
- Home >
- Explainers >
- Zero Trust
Zero Trust Solutions: Key Components and Top 9 Options in 2026
- 10 minutes to read
Table of Contents
What Are Zero Trust Solutions?
A zero trust solution is a modern security framework and suite of technologies that continuously authenticate and authorize every user, device, and application before granting access to resources, whether they are inside or outside the network perimeter.
How zero trust solutions work:
- Never trust, always verify: The core tenet is that no user or device is trusted by default, regardless of location.
- Least privilege: Users are granted only the minimum access necessary for their role or task.
- Real-time analysis: Solutions constantly gather and analyze signals from users, devices, and the network to identify anomalies.
- Automated enforcement: Policies are enforced dynamically, and automated responses, such as blocking suspicious activity, can be triggered.
Key components and capabilities include:
- Device health checks: Ensures devices meet security standards (e.g., up-to-date software) before granting access.
- Identity & access management (IAM): Strong authentication (MFA, biometrics), single sign-on (SSO), and continuous authorization are foundational.
- Zero Trust Network Access (ZTNA): Provides secure, identity-based, application-level access, often replacing traditional VPNs.
- Microsegmentation: Divides a network into smaller, isolated zones to limit the blast radius of a security incident and prevent lateral movement of threats.
- Endpoint security: Focuses on protecting and securing individual devices (laptops, smartphones) that users access the network from.
- AI and machine learning: Used to detect anomalous behavior, score risks in real-time, and automate policy enforcement.
How Zero Trust Solutions Work
Never Trust, Always Verify
Zero trust’s guiding principle is “never trust, always verify.” This means that no user or device, whether inside or outside the corporate network, is trusted by default. Every request to access resources is treated as untrusted until identity, device health, and context are verified. This reduces the risk of internal threats and lateral movement, which are common in breaches where attackers exploit implicit trust within the network.
This verification process is continuous and dynamic, not a one-time check at login. Each interaction and request must pass authentication and meet policy requirements before access is granted. If conditions change, such as the user moving to a different network or the device failing a health check, access can be revoked immediately.
Least Privilege
Implementing least privilege ensures that users and devices have only the minimum access required to perform their tasks. Instead of broad access once inside the network, permissions are tightly controlled and restricted based on the user’s role, context, and need. This containment limits the potential damage from compromised accounts, as attackers cannot move freely or access sensitive data without additional verification.
Least privilege is enforced through detailed policies and granular access controls. Each request is evaluated against these policies, and any divergence from expected behavior triggers additional authentication or blocks the activity.
Real-Time Analysis
Real-time analysis is essential for zero trust architectures, enabling organizations to continuously assess risk factors and adapt access decisions accordingly. Zero trust solutions monitor user activity, device status, and network traffic to detect anomalies or suspicious behavior as it happens. This analysis uses threat intelligence feeds, behavioral analytics, and contextual information to inform immediate security actions.
Continuous monitoring and analysis ensure that security controls are responsive, not static. If an account shows signs of compromise, such as accessing data outside of regular patterns or from an unusual location, the system can trigger alerts, enforce step-up authentication, or block access.
Automated Enforcement
Automated enforcement uses technology to apply security policies uniformly and instantly. When a user or device fails to meet the established criteria during any access attempt, the system automatically blocks or restricts access without manual intervention. Automation replaces human response lag with instant, consistent enforcement, reducing the risk window for attackers.
Automated systems can integrate with other security layers, such as identity providers, endpoint protection platforms, and SIEM tools, to adapt to changes in real time. For example, if a device fails a security scan due to outdated software, access rules can immediately update to quarantine or deny access for that device.
Key Components and Capabilities of Zero Trust Solutions
Identity & Access Management (IAM)
Identity and access management (IAM) platforms are the backbone of zero trust by providing comprehensive control over user identities and their access to resources. IAM solutions handle authentication, authorization, and user lifecycle management, ensuring that only verified users can obtain access and only to approved resources.
They include features like single sign-on, multi-factor authentication, and adaptive access policies based on risk and context. A robust IAM system can dynamically grant or revoke access, respond to suspicious activity, and integrate with other zero trust technologies. By centralizing user authentication, IAM platforms help enforce least privilege and rigorous verification across all access points.
Zero Trust Network Access (ZTNA)
Zero Trust Network Access (ZTNA) replaces traditional VPNs and perimeter-based controls by providing secure, granular access to internal applications based on continuous risk assessment. ZTNA solutions authenticate users and devices before granting access, and limit visibility into the wider network, reducing opportunities for lateral movement by attackers.
Access is granted only to the specific resources required, not the entire network. ZTNA continuously evaluates context, such as user location, device posture, and threat intelligence, to enforce access decisions. In addition, these solutions can automatically adapt policies based on changing risk levels. By decoupling application access from network access, ZTNA creates a more secure environment for remote and hybrid workforces.
Microsegmentation
Microsegmentation divides networks into small, isolated segments, restricting movement between resources and applications. Each segment can have its own access controls, making it much harder for attackers to traverse the network even if they gain a foothold. This isolation is particularly useful for protecting sensitive workloads, such as databases and mission-critical applications.
Implementing microsegmentation requires deep visibility into network traffic and robust policy enforcement tools. Zero trust solutions leverage software-defined networking and real-time analytics to assign and adapt segmentation policies dynamically. By tightly controlling communications between segments, organizations can better contain attacks.
Endpoint Security
Endpoint security focuses on securing all device types (laptops, mobiles, and IoT devices) used to access organizational resources. Solutions constantly monitor device health, configuration, and behavior to detect anomalies or compliance issues. If a device is found to be compromised or running outdated software, access to corporate resources is restricted or denied until the problem is resolved.
Effective endpoint security relies on integration with threat intelligence and response tools. Automated remediation, patch management, and rollback capabilities are often included, allowing organizations to quickly address vulnerabilities.
AI and Machine Learning
AI and machine learning aid in automating threat detection and response. Algorithms analyze vast amounts of user and device activity data, detecting subtle patterns and anomalies that could indicate an emerging threat. These insights power adaptive policies, optimizing security posture in real time without overwhelming security teams with manual alerts.
Machine learning models enable more granular and accurate behavioral profiling, improving the identification of malicious activity versus legitimate use. Zero trust solutions use AI to prioritize risks, enforce policy changes, and automate responses, making security both more efficient and less dependent on human intervention.
Device Health Checks
Device health checks are ongoing assessments of device security posture, configuration, and compliance with corporate policies. Before access is granted, Zero trust solutions verify factors like operating system version, encryption status, patch levels, and the presence of security software. Devices failing these checks are flagged or denied access until they meet the required standards.
Regular health checks provide real-time insight into asset hygiene and help prevent compromised or vulnerable endpoints from becoming attack vectors. Automated remediation steps, such as forcing software updates or quarantining devices, can be triggered by failed health checks. This ensures that only trusted, secure devices participate in the organization’s digital ecosystem.
Related content: Read our guide to zero trust security (coming soon)
Notable Zero Trust Solutions
1. Zscaler Zero Trust Exchange

Zscaler’s Zero Trust Exchange is a cloud-native platform intended to replace traditional perimeter-based security by enforcing least-privileged access to applications, regardless of where users or workloads are located. Instead of allowing broad network access, Zscaler connects users directly to applications using a proxy-based architecture that inspects all traffic, including encrypted data.
Key features include:
- Least-privileged access: Users and devices are connected only to authorized applications, not the network
- Proxy-based architecture: Enables full TLS/SSL traffic inspection without performance degradation
- AI-powered threat protection: Uses machine learning to detect threats and automate responses in real time
- Application cloaking: Makes internal applications invisible to unauthorized users, reducing exposure
- Policy enforcement: Access decisions are based on identity, context, and risk assessment
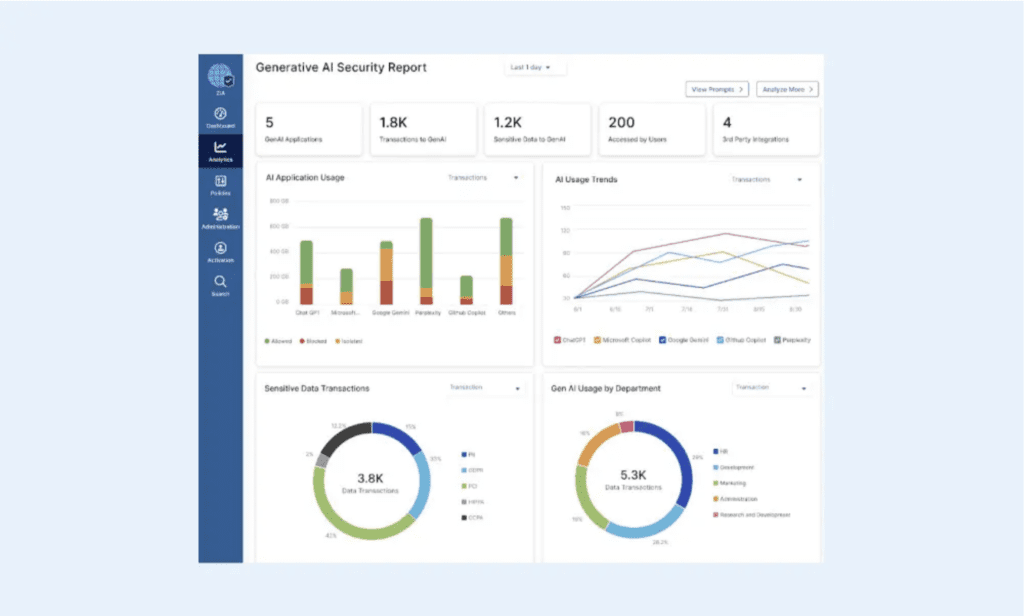
Source: Zscaler
2. Palo Alto Prisma Access

Palo Alto Networks delivers ZTNA 2.0 through Prisma Access, a cloud-native platform that enforces least-privileged access, continuous trust verification, and traffic inspection for all users, devices, and applications without relying on the”allow and ignore” approach. The solution uses patented technologies like App-ID™, User-ID™, and Device-ID™ to provide control over access and behavior.
Key features include:
- Least-privileged access: Uses App-ID™ to enforce precise access at app and sub-app levels
- Continuous trust verification: Monitors device posture, user behavior, and app behavior even after access is granted
- Security inspection: Inspects all traffic, including encrypted, continuously, not just at initial connection
- Unified data protection: Consistent DLP policies for private, SaaS, and cloud-native applications
- Cloud-native architecture: Delivers high performance at scale with simplified deployment and operations
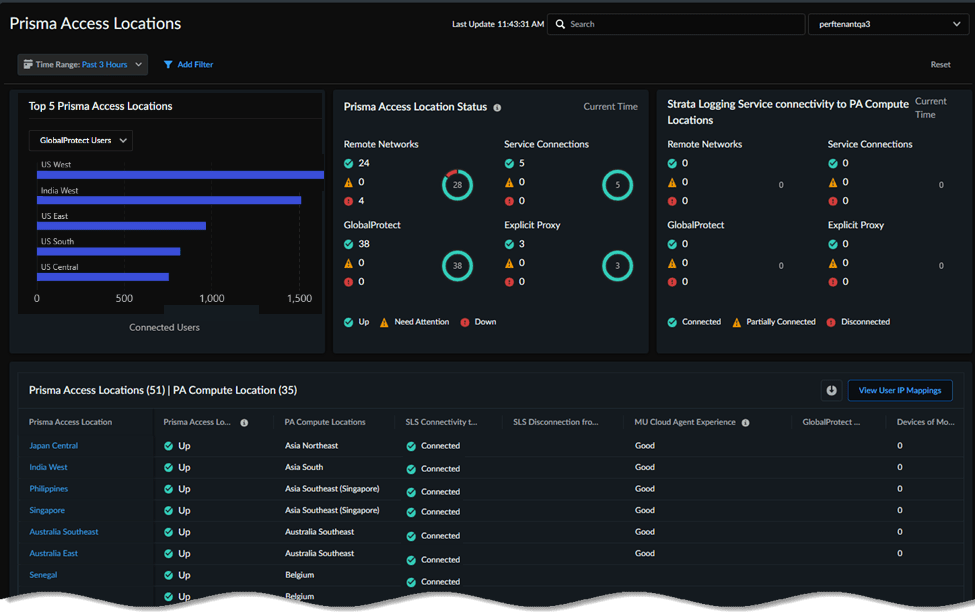
Source: Palo Alto Networks
3. Okta

Okta enables zero trust through an identity-first approach, focusing on verifying who is accessing what, when, and from where across all devices and environments. Rather than relying on network location or static credentials, Okta continuously enforces access based on dynamic user context, device status, and risk signals.
Key features include:
- Identity-centric access control: Grants access based on user identity, not network location
- Adaptive authentication: Adjusts security requirements based on context, device health, and user behavior
- Centralized identity management: Unifies authentication and authorization across cloud, on-prem, and hybrid systems
- Integration with security ecosystem: Works with existing Zero Trust tools to enforce consistent access policies
- Frictionless user experience: Balances security with usability through seamless single sign-on and multi-factor authentication
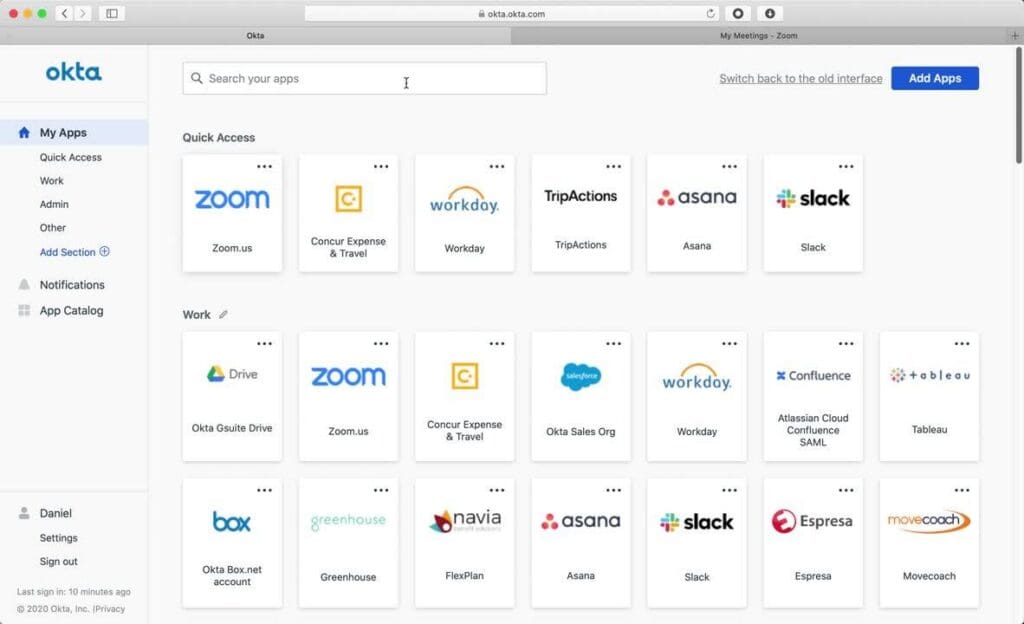
Source: Okta
4. Fortinet Zero Trust Access

Fortinet delivers zero trust access through a tightly integrated set of solutions that provide continuous verification of users and devices, whether they’re on or off the network. Instead of granting broad network access, Fortinet’s approach ensures that users can only access specific applications after their identity and device posture have been verified.
Key features include:
- Continuous verification: Validates user identity and device posture before and during each access session
- Per-session application access: Grants access to individual apps, not the full network, reducing lateral movement
- Consistent policy enforcement: Applies the same zero trust policies to users on-premises and working remotely
- IoT and endpoint security: Detects and controls unknown or unmanaged devices entering the network
- Integrated identity management: Uses FortiAuthenticator and FortiToken for centralized authentication and MFA
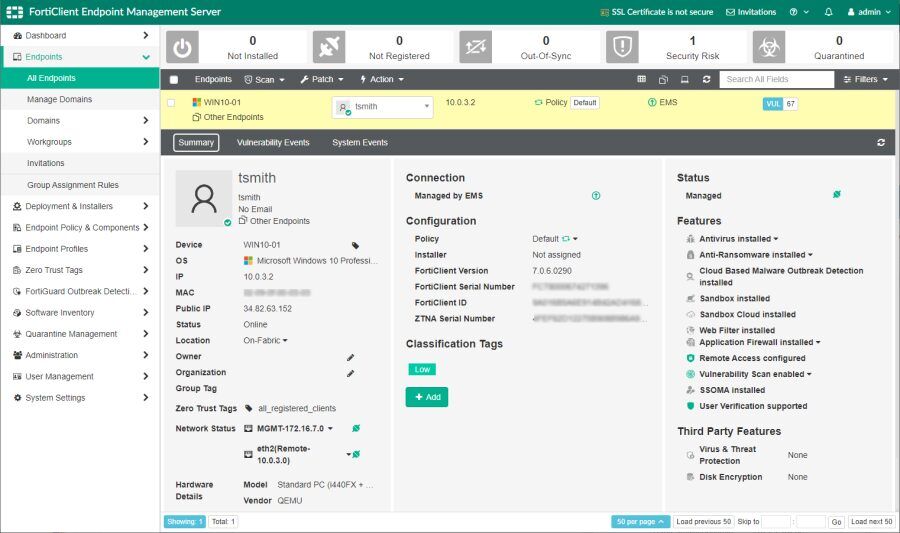
Source: Fortinet
5. Check Point Infinity Platform

Check Point enables zero trust through its Infinity Platform, a unified, AI-powered cybersecurity architecture that applies consistent policies across networks, clouds, users, and devices. Instead of relying on fragmented point solutions, Check Point consolidates threat prevention, identity-based access, and network segmentation into a single management framework.
Key features include:
- Unified security architecture: Combines firewalls, ZTNA, and threat prevention under one platform
- Cross-environment policy enforcement: Applies consistent access policies across cloud, on-prem, and hybrid systems
- Centralized visibility and control: Monitors all users, devices, and traffic from a single pane of glass
- Zero Trust Network Access (ZTNA): Grants application-level access through identity-aware policies and private backbone connectivity
- Granular network segmentation: Prevents lateral movement by isolating workloads and limiting access based on identity and context
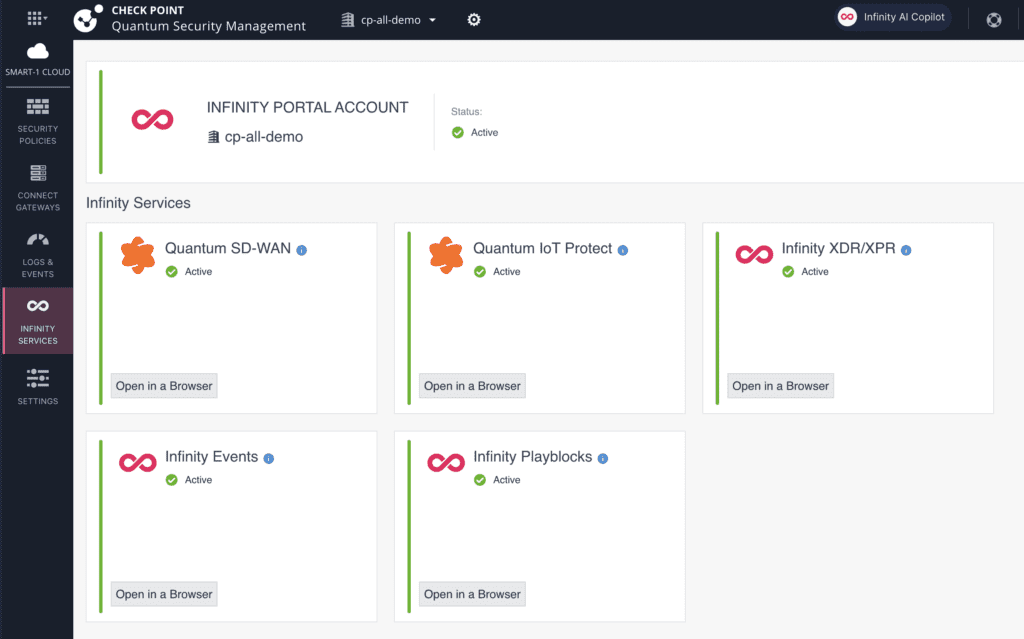
Source: Check Point
6. Illumio Zero Trust Segmentation

Illumio offers Zero Trust Segmentation (ZTS), a proactive containment strategy that assumes breaches will happen and stops them from spreading. Instead of relying solely on detection and response, Illumio focuses on limiting the blast radius of any attack by visualizing communications across workloads and enforcing granular, least-privilege access controls.
Key features include:
- Assume breach mindset: Starts with the expectation that breaches will occur and focuses on containing them
- Granular segmentation policies: Allows only necessary communication between workloads and applications
- Lateral movement prevention: Automatically isolates compromised systems to stop attack spread
- End-to-end visibility: Continuously visualizes how workloads and devices are communicating across the environment
- Least-privilege enforcement: Ensures systems only communicate as needed, based on policy-driven controls
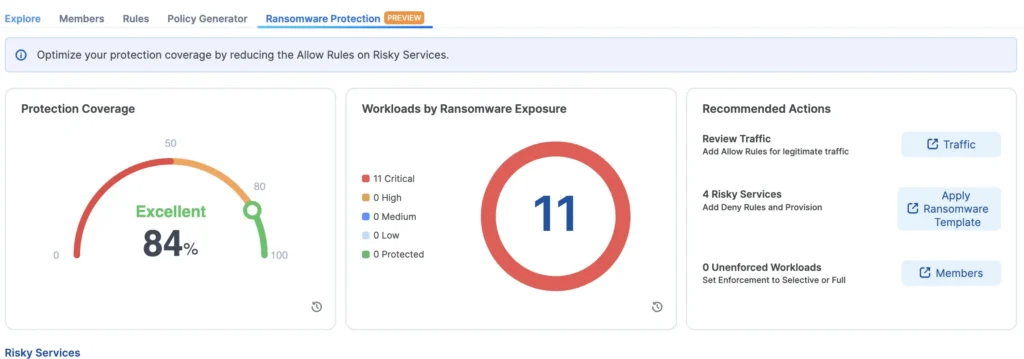
Source: Illumio
7. CrowdStrike Falcon Identity Protection

CrowdStrike delivers zero trust through Falcon® Identity Protection, a cloud-native solution that unifies identity and endpoint security to protect against identity-driven attacks. Rather than relying on static access controls, Falcon continuously evaluates risk across identities, devices, and environments using AI-driven threat detection and adaptive policies.
Key features include:
- Unified identity and endpoint protection: Combines identity and device-level insights to detect and respond to threats in real time
- AI-powered threat detection: Uses behavioral baselines and anomaly detection to identify sophisticated attacks early
- Risk-based conditional access: Enforces MFA and access decisions dynamically, based on live risk assessments
- Cloud-native architecture: Simplifies deployment and reduces overhead with a single lightweight agent
- Identity visibility: Identifies compromised credentials and over-privileged access across identity providers
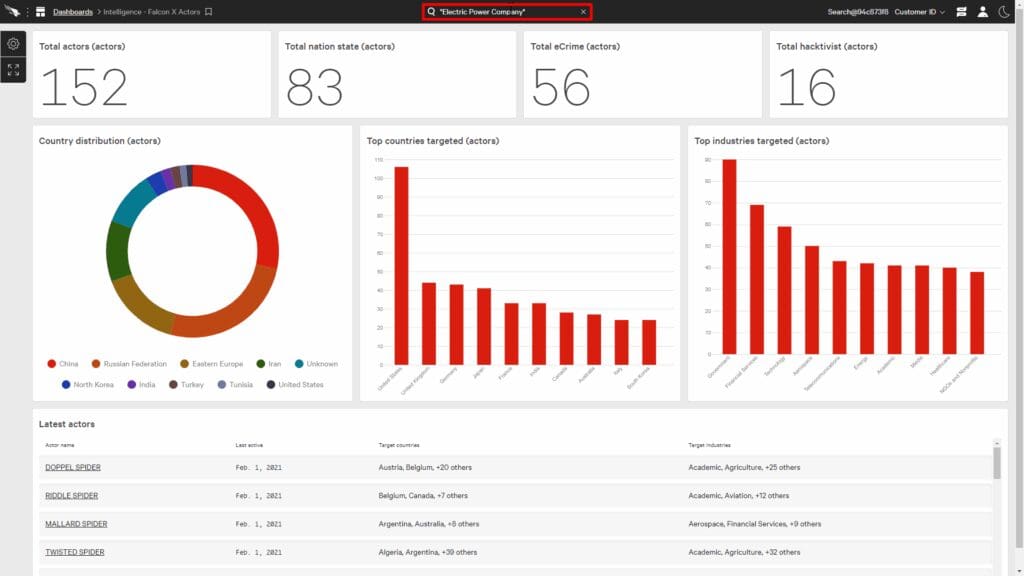
Source: CrowdStrike
8. Cloudflare
Cloudflare Access delivers Zero Trust Network Access (ZTNA) through a cloud-native platform that replaces legacy VPNs with fast, secure, and scalable access controls. Designed to provide least-privilege access to internal applications, infrastructure, and AI tools, Cloudflare Access continuously evaluates identity, device posture, and context for every request.
Key features include:
- Least-privilege access: Enforces per-resource access based on user identity, device posture, and context
- VPN replacement: Eliminates the need for traditional VPNs while improving speed and user experience
- Fast, reliable performance: Delivers low-latency access to internal resources through Cloudflare’s global network
- Support for all applications: Secures web, non-web, SaaS, and internal tools, including AI systems and legacy apps
- Simplified integration: Uses lightweight, composable connectors and one-time setup for rapid deployment
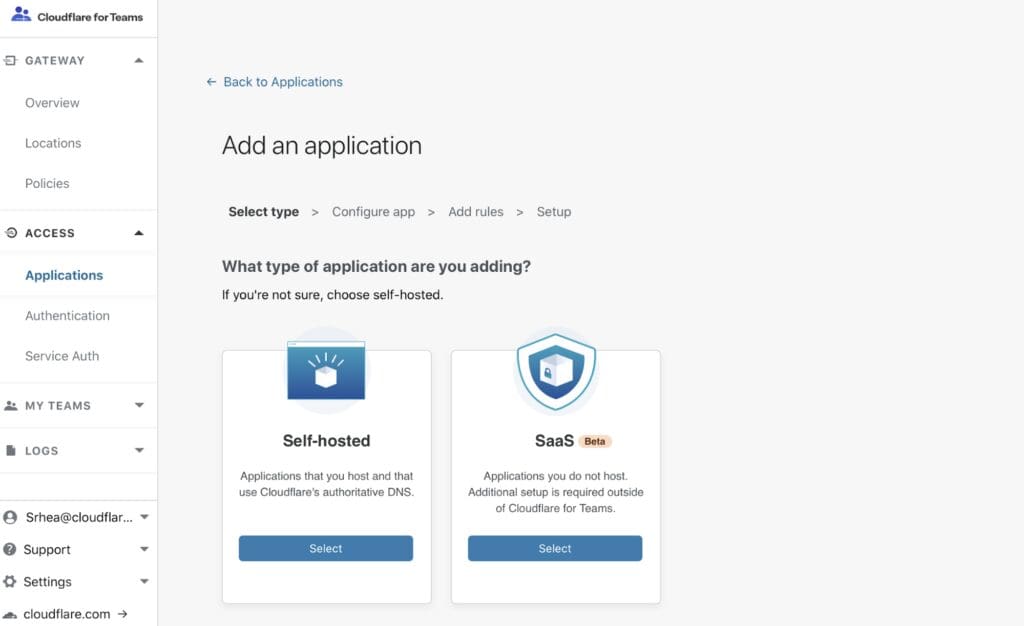
Source: Cloudflare
9. Netskope SSE

Netskope delivers zero trust through its Security Service Edge (SSE) platform, enabling secure, adaptive access across users, devices, applications, and data. Designed to align with SASE architecture, Netskope applies zero trust principles across four core transformation stages: network, security, application, and data.
Key features include:
- Zero trust engine: Dynamically evaluates identity, device, application, and risk context for transactions
- Unified SSE platform: Consolidates ZTNA, SWG, CASB, and DLP into a single agent, console, and policy framework
- Four-stage transformation coverage: Secures every layer (network, security, application, and data) through adaptive controls
- Cloud-native architecture: Delivers security at scale with Netskope’s global NewEdge network for low-latency performance
- Visibility and data protection: Inspects web, SaaS, and IaaS traffic for threat detection and sensitive data control
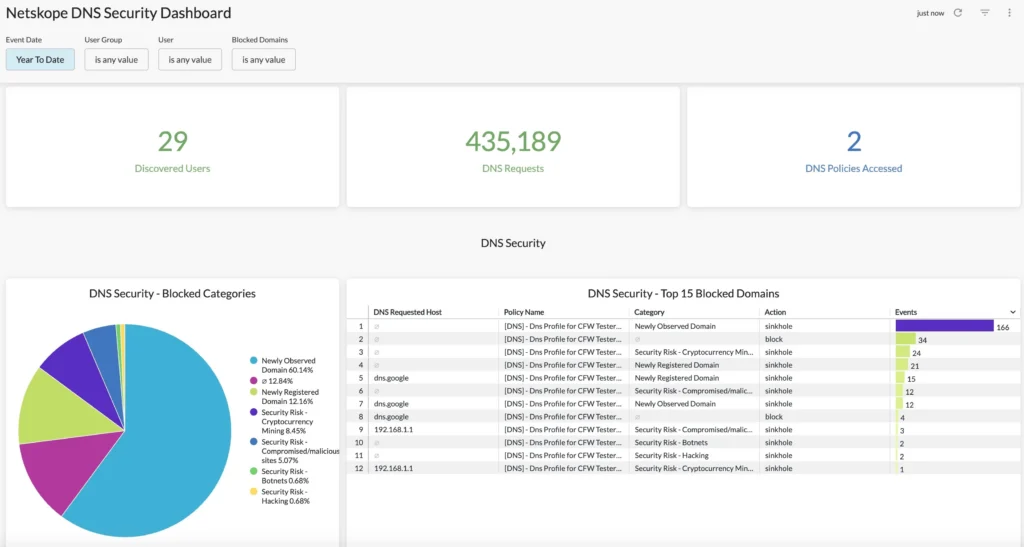
Source: Netskope
How Exabeam Facilitates Zero-trust Telemetry Across the Entire Security Story
Exabeam’s security operations platform supports Zero Trust architectures by providing comprehensive telemetry and advanced analytics that complement core Zero Trust solutions. While not a primary Zero Trust provider, Exabeam specializes in ingesting data from various sources, including identity and access management systems, network devices, and endpoint security tools. This data collection is crucial for a Zero Trust model, as it supplies the granular information needed to continuously verify every access request and assess ongoing risk.
By leveraging behavioral analytics and machine learning, Exabeam can detect anomalies and suspicious activities that might indicate a compromise or a deviation from established Zero Trust policies. For instance, if a user attempts to access a resource from an unusual location, or if a device’s behavior deviates from its established baseline, Exabeam can flag these events. This capability provides essential context and alerts to security teams, enhancing their ability to respond to potential threats even within a “never trust, always verify” framework.
Ultimately, Exabeam helps integrate the vast streams of data generated within a Zero Trust environment into a cohesive security narrative. It aids in understanding the “who, what, when, and where” of access attempts and resource interactions. This contributes to the overall effectiveness of a Zero Trust strategy by ensuring that even subtle indicators of compromise are identified and brought to the attention of security personnel for informed decision-making and rapid response.
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.

