
-
- Home
>
-
- Blog
>
-
- SIEM Trends
Supercharged Protection: Preventing EV Chargers Cyberattacks with LogRhythm
- Jun 18, 2023
- Leonardo Hutabarat
- 2 minutes to read
Table of Contents
In today’s digital age, cyberattacks are becoming increasingly frequent and sophisticated, posing serious threats to both digital and physical infrastructures. Incidents like Stuxnet, which targeted power plants, have demonstrated the dangerous interrelationship between cyberattacks and physical damage. As the adoption of smart city technologies accelerates, the potential for cyberattacks on critical infrastructure grows significantly.
The Rising Threat to EV Charging Stations
Electric Vehicle (EV) Charging Stations are a critical component of smart city infrastructure and are becoming common in major cities worldwide. These stations, essential for the proliferation of electric vehicles, have become prime targets for cyberattacks due to their public accessibility and integration with the power grid. A compromised EV charging station can disrupt the power supply, gather sensitive data from vehicles, and cause widespread issues.
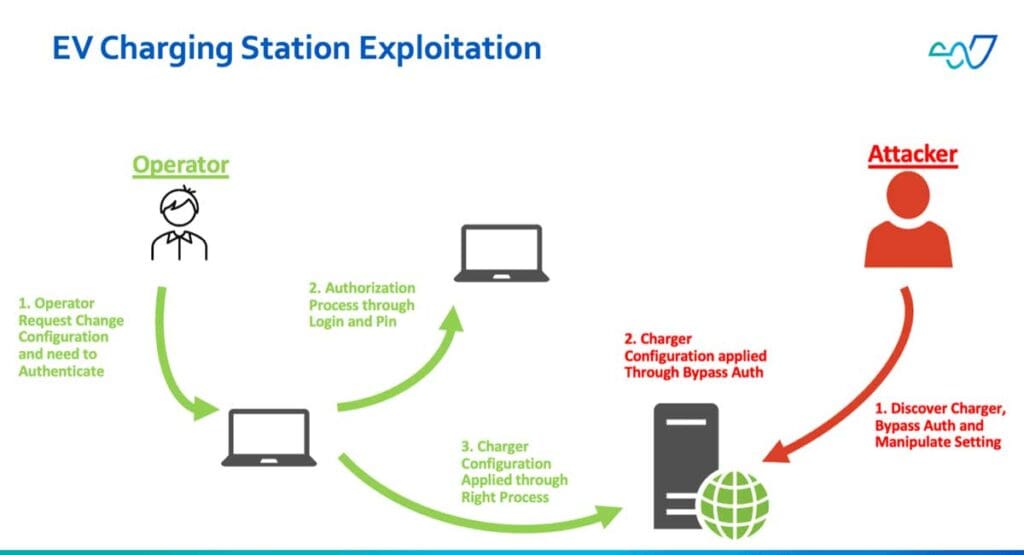
Understanding the Vulnerabilities
EV Charging Stations are vulnerable through their three primary charging methods: Conductive, Inductive, and Battery Swap. Conductive Charging, which involves directly connecting a cable to the vehicle, is the most susceptible to cyberattacks. Recently, significant vulnerabilities have been identified in the ABB Terra AC wallbox, specifically versions 1.6.5 for the UL32A model and 1.5.5 for the UL4080A model. These vulnerabilities, cataloged as CVE-2023-0863 and CVE-2023-0864, allow attackers to exploit the system via Bluetooth Low Energy (BLE), potentially taking control of the station to eavesdrop on communications or alter configurations.
Case Study: ROOTK1T Hacker Group
There are allegations that the hacker group R00TK1T has accessed the GO TO-U backend system, based on posts showing several screenshots depicting the backend systems of TNBX and TNB Electron EV chargers, which run on the platform. While no breach has been confirmed, these reports underscore the critical need for robust cybersecurity measures to safeguard EV charging stations from potential threats.
Mitigation Strategies with LogRhythm SIEM
To counter these risks, it is crucial to implement timely patches and activate Security Event Notifications for “AttemptedReplayAttacks.”
LogRhythm SIEM provides a comprehensive solution to monitor and detect exploitation attempts. By leveraging the SIEM’s capabilities, organizations can identify suspicious activities, such as BLE attacks, in real time.
For instance, the following log entry indicates a detected BLE attack:{
"SecurityEventNotification": {
"type": "AttemptedReplayAttacks",
"techInfo": "bleAttacks",
"timestamp": "2024-02-18T20:33:38.000Z"
}
}
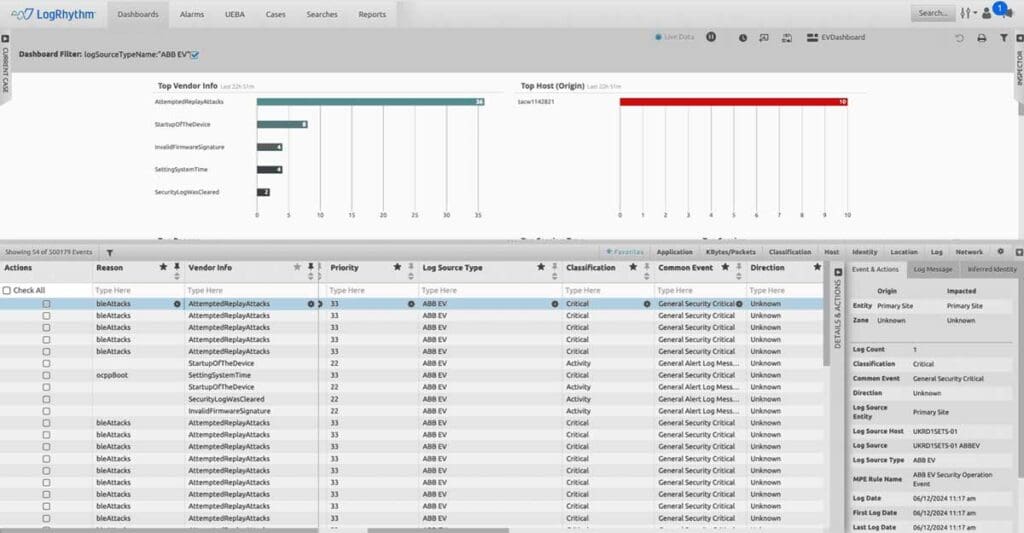
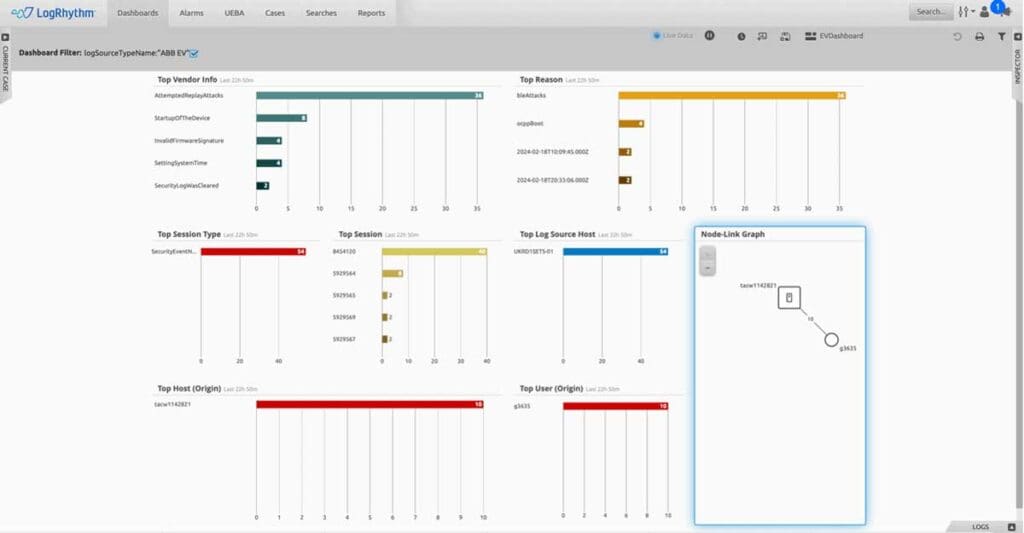
Advanced Monitoring with LogRhythm SIEM
LogRhythm SIEM’s advanced monitoring tools help organizations understand the normal activity of their EV infrastructure, making it easier to detect anomalies. Suspicious activities, such as cleared security logs, invalid firmware signatures, or unexpected device startups, can signal potential cyberthreats.
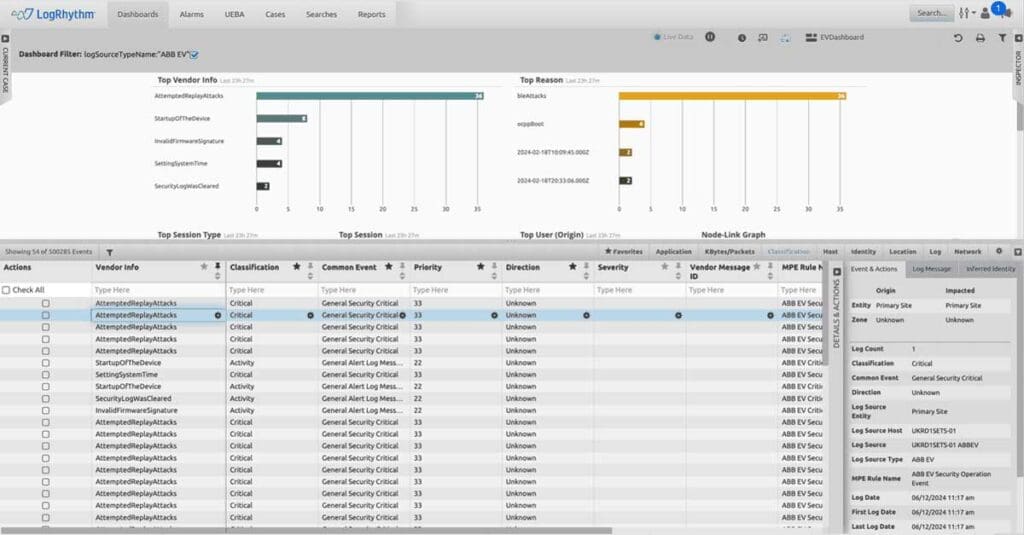
The dashboard offers a consolidated and holistic view of security across Electric Vehicle infrastructure, integrating data from OT, IoT, and IT systems to provide comprehensive monitoring and threat detection capabilities.
Conclusion
As cyberthreats continue to evolve, it is essential for organizations to protect all aspects of their infrastructure, including EV charging stations. These stations, though seemingly mundane, can have significant impacts if compromised. LogRhythm SIEM plays a crucial role in enhancing security visibility and ensuring the resilience of smart city infrastructure.
By implementing robust monitoring and detection capabilities, organizations can safeguard their EV charging stations against cyberattacks, ensuring secure and reliable service for all users.To learn more about how you can bolster your defenses, schedule a demo today.

Leonardo Hutabarat
Director Sales Engineering, APJ | Exabeam | Leonardo Hutabarat is Director Sales Engineering, APJ at Exabeam. He works with customers and partners to increase their cybersecurity posture. He has over 20 years of experience in the cybersecurity field. Leonardo received a Bachelor's degree in Electrical Engineering and an MBA. He also has certifications in CISSP, CISM, CISA, CRISC, GSEC, and 50+ others cybersecurity certifications. Leonardo is a seasoned public speaker at cybersecurity events such as Gartner, GovWare, Cyber DSA, and ISC2. Leonardo contributes to the community as a SANS mentor and lecturer in local universities. He enjoys sharing his expertise with journalists and media outlets such as CNN, Channel News Asia, AsiaOne, The Business Times, and The Straits Times on recent cyberattacks and related topics.
More posts by Leonardo HutabaratLearn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.
-
 Blog
Blog
Making the Switch: A Step-by-Step Guide to Migrating from On-premises to Cloud-native SIEM
- Show More





