
-
- Home
>
-
- Blog
>
-
- InfoSec Trends
Exabeamers Make Cybersecurity Predictions for 2023
- Dec 15, 2022
- Jeannie Warner
- 9 minutes to read
Table of Contents
Winter isn’t just coming — it’s already here
Many companies avoided the Christmas rush by starting their layoffs in November. Other industries are enjoying a boom year of record profits, driven by removing or reducing travel restrictions, higher prices at the pump, and new travel tickets. Internationally, trade wars and real wars alike are waging, impacting every organization from labor and logistics through resource challenges, supply chain difficulties, and nation-state activity. There are opportunities and pitfalls alike for the security professional.
We polled Exabeam experts on both sides of the Atlantic, and gathered their insights to get a global view of their security and corporate organizational predictions for 2023.
Tyler Farrar, Chief Information Security Officer (United States)
Nation-state attacks/geopolitical matters

Nation-state actors will continue cyber operations in 2023; whether these attacks increase, decrease, or stay the same ultimately depends upon the strategic objectives of each campaign. Based on the current geopolitical climate, I think we can expect these cyberattacks to increase across the major players. For example, Russia’s failure in Ukraine exposed its weaknesses to the world, but its attacks are likely to continue in that country, including operational disruption, cyberespionage, and disinformation campaigns. It would be unsurprising for the attacks to expand beyond Ukraine too, as Russia’s leader attempts to prove Russia is not weak.
Likewise, cyberespionage is a key tactic in China’s strategy for global influence and territorial supremacy, and I think we can expect these operations to increase, particularly across private-sector companies. In 2023, state policies will directly influence cybercriminal and hacktivist communities to obfuscate sources and methods, increasingly blurring the lines between nation-states, cybercriminals, and hacktivists. Cybersecurity teams would be wise to remain flexible with respect to threat actor attribution.
Impact of economics on security
The economic downturn, in particular inflation, has had and will continue to have a significant impact on security spending, likely forcing reductions and leveling impacts to organizations and to threat actor behavior. The key to defense for these organizations is doubling down on cyber talent and security tools. Meanwhile, security organizations should aim to consolidate legacy technology platforms — decreasing redundant tooling, in addition to controlling cloud spend — to manage high operational costs and complex integrations.
I think this is a good time to remind organizations that zero trust is not a tool, but rather a framework used to secure data in a modern digital enterprise. Zero trust is not overhyped, despite some opinions to the contrary — it has become a critical step towards mitigating cyber risk, detecting malicious behavior, and responding to security incidents. By requiring users and devices to be authenticated, authorized, and continuously monitored for a “trusted” security posture before access is granted, zero trust can contain threats and limit business impacts when a breach does occur.
Credential-based attacks and evolving threats
We’ve seen the classic cat-and-mouse game before: as credential-based attacks evolve, so do cyberdefenses. Threat actors will continue to leverage tried and true methods like social engineering, initial access brokers, and information stealer tools to carry out their objectives. Where multifactor authentication stands in the way of compromising an account with stolen credentials, we can expect cyberthreat actors to implement new techniques to bypass this particular layer of defense. I think this will lead to an expansion of passwordless authentication solutions, to combat the attackers.
We can also expect to see more malicious attacks, as anyone can play this game. A broader set of threat actors will join in to conduct cyber operations in 2023. They have financial motivation and government mandates to justify their cause, not to mention bragging rights that increasingly attract a younger group of threat actors.
Protecting brand as much as infrastructure
During the past year, we witnessed several high-profile breaches, where organizations suffered severe brand damage. This resulted in a shift from data recovery to reputation management when faced with a ransom. I expect to see threat actors shift their strategies to exploit this fear through extortion vs. ransomware in the year ahead.
Further, threat actors will continue to take advantage of weaknesses in the software supply chain, which will become the number one threat vector in 2023. Organizations should create a vendor risk management plan, thoroughly vet third-parties and require accountability, to remain vigilant and align to cybersecurity best practices. This is critical too, as cyber insurance claims have exploded. We can expect to see insurance companies lowering their risk appetite and reducing client coverage in 2023. If your organization is in the market for a policy, expect to pay a hefty premium, or face a rigorous review of the organization’s security posture, as insurance companies increase their due diligence to avoid liability.
5 continuing security channel/partner trends
I see five trends that I believe will continue in the cybersecurity channel landscape:
- In terms of the cyber landscape and portfolio decisions at resellers, MSSPs and GSI partners, I believe we will continue to see a move towards vendor technologies that can be open and integrated easily into a tech stack. This is borne out of the fact that the SOC and security practices as a whole have a wealth of tools, some that integrate well and others that do a specific task that others maybe don’t. In order to get a holistic view of all of those tools and their outputs, there needs to be interoperability and visibility at a platform/SOC level. It is very clear from the types of high-profile attacks and breaches we have seen that context to alerts and behaviors is needed to get a complete picture and make faster decisions. Open integration is key.
- Another trend I see playing out is the need to embrace cloud scale for both storage and compute power to combat the ever-increasing amount of security data that organizations generate. Each tool and user in an environment generates significantly more data than before and for organizations to store that and make sense of it, they need cloud-scale platforms that use algorithms and machine learning to identify trends or anomalies. It is simply not possible for customers or partners to throw enough human power at the problem in order to solve it. So, the use of technology at cloud scale will help bridge the gap between the ever-increasing amounts of data, the complexity of attacks, and the well-documented cybersecurity skills gap.
- The two previous trends will lead to the continuation of my third prediction. The continued rise of XaaS delivered from partners and vendors. A classic example of this is the rise of Detect and Respond (or MDR) services. These are where a partner (or some vendors) will blend technology and people to deliver an outcome to the customer. Essentially, the customer is unaware or doesn’t care about the underlying technology, but they have the provider contracted to deliver outcomes based on certain agreed KPIs. In the MDR example, that is metrics like Mean Time to Respond (MTTR) or simply the number of incidents investigated in a time period. While these metrics are important, I do see customers becoming more savvy now and moving to business outcomes rather than metrics. This will challenge MSSPs and Service Providers to be more innovative and business focused on how they report and articulate value in their services.
- My fourth prediction is that I see the continued decline of product margins and the need to drive value- add services to replace this. With many vendors delivering SaaS applications and tools built on hyperscale platforms, we will see a rise in the adoption of direct-to-customer marketplaces such as AWS, Azure, and GCP. This has been talked about for a while, and I believe for customers who have contracted committed spends with the hyperscalers, this becomes a really attractive procurement vehicle. With complex technology like SIEM and other enterprise solutions, this will not remove vendor/partner selling effort and, as such, the margins charged for fulfillment through these routes are low. For those of us who understand partner economics, this will be a concerning trend to ensure our value-driven partners can still make money and deliver value to both customers and vendors in this new world. This leads me to my last prediction:
- Vendor programs have to evolve and will continue to do so in the face of the above pressures. This low margin will look great for software providers, but partners cannot run an effective business with loyalty to a software provider to then lose out. As vendors, in particular partner focussed sellers within vendors, we must work hard to articulate the complete value of a partner ecosystem and build programs to allow partners to stay in the chain, be able to deliver their value, and ultimately make money for their business while keeping customers happy and successful.
With all of that playing out, it will be an interesting year in the partner community!
Steve Moore, Chief Security Strategist (United States)
Credentials, geopolitics, and criminal group takedowns

The most significant observable trend to note as we move into 2023 is the increased use of credentials in cyberattacks for both initial and persistent access. Currently, more than half of all attacks happen through stolen credentials. This number will increase for initial access and remain higher for persistence. Adversaries are experiencing continued success without using malware to gain access and sign-in. From there, they can use internal credentials and tools against the defender.
Additionally, with geopolitical changes in the world, we will see an uptick in individual businesses falling victim to nation-state attacks. As information and attack techniques are shared, we can expect the lines to blur between espionage and criminal activity. Loyalists to certain nations will continue cooperating with these international hacking efforts.
As a result, I think we’ll see more governments attempting to create publicly known offensive capabilities to tear down criminal groups physically and technically. These takedowns of criminal networks take great diplomacy with speed and patience and active coordination of local and federal law enforcement.
Sam Humphries, Head of Marketing and Security Strategy, EMEA (England)

In the coming year, I believe we’ll see considerably more legal test cases with cyber insurers refusing to pay out for a myriad of reasons including poor cyber-hygiene, nation-state-sponsored attacks, and inadequate organisational response to ransomware. The latter will be particularly interesting, given the recent shift to extortionware, which has significantly increased the risk of data being leaked, and therefore invites the wrath of the compliance gods.
With regards to nation-state attacks, and given the geopolitical tensions of 2022, such legal test cases will put into question the burden of proof as to who are the culprits behind attacks. Attribution is an often poorly derived art, and whilst individuals can be quick to jump to assumptions regarding the perpetrators, this may prove to be a very costly exercise for both organisations and insurers.
On a different track, it’s a fairly safe bet that we’ll continue to see fallout from the recent Twitter takeover, where a serious reduction in force plus a change in tact regarding acceptable usage of such a widespread social media platform have created a significant amount of risk of attack. More widely in the tech space, unfortunately, layoffs continue across the board. Organisations need to be both taking care of exiting employees on a personal level, and ensuring they have a solid off-boarding policy, with visibility into normal and abnormal user account behaviour to quickly spot and prevent any negative retaliation incidents.
Richard Orange, VP Sales, EMEA (England)

With the UK now in a recession — and a broader background of global economic uncertainty — many businesses are looking to downsize their staff to reduce costs. But this is not without danger. Staff cuts present a significant insider threat risk. When large cuts are imminent, the threat also extends beyond malicious outgoing employees. Those that think they might be about to be fired, or those who have decided to resign (but haven’t yet) are all more likely to remove sensitive data — perhaps to their home devices — often even without knowing they could be committing a data breach.
We’re seeing lots of companies looking to integrate behaviour analytics tools quickly before they make staffing reductions, simply so that they can identify any unusual behaviour and reduce the insider risk. In an age of home working, behaviour analytics is the only way businesses can be confident they have true visibility during times of significant change.
Matt Rider, Area VP, Sales Engineering, EMEA (England)

Since the pandemic, the numbers of people working from home — or, for that matter, from converted school buses touring the California Coast — have risen rapidly, and while many businesses are encouraging workers to go back into offices, very few are mandating a pre-pandemic office-only working environment. Instead, a hybrid working model has quickly become the norm, with employees switching between their home and the office throughout the week.
However, this poses new operational challenges. Having made changes to support remote working, security teams must now tackle devices bouncing between home networks, corporate networks and in many cases, public networks. (Truck stop, anyone?) This opens businesses up to a wide range of new threats. How do you know if a device connecting to the corporate network isn’t also connected to something else it shouldn’t be, or worse, isn’t actually that trusted employee at all? Monitoring devices to understand their behavior will be crucial going into 2023. Zero trust is often cited as the answer to this challenge and, to some extent, that’s correct and highly encouraged. But you also need to truly understand and model user behavior to ensure that even authorized users and their devices are behaving as expected.
The Magic 8 Ball says, “Reply hazy”
Bette Davis in 1950 quipped the famous movie line, “Fasten your seat belts, it’s going to be a bumpy night.” She could have been talking about 2022, but as we slide into 2023, it doesn’t look like it’s getting any clearer out. Organizations are going to need to find new ways of prioritizing employee happiness and productivity while simultaneously protecting margins and the security ecosystem. But even if everyone is enjoying their vocational bliss, there will remain challenges from the outside that can become internal issues through credential theft or attack.
Finding ways to track insider threats and compromised credentials can be key to anticipating incidents and events in your organization — or detecting malicious activity already going on unseen. Exabeam can help you Detect the Undetectable™.
Sometimes even having a SOC isn’t enough to address insider threats. Security operations teams are managing massive amounts of data across billions of events from on-premises and the cloud, but looking for specific needles like insider threats has special requirements that encompass both searching historic data and seeing evolving credential behavior changes as they happen.
Whether from downsizing or expanding business, employees, vendors, contractors and others are moving in and out of your environment. And often, it is during these turbulent times that insider threats go unobserved — because everything is changing.
In this webinar, you will learn about:
- The four common scenarios where you need an insider threat team, and how to build a mission statement and tools
- Four attributes of a successful insider threat program
- How behavioral analytics baselines “normal” behavior of users and devices — showing risk faster
- Automated investigation experience that automates manual routines and guides new insider threat teams
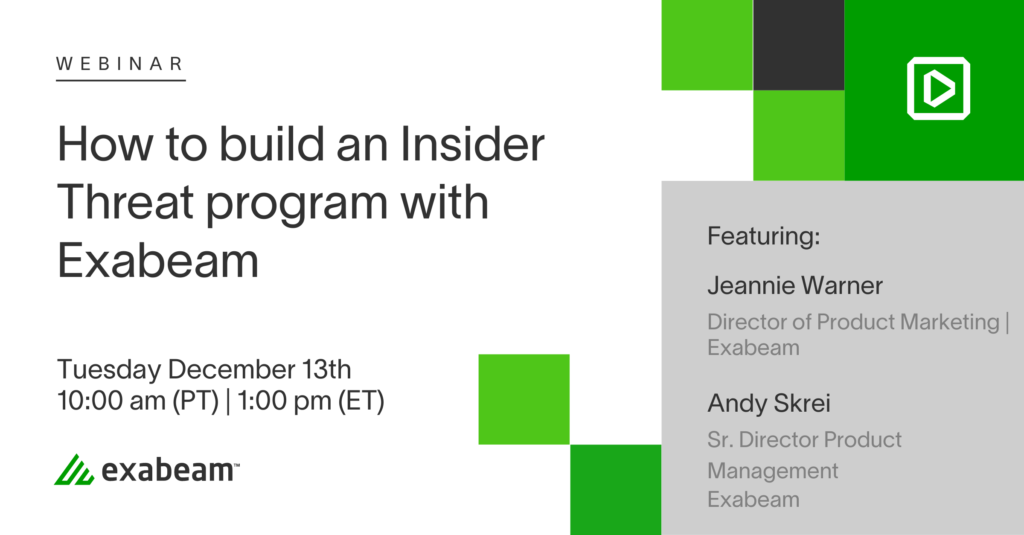

Jeannie Warner
Director, Product Marketing | Exabeam | Jeannie Warner, CISSP, is the Director of Product Marketing at Exabeam. Jeannie is an information security professional with over twenty years in infrastructure operations/security starting her career in the trenches working in various Unix help desk and network operations centers. She started in Security Operations for IBM MSS and quickly rose through the ranks to technical product and security program manager for a variety of software companies such as Symantec, Fortinet, and Synopsis (formerly WhiteHat) Security. She served as the Global SOC Manager for Dimension Data, building out their multi-SOC “follow the sun” approach to security. Jeannie was trained in computer forensics and practices, and plays a lot of ice hockey.
More posts by Jeannie WarnerLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
-
 Blog
Blog
Five Reasons Security Operations Teams Augment Microsoft Sentinel With New-Scale Analytics
- Show More


