
-
- Home
>
-
- Blog
>
-
- SIEM Trends
Five Reasons Security Operations Teams Augment Microsoft Sentinel With New-Scale Analytics
- Apr 24, 2026
- Heidi Willbanks
- 3 minutes to read
Table of Contents
Security operations teams face rising alert volumes, tighter staffing, and growing pressure to reduce risk without adding tools or people. If Microsoft Sentinel sits at the center of your environment, you may already see where it helps and where it starts to strain.
For many teams, that moment shows up when detections lag, investigations drag, or too much work funnels to a small group of specialists. That’s when security operations leaders start looking for ways to augment Sentinel rather than replace it.
Here are five reasons teams in your position extend Microsoft Sentinel with New-Scale Analytics.
1. You Need Earlier Signals Than Rules Can Provide
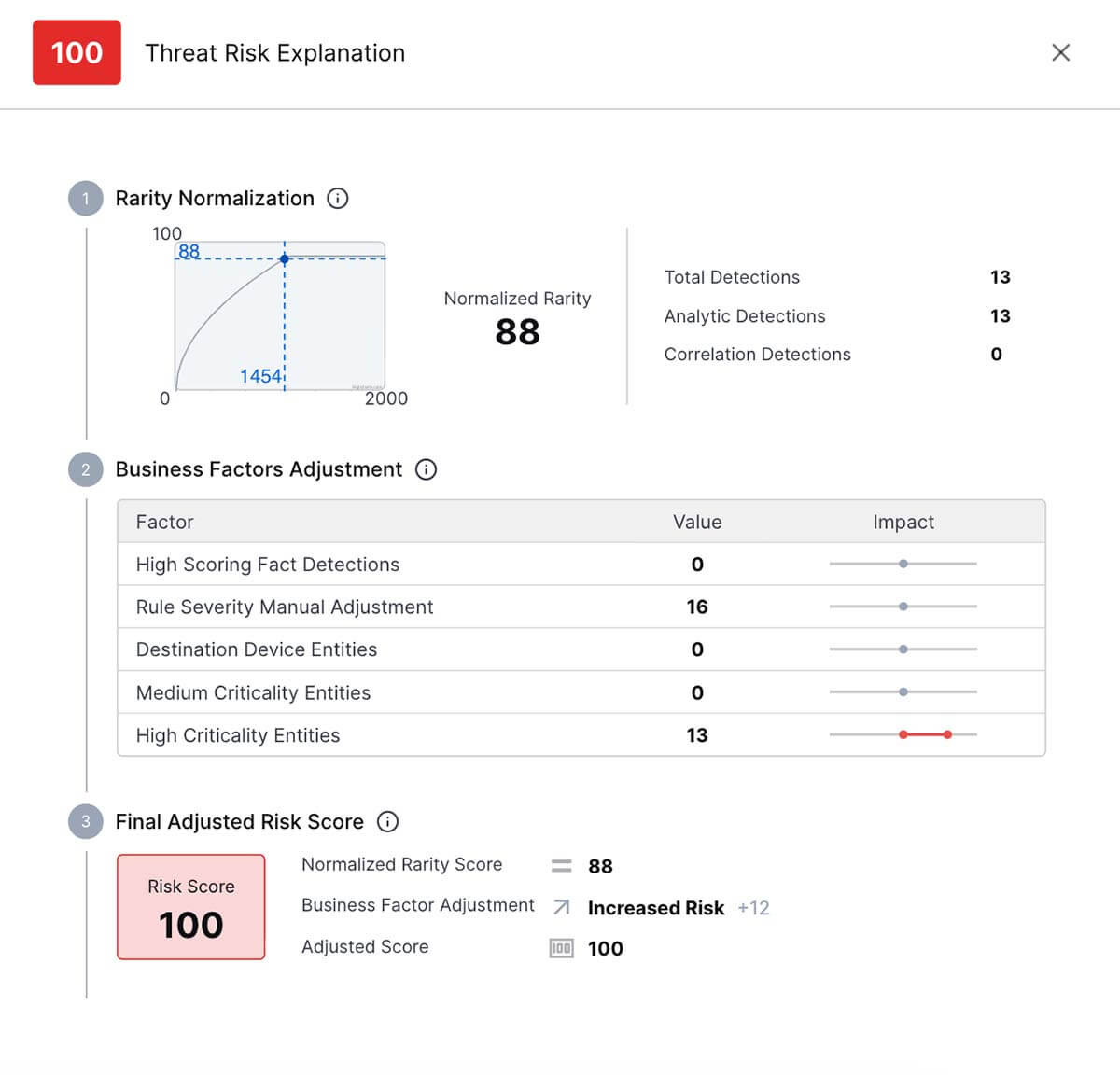
Rule-based detections and scheduled queries tend to surface issues once activity becomes obvious. Slow credential misuse, insider risk, and subtle abuse often build quietly across identities, systems, and tools before alerts fire.
Behavioral analytics helps change that dynamic. You gain visibility into patterns that indicate rising risk, including activity tied to both human users and AI agents operating within your environment.
What this means for your team: You spend less time reviewing noise and more time examining activity that shows early signs of misuse.
2. Investigations Pull You in Too Many Directions
Microsoft Sentinel investigations often require jumping between tables, dashboards, and custom queries. If you notice that investigations slow down as analysts pivot between views, you’re not alone.
Augmenting Sentinel with analytics that keep related activity connected helps investigations stay focused.
What this means for your team: You review related activity in context, which reduces backtracking and shortens investigation cycles when workloads spike.
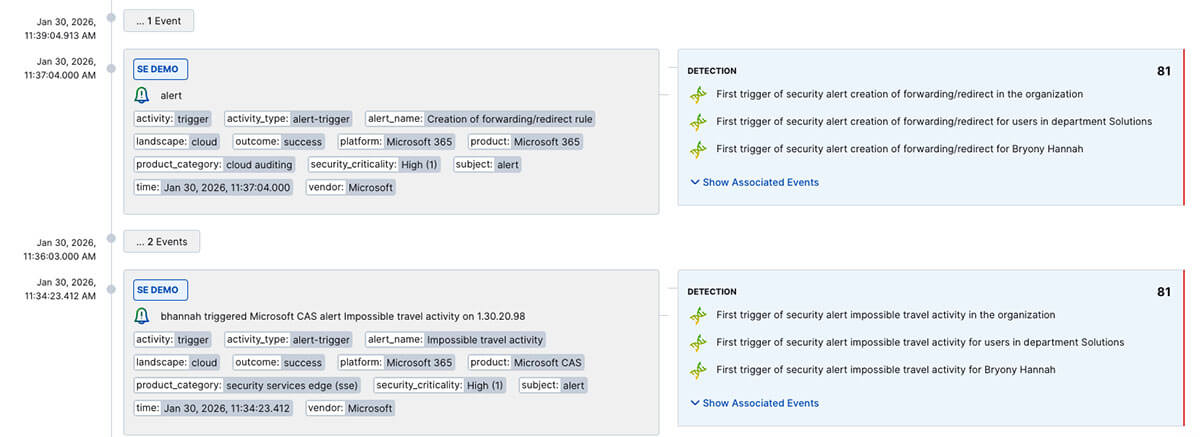
3. Complex Attacks Don’t Show Up as Single Alerts
Many attacks don’t trigger one obvious signal. They unfold gradually and often blend legitimate access with misuse. Rule-driven detections struggle to connect those actions without heavy manual effort.
Behavior-first detection improves visibility into activity patterns that span time, systems, and identities. This becomes even more important as environments rely more heavily on automation and agent-driven activity.
What this means for your team: You recognize multi-step attack paths sooner, instead of uncovering them after impact or during post-incident review.
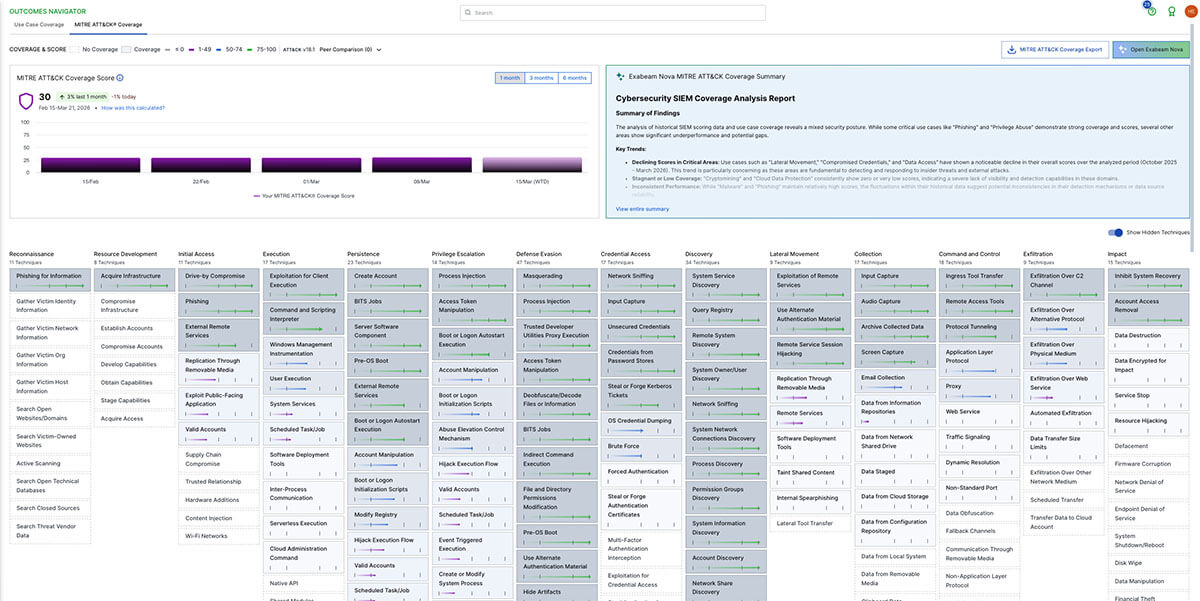
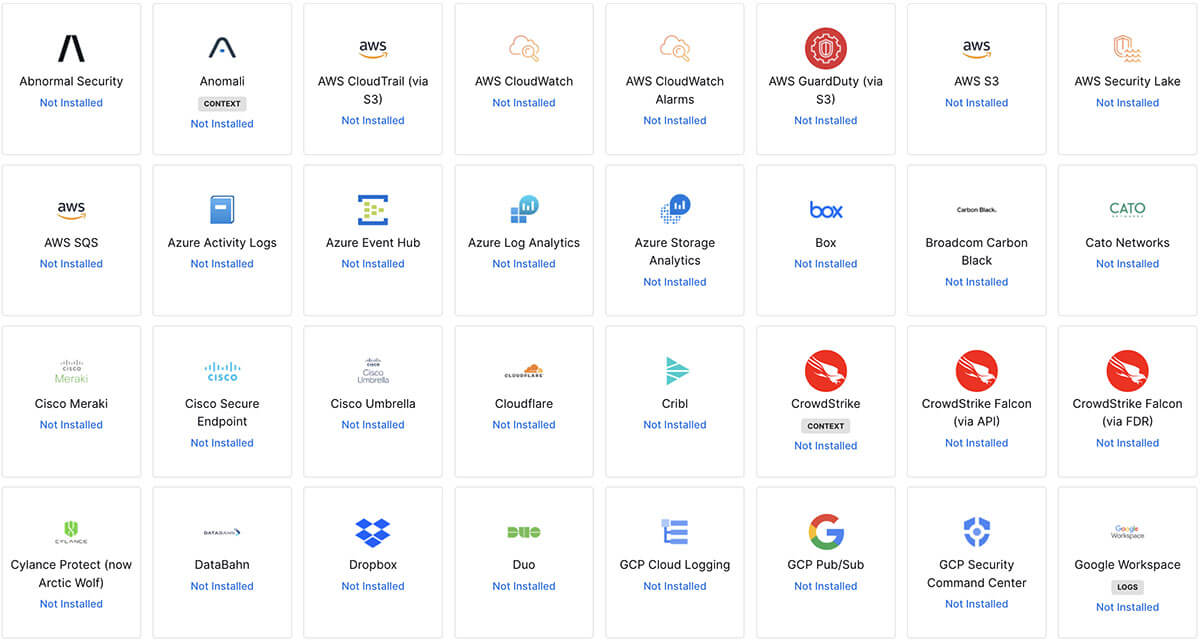
4. Visibility Breaks Down Outside Microsoft-Native Data
If your Sentinel environment leans heavily on Microsoft telemetry, you may feel the friction when identity, SaaS, endpoint, or third-party security data lives elsewhere. Investigations slow when activity sits in silos.
Extending Sentinel with analytics that evaluate behavior across diverse data sources helps reconnect those signals.
What this means for your team: You work from a more complete picture of activity, which improves investigation decisions without adding manual correlation.
5. Search Bottlenecks Limit Who Can Help
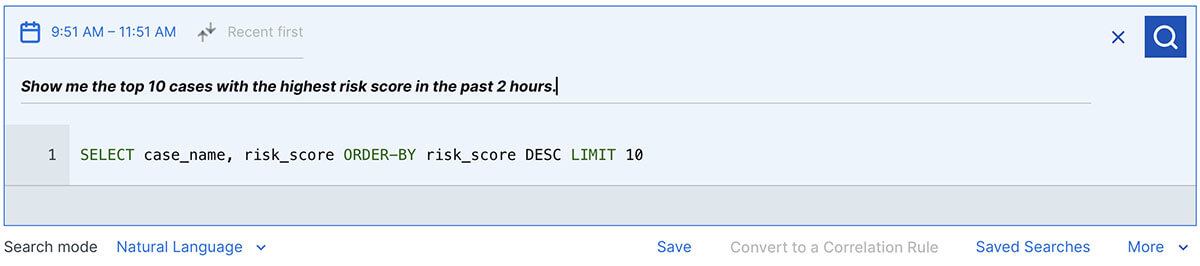
Query-heavy workflows often create bottlenecks. When only a few analysts can write or maintain complex queries, investigations stall and workloads pile up.
Reducing search friction helps more analysts contribute without relying on deep query expertise.
What this means for your team: You shorten investigation time and distribute work more evenly, even when staffing remains flat.
Why This Resonates With Security Operations Leaders
Most teams can’t hire their way out of skills gaps or workload pressure. If that’s your reality, improving outcomes means changing how risk surfaces and how investigations move forward.
Augmenting Microsoft Sentinel with New-Scale Analytics gives you a way to:
- Detect meaningful risk earlier
- Reduce investigation effort
- Expand coverage without replacing existing investments
The result is a security operations team that spends more time acting on risk and less time stitching data together.
Want the Complete Picture?
Read our guide to see what adding New-Scale Analytics to Microsoft Sentinel looks like in practice.
You’ll see:
- Where Sentinel detection coverage typically breaks down
- How behavioral analytics changes investigation flow
- What guided investigations look like for analysts
- How teams reduce investigation time without adding staff
Download the full guide to see how organizations augment Microsoft Sentinel with New-Scale Analytics.

Heidi Willbanks
Senior Product Marketing Manager, Content | Exabeam | Heidi Willbanks is the Senior Product Marketing Manager, Content at Exabeam. She manages content strategy and production for product marketing and supports strategic partners, sales and channel enablement, and competitive content, leveraging her product marketing certification, content expertise, and industry knowledge. She has 19 years of experience in content marketing, with nearly a decade in the cybersecurity field. Heidi received a BA in Journalism with a minor in Graphic Design from Cal Poly Humboldt and was awarded Outstanding Graduating Senior in Public Relations Emphasis. She enjoys reading, writing, gardening, hiking, yoga, music, and art.
More posts by Heidi WillbanksLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
