A Five-Stage Guide to Incident Response For Modern Organizations
Guide
How preparation, detection, containment, response, and recovery reduce disruption
This guide explains how a five-stage incident response plan helps organizations prepare for, detect, respond to, and recover from security incidents.
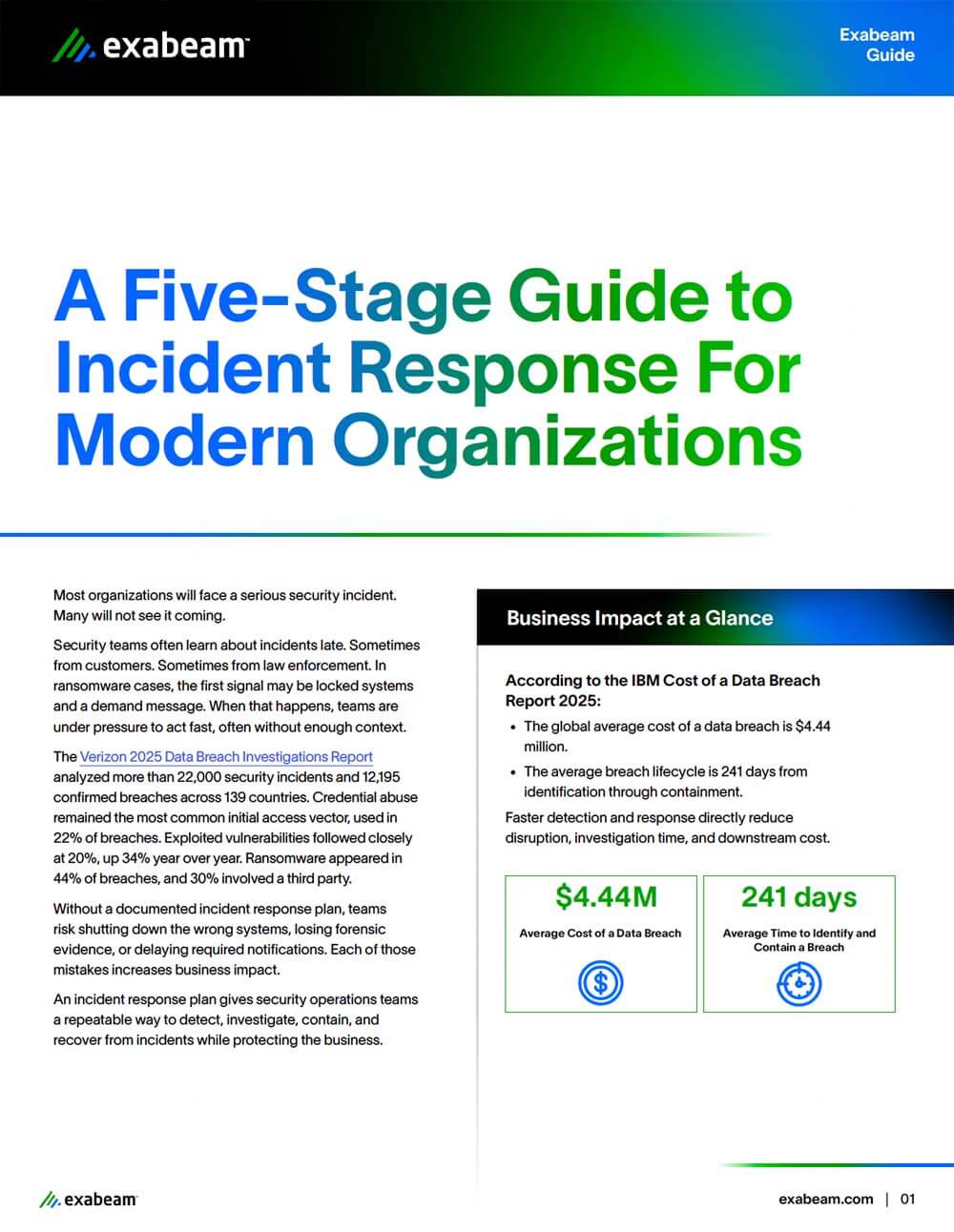
Security incidents often begin with credential misuse or exploited vulnerabilities and unfold over weeks or months. Research shows that unclear response processes and delayed detection increase investigation time, operational disruption, and overall incident impact.
This guide breaks incident response into five stages and explains the role each plays in limiting disruption and recovery effort. It connects real breach and cost data to practical planning decisions security teams can apply before an incident occurs.
Key Questions This Guide Helps You Answer
- What are the five stages of an effective incident response plan?
- How do incidents typically begin and progress across those stages?
- Why does preparation affect investigation and recovery effort?
- How does delayed detection increase incident impact?
- What should teams review and update after an incident?
How Exabeam Helps Security Operations Teams Apply These Findings
Recent reports show that many incidents begin with identity misuse or abnormal system behavior.
Exabeam helps security operations teams apply these insights by focusing on how users, service accounts, and automated agents behave over time. Behavioral analytics establishes baselines and surfaces deviations tied to credential misuse, unusual access patterns, and lateral movement. This approach extends to non‑human identities, including AI agents that authenticate and act within the environment, giving teams broader visibility and more efficient investigation workflows.
Download the guide to understand the five stages of incident response and how each stage reduces disruption and recovery effort.
Get the Guide: A Five-Stage Guide to Incident Response For Modern Organizations
Complete the form below and submit to download this resource.