visual analytics with workbooks: Offers prebuilt and customizable dashboards for visualizing collected security data across the environment.
- Watchlist integration: Enables correlation of security events with custom watchlists (e.g., sensitive accounts or terminated users) for enhanced detection.
- Tamper-proofing and immutability: Inherits Azure Monitor’s data integrity practices for compliance and audit readiness.
Threat detection features:
- Built-in analytics rules: Groups related alerts into incidents and detects anomalies through customizable rules that reduce false positives.
- MITRE ATT&CK coverage: Maps detected behaviors to MITRE techniques, providing visibility into attacker tactics and improving security posture tracking.
- Threat intelligence integration: Correlates ingested events with external IOCs and threat feeds to enrich alerts and improve detection context.
- Threat hunting tools: Allows proactive investigation using custom queries across historical and live data, based on MITRE-aligned techniques.
- AI-driven incident investigation: Uses graph-based tools to trace entity relationships and understand the full scope of an attack.
- Automation and playbooks: Supports response automation via Azure Logic Apps to trigger actions like ticket creation or device isolation based on incident type.
Source: Microsoft Sentinel
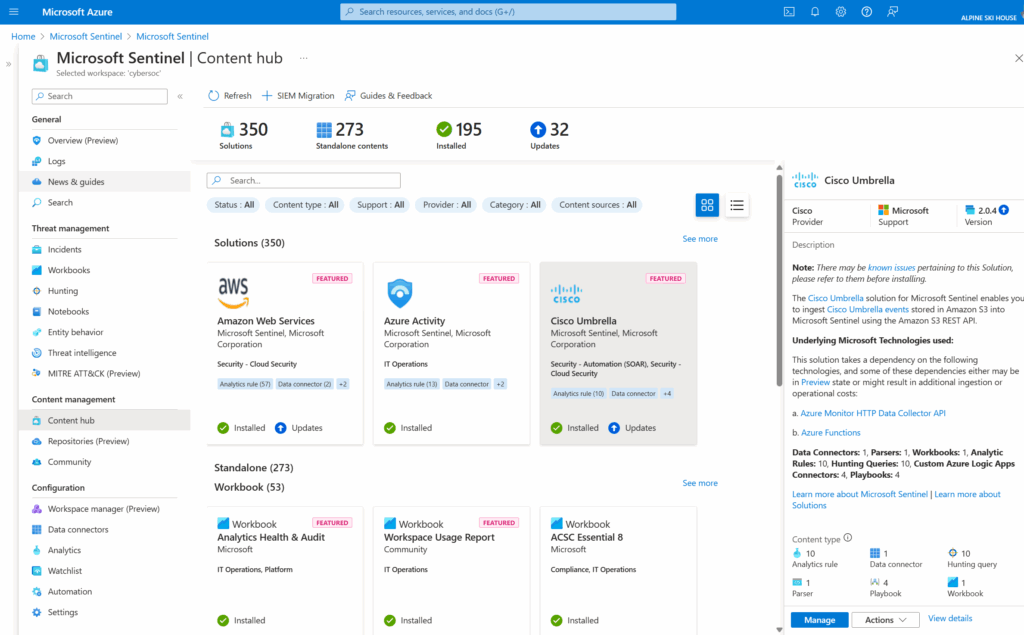
3. Splunk Enterprise Security

Splunk Enterprise Security (ES) is a data-driven SIEM platform to help security teams detect, investigate, and respond to threats. It provides visibility across cloud, on-premises, and hybrid environments, allowing organizations to centralize their security operations and eliminate data silos. It uses AI-driven detection, behavior analytics, and automation.
SIEM features:
- Full-fidelity visibility: Ingests and analyzes data from all domains, clouds, and devices to ensure comprehensive threat detection coverage.
- Unified TDIR platform: Consolidates detection, investigation, and response in a single workspace to reduce tool switching and streamline workflows.
- Detection Studio: Supports the full detection lifecycle, from development to deployment, while mapping detections to the MITRE ATT&CK framework.
- Automation and enrichment: Integrates SOAR and threat intelligence to automate response workflows and enrich alerts with contextual data.
- Risk-based alerting: Prioritizes high-risk events using behavioral context to reduce false positives and improve focus on critical incidents.
Threat detection features:
- UEBA: Applies machine learning and behavior analytics to detect insider threats, zero-day attacks, and account compromise through deviations from baseline activity.
- AI-driven workflows: Supports natural language queries, guided investigations, and automatic report generation to accelerate threat analysis.
- Threat intelligence integration: Provides enriched detection with external threat intelligence, including feeds like Cisco Talos.
- MITRE ATT&CK mapping: Aligns detection coverage with attacker tactics and techniques for visibility into evolving threat behaviors.
- SOC-wide automation: Enables consistent response actions across the SOC with integrated playbooks and orchestration tools.
Source: Splunk Enterprise Security
4. Securonix Unified Defense SIEM

Securonix Unified Defense SIEM is a cloud-native security operations platform that combines SIEM, UEBA, SOAR, and TIP into a single solution for threat detection and response. Using agentic AI, the platform enables organizations to reduce risk, eliminate operational inefficiencies, and deliver measurable security outcomes.
SIEM features:
- Unified architecture: Combines SIEM, UEBA, SOAR, and TIP in one platform to reduce tool sprawl and integration complexity.
- Single data layer: Ingests data once and applies it consistently across detection, investigation, and response workflows.
- Cloud-native performance: Uses a single-tier architecture for faster processing and avoids bottlenecks in data analysis.
- 365-day hot storage: Maintains a full year of always-searchable telemetry to support long-term investigations and compliance.
- Board-ready reporting: Includes prebuilt reporting aligned with regulations such as SEC, GDPR, and DORA to support audit and governance needs.
Threat detection features:
- Agentic AI automation: Modular AI agents automate triage, enrichment, and response while supporting analyst oversight.
- Noise cancellation: Filters out false positives using AI to let analysts focus on credible threats.
- Behavioral analytics: Detects real-time threats through AI-driven analysis of user and entity behavior.
- Threat content-as-a-service: Continuously updated detection rules and analytics from Securonix Threat Labs.
- Compliance mapping: Identifies and explains security issues in the context of regulatory frameworks to support proactive response.
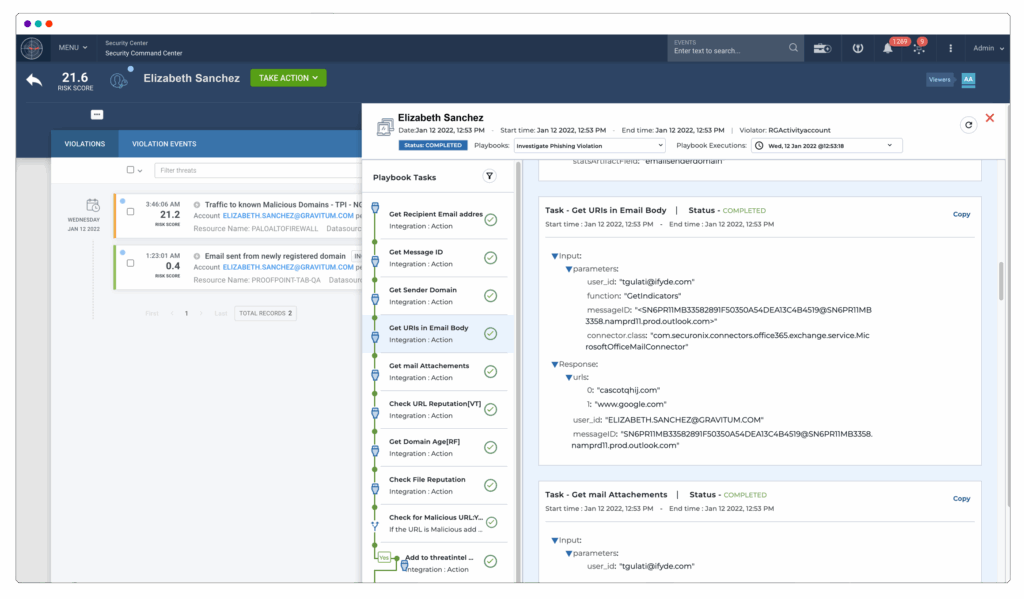
Source: Securonix
5. Sumo Logic Cloud SIEM

Sumo Logic Cloud SIEM is a cloud-native security platform designed to help SOC teams detect, investigate, and respond to threats using behavioral analytics, automation, and log-first intelligence. It unifies SIEM, log management, UEBA, and automation in a single interface, simplifying workflows and accelerating response.
SIEM features:
- Unified interface: Combines SIEM, log analytics, UEBA, and automation in one platform to reduce context switching.
- Cloud-native scalability: Offers multi-tenant elasticity to meet the needs of modern SOCs at any scale.
- Detection-as-Code: Enables teams to manage detection rules in GitHub, supporting version control and reducing rule drift.
- Integrated investigations: Uses natural language search, relationship graphs, and query agents to accelerate root cause analysis.
- MITRE ATT&CK mapping: Provides visibility into detection coverage and gaps through the ATT&CK Coverage Explorer.
Threat detection features:
- Insight Engine: Groups related signals using clustering to generate high-fidelity insights aligned with the MITRE framework.
- User and Entity Behavior Analytics (UEBA): Baselines user behavior in minutes and surfaces anomalies with high precision.
- Threat intelligence enrichment: Aggregates threat intel from multiple trusted sources and custom feeds for contextual alerts.
- Automation and playbooks: Executes prebuilt or custom response actions when insights are triggered to reduce manual effort.
- Summary Agent: Uses AI to generate contextual summaries of alerts, improving triage and communication across teams.
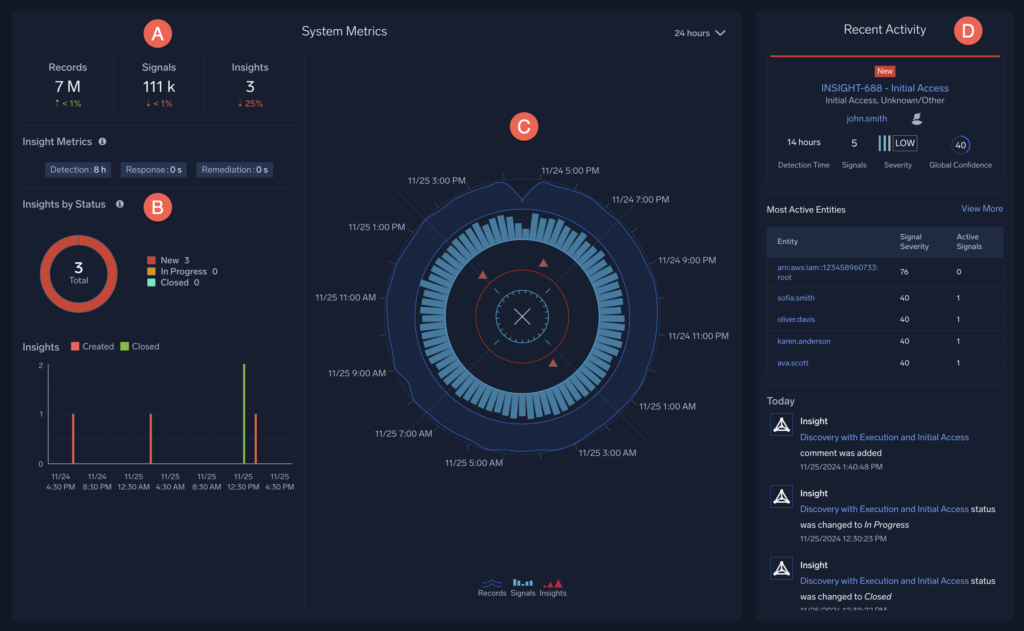
Source: Sumo Logic
Conclusion
SIEM enables organizations to move from reactive to proactive security by centralizing detection and response capabilities. By combining real-time data collection, behavioral analytics, and threat intelligence, SIEM systems help security teams detect attacks earlier, respond faster, and understand incidents more clearly. When properly configured and continuously optimized, SIEM becomes a core component of a modern threat detection strategy, capable of identifying both known and emerging threats across complex IT environments.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.