-
- Home
>
-
- Explainers
>
-
- Splunk
Best Threat Intelligence Tools: Top 8 Providers in 2025
- 8 minutes to read
Table of Contents
What Are Threat Intelligence Tools?
Threat intelligence tools are software applications and platforms that help organizations collect, analyze, and act on information about cybersecurity threats. These tools improve security by providing insights into potential vulnerabilities, attack methods, and threat actors, enabling proactive defense strategies (Related content: Read our guide to threat hunting vs threat intelligence).
There are three main types of threat intelligence:
- Tactical threat intelligence: Focuses on specific, immediate threats and indicators of compromise (IOCs).
- Operational threat intelligence: Provides contextual information about threat actors and their tactics, techniques, and procedures (TTPs).
- Strategic threat intelligence: Analyzes long-term trends and patterns to inform overall security strategies and investments.
Some key features and benefits of threat intelligence tools include:
- Threat detection and analysis: Threat intelligence tools help identify and analyze various threats, including malware, phishing attacks, and other malicious activities.
- Vulnerability management: They provide information on known vulnerabilities, allowing organizations to prioritize and address security weaknesses.
- Incident response: By providing context and remediation guidance, these tools assist in responding to security incidents effectively.
- Integration with security systems: Threat intelligence tools integrate with existing security systems like SIEMs and security testing tools to enhance overall detection and response capabilities.
- Proactive security posture: By providing insights into emerging threats and attack patterns, these tools enable organizations to adopt a proactive security approach.
This is part of a series of articles about cyber threat intelligence.
Types of Threat Intelligence
Tactical Threat Intelligence
Tactical threat intelligence focuses on immediate, actionable data that can be directly applied to defense operations. This includes IOCs such as malicious IP addresses, URLs, file hashes, and specific malware signatures. Security teams use this intelligence to configure firewalls, intrusion detection systems, and endpoint protections to block known threats in real time.
Operational Threat Intelligence
Operational threat intelligence provides contextual information about ongoing threat campaigns and the tactics, techniques, and procedures (TTPs) used by threat actors. It helps organizations understand how attacks are being executed, what tools attackers are using, and what vulnerabilities they are targeting. This intelligence supports the tuning of detection rules and enhances incident response playbooks.
Strategic Threat Intelligence
Strategic threat intelligence focuses on broader trends, threat actor motivations, and geopolitical or industry-specific risks. It is intended for executive decision-makers and helps inform long-term security investments, risk management strategies, and policy development. Strategic intelligence often comes in the form of reports detailing threat actor groups, emerging threats, and future attack trends relevant to the organization’s sector.
Related content: Read our guide to threat intelligence software.
Key Features of and Benefits Threat Intelligence Tools
Threat Detection and Analysis
Threat detection and analysis tools collect and examine data from various sources such as network traffic, logs, endpoints, and external threat feeds. They identify indicators of compromise (IOCs) like suspicious IP addresses, malicious domains, and malware signatures.
Advanced analytics and machine learning help detect abnormal patterns that may signal potential attacks. This early identification enables organizations to take timely preventive or corrective actions to mitigate risks.
Vulnerability Management
Threat intelligence tools assist vulnerability management by correlating external threat data with internal asset information. They provide details on known vulnerabilities, including CVE identifiers, exploit availability, and active threat campaigns targeting specific weaknesses.
By contextualizing vulnerabilities with threat intelligence, organizations can prioritize patching based on real-world risk, rather than just severity scores. This targeted approach improves resource allocation and reduces the attack surface.
Incident Response
During incident response, threat intelligence tools provide valuable context about attackers, their tactics, and known indicators related to the incident. They help security teams quickly identify the scope and impact of an attack by enriching alerts with threat actor profiles and attack patterns.
This contextual information supports faster decision-making during containment, eradication, and recovery phases, ultimately reducing the dwell time of attackers within the network.
Integration with Security Systems
Threat intelligence tools integrate with security infrastructure such as SIEMs, endpoint detection and response (EDR) platforms, and firewalls. This integration allows threat intelligence data to be ingested and correlated with internal logs and telemetry.
As a result, organizations can automate threat detection, enrich security alerts with external intelligence, and trigger predefined response actions across multiple security layers for a more coordinated defense.
Proactive Security Posture
By delivering timely information about emerging threats, attacker tactics, and vulnerability trends, threat intelligence tools help organizations shift from reactive to proactive security. They enable security teams to anticipate potential attack vectors and prepare defenses in advance.
Regular threat reporting and predictive analytics provide visibility into the evolving threat landscape, allowing for informed risk assessments and proactive mitigation efforts.
Related content: Read our guide to threat intelligence services (coming soon)
Notable Threat Intelligence Tools
1. Exabeam
Exabeam integrates threat intelligence into the Security Operations Platform to improve detection, investigation, and response. The platform correlates logs and telemetry from endpoints, networks, identity systems, and cloud environments with curated threat intelligence feeds. This allows analysts to identify anomalous behaviors, enrich alerts with context, and uncover threats that traditional rule-based detection may miss.
Key Features Include:
- Integrated threat intelligence: Correlates firewall logs, endpoint data, and identity activity with external feeds to surface emerging threats.
- Behavioral analytics: Establishes baselines of normal user and entity activity, helping detect credential misuse, insider threats, and lateral movement.
- Automated investigation timelines: Links related events into a single view, reducing the time analysts spend piecing together incidents.
- Open integration ecosystem: Supports hundreds of connectors with SIEM, SOAR, and security products to unify threat intelligence across the SOC.
- Scalability and speed: Processes millions of events per second, ensuring intelligence is applied consistently at enterprise scale.
- Exabeam is often selected by organizations looking to strengthen SOC efficiency by combining behavioral analytics with actionable threat intelligence, reducing noise while accelerating investigations.
2. MISP

MISP (Malware Information Sharing Platform & Threat Sharing) is an open-source platform that supports threat intelligence sharing, storage, and correlation. It enables organizations to collect, organize, and analyze cyber threat information in a structured format. MISP simplifies the management of indicators of compromise (IOCs), threat actors, and attack campaigns.
Key features include:
- Automated correlation engine: Identifies links between indicators and threat attributes, using matching techniques like fuzzy hashing and CIDR matching.
- Structured threat intelligence storage: Stores atomic indicators and threat objects for technical and non-technical data.
- Flexible sharing mechanism: Allows control over data sharing using customizable distribution models and sharing groups.
- Visualization tools: Offers graph-based views of threat data, making it easier to identify relationships and understand threat contexts.
- Import/export support: Supports multiple formats including STIX, OpenIOC, CSV, Suricata, and Snort; enables integration with diverse tools.
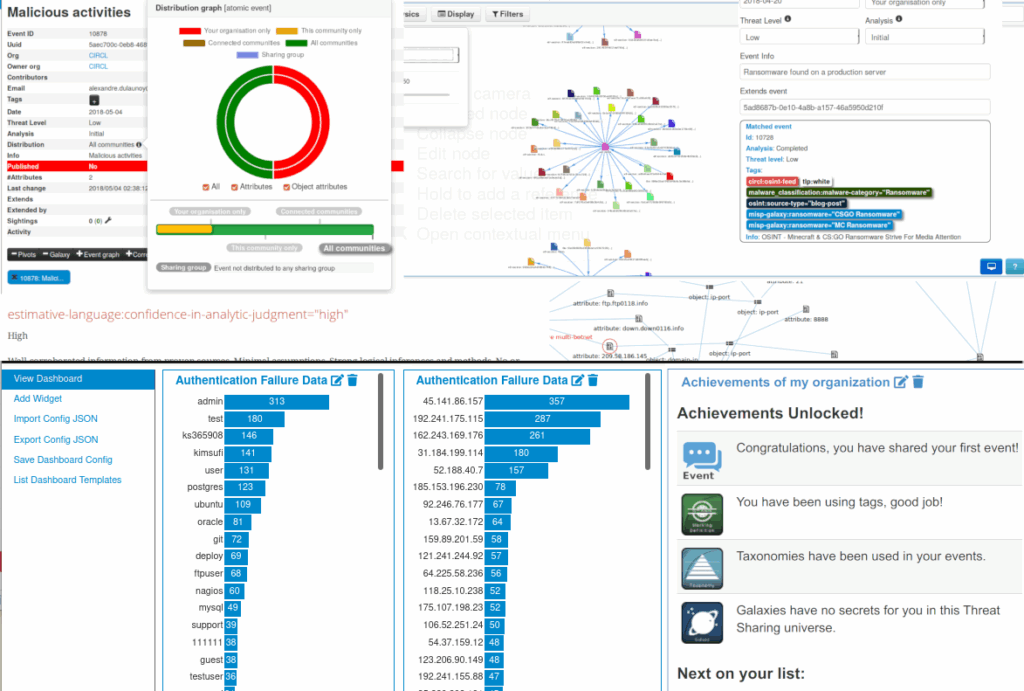
Source: MISP
3. CrowdStrike Falcon X Adversary Intelligence

CrowdStrike Falcon X Adversary Intelligence provides insights into threat actors, tools, and campaigns targeting specific industries or regions. It delivers tailored intelligence that enables organizations to defend against emerging threats and improve their threat-hunting capabilities.
Key features include:
- Threat actor profiles: Includes intelligence on adversary groups, their motivations, capabilities, and historical activity.
- Custom intelligence reporting: Delivers finished intelligence aligned to industry, geography, and relevant threats.
- Threat indicators and malware analysis: Provides IOCs and malware intelligence with technical context and behavioral analysis.
- Intelligence API: Enables automated access to threat data for integration with SIEMs, SOAR, and other security tools.
- Strategic and operational alerts: Issues early warnings and contextual insights into active threat campaigns.
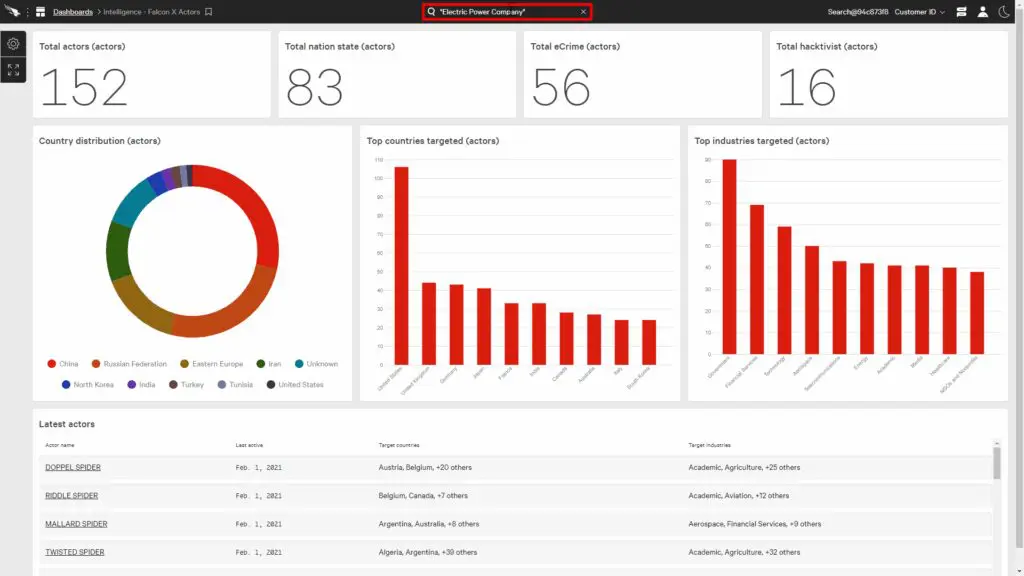
Source: CrowdStrike
4. Rapid7 Threat Command
Rapid7 Threat Command is a threat intelligence platform that focuses on external threat detection and remediation. It monitors the surface, deep, and dark web to uncover risks targeting an organization’s digital footprint, enabling faster mitigation of threats such as phishing, credential leaks, and brand impersonation.
Key features include:
- Digital risk protection: Identifies exposed credentials, domain impersonations, and leaked data across open and covert sources.
- Threat monitoring: Continuously scans web sources for real-time detection of external threats.
- Automated takedown support: Provides workflows to remove malicious content like fake domains or phishing pages.
- Alert prioritization: Filters out noise and delivers alerts relevant to the organization’s risk profile.
- Integrations: Supports integration with SIEMs, SOAR platforms, and ticketing systems for simpler incident handling.
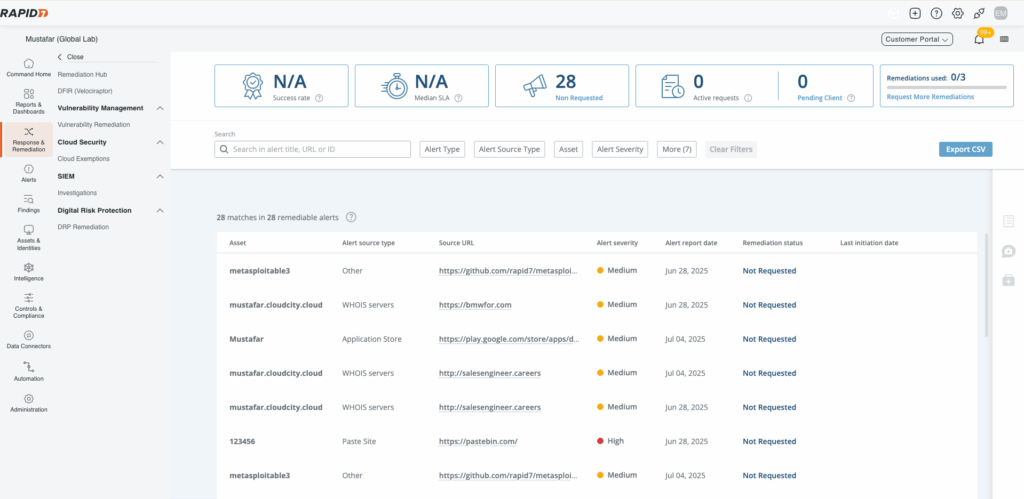
Source: Rapid7
5. Tenable Security Center
Tenable Security Center is a vulnerability and threat intelligence platform that combines asset discovery, vulnerability management, and threat context into a centralized dashboard. It helps organizations assess and manage cyber exposure by aligning threat data with internal network insights.
Key features include:
- Continuous vulnerability assessment: Scans assets for known vulnerabilities using Tenable’s Nessus technology.
- Threat intelligence integration: Correlates internal scan data with threat intelligence feeds to prioritize exploitable risks.
- Risk-based prioritization: Ranks vulnerabilities by severity, exploitability, and asset criticality.
- Custom dashboards and reporting: Provides tailored visualizations and compliance-ready reports.
- Integration capabilities: Connects with third-party tools for broader visibility and incident response coordination.

Source: Tenable
6. ThreatConnect

ThreatConnect is an AI-powered threat intelligence platform that enables organizations to operationalize cyber threat intelligence and quantify cyber risk. By unifying threat data from open-source, commercial, and internal sources, it supports cyber defense and risk-informed decision-making.
Key features include:
- Operationalized threat intelligence: Shifts from managing intel to actively applying it across security operations.
- Unified data access: Provides federated search and correlation across intel sources.
- AI-powered contextual analysis: Delivers insights by correlating threat indicators with organizational context to support informed decisions.
- Cyber risk quantification: Measures cyber risk in financial terms to prioritize defenses, demonstrate ROI, and support board-level reporting.
- Simplified intel management: Reduces complexity by centralizing threat feeds and automating intel processing and sharing.
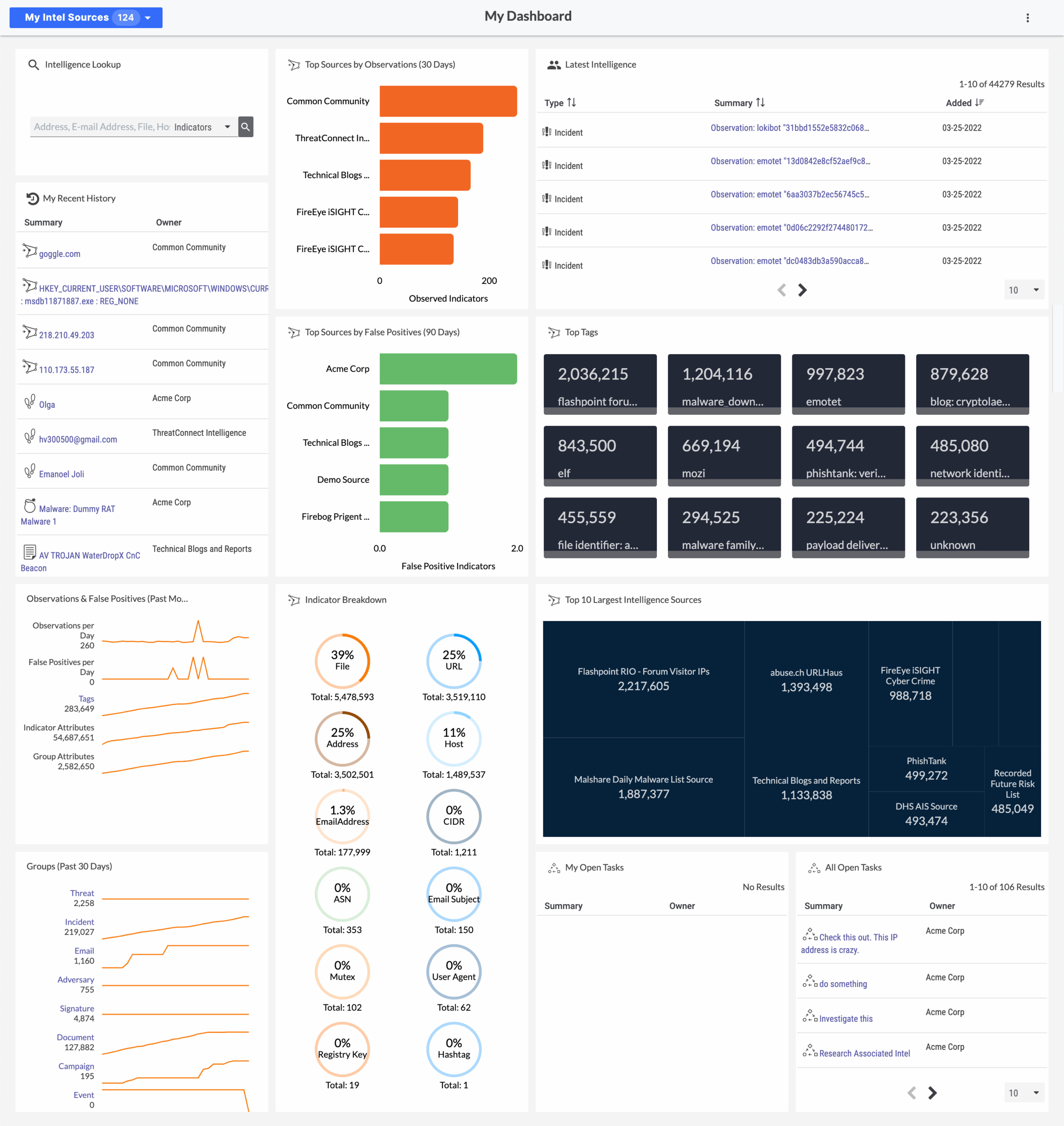
Source: ThreatConnect
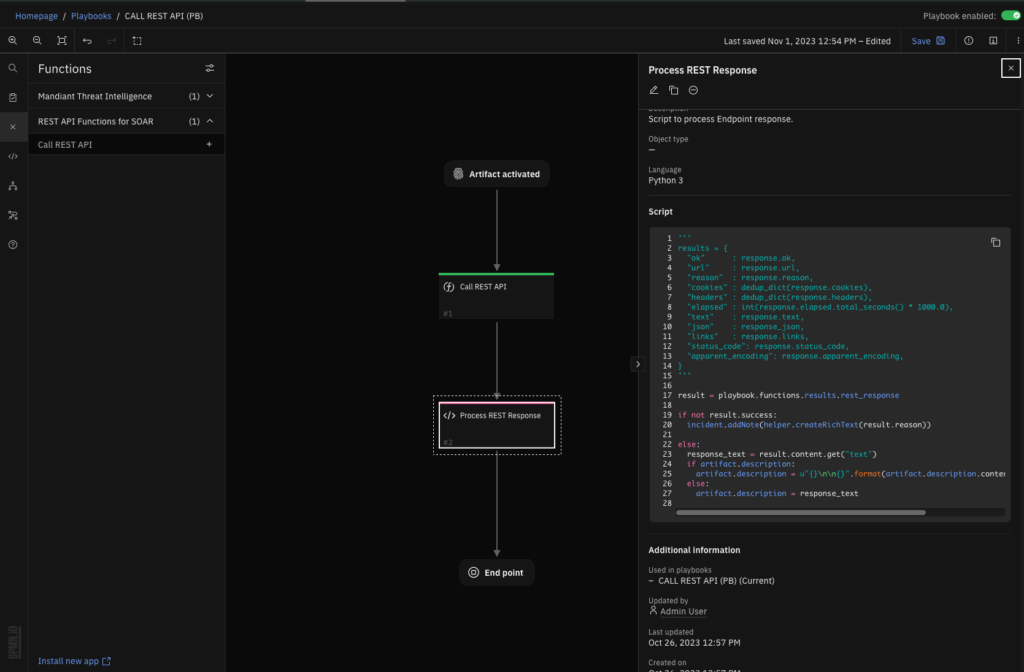
7. Anomali ThreatStream

Anomali ThreatStream is a threat intelligence platform that transforms raw threat data into insights tailored to the organization. It leverages a large repository of curated intelligence to contextualize emerging threats and automate response across the security stack.
Key features include:
- Global threat intelligence repository: Uses hundreds of diverse feeds including open-source, premium, and curated sources from Anomali Labs.
- Automated enrichment and correlation: Matches threat intelligence to the internal data, providing context-aware insights.
- Personalized dashboards and insights: Organization-specific views highlight the most relevant threats, campaigns, TTPs, and vulnerabilities.
- Automated threat distribution: Delivers machine-readable intelligence to security tools, enabling blocking and monitoring.
- MITRE ATT&CK mapping: Visual link analysis expands IOCs into high-level threat models, aiding in threat hunting and defense.
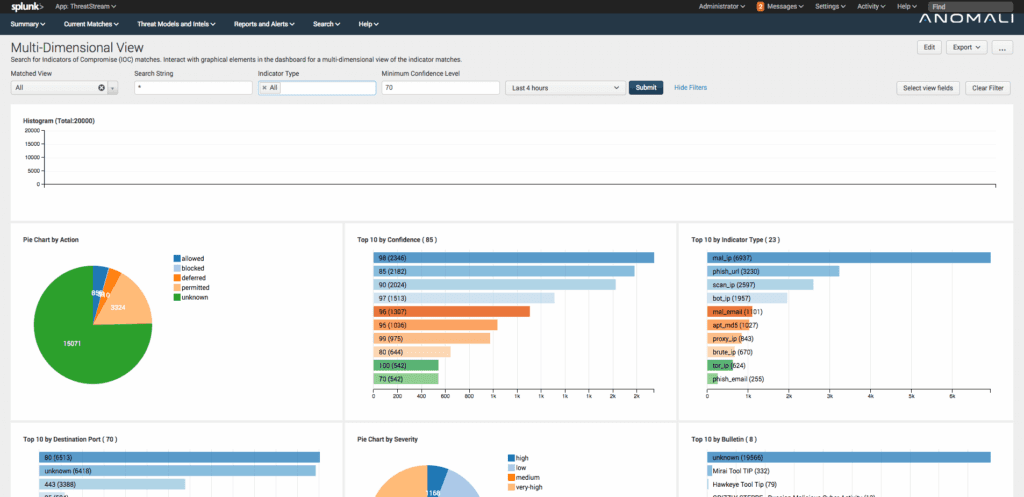
Source: Anomali
8. Recorded Future

Recorded Future is a threat intelligence platform that helps organizations identify, prioritize, and mitigate cyber threats. By combining machine learning with human analysis, it delivers contextual insights across threat activity—including actors, malware, and vulnerabilities—tailored to the industry, geography, and third-party relationships.
Key features include:
- Threat intelligence: Continuously updated intelligence sourced from data points across the web, including dark web monitoring.
- Threat landscape visualization: Interactive views of threat actors, malware, and vulnerabilities relevant to the organization and supply chain.
- Threat prioritization engine: Helps security teams focus on high-risk, exploitable threats with risk scores and contextual relevance.
- IOC enrichment and analysis: Includes indicators of compromise, sandbox analysis, and threat hunting packages to accelerate investigations.
- Tailored alerts and reporting: Custom alerts and visual reports based on geography, industry, and business context.

Source: Recorded Future
9. OpenCTI

OpenCTI (Open Cyber Threat Intelligence) is an open-source platform that centralizes, structures, and visualizes cyber threat intelligence in a way that supports both technical and strategic analysis. Built on the STIX 2 standard, it enables organizations to manage a knowledge base of threat actors, TTPs, indicators, victimology, and attribution.
Key features include:
- Structured threat intelligence modeling: Uses STIX 2 schema to organize both technical (e.g., IOCs, TTPs) and non-technical (e.g., attribution, motivation) threat data.
- Graph-based visualization: Offers a web-based interface for navigating relationships between entities and identifying threat patterns.
- Knowledge inference engine: Infers new connections from existing data, improving contextual understanding.
- Source attribution and metadata: Tracks provenance with features like source linking, confidence levels, and first/last seen dates.
- Integration with CTI ecosystem: Connectors available for MISP, TheHive, MITRE ATT&CK, and other major tools to simplify intelligence flow.

Source: OpenCTI
10. IBM X-Force Exchange
IBM X-Force Exchange is a threat intelligence platform that enables organizations to research global threats, share insights, and integrate threat intelligence into their security operations. It provides access to curated threat data, including indicators of compromise (IOCs), malware reports, and vulnerability information.
Key features include:
- Threat intelligence repository: Offers a continuously updated collection of IOCs, malware details, threat actor profiles, and vulnerability data.
- Collaborative sharing: Enables organizations to share intelligence with trusted peers and partners within private groups or with the public community.
- Search and analysis tools: Provides search capabilities and visual tools to analyze relationships between threat entities.
- API access and integrations: Supports API-based integration with SIEMs, SOAR platforms, and other security tools for automated threat data ingestion.
- Custom collections: Allows users to create and manage personalized threat collections.
Source: IBM
Conclusion
Threat intelligence tools have become essential components in modern cybersecurity strategies. By automating data analysis, integrating with existing systems, supporting collaboration, and providing clear visual insights, these tools empower organizations to stay ahead of evolving threats. They enable more efficient detection, faster incident response, and informed security decision-making.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.