
Table of Contents
What Is a SOAR Platform?
A SOAR (security orchestration, automation, and response) platform centralizes, automates, and simplifies key security operations tasks. These tools connect disparate security solutions, collect and correlate data from multiple sources, and automate response procedures according to predefined workflows.
By integrating threat detection, data analysis, case management, and reporting, SOAR platforms help security teams quickly identify, investigate, and resolve incidents. This orchestration reduces the need for manual intervention, allowing organizations to respond to threats with higher speed and consistency.
Modern SOAR solutions focus on integrating with other security tools and infrastructure. They act as a bridge between security information and event management (SIEM), threat intelligence sources, endpoint protection, and ticketing systems. The result is a holistic view of the threat
landscape, tighter process control, and better collaboration across incident response teams.
Core Components of SOAR Platforms
Data Aggregation and Normalization
SOAR platforms ingest data from a variety of sources, including security appliances, network logs, endpoint agents, and external threat feeds. This aggregation is critical for building a unified picture of potential threats, as it pulls otherwise siloed data into a central repository. However, this information is rarely uniform in its original state; logs and alerts differ in structure, terminology, and significance depending on the originating tool. To make this data actionable, SOAR platforms normalize it into a consistent format.
This process involves parsing, categorizing, and mapping fields so that disparate data sources can be meaningfully compared and correlated. By normalizing data, SOARs ensure that automated workflows and analytics function reliably across diverse inputs, reducing the risk of errors and missed detections caused by inconsistent data.
Playbooks and Workflow Automation
Playbooks are defined, repeatable response procedures encoded within a SOAR platform to automate security tasks and incident handling. These playbooks dictate what steps the system should take when certain events or alerts are triggered. For example, a phishing playbook might automate tasks like isolating a compromised endpoint, extracting malicious indicators, searching for similar events, and sending notifications to affected users.
Workflow automation, enabled by playbooks, can span simple alert triage to complex, multi-step investigations. Automation also allows for escalation rules, approvals, and human-in-the-loop options when necessary. By orchestrating repeatable workflows across integrated security tools, SOAR platforms ensure that best practices are consistently applied, freeing analysts from repetitive tasks and enabling them to focus on higher-value activities.
Case Management and Collaboration
Effective incident response requires detailed tracking and communication between analysts, teams, and departments. SOAR platforms provide case management functionality, turning each security alert or incident into a tracked case with associated data, actions, notes, and audit trails. All relevant information about an incident (emails, logs, response steps, and supporting documentation) is centralized within the platform, enabling efficient oversight and accountability.
Collaboration tools within SOARs enable real-time communication and information sharing so teams can coordinate their efforts. This is particularly crucial for complex incidents involving multiple stakeholders or organizational units. Shared workspaces, notifications, and role-based access control support cross-team collaboration, ensuring transparency and smooth handoffs.
Threat Intelligence Integration
Integrating threat intelligence into the SOAR ecosystem enriches incident context and improves decision-making. SOAR platforms support connectors for multiple threat intelligence sources (commercial feeds, open-source indicators, and sector sharing organizations) allowing them to aggregate and correlate external indicators with internal events in real time.
Automated enrichment of logs and alerts with reputation scores, threat actor profiles, and tactics, techniques, and procedures (TTPs) helps analysts quickly assess the severity and relevance of threats. By cross-referencing live incidents with intelligence data, SOAR platforms simplify processes like assigning priority, automating enrichment, and generating actionable insights.
Reporting, Dashboards, and KPIs
Visibility into security operations is vital for both day-to-day management and strategic planning. SOAR platforms offer reporting features, including customizable dashboards that provide real-time overviews of incident trends, response times, workflow efficiencies, and key performance indicators (KPIs). These dashboards allow security teams and leadership to monitor SOC health, identify bottlenecks, and demonstrate value to stakeholders.
Automated reports can be scheduled or triggered on demand, encompassing metrics such as incident counts, mean time to resolve (MTTR), threat types, and playbook execution rates. This transparency not only improves operational awareness but also supports compliance requirements by maintaining a detailed audit trail of actions taken during incident response.
Key Benefits of SOAR Platforms
A SOAR platform offers improvements to the efficiency, consistency, and effectiveness of security operations. By combining orchestration, automation, and centralized management, SOAR platforms help security teams overcome common operational challenges and better manage today’s complex threat landscape.
Key benefits include:
- Faster incident response: Automated workflows allow for near-instant response to known threats, drastically reducing mean time to detect (MTTD) and mean time to respond (MTTR). This enables containment and mitigation before threats escalate.
- Reduced analyst fatigue: OAR platforms triage and filter alerts, prioritize high-risk incidents, and eliminate noise from false positives. This helps analysts focus on meaningful threats, reducing burnout and alert fatigue.
- Consistent and repeatable processes: Playbooks ensure that incident handling follows standardized procedures, minimizing variation in response quality and ensuring compliance with organizational policies.
- Improved collaboration and transparency: Centralized case management and shared workspaces enable teams to coordinate in real time, maintain full audit trails, and ensure smooth handoffs during multi-team investigations.
- Scalability without hiring: Automation handles repetitive tasks at scale, allowing organizations to grow their security coverage without increasing headcount or overloading current staff.
- Better use of threat intelligence: Integrated enrichment tools correlate internal data with external intelligence, providing context that improves detection accuracy and speeds up decision-making.
- Enhanced reporting and metrics: Real-time dashboards and automated reports provide visibility into SOC performance, support compliance, and help justify investments in security programs.
Notable SOAR Platforms
1. Exabeam

Exabeam combines SIEM, UEBA, and built-in automation to streamline threat detection, investigation, and response. It unifies telemetry from identity systems, endpoints, networks, cloud services, and threat intelligence into a single analytics layer, then automates investigations and playbook-driven actions. The Nova agentic AI accelerates case summaries, suggests next steps, and helps analysts prioritize response while low-code playbooks orchestrate actions across the stack.
Key features include:
- Integrated SIEM and SOAR: Exabeam’s SIEM provides advanced log management and behavioral analytics that feed its automation capabilities. Detections can trigger standardized response workflows, allowing analysts to move from alert to action without switching tools.
- Low-code playbooks and workflow automation: Prebuilt and customizable playbooks enable rapid containment, eradication, and recovery. Analysts can view, modify, and reuse workflows to match evolving threats and operational preferences.
- Agentic AI for faster TDIR: Nova’s agentic AI automatically summarizes cases, classifies threats, identifies attack paths, and recommends next steps, reducing mean time to respond and improving consistency.
- Behavioral analytics and risk-based prioritization: Exabeam’s UEBA models typical user and entity behavior to establish baselines. When deviations occur, it assigns dynamic risk scores that help analysts focus on the most critical threats and automate related responses.
- Broad ecosystem integrations: The platform connects with EDR, NDR, IAM, cloud security, and ticketing systems to enrich alerts and execute response actions such as account lockdown, device isolation, or policy updates.
- Incident response at scale: Machine-built timelines, guided investigations, and automated workflows reduce manual effort throughout the entire detection and response lifecycle.
Exabeam’s combined SIEM and SOAR approach gives organizations unified visibility and automation across their environments, enabling faster, more accurate, and more scalable security operations.
2. Cyware SOAR

Key features include:
- Cloud and on-premise automation: Unified automation across hybrid infrastructure using a lightweight agent, without requiring exposure to external traffic.
- Low-code automation: Drag-and-drop interface with over 100 pre-built templates and a visual playbook editor for fast deployment of automation workflows.
- ISAC threat intel integration: Automates ingestion and actioning of threat intel shared by ISACs into detection and response systems.
- Vendor-agnostic orchestration: Decoupled architecture supports integration with any third-party tools across cybersecurity, IT, and DevOps without platform lock-in.
- Centralized case and threat management: Single-window interface to manage incidents, vulnerabilities, malware, and threat actors with role assignment, visualization, and SLA tracking.
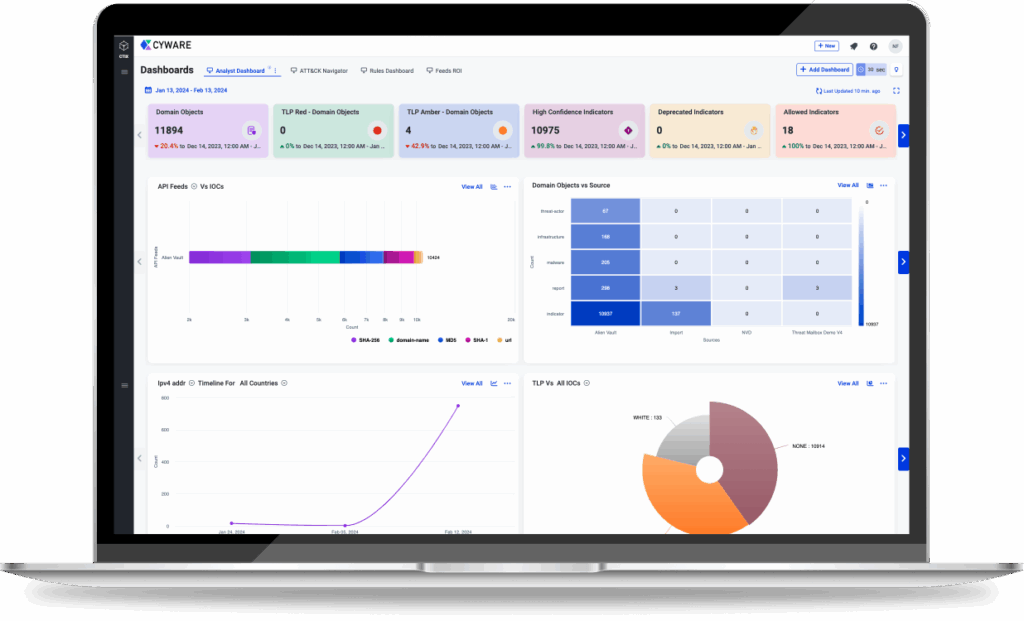
Source: Cyware
3. Microsoft Sentinel

Microsoft Sentinel combines SIEM and SOAR capabilities to help security teams automate threat detection and response tasks across their environments. It allows organizations to reduce manual workload by automating enrichment, triage, and remediation workflows. Sentinel supports automation rules and customizable playbooks to handle incidents and alerts.
Key features include:
- Transition to Defender portal: Enhanced experience with unified automation across Microsoft Sentinel and Microsoft Defender XDR, though some manual features differ from the Azure portal.
- Automation rules: Centralized configuration for incident and alert handling, allowing tagging, assignment, closure, and complex response flows across multiple analytics rules.
- Playbooks via Logic Apps: Custom workflows for threat response using Azure Logic Apps, enabling integration with both Microsoft and third-party systems.
- Flexible triggering: Playbooks can run automatically on alerts or incidents, or be triggered manually when supported.
- Incident correlation engine: Merges related alerts into single incidents, simplifying automation and reducing duplication in responses.

Source: Microsoft
4. Splunk SOAR

Splunk SOAR is a security orchestration, automation, and response solution to unify security operations and accelerate incident response. Now integrated natively within Splunk Enterprise Security, it connects over 300 third-party tools and supports more than 2,800 automated actions to simplify security workflows without disrupting existing infrastructure.
Key features include:
- Threat intelligence: Prioritize threats using intelligence from the Splunk Threat Research Team, integrated into the investigation interface for faster decision-making.
- Automated playbooks: Execute automated workflows using prebuilt or custom playbooks aligned to SOC tasks and MITRE ATT&CK/D3FEND frameworks.
- App integrations: Connect with over 300 security and IT tools and leverage over 2,800 automated actions to orchestrate across the existing security stack.
- Visual playbook editor: Build and customize workflows with a drag-and-drop interface that supports both low-code and advanced scripting for scalable automation.
- Integrated case management: Segment and assign tasks using custom or standardized templates, ensuring a collaborative, auditable, and organized incident response process.
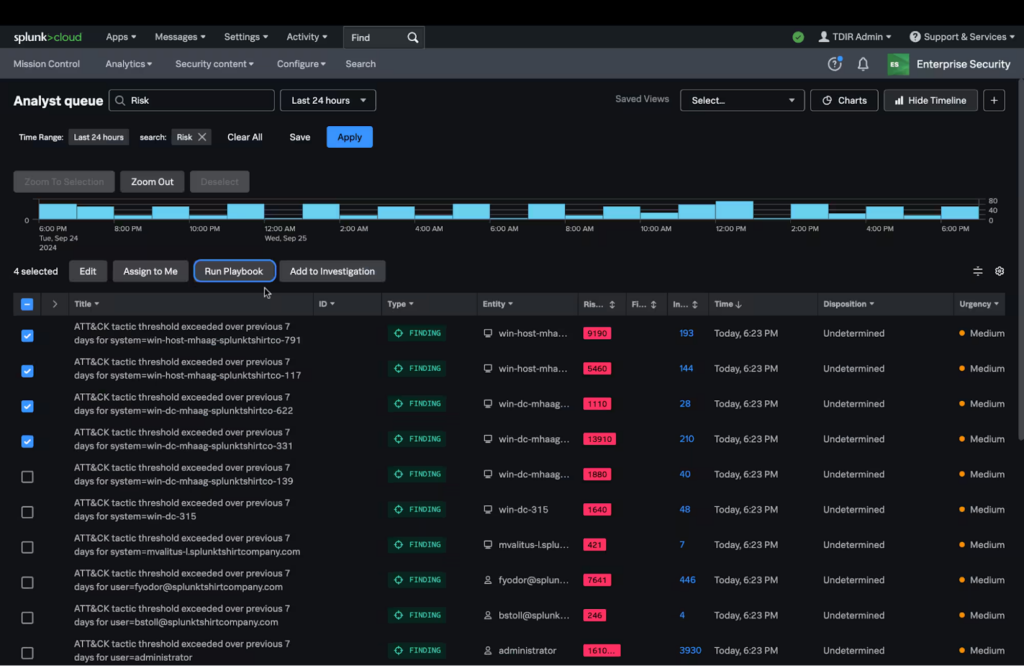
Source: Splunk
5. Palo Alto Cortex XSOAR

Cortex XSOAR by Palo Alto Networks is a SOAR platform to automate, orchestrate, and accelerate incident response. Designed with an automation-first approach, XSOAR helps security operations centers (SOCs) reduce manual work, simplify investigations, and centralize response efforts across teams and tools.
Key features include:
- Cross-stack orchestration: Coordinate security workflows across SIEM, EDR, firewalls, and ITSM platforms without disrupting existing infrastructure.
- Automation-first workflows: Automate alert triage, threat enrichment, and remediation tasks using built-in security actions and content packs.
- Visual playbook editor: Create and customize automation workflows without writing code, using a drag-and-drop interface that supports a range of use cases.
- Integrated investigation war room: Centralized view for analysts to investigate incidents, manage tickets, collaborate in real-time, and perform post-incident analysis.
- Threat intelligence correlation: Automatically map external threat data to SOC incidents to accelerate decision-making and response prioritization.

Source: Cortex
How to Evaluate SOAR Platforms
When evaluating SOAR platforms, organizations should consider both technical capabilities and operational fit. The right solution must align with existing infrastructure, support future scalability, and deliver measurable improvements to security operations. Key evaluation criteria include:
- Integration ecosystem: A SOAR platform’s value depends on how well it integrates with existing tools such as SIEM, EDR, NDR, firewalls, ticketing systems, and threat intelligence feeds. Evaluate the number of prebuilt connectors, API flexibility, and vendor neutrality. Platforms with extensive out-of-the-box integrations reduce deployment effort and enable faster ROI.
- Playbook flexibility and automation depth: Examine how playbooks are created and maintained. Low-code or visual editors enable wider team adoption, while scripting support allows advanced customization. Look for conditional logic, human-in-the-loop checkpoints, and support for both simple and multi-step workflows. The depth of automation directly impacts the speed and consistency of incident response.
- Case management and collaboration: A strong SOAR platform should provide centralized case management with role-based access, task assignments, audit trails, and integration with ITSM tools. Collaboration features such as shared workspaces, real-time notifications, and comment tracking are essential for multi-team or cross-department investigations.
- Threat intelligence handling: Assess how the platform ingests, normalizes, and applies threat intelligence. The ability to automatically enrich alerts with contextual data, correlate indicators across environments, and prioritize based on risk helps analysts make faster, more accurate decisions.
- Reporting and metrics: Dashboards and KPIs should provide visibility into SOC performance, mean time to respond (MTTR), automation success rates, and incident trends. Ensure reporting capabilities can be customized for both operational monitoring and executive-level summaries, with export options for compliance requirements.
- Scalability and performance: The platform should handle the volume of alerts and integrations expected in your environment. Consider how it scales across hybrid and cloud deployments, as well as its performance impact on security operations teams during high-volume incidents.
- Usability and learning curve: Evaluate the user experience, from interface design to workflow clarity. Platforms that are intuitive and provide guided setup reduce training time and speed up adoption across SOC teams.
- Cost and licensing model: Understand the pricing structure, whether it is based on users, data volume, or number of integrations, and match it against projected usage. Transparent licensing is critical to avoid cost overruns as automation expands.
Conclusion
SOAR platforms are now central to modern security operations, helping organizations address the scale and complexity of today’s threats with automation, orchestration, and centralized management. By unifying data, standardizing workflows, and enabling faster, more accurate responses, they allow SOCs to operate more efficiently and effectively. Their ability to integrate diverse tools, reduce analyst workload, and provide measurable visibility into performance makes them a critical enabler of resilience and maturity in security operations.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.