Compromised Credentials
Brief
Outsmart credential-based attacks
Most adversaries don’t break in; they log in. Stolen credentials for both human users and AI agents are a primary vector for modern attacks, allowing adversaries to bypass perimeter defenses and operate undetected within your environment.
Investigating these attacks with traditional SIEMs is a slow, manual process. Analysts are forced to run dozens of queries to chase alerts, struggling to connect the subtle activities that signal a real threat, from a stolen token to an employee pasting sensitive data into an AI tool.
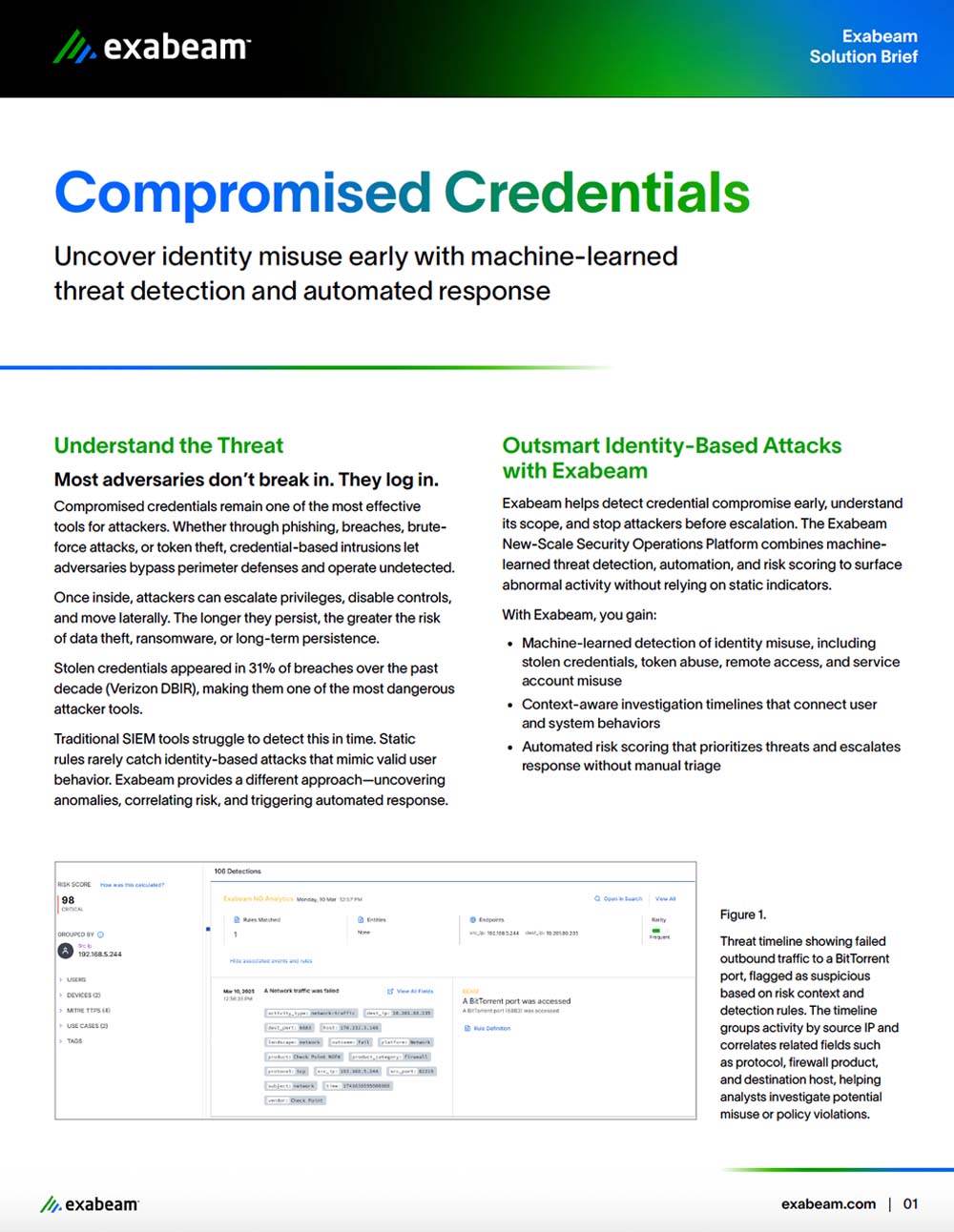
Exabeam delivers a new approach. We apply behavioral analytics to baseline normal user activity and monitor the behavior of autonomous AI agents, helping your team prioritize credible threats. Our multi-agent AI system automates investigation and response, giving your team a clear, context-rich timeline to stop credential-based attacks before they become a breach.