New-Scale Fusion is built on Google Cloud Platform (GCP), which has a 99.5% uptime service level agreement. Exabeam adds application-level resiliency and redundancy. Our global cloud operations team monitors platform health signals around the clock to detect and address issues. You can check service availability at any time through a dedicated status page.
بحث عالي الأداء
Search Terabytes of Data In Seconds
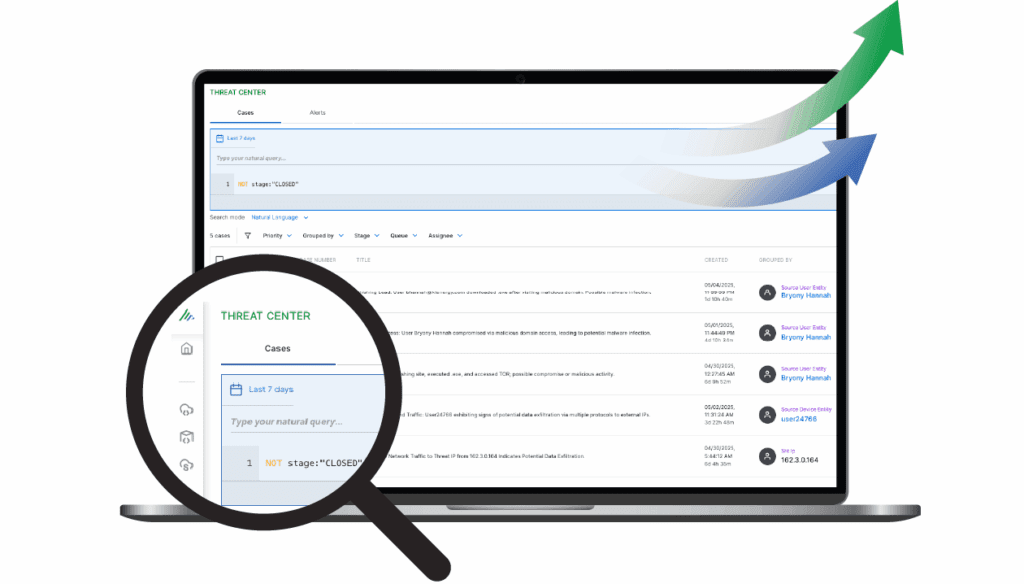
Query TBs of security data in seconds through an investigation-ready search interface. New-Scale SIEM works for every analyst. Power users build advanced queries, and your team can run natural-language searches, create timelines, and build visualizations.
- Power searches, dashboards, and timelines with NLP.
- Use simple or advanced query options based on experience.

الأتمتة المدفوعة بالذكاء الاصطناعي
Automate Workflows With AI Agents
Exabeam Nova is an intelligent agent framework that automates routine and strategic security operations tasks. It creates case summaries, classifies threats, and provides consistent insights that help your team work more efficiently.
- Reduce manual validation and documentation.
- Deliver faster, more consistent decisions.
الأمن الموجه نحو النتائج
Connect Security Work To Business Value
Outcomes Navigator translates technical data into measurable business value. It maps ingested data to security use cases and MITRE ATT&CK®, giving you insight into human and non-human entity behavior. Exabeam Nova Advisor Agent makes recommendations to strengthen your security posture.
- Benchmark your program against peers to guide investments.
- Quantify and report on compliance for common frameworks.
ورشة عمل TDIR المركزية
توحيد كشف التهديدات، والتحقيق، والاستجابة
Threat Center brings alerts, cases, detections, and watchlists into one workbench. It accelerates TDIR by automating prioritization, triage, and evidence collection so analysts can manage cases from start to finish.
- Streamline investigation workflows and reduce context switching.
- Respond faster with automated evidence gathering and guided case decisions.
خدمة المنصة والصحة
مراقبة صحة المنصة واستهلاكها
Identify, diagnose, and address issues quickly within New-Scale Platform services. Deep operational visibility helps engineers isolate service or performance concerns, and daily consumption metrics help manage costs.
- Detect anomalies in ingestion or processing rates.
- Forecast scaling or cost needs.

جمع السجلات المبسط
أضف مصدر بيانات جديد في دقائق
Collect data from on-premises and cloud sources at scale with prebuilt collectors that process more than two million events per second (EPS). A guided wizard helps you create, deploy, and manage custom parsers from new or existing templates.
- ابدأ بأكثر من 7000 محلل سجلات جاهز.
- Use API, agent, syslog, SIEM, or data lake transport.
نموذج المعلومات المشترك
Standardize Data For Faster Analysis
The Common Information Model (CIM) normalizes data at ingestion to make logs easier to parse, store, and manage. The CIM speeds detection, response, visualization, and high-performance search.
- تحويل البيانات الخام إلى أحداث أمنية منظمة وقابلة للتنفيذ.
- Standardize event definitions across all sources.
- Normalize emerging log sources for easier parsing and analysis.
خدمة استخبارات التهديدات
Improve Accuracy With Curated Threat Feeds
The Exabeam Threat Intelligence Service ingests and scores commercial and open-source threat feeds. It refreshes every 24 hours and is included at no extra cost. It uses machine learning to produce a highly accurate stream of indicators of compromise (IoCs).
- Compare intelligence to historical context to lower false positives.
- Enrich detections by linking IoCs to active cases.
- Ingest your own feeds using the STIX/TAXII Cloud Collector.

التقارير المخصصة ولوحات المعلومات
Build Dashboards and Reports With Natural Language
Create custom dashboards using 14 chart types and schedule compliance reports for delivery. Natural-language prompts help you build reports quickly, giving you insight into SIEM data without extra tools.
- Keep leadership informed through scheduled reports.
- Explore SIEM data with interactive dashboards.
هندسة الكشف المخصصة
Build Correlation Rules From Search
Convert searches into detection rules in one click. Write, test, publish, and monitor up to 1,000 custom correlation rules, and assign higher criticality to rules backed by high-fidelity intelligence.
- بناء قواعد من الصفر، استخدام نموذج، أو حفظ بحث.
- حدد الأحداث المهمة والشروط التي يجب أن تستوفيها.
- Assign conditions and criticality to guide response.
نشر مرن وقابل للتكيف
سهل البدء
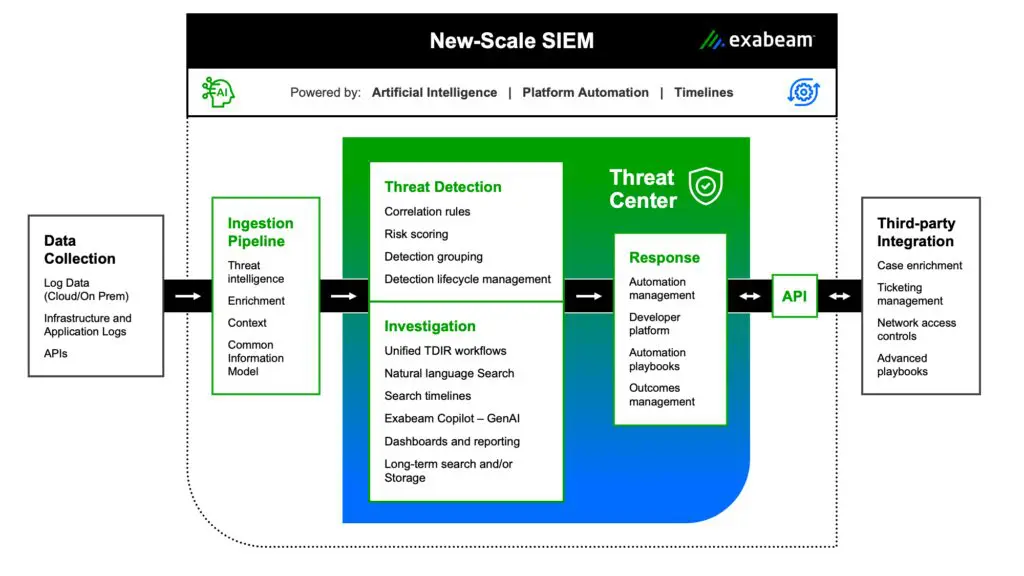
New-Scale Fusion combines the strengths of New-Scale SIEM and New-Scale Analytics in one modular platform. It brings together log management, SIEM, behavioral analytics, dynamic risk scoring, and automation to help your team detect insider threats, reduce manual work, and meet compliance goals. You can use New-Scale Fusion to replace your SIEM or augment your current system with advanced analytics and automation.

كيف يمكننا المساعدة؟ تحدث إلى خبير.
اتصل بناالأسئلة الشائعة
كيف يضمن البائع توفر حل SIEM؟
من أين يتم تسليم الحل، وأين يتم تخزين بياناتي؟
New-Scale SIEM is delivered from GCP. Data is stored securely in availability centers worldwide, and new locations are added regularly. At purchase, you choose where your service is hosted from a list of available global regions. Customer data is protected and isolated.
كيف يتم جمع بياناتي ونقلها؟
Data is transported securely to the New-Scale Platform. Methods include Exabeam Collectors, log forwarding, and API-based ingestion from SIEMs such as QRadar, Microsoft Sentinel, or Splunk. Collectors run as virtual machines on your premises behind your firewalls and use SSL to forward encrypted data. They can also collect data from public clouds like AWS, Azure, and GCP, as well as SaaS applications like Microsoft Office 365 and Salesforce.
"استخدام Exabeam ذكرني بمدى سرعة تحديث المنصة بشكل مفاجئ. هناك تحسين شبه يومي في الوظائف المطلوبة، ومع Exabeam، كل شيء يستمر في التحسن."
شاهد Exabeam في العمل
اطلب المزيد من المعلومات أو اطلب عرضًا توضيحيًا لأقوى المنصات في الصناعة للكشف عن التهديدات والتحقيق فيها والاستجابة لها (TDIR).
تعلم المزيد:
- إذا كان نظام إدارة معلومات الأمان (SIEM) المستضاف ذاتيًا أو القائم على السحابة هو الخيار المناسب لك
- كيفية استيعاب ومراقبة البيانات على نطاق واسع في السحابة
- كيف تكشف مراقبة وتحليل سلوك الذكاء الاصطناعي والوكالات الآلية عن الأنشطة غير البشرية الخطرة.
- كيفية تقييم وتصنيف نشاط المستخدم بشكل تلقائي
- شاهد الصورة الكاملة باستخدام جداول زمنية للحوادث.
- لماذا تساعد أدلة العمل في اتخاذ القرار الصحيح التالي
- دعم الالتزامات المتعلقة بالامتثال
قادة حائزون على جوائز في مجال الأمن



































