At Exabeam, we’re passionate about security and developing the newest cybersecurity. We’re also fascinated by what we can learn from older security technologies. That’s why we created a History of Cybersecurity 2019 Calendar. Each month features key dates in cybersecurity history, along with a related trivia question and other things of interest that occurred in that month during years past.
This is fifth in a series of posts featuring the Cybersecurity Calendar where we look at the birth of Advanced Encryption Standard (AES) and how it became a federal standard for classified information. We’ll be publishing more history around the cybersecurity dates we’ve researched throughout the year. If you think we missed an important date (or got something wrong), please let us know. You can also share your feedback with us on Twitter.
Securing your devices
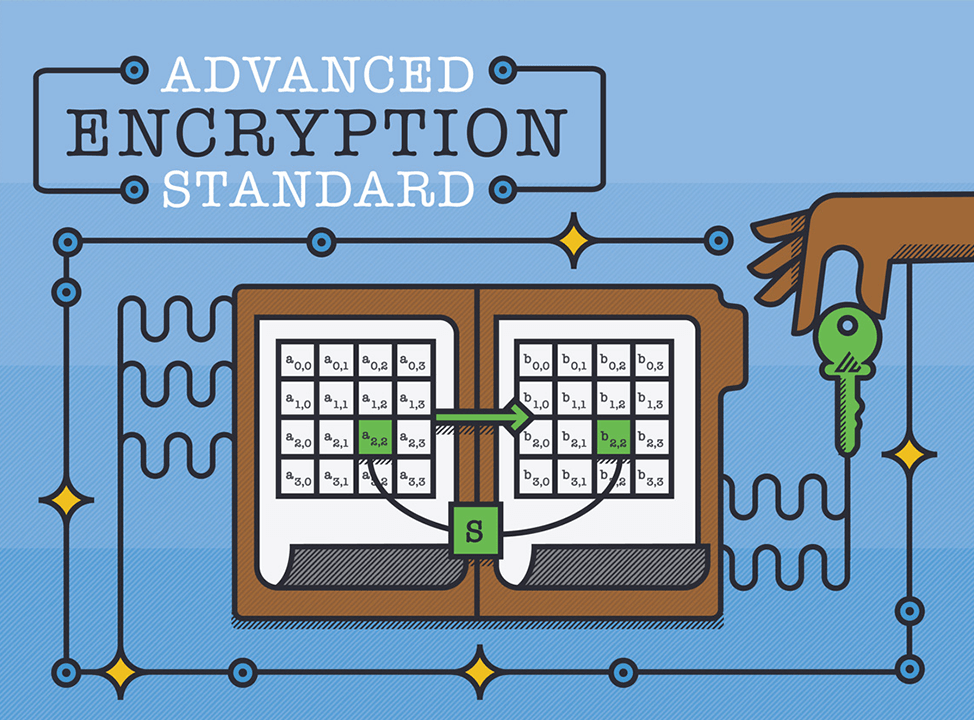
Sensitive information needs to be sealed up before it’s sent from one person to another. Nobody knows that more than the government. Going all the way back to the 1960s, experts have been working hard to find the latest and greatest way to send electronic data safely. Today, we can thank the Advanced Encryption Standard (AES) for keeping our data safe, but that wasn’t always the case.
Before AES, there was the Data Encryption Standard
The Data Encryption Standard (DES) started as a research project for IBM in the late 1960s, with the technology company coming up with a codename for its new encryption method: Lucifer. Lloyd’s Bank in the UK bought the code in 1971 and used it in ATMs in and around London.
While all this was happening, the U.S. National Bureau of Standards was on the hunt for a way to protect digital communications for both the government and the consumer market as a whole. The government decided it needed a mandated standard and guess who happened to already have a great solution? Lucifer was established as proven encryption technology, so the U.S. government chose it as the first-ever national encryption standard on January 15, 1977.
DES had its issues
As with many 20th-century technologies, DES had weaknesses that became clearer over time. The 56-bit key was frequently cited as too short, making it vulnerable to brute-force search. DES wasn’t the only cipher that fell under scrutiny. In fact, all 56-bit and 64-bit keys were highly criticized as technology evolved. This was only heightened with a 1996 paper that recommended at least 75-bit encryption for existing ciphers and 90 bits or more for all new ciphers.
But perhaps the biggest killer of DES came when the internet propelled computers into the mainstream. The issues with its short key length and advanced processing power of modern computers made DES even more vulnerable to attacks. It quickly became clear that the current standard wasn’t good enough to keep sensitive data out of the hands of savvy cybercriminals.
Meanwhile, back at the lab
Fortunately, criminals weren’t the only ones becoming more sophisticated. At the same time, when DES was undergoing widespread criticism, two Belgian cryptographers were already on the case. Joan Daemen and Vincent Rijmen had developed a cipher called Rijndael while working together at the COSIC lab. Rijndael was one of many ciphers considered as part of a 1997 call for a new standard, called Advanced Encryption Standard, that would be available royalty-free across the globe.
Once all the responses had been collected, the pool of candidates was narrowed to five finalists, which were then scrutinized and put out for public comments. On October 2, 2000, the National Institute of Standards and Technology (NIST) announced that Rijndael was the winner and would become the new standard. A new standard AES was announced, with the public invited to comment and those comments were used during revisions until an official standard was released on November 26, 2001.
Move aside, DES
AES brought 128-bit encryption to the market using a block cipher. With AES, you aren’t limited to 128 bits, though. Data can be encrypted in 128-, 192-, and 256-bit amounts, with the number of rounds used to protect data growing as the encryption level increases. There are multiple types of encryption available today, with some having higher levels of security than others. Those levels are:
- Triple Data Encryption Standard (3DES)—Yes, DES is still around, but this technology uses triple DES, with three individual 56-bit keys applied to data, automatically tripling a 56-bit DES to make it a 168-bit key.
- Twofish—Used with smaller CPUs and hardware, Twofish ranges from 128 to 256 bits. This encryption method uses 16 rounds of encryption.
- RSA—RSA keys range from 1024 and 2048 bits. Its asymmetric cryptographic algorithm is used for AES key exchange and digital signatures. This method of encryption is widely used on web browsers, email, VPNs and among other digital communication methods.
As technology continues to evolve, the need to have stronger protections in place will continue to grow, as well. Chances are, someone’s working hard right now to find a cipher that will protect devices during the next decade and beyond.
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!