Five Ways CISOs Can Communicate Cyber Risk and Protect the Business
Guide
A framework for explaining cyber risk in business terms and aligning security operations with organizational priorities
This guide outlines five ways CISOs can communicate cyber risk by connecting identity‑driven activity to business impact.
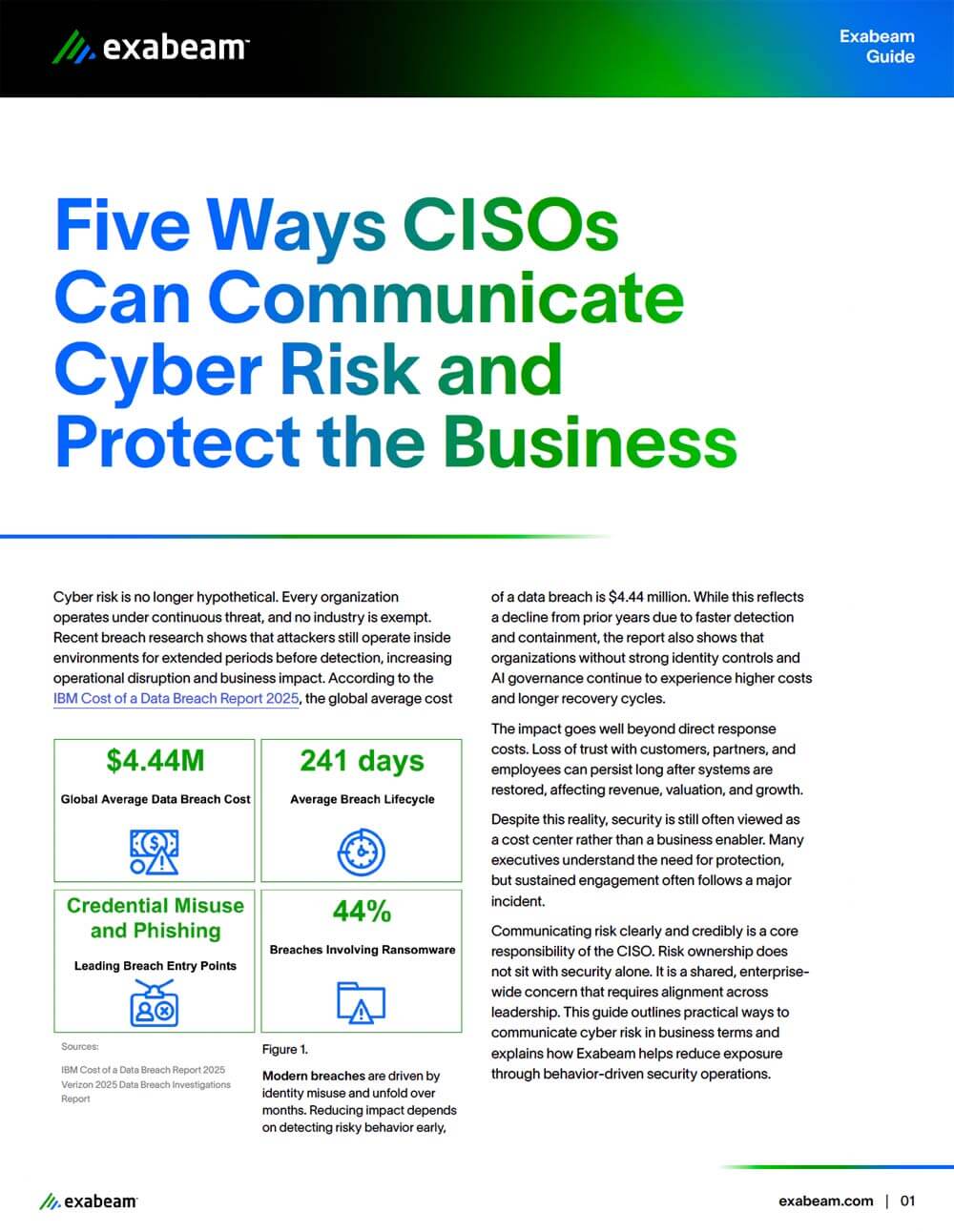
Cyber risk discussions often stall when security teams rely on technical detail instead of business outcomes. Long detection timelines, identity misuse, and unclear ownership make it difficult for leaders to understand exposure and act early.
This guide provides a structured approach for framing cyber risk in terms executives understand. Through five focused practices, it helps CISOs explain threat exposure, align stakeholders, and show how behavior‑based detection reduces business impact.
Key Questions This Guide Helps You Answer
- How can CISOs explain cyber risk without relying on technical detail?
- Why does identity misuse drive many high‑impact security incidents?
- How do attacker behaviors translate into operational and financial impact?
- What role does early detection play in limiting business disruption?
- How can security operations align more closely with executive priorities?
How Does Exabeam Enable the Communication of Behavior‑Driven Risk?
Exabeam applies behavior intelligence and dynamic risk scoring to help security operations teams understand how identities behave over time. By focusing on behavior rather than alerts alone, teams gain clearer insight into risk, investigation priorities, and potential business impact.
Download the guide to learn five ways to communicate cyber risk and align security operations with the business.
Get the Guide: Five Ways CISOs Can Communicate Cyber Risk and Protect the Business
Complete the form below and submit to download this resource.