
- Home >
- Explainers >
- SIEM Tools
Best SIEM Products for IT Security: Top 5 Options in 2026
- 8 minutes to read
Table of Contents
What Is SIEM?
Security information and event management (SIEM) is a category of security solutions that collect, aggregate, and analyze log data from various sources across an organization’s IT environment. SIEM tools centralize event data produced by applications, network devices, servers, and endpoints. They correlate activities from disparate sources, enabling security teams to detect threats and investigate incidents efficiently.
Popular SIEM (Security Information and Event Management) products for IT security include Exabeam, Microsoft Sentinel, and Logpoint. These solutions collect and analyze security logs in real-time to detect threats, automate responses, and help meet compliance by correlating data from firewalls, servers, and cloud services, offering capabilities like advanced analytics, threat intelligence, and incident response.
SIEM solutions use real-time monitoring, analytics, and reporting features to spot suspicious patterns such as unauthorized access attempts or policy violations. Modern SIEM systems also integrate with threat intelligence feeds and leverage machine learning for improved anomaly detection. They provide dashboards and alerts that help organizations prioritize risks and accelerate response efforts.
Benefits of SIEM for IT Security Teams
Improved Detection of Threats
Traditional security tools often miss attacks that blend in with regular network traffic or utilize multiple stages. SIEM platforms can correlate data from many sources and employ behavioral analytics to reveal subtle deviations that indicate a threat. This approach enables detection of tactics like lateral movement, privilege escalation, or zero-day exploits that would otherwise go unnoticed.
By providing a more nuanced understanding of normal versus suspicious activity, SIEM tools help minimize attacker dwell time. These systems can incorporate external intelligence feeds to further enhance detection capabilities. They stay current with emerging indicators of compromise and attack methods, increasing the likelihood of catching threats early.
Faster and More Accurate Incident Response
A major advantage of SIEM solutions is their ability to automate alerting and simplifying investigation workflows. By aggregating and normalizing data in real time, SIEMs reduce the noise typically faced by security analysts, allowing them to focus on true incidents rather than being overwhelmed by false positives.
Automated correlation and enrichment of alerts ensure that relevant contextual information is available during triage, making root cause analysis faster and more precise. Many SIEM platforms integrate with incident response playbooks and orchestration tools. This means that once a threat is detected, predefined remediation steps can be launched automatically or semi-automatically.
Centralized Visibility Across IT Infrastructure
SIEM solutions deliver unified visibility by aggregating logs and events from servers, endpoints, network devices, and cloud services. This holistic view allows security teams to monitor the entire IT landscape from a single interface, reducing blind spots and enabling comprehensive oversight. Centralization also simplifies compliance audits, as all relevant security data can be accessed and reported on from one system.
Real-time dashboards and customizable reports provide immediate insight into ongoing threats, attempted attacks, and overall security posture. This level of visibility not only supports swift decision-making but also aids in capacity planning and resource allocation.
Reduced Workload Through Automation
SIEM platforms automate many routine security tasks such as log collection, data normalization, threat detection, and alerting. This means IT security staff can focus their attention on strategic tasks instead of sifting through vast quantities of raw data. Automation reduces the risk of human error and ensures critical incidents are not overlooked due to high volumes or analyst fatigue.
Advanced SIEMs also support automated incident response actions, such as isolating compromised hosts or blocking malicious URLs. By integrating with other security and network management systems, SIEM can trigger workflows to contain threats quickly.
Enhanced Compliance and Audit Readiness
Many regulations require organizations to maintain detailed logs and demonstrate effective monitoring of sensitive systems. SIEM solutions make it easier to meet these compliance requirements by automating data collection, retention, and reporting. With built-in templates for common standards (such as HIPAA, PCI DSS, or GDPR), SIEMs generate audit trails and reports demonstrating adherence to policies.
This centralization of compliance evidence simplifies audit processes, reducing the manual effort needed to gather documentation. Additionally, SIEM helps identify and alert on policy violations or compliance gaps, allowing for prompt correction.
Notable SIEM Products for IT Security
1. Exabeam
Exabeam offers its New-Scale Security Operations Platform, a cloud-native SIEM designed to provide comprehensive visibility through behavior analytics, advanced threat detection, and automated response capabilities for modern IT environments. The platform focuses on behavioral analytics, leveraging AI to understand normal user and entity behavior across an organization’s infrastructure. This approach allows Exabeam to identify subtle anomalies and sophisticated threats that might bypass traditional, signature-based security tools. It aims to reduce the burden on security teams by automating many aspects of the threat detection, investigation, and response (TDIR) workflow.
Key features include:
Threat Detection and Prioritization: Leverages risk scoring and machine learning to prioritize alerts, helping security teams focus on the most critical threats and reducing alert fatigue.
New-Scale SIEM: A cloud-native platform built for petabyte-scale data ingestion and analysis, supporting hybrid and multicloud environments with elastic scalability.
User and Entity Behavior Analytics (UEBA): Applies advanced machine learning to establish behavioral baselines for all users and entities, detecting high-risk anomalies, insider threats, and compromised accounts.
Automated Investigation Timelines: Automatically stitches together related security events into clear, actionable timelines, providing context for investigations and reducing manual effort.
Automated Response Capabilities: Facilitates automated or semi-automated response actions, such as isolating compromised endpoints, revoking user credentials, or initiating password resets during an attack, often through integrations with security orchestration platforms.
Comprehensive Data Collection: Collects and normalizes data from a wide array of sources, including network devices, endpoints, applications, cloud services, and identity providers.
2. Microsoft Sentinel SIEM

Microsoft Sentinel is a cloud-native SIEM platform that delivers scalable, AI-powered security across hybrid and multicloud environments. It centralizes data collection from users, devices, applications, and infrastructure, providing visibility for security teams. Sentinel leverages built-in analytics, threat intelligence, and automation to detect and respond to threats quickly.
Key features include:
- Cloud-native architecture: Built on Azure, Sentinel scales automatically to handle high-volume data ingestion and analysis across cloud and hybrid environments.
- Data collection: Offers built-in connectors for Microsoft and non-Microsoft services, with support for custom connectors via CEF, Syslog, or REST APIs.
- Data normalization: Translates diverse data sources into a unified format using normalization at both query and ingestion time.
- Threat detection: Uses analytics, MITRE ATT\&CK mappings, and threat intelligence to detect and correlate complex attacks with reduced false positives.
- Interactive investigations: Provides visual graph-based tools to explore incidents and their related entities, making it easier to determine root causes.
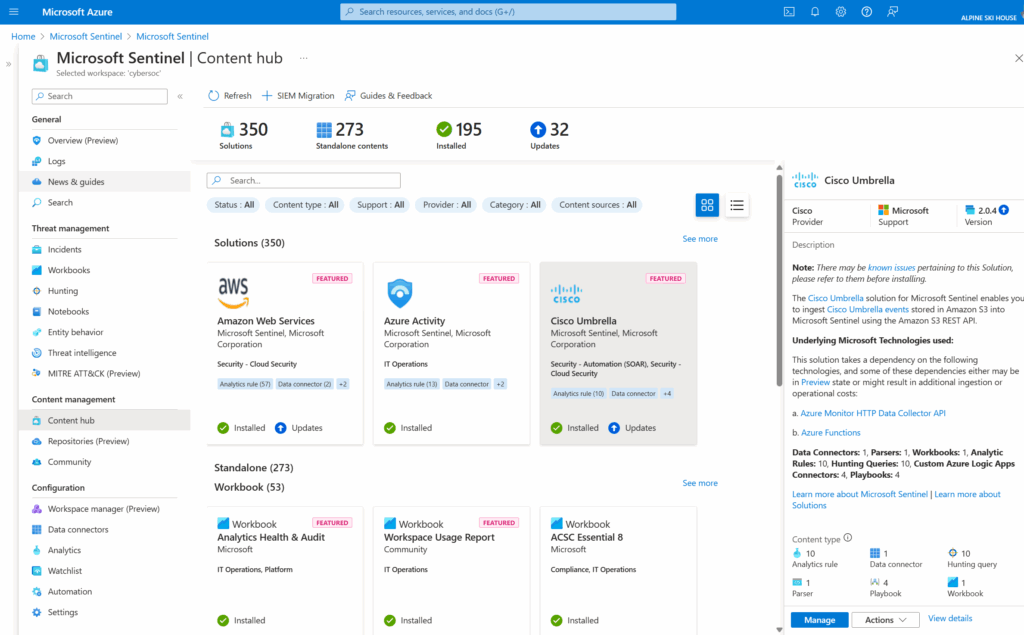
Source: Microsoft Sentinel
3. Logpoint SIEM

Logpoint SIEM is a centralized, analytics-driven solution designed to provide visibility across IT infrastructure while simplifying threat detection, investigation, and compliance. It ingests data from diverse sources (devices, applications, and endpoints) and normalizes it into a common taxonomy for consistent analysis.
Key features include:
- Centralized data monitoring: Collects log and event data from across the infrastructure, giving security teams visibility into activity across devices, applications, and endpoints.
- Data normalization and enrichment: Converts raw logs into a unified format and enriches them with contextual data such as threat intelligence, geography, and user info.
- Threat detection: Translates alerts into a standard format and maps them to the MITRE ATT\&CK framework, enabling faster and more precise threat detection.
- Visual investigation tools: Provides dashboards and visualizations that help analysts understand incidents quickly and make informed decisions.
- Out-of-the-box compliance support: Includes prebuilt dashboards and reports to help meet requirements for GDPR, NIS2, GPG13, and other regulations, along with audit trails for Change tracking.
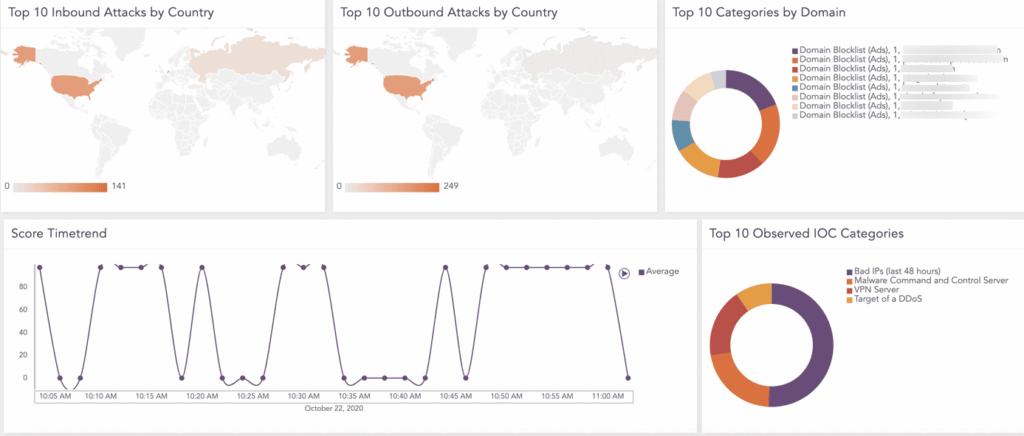
Source: Logpoint
4. Securonix Unified Defense

Securonix Unified Defense is a SIEM platform that merges SIEM, UEBA, SOAR, and TIP into a single, cloud-native solution with agentic AI. Intended to eliminate tool sprawl and reduce operational overhead, it delivers faster threat detection, precise response, and measurable security outcomes.
Key features include:
- Unified cloud-native platform: Combines SIEM, UEBA, SOAR, and TIP in a single architecture, reducing tool sprawl by up to 60% and eliminating integration overhead.
- Agentic AI across the SOC: AI agents automate threat detection, enrichment, triage, and response, while offering human-in-the-loop oversight for explainability and control.
- Noise cancellation: AI filters reduce false positives, allowing analysts to focus on real threats and accelerate response.
- Ingest once, use everywhere: A unified data layer enables consistent use of data across detection, investigation, and response workflows.
- 365 days of always-hot data: Analysts and auditors have immediate access to long-term telemetry for faster investigations and smoother audits.
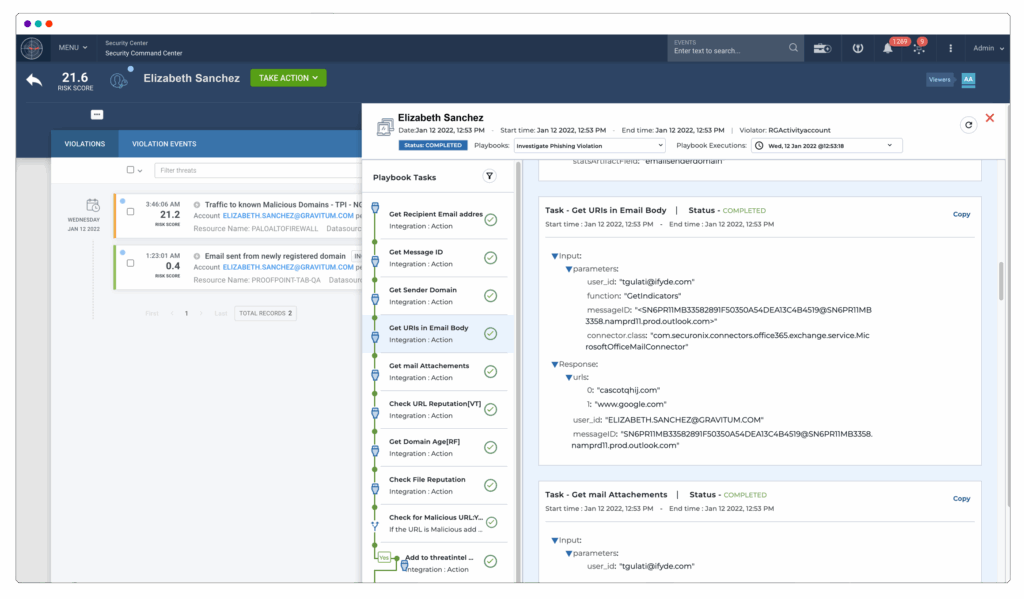
Source: Securonix
5. Splunk Enterprise Security

Splunk Enterprise Security is an AI-driven SIEM platform to help security operations teams detect threats faster, reduce alert fatigue, and unify their threat detection, investigation, and response (TDIR) workflows. It provides full-spectrum visibility across all environments, allowing analysts to detect insider threats, zero-day attacks, and anomalous behavior using machine learning and user and entity behavior analytics (UEBA).
Key features include:
- Unified TDIR platform: Combines detection, investigation, and response in one integrated workspace to simplify SOC operations and eliminate context switching.
- Full-fidelity data visibility: Provides end-to-end visibility across all domains, clouds, and devices, regardless of data location, enabling rapid threat discovery.
- AI-powered alert prioritization: Uses machine learning and AI to cut through noise, reduce alert fatigue, and ensure analysts focus on the highest-risk threats.
- UEBA for insider and zero-day threats: Leverages behavioral analytics to detect compromised accounts and subtle deviations from normal activity that signal advanced threats.
- SOAR and contextual enrichment: Integrates security orchestration and automated enrichment to speed up investigations, reduce manual effort, and enforce consistent response.
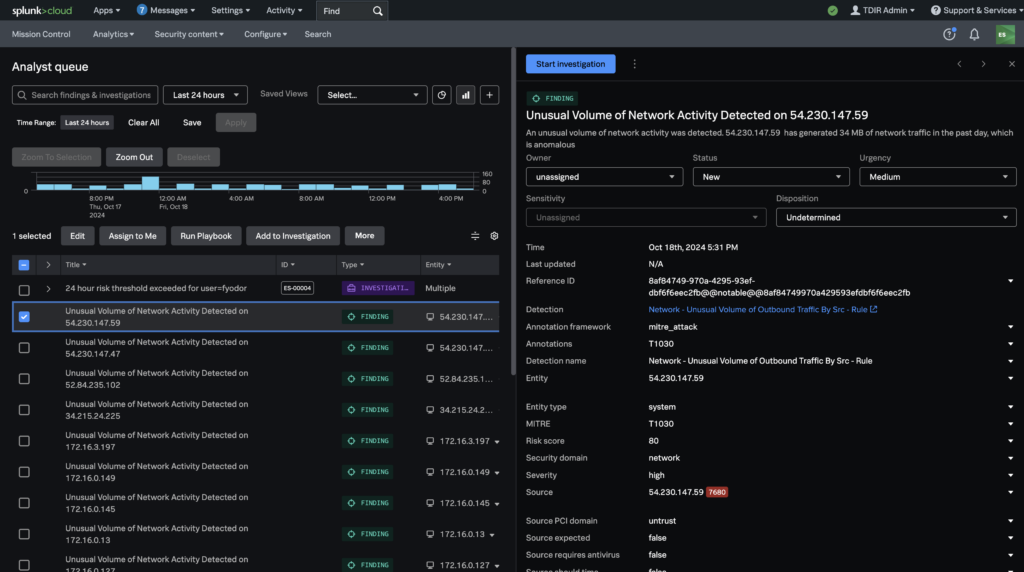
Source: Splunk Enterprise Security
Best Practices for Implementing SIEM in IT Security
Organizations should consider the following practices when working with SIEM tools to improve their IT security.
1. Define Clear Objectives and Use Cases
Successful SIEM deployments begin with a thorough assessment of organizational needs. Clearly defined objectives ensure the SIEM tool is tailored to address specific risks, compliance obligations, and operational requirements. Organizations should identify critical assets, typical threat vectors, and the outcomes they expect from SIEM, such as early threat detection or improved incident response times.
This upfront planning sets the scope for deployment and helps avoid wasted resources spent on unnecessary features. Additionally, mapping out primary use cases, like identifying lateral movement or privileged account misuse, guides the configuration of correlation rules and alerts. Reviewing past security incidents, regulatory demands, and industry best practices can inform relevant scenarios that the SIEM must support.
2. Establish Proper Log Collection and Retention Policies
To gain value from SIEM, organizations need robust log collection policies that cover all critical sources, including firewalls, servers, endpoints, applications, and cloud environments. Capturing comprehensive data ensures accurate threat detection and visibility. It is important to standardize log formats and maintain consistent timestamps to simplify data correlation across systems. Gaps in log collection create blind spots that adversaries may exploit.
Retention policies should be guided by both business needs and regulatory requirements. Many industries mandate keeping logs for a specific period to support forensic investigations and audits. Establishing tiered retention (hot storage for frequently accessed recent logs and cold storage for older data) helps balance performance needs and cost.
3. Regular Tuning and Rule Updates
Threats and IT environments evolve, making it essential to regularly review and adjust SIEM use cases, correlation rules, and alert thresholds. Frequent tuning helps minimize false positives and false negatives, enabling more precise incident detection. Security teams should use feedback from investigations to update rules, improve filters, and refine detection logic to reflect new attack techniques and changes in the business environment.
It’s also important to periodically assess the value of existing rules, retiring obsolete ones and adding new logic to address emerging threats. Incorporating threat intelligence feeds or user behavior analytics can improve detection accuracy.
4. Align SIEM Workflows with Security Operations Center (SOC) Processes
For peak efficiency, SIEM activities should be tightly integrated with existing SOC workflows. This means designing alerting, escalation, and response procedures that mirror how the SOC operates, so relevant data flows directly to analysts when a threat is detected. Consistent processes reduce confusion and ensure incidents are handled efficiently from detection through remediation.
Documentation is critical in this alignment effort. Playbooks outlining how SIEM alerts are triaged, escalated, investigated, and resolved help maintain consistency and accountability. Automated ticketing and case management features can bridge the gap between SIEM and SOC tools, aiding collaboration, tracking, and performance measurement.
5. Continuous Training for IT Security Staff
The effectiveness of any SIEM system depends on the people using it. Continuous training ensures analysts stay up to date with platform features, new detection techniques, and evolving threat landscapes. This includes vendor-provided certification programs, threat intelligence updates, and in-house workshops.
Regular training builds confidence in using advanced SIEM functions, such as building custom correlation rules or integrating threat intelligence feeds. Beyond technical skills, it is important to develop incident response, forensic, and investigative capabilities. Tabletop exercises using real SIEM data prepare teams to work systematically during genuine incidents.
Conclusion
SIEM platforms play a central role in modern cybersecurity by enabling organizations to detect threats early, respond quickly, and maintain full visibility across complex IT environments. By correlating diverse data sources and automating security workflows, SIEM helps reduce operational burden while improving accuracy and response time. When implemented with clear objectives, proper data policies, and ongoing tuning, SIEM strengthens an organization’s security posture and supports compliance efforts, making it a foundational component of enterprise security operations.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.