
- Home >
- Explainers >
- SOAR
Best SOAR Platforms for Enterprises: Top 5 Options in 2026
- 10 minutes to read
Table of Contents
What Are Enterprise SOAR Platforms?
SOAR (Security Orchestration, Automation, and Response) platforms for enterprises unify security tools, automate threat response via playbooks, and centralize incident management, reducing manual work and speeding up resolution.
By consolidating multiple security operations, SOAR platforms allow enterprises to address increasingly complex threats with greater speed and efficiency. They offer features such as case management, playbook automation, and integration with threat intelligence feeds.
Leading enterprise SOAR platforms include:
- Exabeam: Pre-built playbooks simplify process documentation and speed up time-to-resolution.
- Splunk SOAR: Deep integration with Splunk’s SIEM, playbook editor, vast integrations.
- Cortex XSOAR: Focus on threat intelligence integration and playbook automation.
- Microsoft Sentinel: Cloud-native SOAR integrated with Microsoft’s security ecosystem.
- Swimlane: Scalable for large enterprises, focusing on workflow automation.
Benefits of SOAR Platforms for Enterprises
SOAR solutions empower security teams to operate at scale, automate routine work, and establish consistent response procedures across various incident types:
Boost Analyst Productivity
SOAR platforms automate repetitive security tasks, freeing up analysts to focus on high-value investigations and strategic activities. By eliminating the burden of manual data gathering, alert triage, and evidence collection, analysts can spend more time performing in-depth analysis and making informed decisions. Finding and resolving threats becomes a simpler process, reducing fatigue and improving job satisfaction for security professionals.
In addition, SOAR tools help address the growing cybersecurity talent gap by enabling organizations to do more with existing staff. Workflows and playbooks codify best practices, accelerating onboarding of new analysts and reducing the learning curve. This results in greater operational efficiency and allows security teams to handle more incidents without increasing headcount.
Faster Response
Automated workflows in SOAR platforms enable enterprises to react to threats in real time, reducing the mean time to detect (MTTD) and mean time to respond (MTTR). Predefined playbooks can trigger immediate actions such as isolating endpoints, blocking malicious domains, or gathering forensic evidence without human intervention. This rapid response minimizes the window of opportunity for attackers and limits potential damage.
SOAR platforms standardize and accelerate incident escalation, ensuring that critical alerts are prioritized and addressed promptly. By centralizing alert management and automating common investigations, organizations reduce the likelihood of missed alerts or delayed responses, leading to a more resilient security posture.
Improved Consistency
SOAR platforms enforce standardized response procedures across the security operations center (SOC). Automated playbooks ensure that each incident is handled according to documented best practices, eliminating deviations that can lead to mistakes or incomplete resolution. As organizations grow or staff shifts, the consistency provided by SOAR tools helps maintain a high level of quality and repeatability in incident management.
This consistency also aids regulatory compliance and auditability. With every action logged and repeatable, enterprises can demonstrate a clear, systematic response to incidents. This level of detail is invaluable during audits or post-breach investigations, ensuring organizations can show due diligence and process adherence.
Better Visibility
SOAR solutions aggregate data from multiple security tools and sources, providing analysts with a consolidated view of incidents and threats. This centralization makes it easier to correlate events, identify patterns, and understand the full context of an attack. Analysts gain deeper insights into the threat landscape, supporting more informed decision-making and root-cause analysis.
Additionally, robust reporting and dashboard capabilities help security leaders monitor trends, track key performance indicators (KPIs), and identify areas for improvement. This transparency allows organizations to continuously refine their security operations, allocate resources effectively, and communicate risk to business stakeholders.
Key Features of Enterprise SOAR Platforms
Orchestration of Security Tools
Enterprise SOAR platforms connect and manage a wide range of security tools, such as SIEM, EDR, firewalls, vulnerability scanners, and ticketing systems. This orchestration simplifies processes by allowing analysts to execute actions across multiple tools from a single interface. Integration capabilities ensure that data flows seamlessly between different solutions, breaking down operational silos and enhancing overall situational awareness.
By coordinating diverse tools, SOAR platforms reduce manual context switching and ensure that security workflows are consistent and efficient. Automation of repetitive subprocesses (such as blocking malicious IP addresses or fetching logs) helps analysts respond to incidents faster and with fewer errors.
Automated Workflows and Playbooks
SOAR platforms allow organizations to build automated workflows and playbooks, which standardize how common incident types are handled. Playbooks define step-by-step procedures for tasks such as phishing response, malware investigation, and privilege escalation detection. Once triggered, these playbooks execute predefined actions without manual intervention, reducing response time and operational overhead.
Automation not only enforces consistency but also improves efficiency across the SOC. Analysts can focus on complex, high-stakes investigations, while routine tasks are handled automatically. Well-developed playbooks can be refined and iterated over time to reflect lessons learned and industry best practices.
Threat Intelligence Integration
Many SOAR platforms integrate with external and internal threat intelligence sources, enriching incident data with actionable context. Automated enrichment pulls data about indicator reputation, known tactics, and adversary profiles, enabling analysts to make more informed decisions about the severity and relevance of an alert. This context is crucial for prioritizing incidents and selecting appropriate response actions.
Integration with threat intelligence also enables proactive defenses, such as automated blocking of indicators present in current campaigns. SOAR platforms can update denylists, correlate internal alerts with ongoing threats, and trigger proactive hunting activities, improving an organization’s ability to defend against sophisticated attacks and react to emerging threats.
Case and Ticket Management
SOAR platforms often include comprehensive case and ticket management features, which centralize evidence, notes, and task tracking for every incident. Analysts can manage escalations, collaborate on investigations, and document actions within the platform. This eliminates the need for ad hoc communication and ensures that information is accessible, complete, and organized.
Centralized case management simplifies team workflows and can automate the escalation of cases based on severity or compliance requirements. Audit trails are automatically maintained, making it easy to review who took what action and when. This accountability helps organizations improve their incident response processes and meet regulatory obligations.
Customizable Triggers and Actions
A key advantage of SOAR platforms is their ability to support customized triggers and actions. Security teams can define what events should activate automated workflows such as specific alert types, changes in asset status, or the outcome of prior investigations. Flexibility in trigger definitions enables organizations to tailor workflows to their unique risk profile and operational needs.
Custom actions further expand automation by allowing organizations to incorporate custom scripts, APIs, and integrations with proprietary tools. This enables security teams to automate niche workflows not supported out of the box, ensuring that the SOAR solution remains adaptable as environments, tools, and threats change over time.
Integration with Existing SecOps Stack
Compatibility with existing security operations (SecOps) infrastructure is essential for enterprise SOAR adoption. Leading SOAR platforms provide extensive APIs and pre-built connectors for a variety of security and IT tools. Whether integrating with SIEM systems, ticketing platforms, or cloud services, these integrations ensure that organizations can leverage their current investments and avoid disruption during SOAR deployment.
Deep integration with the existing tool stack allows events and actions to be correlated across platforms, enriching investigations and automating complex, cross-system responses. Seamless interoperability makes it quicker to deploy new workflows and respond to evolving threats, maximizing the value of both the SOAR platform and existing security infrastructure.
Notable SOAR Platforms for Enterprise
1. Exabeam
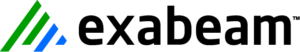
Exabeam offers SOAR capabilities as an integral part of its New-Scale Security Operations Platform, enhancing security operations with intelligent automation driven by its leading User and Entity Behavior Analytics (UEBA). Exabeam’s approach to SOAR leverages deep behavioral context and risk-based scoring to automate incident response workflows, streamline investigations, and reduce manual effort for enterprise security teams.
Key features include:
- AI-driven automation workflows: Automates repetitive security tasks and response actions based on behavioral context and risk scores, moving beyond simple rule-based automation.
- Behavioral context for playbooks: Enriches playbooks with UEBA-driven insights, ensuring automated responses are highly relevant and accurate to the specific user or entity behavior.
- Integrated incident management: Centralizes case management, evidence collection, and task assignment within a single platform for streamlined investigations and collaboration.
- Risk-based prioritization and response: Prioritizes high-fidelity alerts based on dynamically calculated risk scores, triggering automated actions or escalating incidents efficiently.
- Extensive security ecosystem integration: Connects with a wide range of security tools and IT systems, orchestrating actions across firewalls, EDR, identity platforms, and more.
- Accelerated investigation timelines: Provides automated timelines and rich contextual data for every incident, significantly reducing mean time to investigate and respond.
Source: Exabeam Threat Center
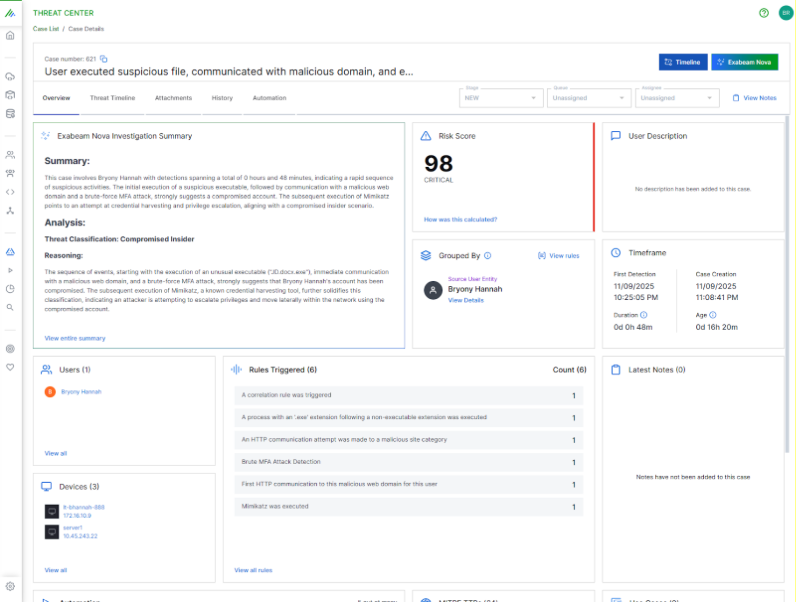
2. Splunk SOAR

Splunk SOAR is a security orchestration, automation, and response platform to help security teams respond faster and more consistently to threats. It integrates with a range of tools across the security stack, enabling teams to automate workflows, centralize incident data, and reduce manual effort.
General features include:
- Prebuilt automated playbooks: Includes a broad set of predefined playbooks aligned with frameworks like MITRE ATT\&CK and D3FEND, allowing teams to automate common tasks such as malware triage, phishing response, and user access reviews.
- Visual playbook editor: Enables both technical and non-technical users to build automation workflows using a drag-and-drop interface with modular code blocks, supporting both simple actions and complex multi-step processes.
- Extensive app integration: Connects with over 300 third-party tools and supports over 2,800 automated actions, allowing orchestration across SIEM, EDR, firewalls, threat intel platforms, and IT service management tools.
- Built-in threat intelligence: Enriches alerts using internal and external threat data, with research-backed insights from the Splunk Threat Research Team to support informed decision-making and faster triage.
- Alert and data consolidation: Aggregates data from across tools into a centralized view, helping analysts identify high-priority threats, reduce alert fatigue, and simplify investigation workflows.
Enterprise features include:
- Integration with Splunk Enterprise Security (ES): Provides native integration with Splunk ES to deliver unified SecOps workflows, enabling teams to investigate, automate, and respond within a single operational environment.
- Customizable and scalable playbooks: Supports custom logic, branching, and reusable components, allowing organizations to tailor playbooks to their specific environments and scale automation across diverse use cases.
- Case management: Centralizes incident documentation, task assignments, evidence, and analyst notes within the platform, ensuring a structured and collaborative response process with audit trails.
- Investigation panel with prioritization: Offers a dedicated interface for reviewing incident context, evaluating threat indicators, and deciding on next steps, enabling quicker decisions based on enriched, centralized data.
- Flexible deployment options: Supports deployment in cloud, on-premises, or hybrid environments, giving enterprises the ability to choose the architecture that aligns with their operational and regulatory needs.
Source: Splunk SOAR
3. Cortex XSOAR
Cortex XSOAR is a security orchestration, automation, and response platform to help SOC teams move to an automation-first approach. It reduces manual workloads, centralizes incident response processes, and improves collaboration across teams. It integrates threat intelligence, case management, and playbook-driven automation into one platform.
General features include:
- Automation of manual tasks: Automates repetitive processes like alert triage, data enrichment, and indicator correlation, allowing analysts to focus on high-value investigation and decision-making.
- Visual playbook editor: Includes a code-free interface to build and customize playbooks using thousands of prebuilt security actions. Playbooks can automate response workflows, from detection to remediation.
- Integrated war room: Provides a collaborative space where analysts can manage incidents, access contextual data, coordinate actions, and document decisions for post-incident analysis.
- Threat intelligence integration: Centralizes threat intel with incident data and indicators, allowing analysts to act on enriched context and better prioritize response actions.
- Alert noise reduction: Helps reduce false positives and surface high-priority incidents through automated triage, correlation, and context-aware filtering of alerts.
Enterprise features include:
- Extensive integration ecosystem: Includes over 900 prebuilt integrations and automation packs covering a range of tools, enabling seamless orchestration across SIEM, EDR, ticketing systems, and threat intel feeds.
- Customizable playbooks at scale: Supports thousands of security actions that can be tailored to enterprise-specific use cases, enabling organizations to automate both simple tasks and multi-stage workflows.
- Centralized case management: Combines ticketing, task tracking, notes, and evidence management into a single platform, supporting structured investigations with auditability.
- Reduced remediation and investigation time: Enables significant performance improvements, including up to 90% reduction in remediation time and 89% faster investigations, based on aggregated customer use cases.
- Support for large-scale deployments: Designed to meet the needs of large public and private sector organizations, with features that allow SOCs to scale automation equivalent to adding multiple analysts.
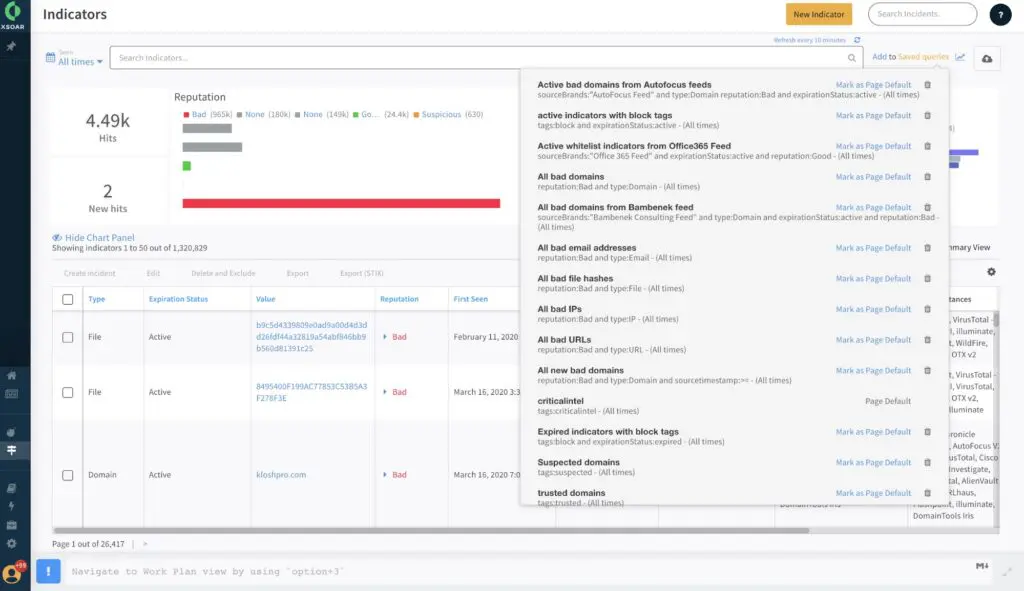
Source: Cortex XSOAR
4. Microsoft Sentinel SOAR

Microsoft Sentinel combines SIEM and SOAR capabilities into a unified, cloud-native security platform for complex, multicloud environments. It uses AI-driven detection, automation, and orchestration to reduce response time, improve analyst efficiency, and support proactive defense.
General features include:
- Integrated SOAR capabilities in a unified platform: Built into Microsoft Sentinel, SOAR capabilities are natively integrated with detection, investigation, and hunting features, reducing the need for third-party tools and providing a single view across the SOC.
- Automation with Azure Logic Apps: Uses Azure Logic Apps as the foundation for building automated workflows. Playbooks built on Logic Apps can automate response actions across services like Microsoft Defender, Azure AD, ServiceNow, Jira, and Slack.
- Prebuilt playbook templates: Includes a large library of ready-to-deploy playbook templates for common incident types such as ransomware, phishing, and privilege escalation. These playbooks accelerate automation adoption and reduce implementation time.
- Managed and custom connectors: Offers hundreds of managed connectors for Microsoft and non-Microsoft services. For unsupported systems, custom connectors can be built to define triggers and actions, extending automation to virtually any endpoint or service.
- Security graph and contextual awareness: Converts telemetry into a connected security graph, allowing playbooks to use context from across users, devices, and cloud resources to make informed decisions and prioritize actions.
Enterprise features include:
- Multicloud and multiplatform coverage: Supports automation across Azure, AWS, GCP, Microsoft 365, on-prem systems, and third-party SaaS applications, enabling consistent response across heterogeneous environments.
- Customizable and scalable playbook automation: Enterprises can build tailored playbooks that reflect their policies, processes, and risk models. Logic Apps supports complex conditional logic, looping, error handling, and parallel processing.
- Tight integration with Microsoft ecosystem: Deeply integrated with Microsoft Defender, Intune, Purview, Entra, and other security tools, allowing automation across the Microsoft security stack.
- Security store and GitHub solutions repository: Access hundreds of automation solutions, connectors, and playbooks from the Microsoft Security Store and GitHub, enabling rapid deployment and reuse of community-developed content.
- Governance and access control: Built on Azure, Sentinel SOAR inherits enterprise-grade identity, access management, and role-based access control (RBAC) to ensure secure and compliant automation workflows.
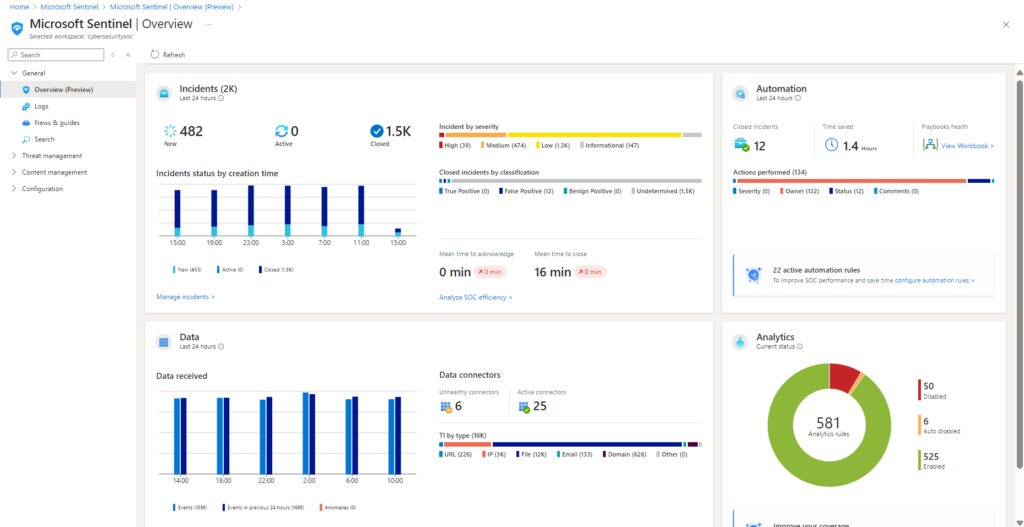
Source: Microsoft Sentinel
5. Swimlane

Swimlane is a next-generation SOAR platform for the demands of security operations. Instead of relying on rigid, legacy architectures, Swimlane combines agentic AI, no-code automation, and scalable orchestration to help security teams operate faster and more effectively. It delivers automation that integrates with any tool and supports customizable case management.
General features include:
- No-code to full-code playbook builder: Offers flexible playbook creation with no-code, low-code, and full-code options. Security teams can build automation workflows with drag-and-drop interfaces or custom code, depending on their needs and expertise.
- Agentic AI capabilities: Includes a private Swimlane LLM that assists with playbook building, case management, and report generation. AI-driven tools enable natural language inputs and automated analysis for faster decision-making.
- Unlimited integrations on demand: Unlike platforms that rely only on static, prebuilt integrations, Swimlane supports dynamic, continuously maintained integrations that allow teams to connect to any API-driven system.
- Customizable case management: Provides configurable case management features with 72 record fields, allowing organizations to define and track incident data exactly how they need. AI enhances workflows with smart routing, auto-prioritization, and contextual suggestions.
- Dashboards and reporting: Users can build visual dashboards tailored to their role or function and generate reports with AI-powered summaries and multilingual translation support, reducing the time required for executive communication and audit preparation.
- Cloud-native architecture: Swimlane is built for cloud deployment but also supports on-premises and air-gapped environments, offering flexibility for enterprises with strict data residency or network isolation requirements.
Enterprise features include:
- High-performance automation at scale: Swimlane executes up to 25 million automated actions per customer per day. This performance allows organizations to scale automation without performance bottlenecks.
- AI-driven case and workflow management: Uses agents to improve each stage of the response lifecycle, from triage to closure. AI supports analysts with summaries, alert deduplication, and automated playbook recommendations.
- Self-service reporting and auditability: Enables users to generate and manage reports without developer intervention. AI enhances report generation with context-rich summaries and translation, simplifying compliance and stakeholder communication.
- On-demand integrations: Swimlane’s architecture supports continuous integration updates and customization. Security teams can connect with virtually any tool in their environment, regardless of vendor or API constraints.
- Flexible deployment options: Supports diverse infrastructure needs with deployment options in public cloud, private cloud, on-premises, and air-gapped environments.
Conclusion
SOAR platforms have become essential for enterprise security operations, enabling faster, more consistent, and more efficient incident response. By integrating disparate tools, automating repetitive tasks, and standardizing response workflows, SOAR helps reduce operational overhead while improving detection and mitigation speed. These platforms empower SOC teams to scale their efforts, maintain audit-ready documentation, and adapt to evolving threats with flexibility and precision. As threats grow in complexity, SOAR provides the coordination and automation needed to maintain resilience and manage cyber risk at enterprise scale.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
-
 Blog
Blog
What’s New in New-Scale April 2026: Securing the Agentic Enterprise With Behavioral Analytics
- Show More

