Table of Contents
A firewall monitors traffic into and out of the environment it was developed to protect. Some firewalls also offer visibility into the source and type of traffic coming into this environment. A firewall is configured using rules. To be successful, the ruleset of a firewall must be augmented with a successful logging feature.
The logging feature records how the firewall manages traffic types. The logs provide organizations with information about, for example, source and destination IP addresses, protocols, and port numbers and can be used by a SIEM to help investigate an attack.
This content is part of a series about event logging.
Firewall Logging
A firewall, at its most basic form, is created to stop connections from suspicious networks. It inspects the source address, destination address, and the destination port of all connections, and decides if a network can be trusted.
For simplicity, we can aggregate information on the source address, source port, and destination address and port. We can view this information as an identifying quality of any attempt to connect, as tracked by the firewall.
This quality is similar to a set of rules that determine which connections are permitted and which must be denied. If this identifying quality holds information that is the same as a permitted connection, then the source address can create a connection with the destination address on the permitted port. Thus, the traffic is allowed into the network.
The success of any firewall, therefore, typically relies on the rules used to configure it.
The firewall monitors traffic into and out of the environment it was created to safeguard and provides visibility into the type and source of traffic entering this environment. It typically serves two purposes:
- Protecting the environment from threats from internal and external (Internet) sources
- Acting as an investigative resource for security professionals who need to track how a breach penetrated the firewall
To be most effective, a firewall ruleset must be augmented with a successful logging feature.
The logging feature documents how the firewall deals with traffic types. These logs offer insights into, for example, source and destination IP addresses, protocols, and port numbers.
When and why firewall logging is useful
- To see if new firewall rules work well or to debug them if they do not work properly.
- To discover if any malicious activity is occurring within your network. However, it doesn’t offer the information you need to isolate the source of the activity.
- If you identify repeated unsuccessful tries to access your firewall from a single IP address (or from a group of IP addresses), you may wish to create a rule to stop all connections from that IP.
- Outgoing connections derived from internal servers, for example, web servers, may show that someone is using your system as a launch pad. They could be launching attacks against computers on other networks from your system.
Linux Firewall Logs
The Linux kernel has a packet filtering framework called netfilter. This framework lets you permit, drop, and modify the traffic that comes in and out of a system. A tool, iptables furthers this functionality with a firewall, which you can configure using rules. Additional programs, like fail2ban, also rely on iptables to block attackers.
How does iptables work?
Iptables is a command-line interface to the packet filtering capabilities in netfilter. However, we won’t distinguish between iptables and netfilter for the purposes of this article. To keep things clear we will refer to the entire concept as iptables.
The packet filtering function offered by iptables is structured as tables, targets, and chains. Put simply, a table lets you process packets in a certain way. The filter table is the default table.
Chains are connected to these tables. You can monitor traffic at different points, using these chains. You can see traffic, as it arrives on the network interface or before it is passed over to a process. You can also add rules to the chains so that they match certain packets, for example, TCP packets going to port 70, and connect it to a target. A target will determine if the packet should be permitted or blocked.
When a packet enters or exits (according to the chain) iptables compares it against rules in these chains one at a time. When it identifies a match, it isolates the target and carries out the required action. If it doesn’t identify a match with any of the rules it carries out the action specified by the default policy of the chain. The default policy also acts as a target. By default, all chains have a policy of permitting packets.
Working with and interpreting iptable firewall logs
To create firewall logs, the kernel needs to be firewall logging enabled. By default, matched packets are logged as kern.warn (priority 4) messages. You can change the log priority with the --log-level option to -j LOG.
The majority of the IP packet header fields are disclosed when a packet matches a rule with the LOG target. By default, firewall log messages are written to /var/log/messages.
Windows Firewall Logs
Microsoft Windows has a built-in firewall. The firewall does not log any traffic, by default. However, you can choose to configure the firewall to log connections that are permitted and traffic that is dropped. If you authorize Windows firewall logging, it creates “pfirewall.log” files in its directory hierarchy. You can see the Windows firewall log files via Notepad.
How to enable windows 10 firewall logs
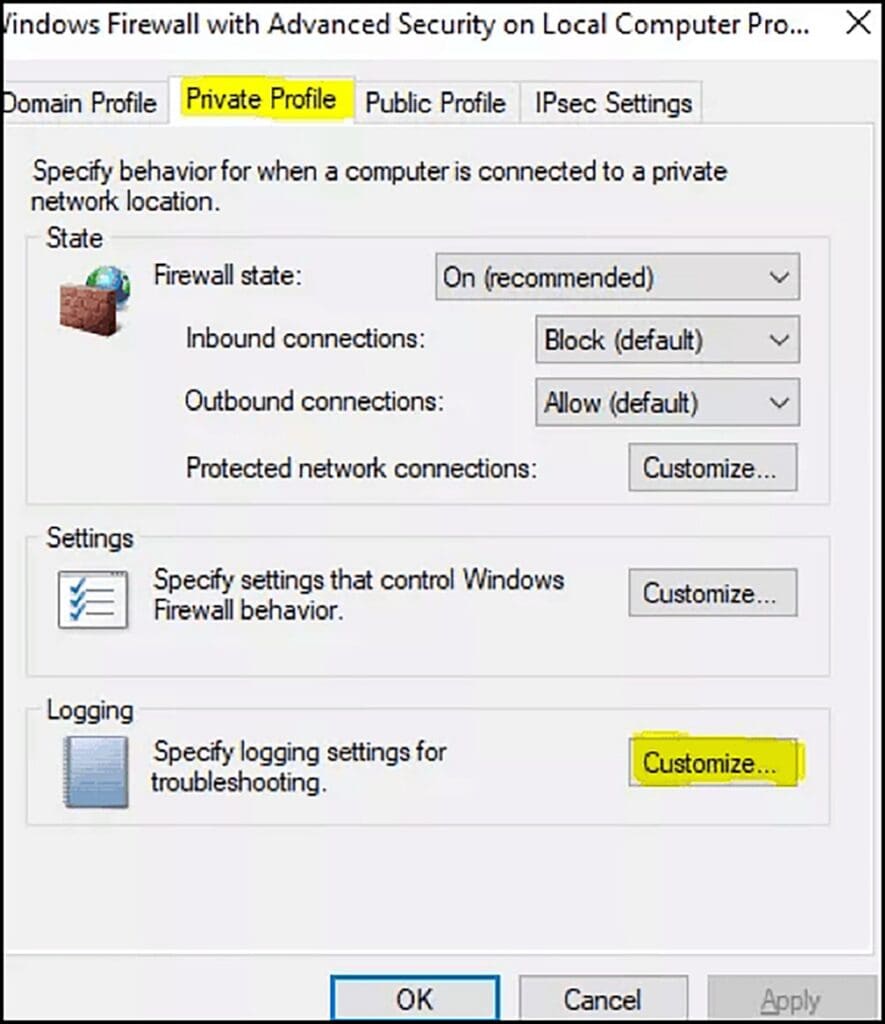
Go to Windows Firewall with Advanced Security. Right-click on Windows Firewall with Advanced Security and click on Properties.

The Windows Firewall with Advanced Security Properties box should appear.
You can move between Domain, Private, and Public Firewall profiles. Generally, you should configure the Domain or Private Profile. Let’s see how to create Windows Firewall logging on a Windows Firewall Private Profile. The steps below will work both for a public profile or a domain.
Click Private Profile > Logging > Customize
Go to “Log Dropped Packets” and switch to Yes
Generally, we turn on logging for “Log Dropped Packets” only. We won’t log successful connections as successful connections generally are not so helpful when resolving problems.
Copy the default path for the log file. ( %systemroot%\system32\LogFiles\Firewall\pfirewall.log ) and then Press OK
Open File Explorer and go to where the Windows Firewall log is kept. ( %systemroot%\system32\LogFiles\Firewall\) . You will see, in the Firewall folder, a pfirewall.log
Copy the pfirewall.log to your desktop. This will let you open the file with no firewall warnings.
Interpreting the windows firewall logs
Your Windows Firewall log will look something like the following:
Here is an analysis of the key aspects of the above log:
- The time and date of the connection.
- What became of the connection. “Allow” means the firewall permitted the connection, while “drop” means it has prevented it.
- The kind of connection, TCP or UDP.
- The IP of the source of the connection (your PC), the IP of the destination (your desired recipient, e.g. a webpage), and the port used on your computer. You can use this to identify any ports that need opening for software to work. You should also look out for any suspicious connections, as they may indicate malware.
- Tells you if this connection was your computer receiving a packet of data or sending one.
Read detailed explainer about log aggregation.
How to Analyze Firewall Logs
Firewall logging, especially of permitted events, can be helpful for discovering potential network security threats. An organization generally places strict protection on assets that should not be freely accessible. These may include internal corporate networks and the workstations of employees. Typically, no unmediated inbound connection to these systems is allowed.
What to look for when performing firewall log analysis
Once you have gathered the firewall logs and started the process of analyzing the logs, you can decide what to look for in the log. You should refrain from only looking for “harmful” events. Your firewall logs not only help you isolate compromises and incidents, but they can also help you specify the normal operations of the firewall.
One way to see whether the behavior that has been logged is suspicious is to see what the normal operations are and then to note the exceptions.
Some events should always cause suspicion and prompt further investigation. They are as follows:
- Authentication permitted
- Traffic dropped
- Firewall stop/start/restart
- Firewall configuration modifications
- Administrator access granted
- Authentication failed
- Administrator session ceased
Log Analysis and Alerting with Exabeam
Log Management and Next Generation SIEMs
Log management is challenging, and it is becoming increasingly so with the rapid growth of network devices, microservices and cloud services, endpoints, and the vast increase in data and traffic volumes.
Next-generation Security Information and Event Management (SIEM) solutions can assist you with your management of security-related log events and help you learn about events that are relevant to a security incident.
Features of next-generation SIEMs:
- Security data lake, which can retain unlimited data volumes of historical logs
- User and entity behavioral analytics technology for improved threat detection via behavior analysis.
- Automated incident response capabilities, which provide service integrations via playbooks for automated investigation, containment, and mitigation of incidents.
- Advanced data exploration features, which can assist security analysts with their threat hunting activity, by examining logs.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
-
 Blog
Blog Five Reasons Security Operations Teams Augment Microsoft Sentinel With New-Scale Analytics
- Show More