
-
- Home
>
-
- Blog
>
-
- InfoSec Trends
17 InfoSec Resources You May Have Missed in March
- Apr 07, 2022
- Madeleine Korn
- 7 minutes to read
Table of Contents
At Exabeam, part of our mission is to help keep security professionals educated and informed on threat detection and incident response topics. In March, we created several resources for you. In case you missed them, here are 17 of our most recent pieces geared toward helping you mature your SOC and enhance your security posture with XDR and next-gen SIEM. Whether you’re a CISO or a security practitioner, there is something on this list for you.
1. Insider Threats: When the Attacker Has Valid Credentials | Guide
Insider threats are security risks that originate from within the organization. The threat actor is not always a current employee or officer in the organization; the threat actor can be consultants, former employees, business partners, or board members.
Insider threats are classified into three categories: malicious insiders, negligent insiders and compromised insiders. Read the guide to learn more about these insider threats and three ways Exabeam can help you combat the threats.
2. Phishing: Guide to Mitigating Attacks | Guide
Phishing is a cybersecurity threat and social engineering tactic that collects private information on the internet. Phishing scams typically use fake websites (emulating financial or eCommerce websites) with altered URLs that resemble the web address of the actual website.
Phishing emails are one of the most common ways attackers attempt to trick users into providing information through links to sites that imitate legitimate websites. Read our guide to make sure you understand the common challenges of phishing attacks and 5 steps you can take to protect your organization.
3. External Attacks: Ransomware and Phishing Attacks | Solution Brief
Cyber threats are getting more sophisticated as more companies migrate to the cloud and remote work becomes a staple of a modern business. The changing dynamics of security threats and business processes have led to a fourfold increase in cybersecurity complaints and global losses from cybercrime exceeding $1 trillion in 2020.
Security operations teams not only manage internal threats but contend with software and security vulnerabilities that can expose intellectual property and financial data to external entities. Ransomware, social engineering, DDoS attacks, and phishing attacks are all common external threats most SOC teams have to contend with.
4. 5 Key Things to Achieve in Your First 90 Days as CISO | Infographic
The role of CISO has changed — the increase in cyberattacks has placed the role of the CISO at center stage. As a CISO, you need to identify the organization’s cybersecurity goals and business-critical processes. Here are 5 key things to hit the ground running in your first 90 days.
5. Selecting a Next-Generation Security Information and Event Management Solution, 2021– 22 | Report
This report helps enterprise buyers understand the next-gen SIEM competitive landscape and successfully navigate the product evaluation, purchasing, and deployment lifecycle by offering a detailed review and analysis of seven next-gen SIEM solutions.
Key takeaways from this report:
- Cloud-native next-gen SIEMs offer compelling advantages over cloud-hosted alternatives.
- IBM and Micro Focus remain market share leaders despite increasing competition.
- XDR is emerging to challenge next-gen SIEM, but ultimately both should prosper.
- Omdia recognized five leaders and two challengers; Exabeam Fusion SIEM earned the distinction of being Omdia’s overall top-ranked next-gen SIEM solution.
6. What Is the HIPAA Compliance Standard and How to Adhere to It? | Blog
Any organization dealing with protected health information (PHI) in digital or analog form must comply with the Health Insurance Portability and Accountability Act (HIPAA). HIPAA fines cost one company more than $5 million in 2021.
Strict adherence to the HIPAA compliance standard helps prevent data loss and avoids the legal and financial consequences involved. Organizations need security tools and solutions to help prevent data loss and data breaches to protect and secure HIPAA-protected data.
An organization bound by HIPAA may find compliance a rather daunting task. In this article, we aim to cover the basic aspects of HIPAA compliance standards and give some guiding principles to effectively achieve compliance.
7. Planning Before the Breach | Blog
Cybersecurity risk can come from anywhere — a lone wolf, organized cybercriminals, nation-states, or rogue insiders. In 2020, more than 80 percent of the breaches that were reported involved compromised credentials, according to the Verizon Data Breach Investigations Report (DBIR). How many times have you gotten a breached password detection alert, prompting you to change your password? Unfortunately, our credentials are out there in the wild, making them a big part of the risk picture.
In the event of an intrusion, it’s the security analyst’s job to chase the attacker. An analyst may get 500 alerts or more. How do they know where to start? How to triage and manage hundreds of alerts while there’s an active attack underway?
8. The Significance and Role of Firewall Logs | Blog
A firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules. In addition to this policy, firewall log information is needed to audit the security efficacy of the firewall.
Firewall logging records when and how access attempts are made, including source and destination IP addresses, protocols, and port numbers. A SIEM data lake uses this data to help investigate historic attacks and find evidence of probing.
9. SOX Compliance: Requirements and Checklist | Blog
Organizations that offer stocks or securities must maintain both good financial practices and maintain data security standards. The higher the financial stakes, the higher the risk of being targeted for data theft and the greater the consequences of a successful attack.
The Sarbanes-Oxley Act of 2002 (SOX) was originally enacted to combat unethical corporate and financial practices, notably the Enron and WorldCom scandals. These scandals caused billions of dollars in losses for investors and eroded public confidence in the US stock market.
A major part of SOX regulations relate to information technology and security best practices. Because SOX is a mandatory standard that applies to all US-based public companies, it has had the positive side effect of encouraging robust information security practices.
10. Security Incidents: What You Should Look Out For | Blog
Security incidents are events that occur with a potential impact to an organization that can represent a cybersecurity threat or attack. Identifying incidents and responding to them quickly is a critical cybersecurity process.
11. Top 3 Skills Cybersecurity Project Managers Rely On | Blog
Exabeam’s Pamela Turner writes, “When people ask me about my experience as a project manager in cybersecurity, one of the first things that come to mind is that I have been fortunate to work on some of the most exciting projects. And, it has been a learning experience for me every time.
I wasn’t always in cybersecurity and I like to tell the story of what brought me to Exabeam. Credit goes to my coworker at the time for calling me about an opportunity at this up-and-coming cybersecurity company. I immediately researched Exabeam and learned it was making waves in the security industry. Women in cybersecurity are underrepresented and I saw it as a challenge to do something I hadn’t done before.”
12. What is Security Analytics? | Blog
No organization has a crystal ball and thus cannot predict the future, particularly where security threats are involved. However, by using security analytics tools like UEBA, your organization can better analyze security events and potentially detect a threat before it impacts your revenues or infrastructure.
13. Incident Response Plan 101: The 6 Phases, Templates, and Examples | Blog
An incident response plan is a set of tools and procedures that your security team can use to identify, eliminate, and recover from cybersecurity threats. It is designed to help your team respond quickly and uniformly against any type of external threat.
Incident response plans ensure that responses are as effective as possible. These plans are necessary to minimize damage caused by threats, including data loss, abuse of resources, and the loss of customer trust.
In this post, you will learn how to build an incident response plan around the 6 phases of incident response, examples to get you started, and sneak a peek at incident response automation.
14. The Relationship Between Business Risk and Security and the Role of the Modern CISO | Blog
Today, businesses face more risk than ever, and modern security teams shoulder the enormous responsibility of protecting their organization’s most sensitive and valuable data. Cybersecurity has become a business guardian and enabler, its critical role being the management and control of organizational risk. Savvy executive leaders are well aware of how important security has become to the function and success of their businesses.
It’s easy to understand the importance of cybersecurity for business, but what about business risk’s impact on the shape of security today? How does an organization’s view of business risk shape its security posture and priorities? What’s the nature of the relationship between business risk and cybersecurity, and how does this affect the role of the modern CISO?
15. Change Your Risk Mindset to Level the Security Playing Field | Blog
Cybercriminals, nation-state actors, and malicious insiders are actively targeting organizations for financial gain, to steal secrets and intellectual property, disrupt operations, and harvest personally identifiable information (PII). According to the 2020 Verizon Data Breach Investigations Report (DBIR), in that year alone, more than 80% of reported breaches used valid credentials or were from brute-force attacks.
Keeping up with attackers requires a deeper understanding of the risk in your environment — behavioral context — about every user and asset. The data science behind this context, amplifying the rules you already have, arms you with a picture of normal activity, which is likely the best defense available to avoid being blindsided by an attack. By adopting this “assume breach” mindset, you’ll be able to rapidly detect any anomalous behaviors so you can respond faster.
In this post, we’ll examine ways that organizations can better understand their risk, improve their threat detection and incident response (TDIR) capabilities, and level the playing field against sophisticated adversaries.
16. The New CISO: Demonstrating Your Value of Your Program to the Layperson | Blog
Many businesses fail to understand the business value of cybersecurity and only realize it once a breach has already occurred. How can a CISO demonstrate value to the organization without making false guarantees? In this episode of The New CISO Podcast, Andrew Obadiaru, CISO and Head of IT at Cobalt, shared advice and tips for CISOs, as well as how to respond to some of the most difficult questions that may arise.
17. What’s the Big Deal with Big Data Analytics? | Blog
Big data is changing the way we communicate, conduct research, and operate businesses. The large variety and volume of data available today holds the key to many advances in technologies and services, allowing organizations to learn from past and present behavior, and even predict future patterns using tools like SIEMs.
Big data allows both public and private organizations to optimize their operations to best meet the needs of their customers. However, this large amount of raw data can be overwhelming and sorting through a mountain of information can be a massive task. Analytics can help to make the data usable.
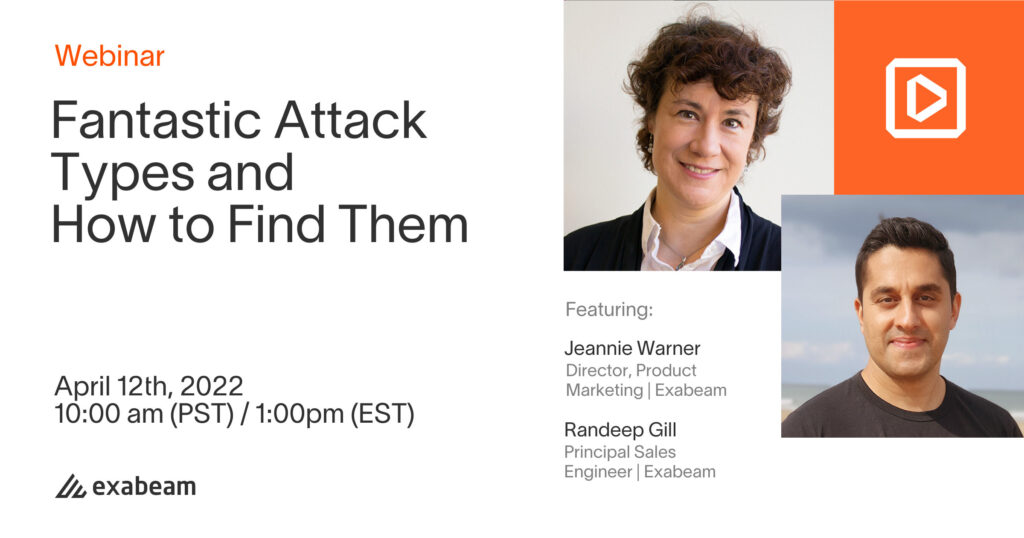
Register for our upcoming webinar, “Fantastic Attack Types and How to Find Them.” You’ll learn:
- The difference between chasing IoCs and leveraging TTPs
- Why credential theft and subsequent usage is key to detect virtual pickpockets
- Automated threat analytics – how it helps outsmart the fantastic and turn it into commonplace
- Tags
- Resources

Madeleine Korn
Marketing Content Coordinator | Exabeam | Madeleine Korn is a Marketing Content Coordinator at Exabeam. Prior to Exabeam, she worked as a Business Operations and Management Intern for United Airlines and as the Advertising Director for The Bottom Line Newspaper. She graduated from the University of California, Santa Barbara with a communication degree. In her free time, she loves hiking and traveling.
More posts by Madeleine KornLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
-
 Blog
Blog
What’s New in New-Scale April 2026: Securing the Agentic Enterprise With Behavioral Analytics
- Show More

