
Table of Contents
What Is SIEM?
SIEM (Security Information and Event Management) for compliance monitoring centralizes log data, detects security anomalies, and automates reporting to help organizations meet regulations like HIPAA, PCI DSS, GDPR, and SOX by providing audit trails, real-time threat detection, and continuous oversight of security controls, proving adherence through detailed logs and alerts.
How SIEM supports compliance:
- Centralized log management: Gathers logs from networks, servers, apps, and cloud services into one place, meeting data retention & monitoring requirements (e.g., PCI DSS Req 10).
- Data aggregation and normalization: Standardizes logs from different sources, making analysis for patterns and anomalies easier.
- Real-time monitoring and alerting: Detects suspicious activities like unauthorized access or data exfiltration instantly, triggering alerts for immediate action.
- Automated correlation: Links seemingly unrelated events (e.g., failed logins + data access attempts) to uncover complex threats.
- Compliance reporting: Generates audit-ready reports for specific standards (HIPAA, PCI, SOX, GDPR) to prove controls are in place and functioning.
- User activity monitoring: Tracks user actions, privilege escalations, and access to sensitive data.
This is part of a series of articles about SIEM tools
How SIEM Supports Compliance
Centralized Log Management
SIEM platforms consolidate logs from disparate sources, including servers, network devices, databases, and applications, into a single repository. This centralization ensures consistency in data retention and protection, two critical requirements under standards such as PCI DSS, HIPAA, and GDPR.
By storing all logs securely and making them easily accessible, organizations can efficiently address audit requests and forensic investigations. Additionally, centralized log management simplifies log searchability and analysis. Compliance teams can quickly retrieve relevant events without manually accessing each device, reducing response times for both routine compliance checks and investigations.
Data Aggregation and Normalization
SIEMs aggregate and normalize data from various sources to create a consistent and uniform event format. Devices and applications produce logs in different structures and message types, making it challenging to analyze events cohesively. SIEMs process incoming data, mapping disparate formats into standardized records, allowing correlation rules and analytics to function effectively across an enterprise’s entire infrastructure.
When data is normalized, compliance monitoring becomes less error-prone and more reliable. Analysts and auditors can review activity regardless of the originating platform, ensuring nothing is overlooked due to inconsistent log formats. As many regulations require detailed tracking of access and activity, normalized data also supports complete and accurate compliance reports.
Real-Time Monitoring and Alerting
SIEM tools continuously scan incoming log data for patterns or activities that violate security or compliance policies. When such events are detected, the system generates alerts for security teams to investigate. This proactive monitoring helps organizations identify and respond to suspicious behavior, unauthorized access, or configuration changes before they escalate into data breaches or compliance violations.
The alerting mechanism in SIEMs can be finely tuned to correspond with specific regulatory requirements, such as detecting failed login attempts, unauthorized privilege escalations, or exfiltration of sensitive data. This enables organizations to demonstrate to auditors that they have controls in place to detect and respond rapidly to compliance-related incidents.
Automated Correlation
SIEM platforms use automated correlation engines to link related security events across multiple sources and timelines. This function identifies complex attack patterns or violations that may be undetectable if logs are analyzed in isolation. By correlating events, SIEM systems can uncover incidents such as privilege misuse, lateral movement, or data exfiltration, which are often subject to regulatory scrutiny.
This automation ensures that potential violations, such as unauthorized data access or suspicious changes to critical systems, are detected promptly, helping organizations to meet incident response timing requirements prescribed by regulations. It also enables more comprehensive investigations, supporting root cause analysis and response documentation.
Compliance Reporting
SIEM tools simplify compliance reporting by providing ready-to-use templates and customizable dashboards for different frameworks, such as SOX, HIPAA, PCI DSS, and GDPR. These reporting features extract relevant events and metrics directly from log data, reducing the manual effort required to prepare audit documentation.
Pre-built compliance reports allow organizations to respond quickly to auditor requests with evidence of controls and event histories. The ability to generate detailed, standardized reports is vital for demonstrating compliance and tracking the effectiveness of security controls over time. SIEM platforms automate the production and scheduling of these reports.
User Activity Monitoring
Monitoring user activity is essential for compliance with data security and privacy standards. SIEM platforms track user actions across applications, networks, and systems, recording events such as logins, access to sensitive files, privileged command execution, and policy violations. This visibility makes it possible to detect inappropriate or unauthorized behavior that could lead to data leaks or regulatory breaches.
Beyond detecting direct policy violations, user activity monitoring supports user behavior analytics, identifying anomalous patterns that might indicate compromised accounts or insider threats. SIEM-generated audit trails meet logging and audit requirements of most regulations by providing a detailed, timestamped record of user activity.
Notable SIEM Solutions for Compliance Monitoring
1. Exabeam
Exabeam and LogRhythm offer a powerful combination of SIEM solutions designed to meet diverse organizational needs for security operations and compliance. Exabeam Fusion SIEM is a modern cloud-native platform providing scalable threat detection, investigation, and response for hybrid environments. LogRhythm SIEM complements this by offering a robust enterprise-grade solution often favored for on-premise deployments, particularly where data sovereignty and stringent compliance requirements necessitate local infrastructure control. Together, these platforms provide comprehensive visibility, advanced analytics, and extensive reporting to ensure audit readiness and proactive threat management.
Key features include:
- Flexible Deployment Options: Exabeam Fusion SIEM offers cloud-native scalability for elastic environments, while LogRhythm SIEM provides a strong on-premise option for organizations with specific data residency or infrastructure preferences.
- Behavioral Analytics (UEBA): Both platforms leverage User and Entity Behavior Analytics to detect anomalous activity and insider threats, significantly reducing false positives and improving threat prioritization.
- Comprehensive Data Ingestion and Normalization: Collects, parses, and normalizes logs from a vast array of sources, including network devices, endpoints, applications, and cloud services, ensuring a unified view of security events.
- Automated Timelines and Correlation: Automatically builds incident timelines and correlates events across disparate sources, accelerating investigations and response times.
- Extensive Compliance Reporting: Delivers robust audit and compliance reporting capabilities with pre-built templates for major regulatory frameworks such as GDPR, PCI DSS, SOX, and HIPAA.
- Outcomes Navigator: Exabeam’s Outcomes Navigator provides measurable evidence of control coverage and improvement over time, aiding in reporting and audit processes. LogRhythm’s compliance automation offers similar capabilities with pre-packaged modules.
- Advanced Threat Detection: Utilizes sophisticated correlation engines, guided search, and customizable rules to identify complex attack patterns and policy violations.
2. Splunk Enterprise Security

Splunk Enterprise Security is a SIEM solution to help organizations improve threat detection, simplify investigation workflows, and meet compliance obligations through automation and full-spectrum visibility. It centralizes data from all environments into a single platform, enabling security operations centers (SOCs) to detect, investigate, and respond to incidents efficiently.
Key features include:
- Full-fidelity visibility: Ingests and analyzes data across all sources and domains for unified monitoring
- Automated threat detection: Uses AI, rule-based, and behavior-based analytics to detect known and unknown threats
- User and Entity Behavior Analytics (UEBA): Identifies insider threats and anomalous activity with ML-driven analysis
- Risk-Based Alerting (RBA): Reduces alert fatigue by prioritizing high-risk threats and increasing true positive rates
- Compliance reporting: Supports audit readiness with reporting and evidence of security controls
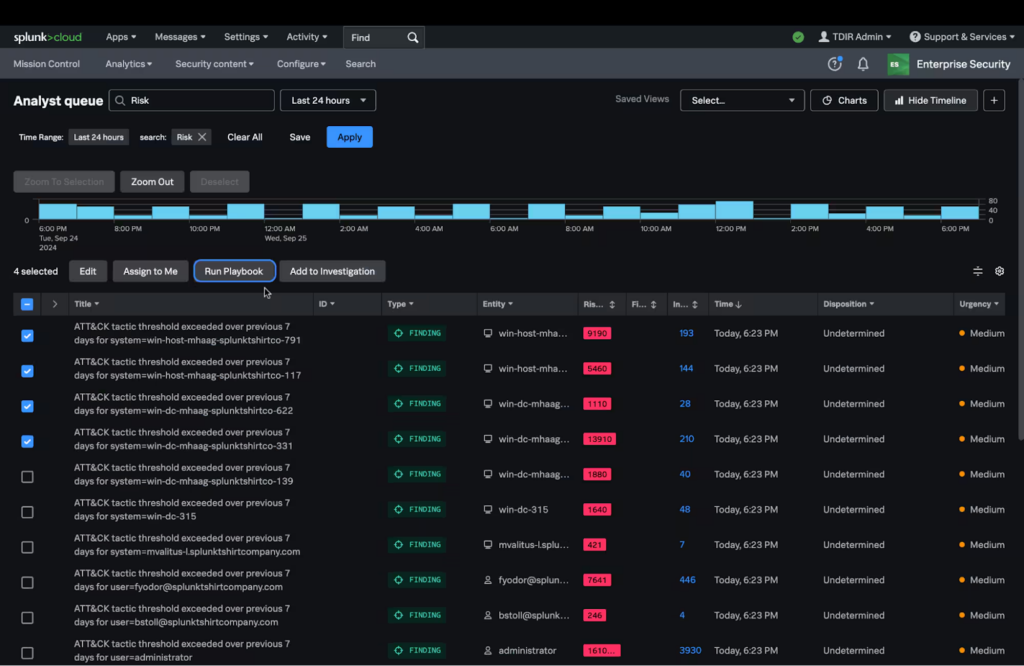
Source: Splunk Enterprise Security
3. Microsoft Sentinel SIEM

Microsoft Sentinel is a cloud-native SIEM platform that provides security visibility and response across multicloud and hybrid environments. It collects and normalizes data from diverse sources, applies analytics to detect threats, and automates responses using playbooks and rules.
Key features include:
- Cloud-native scalability: Deployed on Azure, enabling elastic scaling and reduced infrastructure overhead
- Data collection across platforms: Supports native connectors for Microsoft services and third-party sources using CEF, Syslog, and REST API
- Data normalization: Uses Advanced Security Information Model (ASIM) for consistent data analysis across all sources
- Analytics and threat detection: Leverages prebuilt and custom rules to detect threats and reduce false positives
- MITRE ATT&CK integration: Maps detections to MITRE framework tactics and techniques for coverage visibility
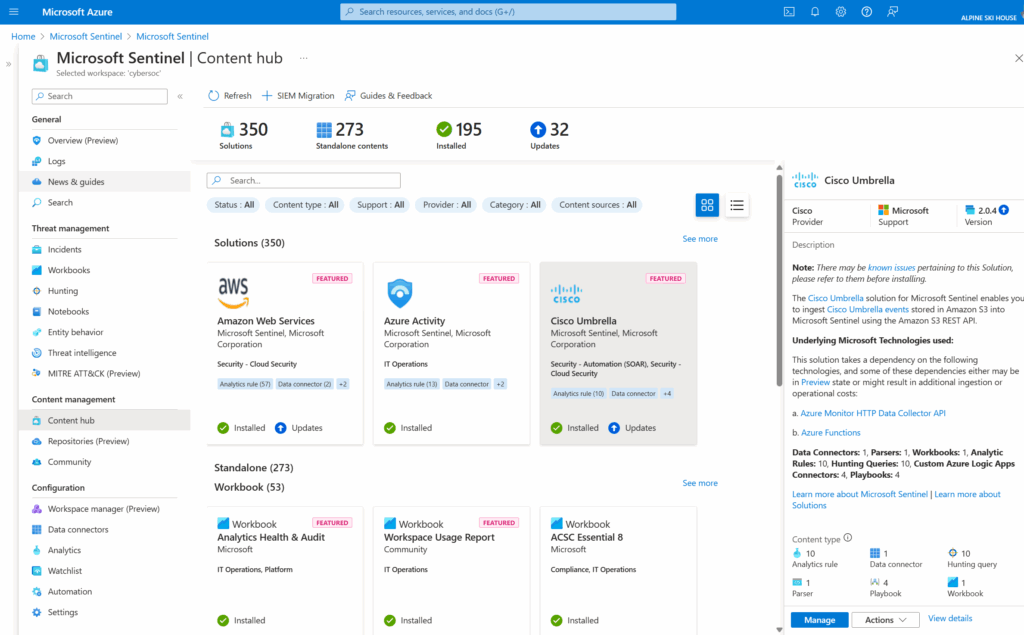
Source: Microsoft Sentinel
4. ManageEngine Log360

ManageEngine Log360 is a unified SIEM platform that combines log management, threat detection, user behavior analytics, and automated response in a single solution. Designed for SOCs, it supports automated threat detection, investigation, and response (TDIR) across hybrid environments.
Key features include:
- Automated TDIR with Vigil IQ: Enables detection, investigation, and response using cloud-delivered analytics and contextual investigation tools
- Precision alert tuning: Reduces noise and false positives through no-code rule adjustments, object-level exclusions, and adaptive ML-based thresholds
- User Behavior Analytics (UEBA): Detects insider threats with continuous monitoring, identity mapping, and dynamic peer grouping
- Dark web monitoring: Identifies leaked credentials and sensitive data before threat actors can exploit them
- Generative AI insights (Zia): Provides human-readable summaries of incidents, visualized attack timelines, and remediation advice to accelerate investigations
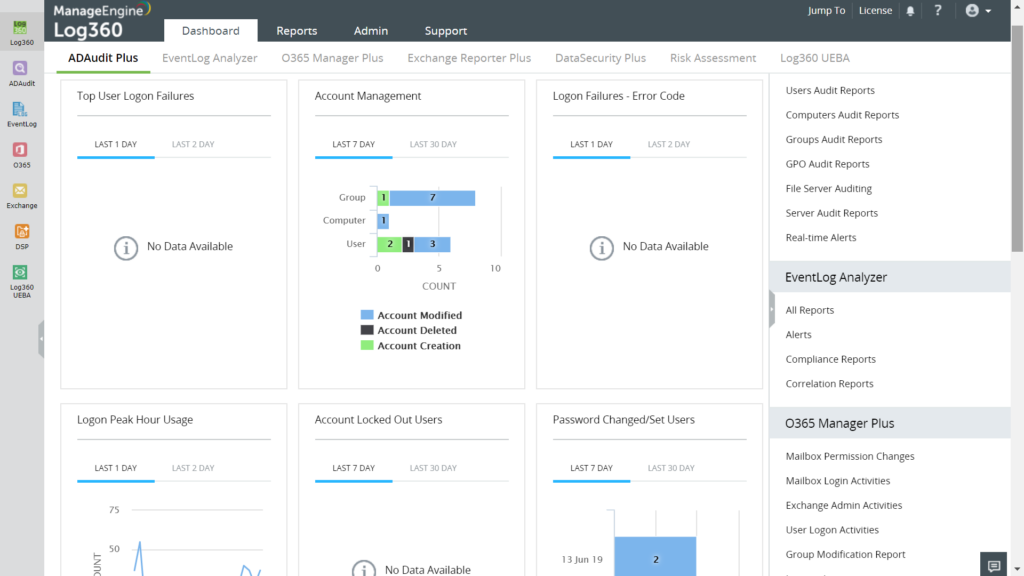
Source: ManageEngine Log360
5. Sumo Logic Cloud SIEM

Sumo Logic Cloud SIEM is a cloud-native security analytics platform to accelerate threat detection, investigation, and response (TDIR) through data processing, automation, and behavioral analytics. It reduces alert fatigue with signal grouping, enriches alerts with contextual threat intelligence, and enables fast, AI-guided investigations.
Key features include:
- Threat detection: Ingests and analyzes structured and unstructured data for immediate threat identification and correlation
- Insight engine: Automatically clusters signals into high-confidence insights using adaptive algorithms aligned to the MITRE ATT&CK framework
- AI-guided investigations: Uses natural language queries and relationship graphs to simplify threat analysis and expose attack scope
- User and Entity Behavior Analytics (UEBA): Baselines behavior quickly and surfaces high-risk anomalies to detect insider threats and compromised accounts
- Automation and playbooks: Enriches and responds to alerts using built-in and custom playbooks triggered by specific security insights
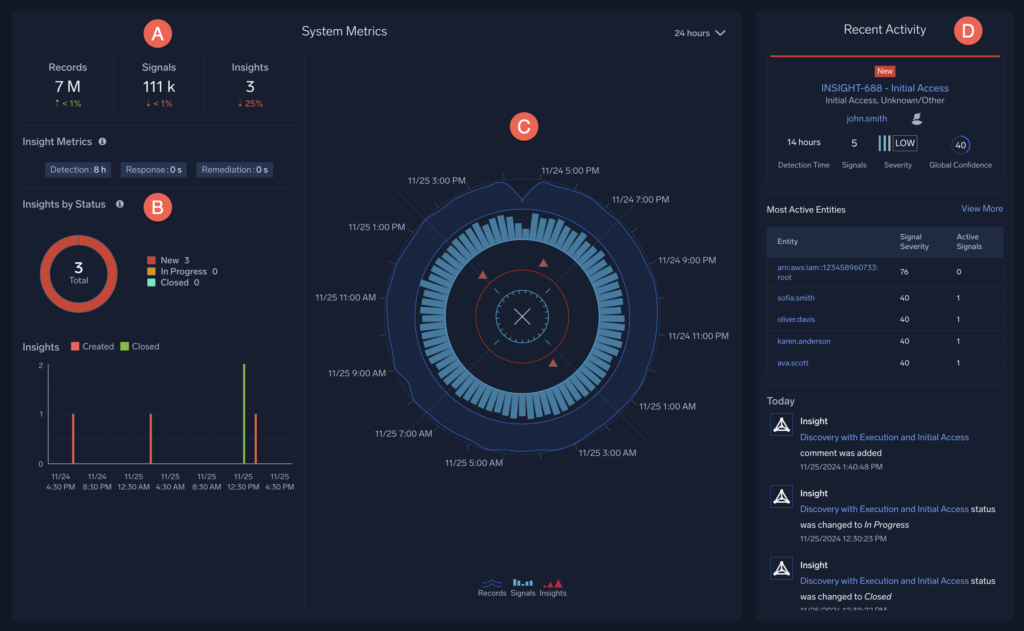
Source: Sumo Logic
Learn more in our detailed guide to SIEM solutions
Best Practices for Effective Compliance Monitoring with SIEM
Here are some of the ways that organizations can better use their SIEM solutions for compliance monitoring.
1. Define Clear Compliance Objectives and Align SIEM Rules
Organizations should begin by establishing precise compliance objectives, which might include requirements for data retention, user access management, incident response timelines, or reporting criteria set by regulations like SOX, HIPAA, or PCI DSS. These objectives form the foundation for configuring SIEM rules, detection logic, and reporting modules.
Without clearly defined goals, there’s a risk of gaps between what is monitored and what compliance frameworks require, leading to audit failures or regulatory penalties. Once objectives are clear, align SIEM configuration accordingly. This involves mapping log sources, specifying relevant events, and tailoring alerts to detect policy violations covered by specific mandates.
2. Ensure Complete Log Coverage Across Systems
Enterprises should identify all systems, applications, endpoints, and network devices that process, store, or transmit sensitive data, then configure their SIEM to collect logs from each source. Gaps in log collection can result in incomplete investigation trails and non-compliance with regulatory expectations for monitoring and auditability.
In addition to device and application diversity, organizations must consider cloud, on-premises, and hybrid resources in their log strategy. Regular reviews and updates to log source inventories are required as infrastructures evolve. Ensuring all security-relevant activity is logged and ingested by the SIEM reduces risk exposure and strengthens the organization’s ability to provide exhaustive evidence during audits or investigations.
3. Fine-Tune Alerts and Automate Evidence Collection
Generic SIEM alerts can overwhelm teams with noise or miss relevant compliance events. Fine-tuning alert thresholds, refining correlation rules, and tailoring notifications help ensure that alerts align not only with technical risks but also with regulatory requirements. This increases the likelihood of early detection for compliance breaches and reduces the volume of false positives that drain investigative resources.
Automation further boosts compliance monitoring efficiency. Automated evidence collection, such as retaining event logs for required periods or auto-generating incident documentation, allows organizations to respond quickly to auditor requests. Automated case management and alert tracking support the creation, tracking, and reporting of compliance incidents.
4. Periodically Assess SIEM Effectiveness
Continuous assessment is critical to maintaining an effective SIEM-driven compliance program. Organizations should periodically review the quality and completeness of log ingestion, the accuracy of detection rules, and the relevance of compliance dashboards and reports. Routine SIEM tuning ensures that changes in regulations, IT infrastructure, or business processes are promptly reflected in monitoring strategies.
Periodic effectiveness assessments can involve simulated scenarios, such as mock audits, red team exercises, or compliance table-top drills. These tests reveal gaps or oversights in coverage, detection, and response capabilities.
5. Train Teams on Interpreting Compliance Alerts and Reports
Technical staff must be adequately trained to understand and act upon compliance-related SIEM alerts and reports. Training programs should cover how to investigate alert types tied to regulatory obligations, interpret compliance dashboards, and generate evidence for auditors. Teams must be familiar with documentation requirements for incident response and regulatory reporting so that actions are properly justified and logged.
Ongoing training is necessary as SIEM platforms, compliance standards, and organizational processes evolve. Drills, workshops, and real-world scenario reviews help keep analysts, auditors, and IT staff prepared to respond to events and requests. Well-trained teams close gaps between detection, investigation, and reporting.
Related content: Read our guide to SIEM products
Conclusion
SIEM plays a critical role in helping organizations meet compliance requirements by centralizing log data, standardizing analysis, and automating detection and reporting. Through features like real-time monitoring, event correlation, and user activity tracking, SIEM solutions not only improve security posture but also provide the transparency and auditability demanded by regulations such as PCI DSS, HIPAA, GDPR, and SOX. To maximize value, organizations must align SIEM configurations with compliance goals, ensure complete data coverage, and continuously tune their systems and processes.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.