
Understanding the Challenges of Frontline Security Teams and the CISOs who Lead Them
- Dec 04, 2018
- Maritza Marie Dubec
- 4 minutes to read
Table of Contents
The security operations center (SOC) is a critical frontline outpost of cyber defense. It pays to ensure your SOC is equipped with the right strategies, solutions, and talent so it runs smoothly.
Exabeam’s 2018 State of the SOC Report dove into the mindset of those in the cybersecurity trenches, as well as the managers and CISOs who lead them. Their views on critical aspects of operations, technology, hiring, and staffing provided key insights on how organizations can maintain a well-run and effective SOC.
The study also reveals several common concerns—ranging from staffing and retention to frustration over legacy technologies. And it found a surprising degree of separation between the perspectives of top management and their frontline security analysts.

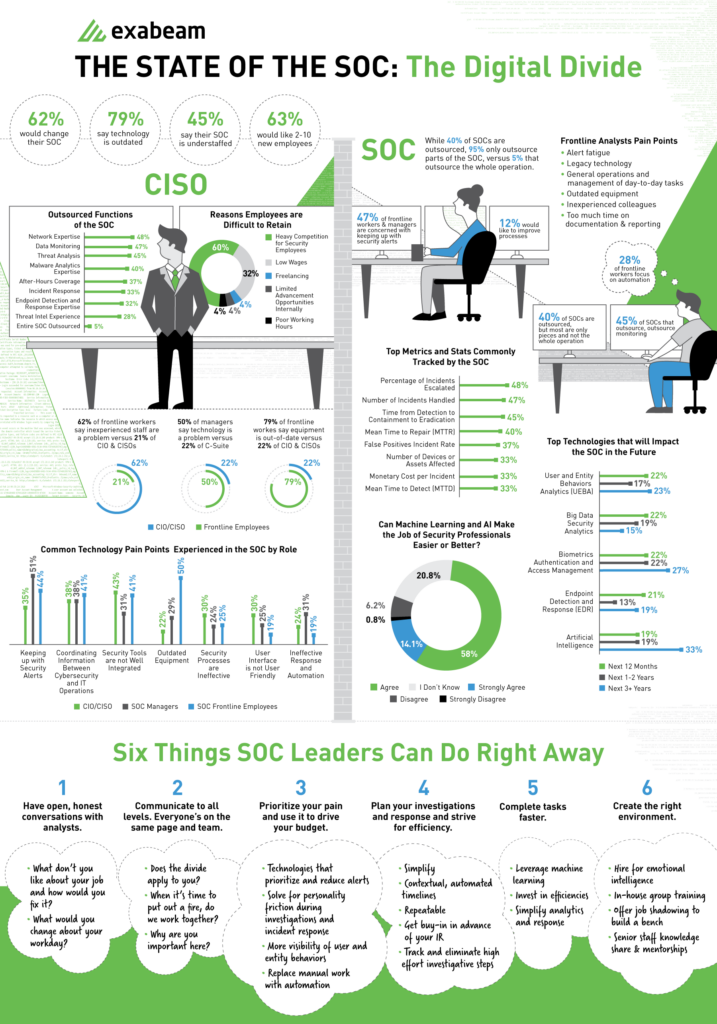
The good news is that security operations centers have become a more established part of organizational security—91 percent of SOCs have been operating for three years or more. Overall, 40 percent outsourced; of these 95 percent of organizations outsource only a portion of their SOC, whereas 5 percent outsource the entire operation.
The most commonly outsourced SOC functions include network expertise, data monitoring, threat analytics, and malware analytics expertise. The reasons for outsourcing these skills-intensive functions are clear to those in the security field today. Security expertise is scarce and there is heavy competition to recruit the most skilled and experienced talent. And once onboard, talent is difficult to retain; reasons range from poor working hours to lucrative opportunities available for freelancers.

The view from the C-suite is different than the trenches
Our study also found that SOC life is not an easy one. Pain points shared by analysts include:
- Alert fatigue
- Legacy technology
- General operations and management of day-to-day tasks
- Outdated equipment
- Inexperienced colleagues
- Too much time spent on documentation and reporting
And the pain isn’t shared equally. More frontline workers (50 percent) experience frustration with outdated equipment compared to their direct managers (29 percent) and members of the C-suite (22 percent). In addition, more than half of SOC managers expressed concerns over keeping up with security alerts, while just 35 percent of CIOs and CISOs experienced that as a pain point themselves.

Exabeam’s survey also found that CIOs/CISOs and managers are more focused on technology, preventative measures, and process improvements than are frontline analysts. Differing views become more pronounced when it comes to critical issues such as the importance of experience. Here, more than 62 percent of those working in the SOC cited inexperienced staff as a major pain point. Yet only 21 percent C-level think staff see that as an important concern.

When it comes legacy technology, 50 percent of SOC managers report this as being a problem, while only 22 percent of those in the C-suite cite it as a core issue. Meanwhile, a big majority (79 percent) of SOC analysts cited out-of-date equipment as being problematic, compared with only 22 percent of CIOs and CISOs.
When it comes to being on the same page, the survey responses reflect a lack of alignment between executives and their teams. This may stem from CISOs and CIOs being less aware of what frontline security teams face on a daily basis. Perhaps this isn’t surprising when you look at the number of IT executives who have never worked in security operations previously. Frequently they come from another area of the business and have less security experience. This misalignment of shared understanding can have major ramifications when it comes to making important security decisions.
Is it time for a change?
Those familiar with inner workings of the SOC know that a great number of security professionals believe their technology is outdated and that they’re understaffed. Here, the majority of respondents (62 percent) would like to change their SOC, with outdated technology an issue for 79 percent. Meanwhile, 45 percent report their SOC is short of the right talent, with 63 percent stating they would like to add from two to ten new employees.

But change doesn’t come easily. Given the chronic shortage of skilled security experts, filling open requisitions could be a Herculean task.
Too few analysts handling too many alerts
Managers and analysts do agree about their frustration with outdated equipment. Short staffs and legacy technology issues converge in another SOC report takeaway—nearly half of all respondents (47 percent) reported that security alert volume remains their biggest pain point.

Implementing meaningful automation comes from feeling frontline pain
Automation can also help to ensure that your security teams don’t end up suffering from burnout, which is crucial considering that detecting and defending against cyberattacks requires around-the-clock vigilance. And automation can help with prioritizing alerts and missing threats due to alert fatigue.
But while alert fatigue is a big factor for SOC analysts, it’s a lesser concern for leadership. The ability to examine everyday issues like legacy tools issuing too many alerts that lack prioritization or context is a focus of case management that’s evolving.
Respondents saw automated technologies that use AI, machine learning, and big data analytics as the path to a more efficient SOC. For technologies impacting the SOC for the next 12 months to three-plus years, user and entity behavior analytics (UEBA) ranked highest, followed by big data security analytics. Exabeam also found agreement (more than 71 percent) on whether machine learning and AI can make security professionals’ jobs easier and better.


Technology alone can’t win the battle against today’s cyber threats
A major takeaway of the Exabeam report shows the need for combining technology improvements with better communication between the ranks—improving the chances that your organization’s SOC can prevent the next cyberattack.
For more information on the State of the SOC, see Exabeam’s Report.
- Tags
- Security
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
-
 Blog
Blog
Five Reasons Security Operations Teams Augment Microsoft Sentinel With New-Scale Analytics
- Show More


