
Add Context, Risk Scoring, and Automation to Microsoft Sentinel
- Apr 13, 2026
- Heidi Willbanks
- 3 minutes to read
Table of Contents
Microsoft Sentinel gives security operations team visibility into activity across Microsoft environments. As those environments grow, many teams start looking for deeper behavioral context, more consistent investigations, and ways to reduce manual work without replacing what already works.
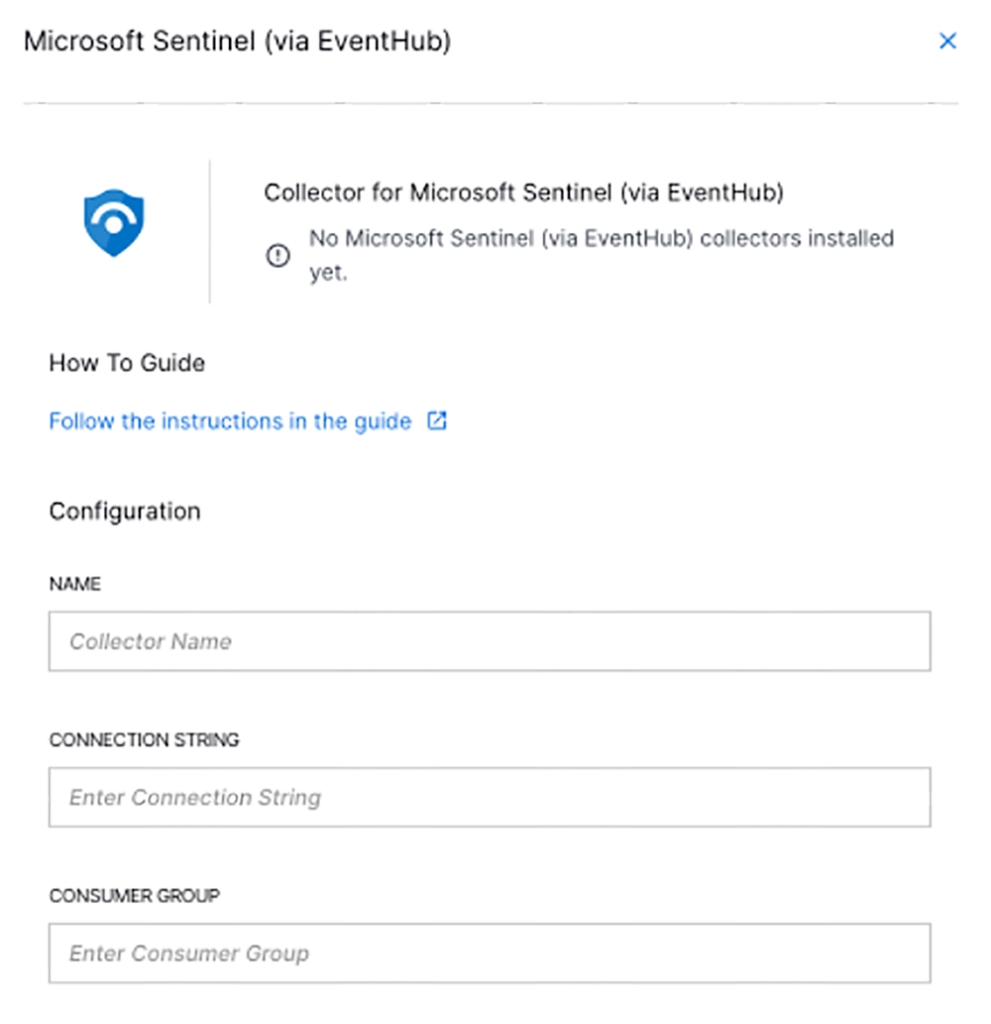
That’s where the Exabeam Microsoft Sentinel Collector comes in. It sends Sentinel telemetry into New-Scale Fusion, where analytics, timelines, and automation help teams move from raw activity to prioritized response with less effort.
Below are four ways security operations leaders and practitioners use the collector to extend what Sentinel already provides and get more from their existing investment.
1. Extend Visibility Beyond Microsoft Data
Most investigations don’t stop at Microsoft services. Identity, endpoint, cloud, and SaaS activity often intersects in ways that are difficult to piece together when data lives in separate tools.
The Exabeam Microsoft Sentinel Collector brings Sentinel data into the New-Scale Platform, where it aligns with additional security data through collectors, a security-specific Common Information Model (CIM), and continuous behavioral modeling. Activity from Microsoft and non-Microsoft sources follows the same structure, so analysts can trace behavior across systems instead of jumping between views.
What this means for you:
- Visibility that spans hybrid and multi-cloud environments, not just Microsoft services
- Consistent normalization and context enrichment that reduce manual log work
- Behavioral models that adjust as normal activity changes, improving coverage over time
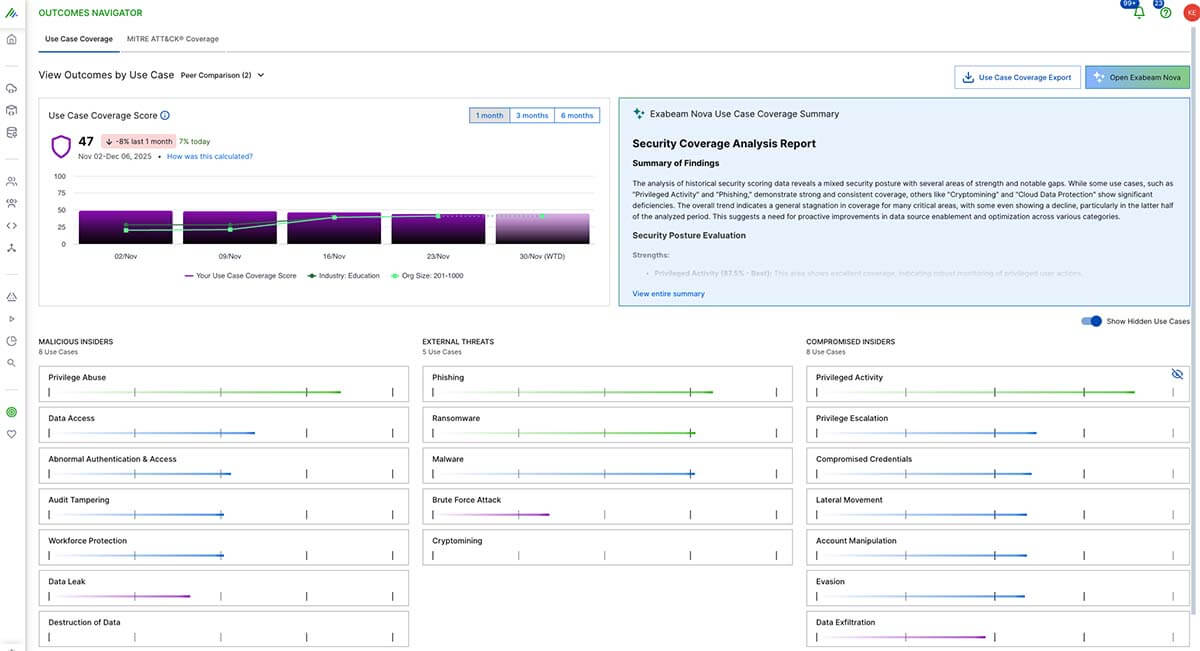
2. Add Behavioral Intelligence and Dynamic Risk Scoring
Correlation rules are important, especially for known patterns. Many teams add behavioral analytics to uncover familiar or slow-moving activity that rules alone struggle to identify.
When Sentinel telemetry enters New‑Scale Analytics, it contributes to continuously updated behavioral profiles. Related signals group into evidence-based response objects and dynamic risk scoring tracks how unusual actions accumulate over time. Analysts see not only what happened, but why it deserves attention.
What this means for you:
- Broader coverage driven by continuous profiling rather than short lookback windows
- Detections that adapt as behavior and attack techniques change
- Risk scores that help teams focus on activity with the highest potential impact
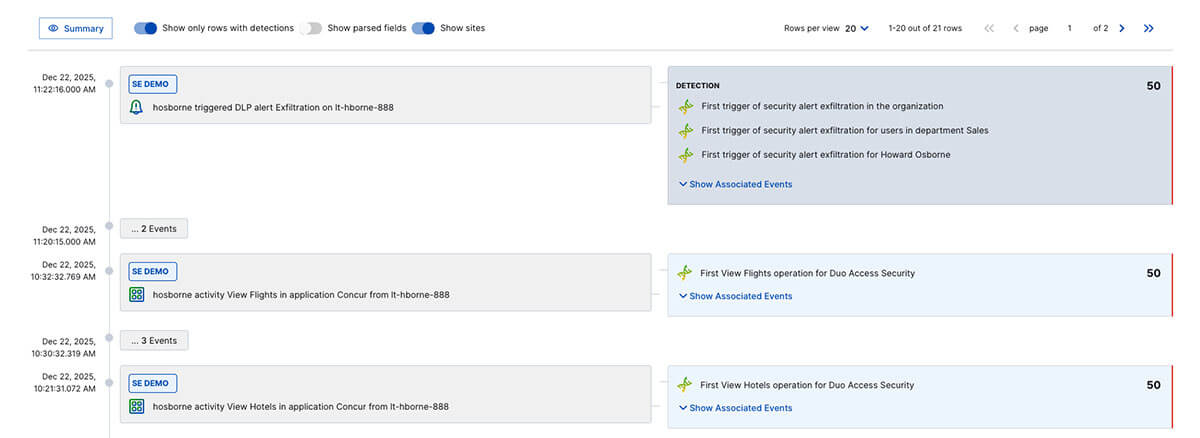
3. Standardize Investigations With Timelines
Investigations often slow down when analysts piece together activity across multiple searches and tools. That friction adds time and inconsistency.
Within Threat Center, Sentinel events appear in structured Threat Timelines alongside activity from the rest of the environment. Events are normalized, scored, and arranged chronologically so analysts can follow the sequence without stitching logs together manually. Cases, evidence, and tasks live in the same workspace, which helps teams work faster and follow repeatable investigation paths.
What this means for you:
- Faster investigations built on structured timelines rather than ad hoc searches
- A predictable investigation flow that supports analysts at every experience level
- Less manual effort organizing evidence and context
4. Reduce Manual Response With Built-In Automation
After a detection, teams often spend hours on repetitive steps like enrichment, tagging, routing, and closure. That work adds up quickly.
Automation Management within New-Scale Fusion introduces structure to these tasks. Sentinel data flows directly into automation workflows built with no- and low-code tools, prebuilt playbooks, and OpenAPI Standard (OAS) support. Exabeam Nova Investigation, Threat Scoring, and Analyst Assistant agents provide context and recommendations that automation can act on.
What this means for you:
- Fewer repetitive steps without added engineering overhead
- Consistent response patterns driven by reusable playbooks
- Automation that scales as your environment and integrations grow
Get More from Microsoft Sentinel Without Starting Over
Microsoft Sentinel delivers deep visibility for Microsoft-centric environments. By adding the Microsoft Sentinel Collector, teams extend that visibility into a broader behavioral view, accelerate investigations with structured, automated timelines, and reduce manual response through automation.
If you’re evaluating how to mature security operations without replacing tools you already rely on, this approach offers a practical path forward.
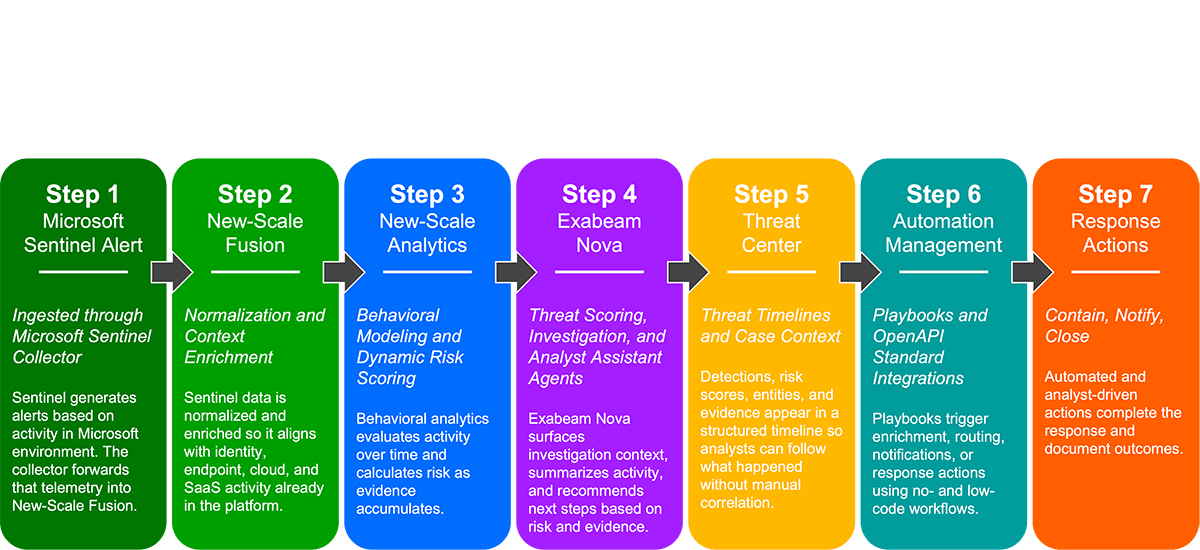
Together, these capabilities form a direct path from alert to response.
Learn the Four Approaches in Detail
Read the full guide, Four Ways to Augment Microsoft Sentinel With the Exabeam Microsoft Sentinel Collector, for a walkthrough of each approach with architecture details and examples.

Heidi Willbanks
Senior Product Marketing Manager, Content | Exabeam | Heidi Willbanks is the Senior Product Marketing Manager, Content at Exabeam. She manages content strategy and production for product marketing and supports strategic partners, sales and channel enablement, and competitive content, leveraging her product marketing certification, content expertise, and industry knowledge. She has 19 years of experience in content marketing, with nearly a decade in the cybersecurity field. Heidi received a BA in Journalism with a minor in Graphic Design from Cal Poly Humboldt and was awarded Outstanding Graduating Senior in Public Relations Emphasis. She enjoys reading, writing, gardening, hiking, yoga, music, and art.
More posts by Heidi WillbanksLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
