
-
- Home
>
-
- Blog
>
-
- SIEM Trends
Announcing Availability of the Exabeam Cloud Connector for Zoom
- May 12, 2020
- Phil Routley
- 4 minutes to read
Table of Contents
Usage of cloud services, in particular video conferencing apps, has exploded.
According to Okta’s Businesses @ Work (From Home) Report published in April 2020, Zoom was the fastest growing app with 110% growth in unique workforce users in March over February, 2020. To further highlight that incredible growth in users, during that same time period in 2019, Zoom’s workforce user growth was a mere 6%.

Such rapid adoption in cloud applications, whether officially authorized or not, exposes organizations to compromises in cloud security by attackers or malicious insiders.
Prior to the sudden surge in cloud application usage this year, swaths of organizations were already executing on their hybrid cloud strategy, while many others were ‘born in the cloud’. In mid-2019 Exabeam, acknowledging this shift, made the acquisition of SkyFormation, a leading Israel-based cloud application security business and the first company to collect and feed cloud logs into any security information and event management (SIEM) tool.
The acquisition accelerated the development of Exabeam Cloud Connectors
Cloud Connectors reliably collect logs from over 40 cloud services into Exabeam Data Lake and Exabeam Advanced Analytics to enhance cloud security. Earlier this year we added Cloud Connectors support for Workday and Ping. Today we are announcing support for the collection of logs from Zoom; further supporting security teams’ need to carry out their investigations across a diverse environment. This new log source is included as part of the existing Cloud Connectors solution. Clients who are already leveraging Cloud Connectors today will be able to ingest Zoom logs at no additional cost – for those readers not familiar with how Exabeam pricing is structured, we charge per user, not per byte.
Cloud Connectors are updated automatically whenever there are API changes, eliminating the need for your security team to spend precious time coding or for you to invest in costly professional services engagements.
Leveraging event and management API’s, Exabeam feeds the necessary event information from Zoom into Data Lake, and Advanced Analytics.
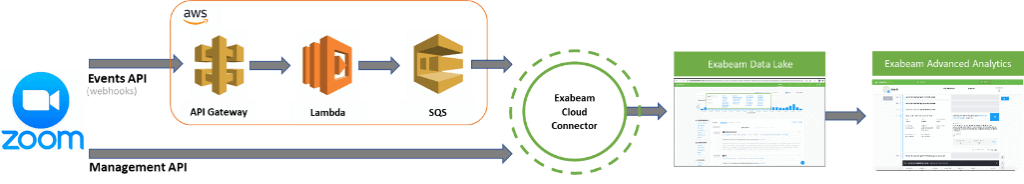
Cloud Connectors for Zoom operates in one of two ways. In the first, Zoom publishes the event data to a secured endpoint in a public cloud environment, in this case AWS. Cloud Connector then pulls that data down from AWS. The second method pulls data directly from the Zoom Management APIs into Cloud Connector.
Using Cloud Connectors; logs can be reliably ingested to provide the visibility needed to meet your regulatory requirements.
With regards to the Management API’s, the following audit sources and events are made available for investigations in Data Lake and Advanced Analytics.
| Zoom Audit Source (API) | Service/Module Covered |
| Operations logs report | The Operations Logs report allows you to audit admin and user activity, such as adding a new user, changing account settings, and deleting recordings. Use this API to retrieve an operation logs report for a specified period of time. |
| Sign-in/Sign-out activities report | Retrieve a list of Zoom meeting log-ins, sign-outs and other activity logs under a Zoom account |
Once the Zoom activity logs are ingested you can prepare reports to support audit, and risk and compliance requirements.


Cloud Connector allows you to easily collect logs from Zoom (and 40 other cloud applications), and bring them into Advanced Analytics, where they can be combined with data from on-premises applications to improve detection of attacker tactics, techniques and procedures using behavior-based threat detection.
Behavioral analysis-based threat detection – Exabeam’s threat detection is based on the world’s most-deployed user and entity behavior analytics (UEBA) solution. Combining cloud activity data with that from your on-premises log sources, it creates baseline behaviors for all users and entities. Exabeam Smart Timelines stitches together all events from various sources and automatically identifies risky, anomalous activity that may point to threats.
While monitoring of Zoom activity is important, the real value comes when that activity is tracked in the wider context of normal and abnormal user behaviors such as account switching, remote logins, database logins, and administrative asset logins to detect anomalous activity. Enriched with additional contextual data, all Zoom events are mapped to user sessions. All risky behaviors within a session are assigned a risk score, with critical events being elevated to a higher score level and displayed as part of a timeline.
Most legacy products build a timeline that tracks a single dimension such as IP address, hostname, or username. While with time and effort, this could yield a timeline of events, it misses critical parts of the attack such as privilege escalation used to gain access to other computers, and with that access to confidential information shared via Zoom meetings.
Exabeam Smart Timelines use machine learning to automatically gather and stitch together all events that originated from a single user including privilege escalations making it easy to spot lateral movement.

Summary
In summary, Cloud Connectors deliver:
- Out-of-the-box cloud services connectors for your SIEM saving you expensive development or professional services
- Integration with over 40 cloud services such as AWS, GitHub, Google, Microsoft Office 365, Salesforce, Workday, Zoom and many other cloud security, identity and access management, infrastructure and business applications.
- An opportunity to broaden your investigations at a predictable per-user price point
- Integration with Advanced Analytics to create Smart Timelines which identify normal and abnormal user behaviors and halve the time for investigations
The Cloud Connector for Zoom specifically delivers
- The ability to audit admin and user activity, such as adding a new user, changing account settings, and deleting recordings.
- Retrieve Zoom meetings activity such as log-in, sign-out and more
- Reports that support audit, and risk and compliance requirements
Further learning
- Insider threat hunting demo showing exactly how Exabeam when combined with Okta and Netskope prevents a disgruntled employee downloading your critical data from Salesforce
- Exabeam Cloud Security 101 blog
- Tags
- Cloud
- Product
- Product Update
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
-
 Blog
Blog
Five Reasons Security Operations Teams Augment Microsoft Sentinel With New-Scale Analytics
- Show More



