
Table of Contents
What Are SOAR Solutions?
SOAR refers to Security Orchestration, Automation, and Response (SOAR). SOAR solutions are software platforms and processes that help organizations automate and simplify their cybersecurity operations. These platforms integrate disparate security tools, automate repetitive tasks to speed up incident response, and provide a centralized platform for security teams to manage threats and coordinate actions efficiently.
SOAR solutions use pre-defined playbooks to automate routine responses, reducing the need for manual intervention. The goal of a SOAR solution is to simplify incident response and provide deeper visibility into the overall security posture of an organization. With threats becoming more sophisticated, SOAR tools are increasingly critical for modern cybersecurity operations centers (SOCs).
Benefits of SOAR Solutions
SOAR solutions provide several operational and strategic advantages for security teams. By automating tasks and centralizing workflows, they allow analysts to focus on higher-value investigations rather than repetitive manual work. This leads to more consistent, faster, and accurate incident handling across the organization.
Key benefits include:
- Comprehensive reporting: Detailed logs and reports simplify compliance and post-incident reviews.
- Faster incident response: Automation reduces the time needed to detect, analyze, and remediate threats.
- Improved efficiency: Routine tasks like data collection, enrichment, and correlation are handled automatically, freeing analysts for complex work.
- Consistent processes: Playbooks ensure incidents are managed in a standardized way, lowering the risk of missed steps.
- Reduced analyst fatigue: By cutting repetitive work, SOAR helps prevent burnout in SOC teams.
- Better collaboration: Centralized dashboards and case management enable multiple teams to work together on incidents.
- Enhanced accuracy: Automated workflows reduce human errors in investigation and response.
- Scalable security operations: SOAR platforms allow organizations to handle more alerts without proportionally increasing headcount.
Notable SOAR Solutions
1. Exabeam

Exabeam combines SIEM, UEBA, and built-in automation to streamline threat detection, investigation, and response. It unifies telemetry from identity systems, endpoints, networks, cloud services, and threat intelligence into a single analytics layer, then automates investigations and playbook-driven actions. The Nova agentic AI accelerates case summaries, suggests next steps, and helps analysts prioritize response while low-code playbooks orchestrate actions across the stack.
Key features include:
- Integrated SIEM and SOAR: Exabeam’s SIEM provides advanced log management and behavioral analytics that feed its automation capabilities. Detections can trigger standardized response workflows, allowing analysts to move from alert to action without switching tools.
- Low-code playbooks and workflow automation: Prebuilt and customizable playbooks enable rapid containment, eradication, and recovery. Analysts can view, modify, and reuse workflows to match evolving threats and operational preferences.
- Agentic AI for faster TDIR: Nova’s agentic AI automatically summarizes cases, classifies threats, identifies attack paths, and recommends next steps, reducing mean time to respond by 80% and improving consistency.
- Behavioral analytics and risk-based prioritization: Exabeam’s UEBA models typical user and entity behavior to establish baselines. When deviations occur, it assigns dynamic risk scores that help analysts focus on the most critical threats and automate related responses.
- Broad ecosystem integrations: The platform connects with EDR, NDR, IAM, cloud security, and ticketing systems to enrich alerts and execute response actions such as account lockdown, device isolation, or policy updates.• Incident response at scale: Machine-built timelines, guided investigations, and automated workflows reduce manual effort throughout the entire detection and response lifecycle.
2. ManageEngine Log360

ManageEngine Log360 is a unified SIEM platform that includes built-in SOAR capabilities to help security teams detect, investigate, and respond to threats with greater efficiency. Its automation-driven design allows SOCs to reduce alert fatigue, accelerate response times, and handle complex incidents using guided workflows.
Key features include:
- Automated threat detection and response: Uses over 2,000 cloud-delivered, MITRE-mapped detection rules and pre-defined playbooks to automate TDIR (threat detection, investigation, and response).
- Incident workbench: Centralizes telemetry and context from multiple sources, enabling AI-generated user timelines and process lineage views for faster investigations.
- Precision tuning for alert management: Reduces false positives with no-code rule tuning, object-level filtering, and ML-based adaptive thresholds.
- Dark web monitoring: Proactively detects leaked credentials and supply chain breaches to prevent external attacks before they start.
- Behavioral analytics: Applies UEBA to detect insider threats through continuous monitoring of user behavior and dynamic risk scoring.

Source: ManageEngine
3. Tines

Tines offers a no-code SOAR platform to eliminate the complexity found in legacy systems. Focused on flexibility, speed, and accessibility, Tines helps security teams to automate workflows directly, without relying on developers or extensive integration overhead.
Key features include:
- No-code workflow automation: Enables security practitioners to build and deploy complex automation workflows without writing code, allowing faster setup and iteration.
- API integration: Designed as an integrator rather than relying on pre-built integrations, Tines can connect to any internal or external API for real-time data sharing and orchestration.
- Simplified incident response: Provides collaborative case management features for investigating, remediating, and documenting incidents in a unified workspace.
- Fast time-to-value: Avoids the long deployment times common with traditional SOAR platforms; teams can build and launch automation within minutes.
- Scalable for any team size: Built to support both small teams and large enterprises, allowing security operations to grow without adding complexity.
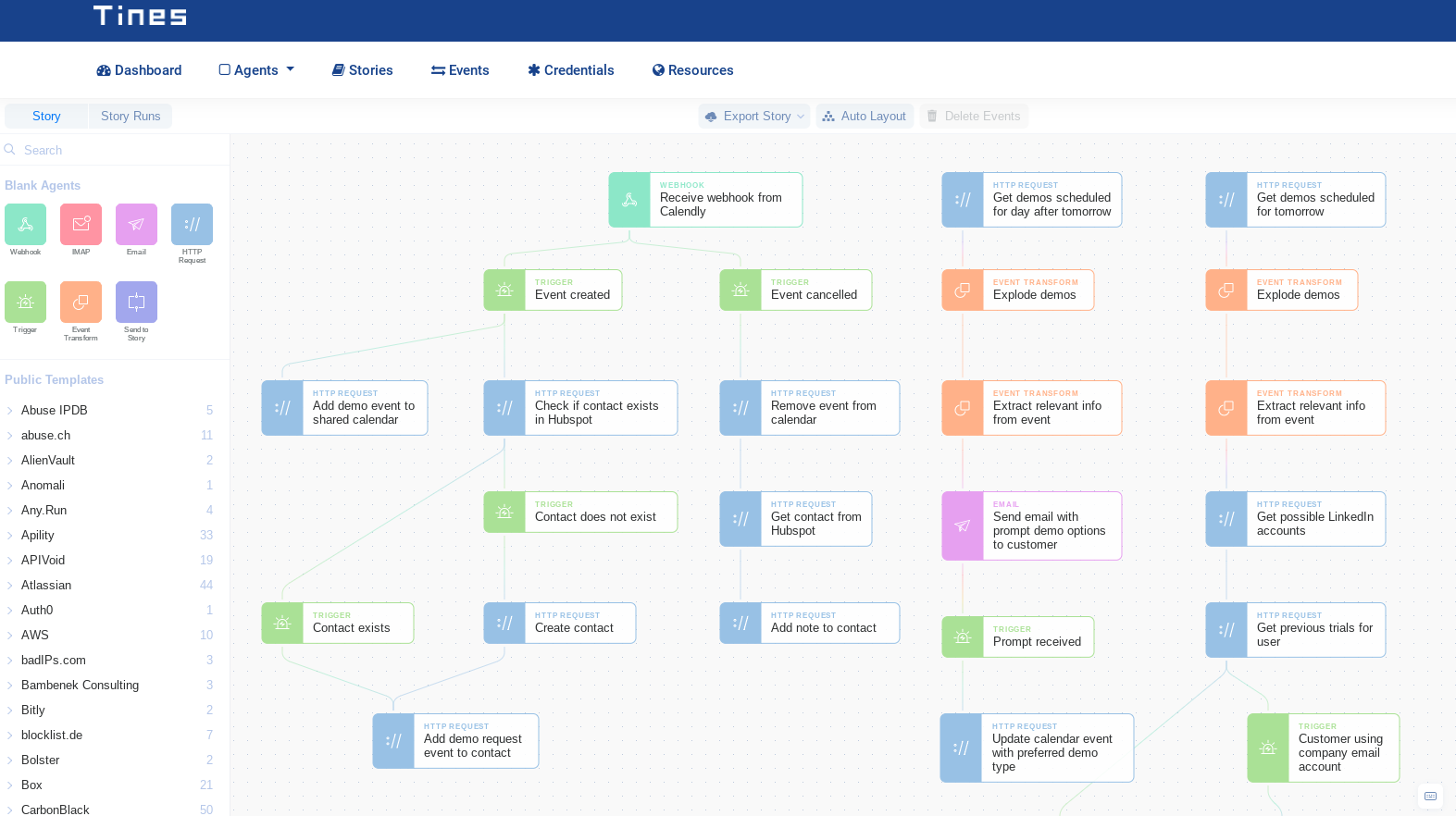
Source: Tines
4. Sumo Logic Cloud SOAR

Sumo Logic Cloud SOAR is a cloud-native platform to automate and scale incident response across SecOps environments. Designed to reduce false positives and analyst fatigue, it centralizes investigation, case management, and response workflows in a single interface.
Key features include:
- Extensive integration framework: Supports open integration with hundreds of third-party tools, enhancing the platform’s flexibility across diverse environments.
- Automated threat investigation: Accelerates incident triage by automatically analyzing indicators of compromise (IoCs) to reduce manual workload and false positives.
- Centralized case management: Offers structured, collaborative case handling with automated standard operating procedures (SOPs) to guide decision-making.
- Customizable dashboards: Visualize key performance indicators and security metrics through tailored dashboards for better operational insight.
- Cloud-native scalability: Built for multi-tenant, elastic environments, enabling seamless scaling across single, multi-, or hybrid cloud infrastructures.
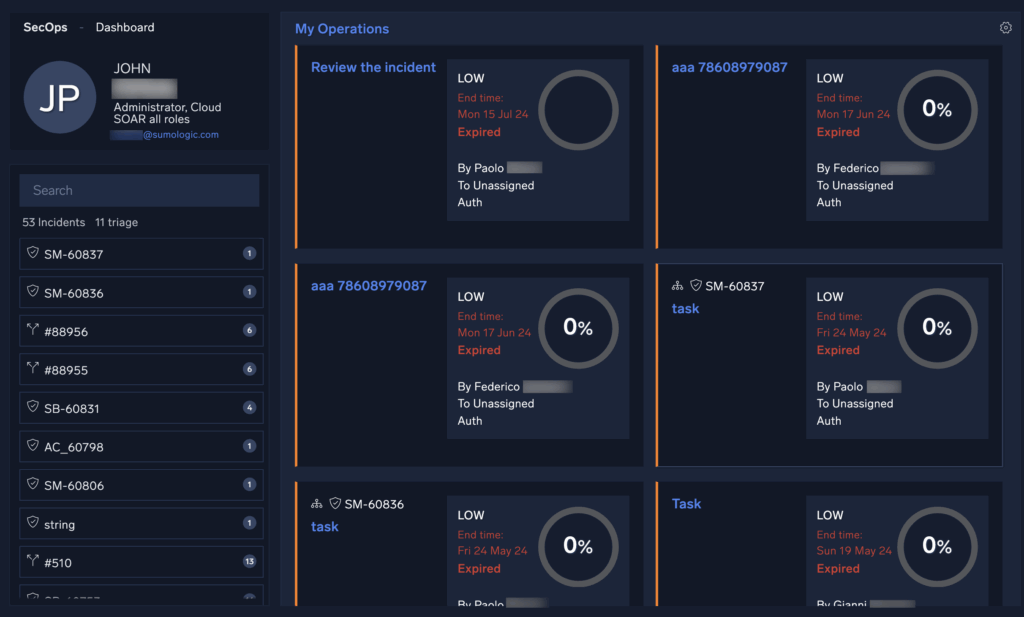
Source: Sumo Logic
5. Splunk SOAR

Splunk SOAR is an automation-driven security platform that helps security teams to simplify workflows, reduce response times, and unify their security operations. Now a native capability within Splunk Enterprise Security, it integrates with SIEM, UEBA, and threat intelligence tools, helping organizations build a cohesive and responsive SecOps environment.
Key features include:
- Automated playbooks: Execute critical security actions across tools in seconds using a wide selection of prebuilt and customizable playbooks aligned with frameworks like MITRE ATT\&CK and D3FEND.
- Visual playbook editor: Create and modify automation workflows using a drag-and-drop interface that supports both no-code and advanced scripting, making it accessible to teams with varying skill levels.
- Extensive integrations: Connect with over 300 tools and leverage 2,800 automated actions to coordinate complex workflows across the IT and security ecosystem.
- Unified security operations: Integrates with Splunk Enterprise Security to provide a single, unified SecOps platform with consolidated alerting, case management, and analytics.
- Case management: Supports task assignment, segmentation, and tracking to improve team collaboration and maintain consistent incident documentation.
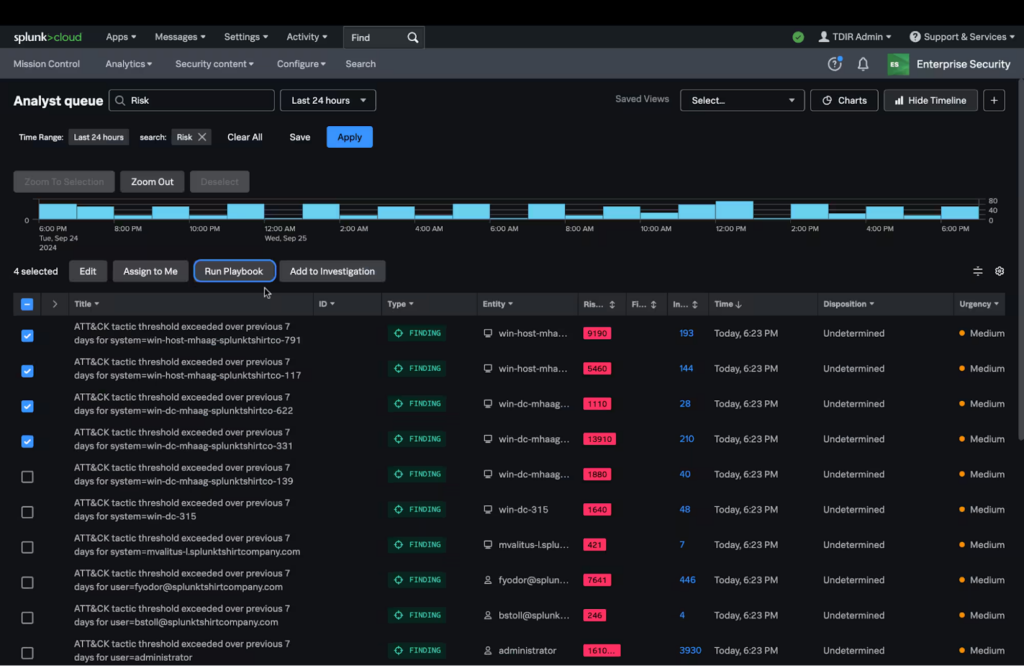
Source: Splunk
Related content: Read our guide to SOAR tools (coming soon)
Considerations for Choosing SOAR Solutions
Choosing the right SOAR solution involves aligning platform capabilities with your team’s workflows, existing toolsets, and operational maturity. Below are key and often overlooked considerations to guide an effective selection process:
- Integration depth, not just breadth: Evaluate how deeply the SOAR platform integrates with your current tools: SIEM, EDR, ticketing, threat intelligence, etc. Shallow or generic connectors can limit automation potential and require workarounds.
- Playbook customization and maintenance: Look for platforms that support both prebuilt and easily customizable playbooks. Consider the effort needed to maintain playbooks over time, especially as threat models and environments evolve.
- Security team skill sets: Some SOAR platforms require scripting or development skills to build and manage workflows. Assess whether your team has, or can develop, the necessary capabilities, or if a no-code/low-code platform is more suitable.
- Case management and collaboration features: Strong incident handling often depends on how well a SOAR platform supports collaboration; task assignments, role-based access, timelines, and documentation tracking are critical for response consistency.
- Scalability and deployment model: Consider whether the solution supports your infrastructure: cloud-native, hybrid, or on-prem. Ensure it can scale with your operations without requiring major rearchitecture.
- License and cost structure: Understand the pricing model, whether it’s per action, user, or endpoint, and how that scales. Some models can become cost-prohibitive as automation use grows.
- Vendor support and community ecosystem: A strong support model, active user community, and available integrations are often as valuable as the core platform features. Evaluate how easily you can get help, documentation, and shared playbooks.
Conclusion
SOAR solutions are essential for modern security operations, enabling organizations to simplify workflows, improve response times, and manage increasing alert volumes with greater consistency. By combining automation, orchestration, and centralized incident handling, these platforms reduce manual effort and improve collaboration across security teams. Their ability to integrate diverse tools and enforce standardized playbooks helps ensure that incidents are handled efficiently while minimizing human error.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.