
- Home >
- Blog >
- InfoSec Trends
FireEye and SolarWinds Cyber Attack: Information for Exabeam Customers and Partners
- Dec 16, 2020
- Ralph Pisani
- 4 minutes to read
Table of Contents
By now you’ve heard of the supply chain attack on the SolarWinds Orion Platform, made public by FireEye on December 8, 2020. FireEye, U.S. governmental agencies, and other global entities were all involved in this highly-sophisticated attack. As a cybersecurity vendor, we know how hard it is when a breach happens – especially one perpetrated by a well-funded, state-sponsored actor. Like all cybersecurity vendors, we’re committed to helping our customers secure their organizations and address security incidents. FireEye has quickly addressed this breach and provided much information on steps for detection and remediation.
We just released new detection rules specific to this attack which customers can access through their Community page. As always Exabeam is here to support you. Our OOTB capabilities can be used to help identify similar incidents in your environment.
Information for Exabeam customers and partners
Based on information that FireEye has shared on “Post Compromise Activity and Detection Opportunities,” here is how parts of the attack unfolded.
“The attacker used multiple IP addresses per VPS provider, so once a malicious login from an unusual ASN is identified, looking at all logins from that ASN can help detect additional malicious activity. This can be done alongside baselining and normalization of ASN’s used for legitimate remote access to help identify suspicious activity.”
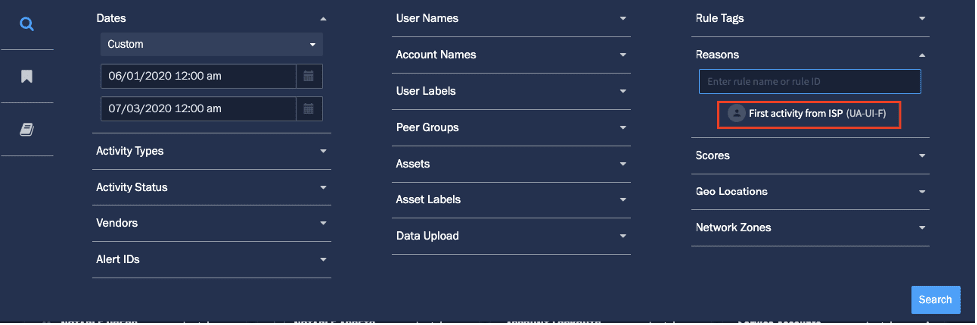
Exabeam take: The attacker optimized their IP addresses based on the victim’s country. This was done to avoid detection. We recommend finding the first and abnormal activity from the ISP.
“Once the attacker gained access to the network with compromised credentials, they moved laterally using multiple different credentials. The credentials used for lateral movement were always different from those used for remote access.”
Exabeam take: Lateral movement using different credentials is a technique of the attack. As accounts were switched in this attack, using lateral movement rules will help with tracing the timeline of the attack.
Here is MITRE’s guidance on lateral movement detection:
Correlate use of login activity related to remote services with unusual behavior or other malicious or suspicious activity. Adversaries will likely need to learn about an environment and the relationships between systems through discovery techniques prior to attempting lateral movement.
![“DGA and Blocklists: The backdoor determines its C2 server using a Domain Generation Algorithm (DGA) to construct and resolve a subdomain of avsvmcloud[.]com. The Update method is responsible for initializing cryptographic helpers for the generation of these random C2 subdomains.”](https://cdn-ilemogb.nitrocdn.com/hxeNzoFtzCLhholgTkBlCriLCctWhMdW/assets/images/optimized/rev-130b55a/www.exabeam.com/wp-content/uploads/BLOG-fireeye-and-solarwinds-cyber-attack-information-for-exabeam-customers-and-partners-fe-sw-2-inpage-01.png)
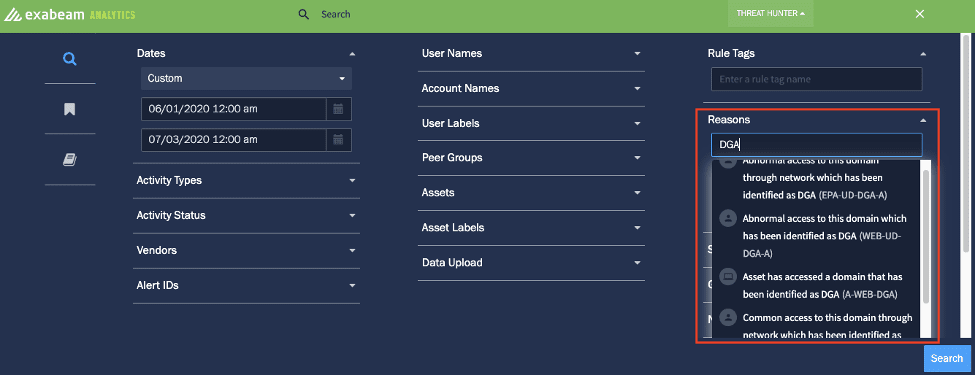
“DGA and Blocklists: The backdoor determines its C2 server using a Domain Generation Algorithm (DGA) to construct and resolve a subdomain of avsvmcloud[.]com. The Update method is responsible for initializing cryptographic helpers for the generation of these random C2 subdomains.”
Exabeam take: We have a number of DGA-related rules for customers to use that auto-detect DGAs, e.g. “cnn[.]com” compared to “xhibfwda[.]com“. We group this with other granular, contextual information so you can investigate in a comprehensive manner. DGA is one of Exabeam’s contributions to the ATT&CK framework that has been accepted by MITRE as T1483. This technique was cited in FireEye’s list of observed MITRE ATT&CK techniques.
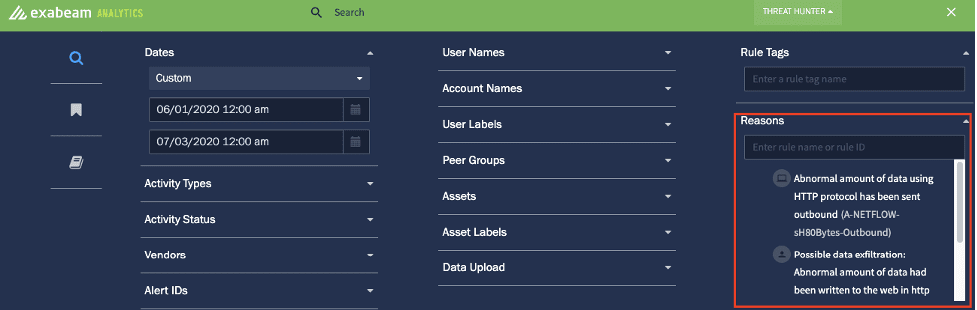
In HTTP Command and Control (C2) Communication/Data Exfiltration, “The HTTP thread begins by delaying for a configurable amount of time that is controlled by the SetTime command. The HTTP thread will delay for a minimum of 1 minute between callouts. The malware uses HTTP GET or HEAD requests when data is requested and HTTP PUT or HTTP POST requests when C2 output data is being sent to the server. The PUT method is used when the payload is smaller than 10000 bytes; otherwise the POST method is used.”
Exabeam take: The varying delay between calls means you can’t build a correlation rule for this. But data exfiltration could be detected in the abnormal amount of data being sent outbound using the HTTP protocol. Exabeam gives you visibility into abnormal amounts of data uploaded to the web in HTTP GET requests as you conduct your investigation.
Keeping your network safe
If you think you may have been affected in a similar way, here are the known attacker techniques according to FireEye’s reporting. Below you will find the Exabeam detections for these known TTPs.
| Attacker TTPs | Exabeam OOTB detections |
| The attacker used multiple IP addresses per VPS provider, so once a malicious login from an unusual ASN [ISP] is identified | First/abnormal activity from ISP for (user, peers, org) |
| Once the attacker gained access to the network with compromised credentials, they moved laterally using multiple different credentials. | First/Abnormal access to asset for (user, peers, org) Abnormal number of hosts accessed for (user, peers, org) Abnormal number of failed logins for (user, peers, org) First RDP/SSH for (user, peers, org) First Credential switch for user |
| They routinely removed their tools, including removing backdoors once legitimate remote access was achieved. Defenders can monitor existing scheduled tasks for temporary updates, using frequency analysis to identify anomalous modification of tasks. | First scheduled task creation for (user, peers, org) Usual process for scheduled task First scheduled task created on host Scheduled task created at an unusual time |
| The backdoor determines its C2 server using a Domain Generation Algorithm (DGA) to construct and resolve a subdomain of avsvmcloud[.]com | First access to a domain that has been identified by Exabeam as DGA (Exabeam MITRE contribution) |
| HTTP C2 Communication / Data Exfiltration | Abnormal amount of data using HTTP protocol has been sent outbound Possible data exfiltration: Abnormal amount of data had been written to the web in HTTP GET requests Abnormal amount of data uploaded to the web |
We’re here for you
Customers can now access new detection rules specific to this attack through their Community page. We have also released a saved searches package for this breach for Data Lake. Exabeam is here to partner with your organization to help you meet your security needs. If you have any cybersecurity-related questions or just want to talk with a security expert about this or any other security concerns, don’t hesitate to reach out.
Ralph Pisani
President | Exabeam | Ralph Pisani is President of Exabeam. Ralph leads all global sales and marketing go-to-market functions at Exabeam. With 20 years of experience in sales, channel, and business development, he is widely recognized as one of the top security sales leaders in Silicon Valley. Prior to Exabeam, Ralph led the worldwide sales organization at cybersecurity firm Imperva from early stage through the company’s successful IPO. Prior to Imperva, he served as Vice President of Worldwide OEM Sales at SecureComputing (acquired by McAfee) and Regional Vice President of Sales and Vice President of Channel and Business Development for CipherTrust (acquired by SecureComputing). Ralph also has held global sales leadership roles with Sophos, Inc., HR Logic, Inc. and EMDS Consulting, Inc. He has a B.A. in Business from Bentley University.
More posts by Ralph PisaniLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.

