
OWASP Defines AI Agent Risk. Behavioral Analytics Detects It
- Apr 22, 2026
- Kevin Binder
- 3 minutes to read
Table of Contents
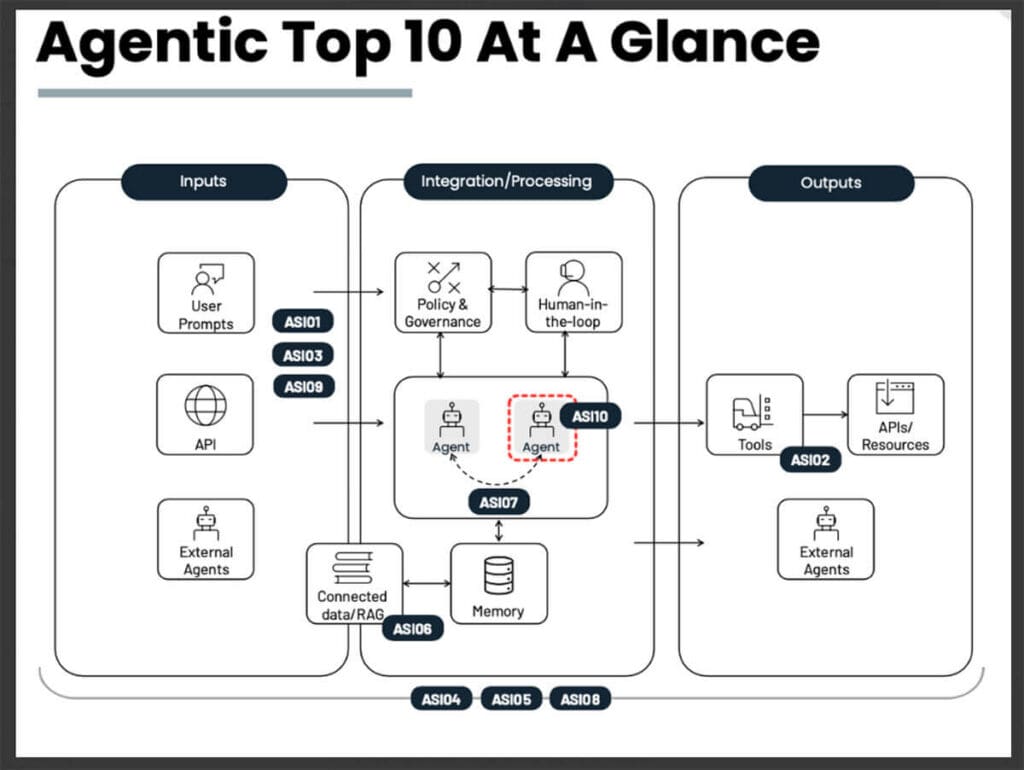
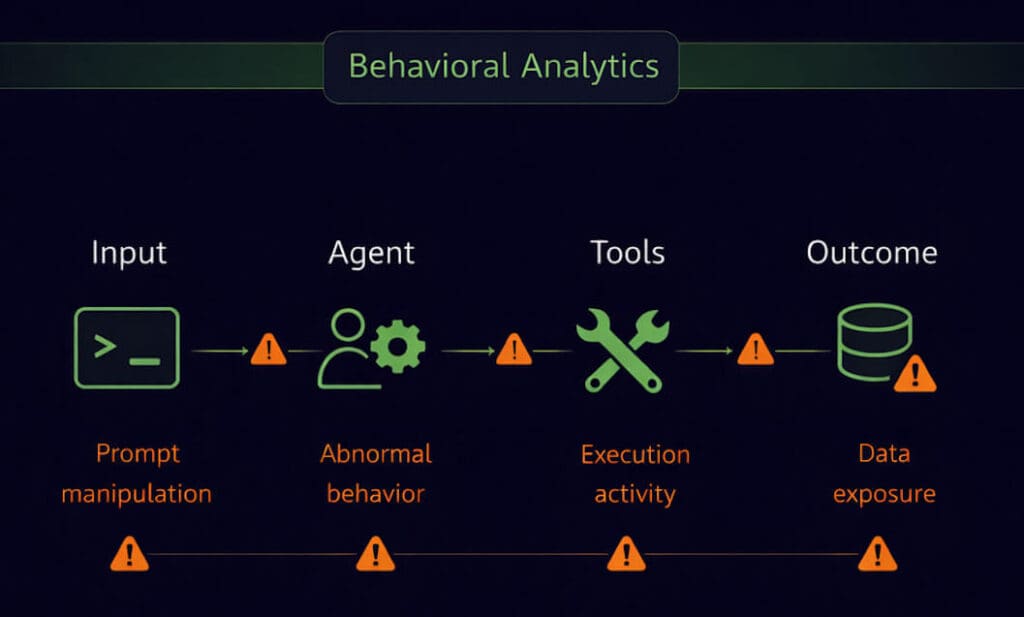
The OWASP Top 10 for Agentic Applications defines the most common AI agent risks, but real attacks unfold across multiple stages of behavior. Behavioral analytics detects those risks by modeling how users, AI agents, and their interactions change over time. By observing deviations across inputs, processing, and outputs, security operations teams can identify insider‑driven and agent‑driven threats that traditional, event‑based detection misses.
How Behavioral Analytics Detects OWASP Agentic Risk
Behavioral analytics detects AI agent risk by modeling normal behavior for users, agents, and their interactions, then identifying meaningful deviations across the AI lifecycle. This approach reveals insider‑driven misuse, rogue agent behavior, and compounding risk patterns that align with the OWASP Top 10 for Agentic Applications.
Why This Matters
AI agents operate with valid credentials and increasing autonomy, which makes misuse difficult to detect with rules alone. Security operations teams need a way to identify risk that develops over time, especially when actions appear authorized in isolation. Behavioral analytics provides that visibility, helping teams detect insider‑driven and agent‑driven risk earlier in agentic environments.
Key Takeaways
- OWASP agentic risks emerge through sequences of behavior, not single events, which limits the effectiveness of static rules.
- Behavioral analytics detects risk by learning how users and agents normally behave and flagging deviations.
- Insider threat detection now includes AI agents acting with legitimate access.
- Visibility across inputs, processing, and outputs reveals how small actions compound into impact.
From OWASP Risk to Behavioral Detection
The OWASP Top 10 for Agentic Applications categorizes risks such as prompt manipulation, excessive privileges, rogue agents, and tool misuse. In practice, these risks do not appear as isolated failures. They unfold as a chain of activity that begins with user input, influences agent behavior, and results in downstream actions. Understanding risk requires observing how that chain evolves over time.
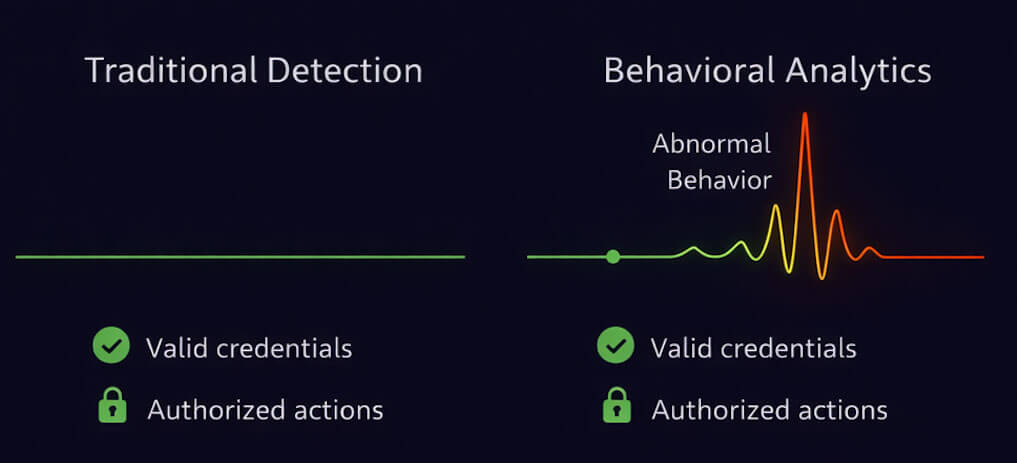
Why Traditional Detection Misses Agentic Risk
Traditional detection validates credentials, permissions, and policy compliance. That works when threats violate known rules. In agentic environments, misuse often occurs within approved access. A user prompt may be valid. An agent action may be authorized. Risk only becomes visible when behavior shifts from established patterns. Event‑based tools struggle to identify that shift.
How Behavioral Analytics Detects Agentic Risk
Behavioral analytics builds baselines for users and AI agents, tracking how prompts, sessions, tool calls, and data access normally occur. When behavior deviates, such as unusual token usage, first‑time agent actions, or abnormal interaction sequences, risk signals surface. These signals align directly with OWASP agentic risk categories without relying on predefined signatures.
Why Insider Threat Looks Different in the Agentic Enterprise
In the agentic enterprise, insider risk includes human users, AI agents, and the interactions between them. A legitimate user can unintentionally trigger unsafe automation. An agent with valid permissions can drift from its intended role. Behavioral analytics connects these actions into a single investigative view, helping teams see how insider‑driven risk develops.
How This Applies by Role
For Security Leaders
Behavioral analytics provides visibility into AI agent risk without requiring new control planes or constant rule tuning. This supports governance, risk oversight, and informed investment decisions as AI adoption grows.
For Security Architects
Behavioral modeling complements existing controls by detecting risk patterns that span users, agents, and tools. This helps architects design resilient detection strategies for agentic systems.
For Security Analysts
Unified behavioral signals reduce noise and surface meaningful deviations. Analysts gain context that explains how agent activity connects to user behavior, which speeds investigation and prioritization.
Key Concepts
Agent Behavior Analytics (ABA): Behavioral modeling that applies anomaly detection to AI agents, tracking creation, usage, and activity changes over time.
User and Entity Behavior Analytics (UEBA): Analytics that learns normal behavior for users and entities to identify deviations linked to insider risk.
Agentic Enterprise: An environment where AI agents operate alongside humans with real identities, access, and decision‑making authority.
OWASP Top 10 for Agentic Applications: A framework that categorizes common security risks associated with autonomous and semi‑autonomous AI agents.
What Securing the Agentic Enterprise Requires
The OWASP Top 10 defines where AI agent risk exists. Behavioral analytics shows when that risk begins and how it unfolds. By modeling behavior across users, agents, and interactions, security operations teams gain the visibility needed to detect insider‑driven and agent‑driven threats in agentic environments.
See How Behavioral Analytics Detects AI Agent Risk
See how behavioral analytics detects AI agent risk by modeling user and agent behavior across the AI lifecycle. Read the Agent Behavior Analytics feature brief to learn more.

Kevin Binder
Senior Product Marketing Manager | Exabeam | Kevin Binder is a cybersecurity marketing professional based in Morgan Hill, CA. Kevin has over 20 years of experience in information security marketing with companies including Amazon Web Services, Citrix Systems, and Nortel Networks. In his previous roles, Kevin was responsible for go-to-market strategy for emerging technologies such as cloud-based security services, mobile device management, and user-behavior analytics. He received a B.S. degree in Managerial Economics from UC Davis. In his free time, Kevin enjoys spending time with family and friends, sporting events, and golf.
More posts by Kevin BinderLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.


