
-
- Home
>
-
- Explainers
>
-
- Securonix
Securonix: Solution Overview, Limitations and Top 5 Alternatives
- 8 minutes to read
Table of Contents
What Is Securonix?
Securonix is a cybersecurity platform specializing in identifying, analyzing, and responding to security threats. It uses analytics to provide visibility into network activities, aiming to detect suspicious behavior before it manifests into a breach.
Securonix combines user and entity behavior analytics (UEBA), security information and event management (SIEM), and threat detection capabilities to support threat identification and response while reducing false positives.
Securonix operates through a cloud-native architecture, allowing integration and scalability. This platform offers threat intelligence through data correlation across various sources. Securonix provides automated response mechanisms that allow organizations to react to threats potentially.
This is part of an extensive series of guides about information security.
Securonix Products
Here’s an overview of the various security products offered by Securonix.
Securonix Platform
The Securonix platform is a cloud-native SIEM solution that improves threat detection, investigation, and response (TDIR) with AI-powered analytics. By integrating SIEM and SOAR capabilities, the platform automates data analysis, reduces false positives, and provides real-time threat detection. It offers scalability through a flexible cybersecurity mesh architecture, allowing integration with existing security tools and data sources.
Key features of the Securonix platform include:
- Cybersecurity mesh: Integrates with various security tools, clouds, or data lakes.
- AI-reinforced platform: Intends to improve threat detection accuracy and response through artificial intelligence.
- Scalable data lake: Provides fast access to one year of hot data for threat hunting and investigations.
- Threat content-as-a-service: Continuously delivers curated threat intelligence to reduce false positives.
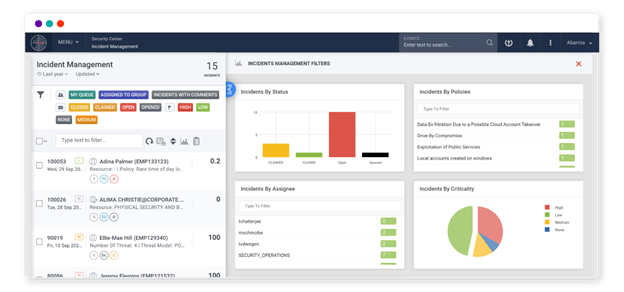
Source: Securonix
Securonix EON
Securonix EON is an AI-driven cybersecurity solution attempting to improve the speed, precision, and effectiveness of security operations. It leverages AI to streamline decision-making, reduce manual tasks, and improve operational efficiency. With integration capabilities and threat detection features, Securonix EON intends to provide a defense against both external and insider threats.
Key features of Securonix EON include:
- AI-reinforced platform: Uses AI to automate and optimize security operations.
- Cybersecurity mesh: Integrates with existing security tools, clouds, and data lakes to maximize security investments.
- Insider Threat Psycholinguistics: Like other solutions in the category, detects insider threats by analyzing behavioral patterns and intent-based indicators.
- InvestigateRX: The use of AI-driven summaries to potentially reduce investigation times.
Securonix Unified Defense SIEM
Securonix Unified Defense SIEM is a scalable, cloud-based solution that improves threat TDIR capabilities for modern enterprises. Built on Snowflake’s data cloud, it enables organizations to handle volumes of data while providing end-to-end threat defense.
Key features of Securonix Unified Defense SIEM include:
- Single-tier storage model: Provides a scalable storage solution for data searches.
- Scalable data cloud: Leverages Snowflake’s data cloud to manage data requirements, offering 365 days of ‘hot’ searchable data for continuous visibility.
- Threat content-as-a-service: Provides threat content to potentially improve threat coverage and detection accuracy.
- Proactive defense: Enables collaborative threat intelligence sharing and automated threat sweeps.
- Unified TDIR experience: Offers a workflow with built-in SOAR capabilities for detection, investigation, and response.
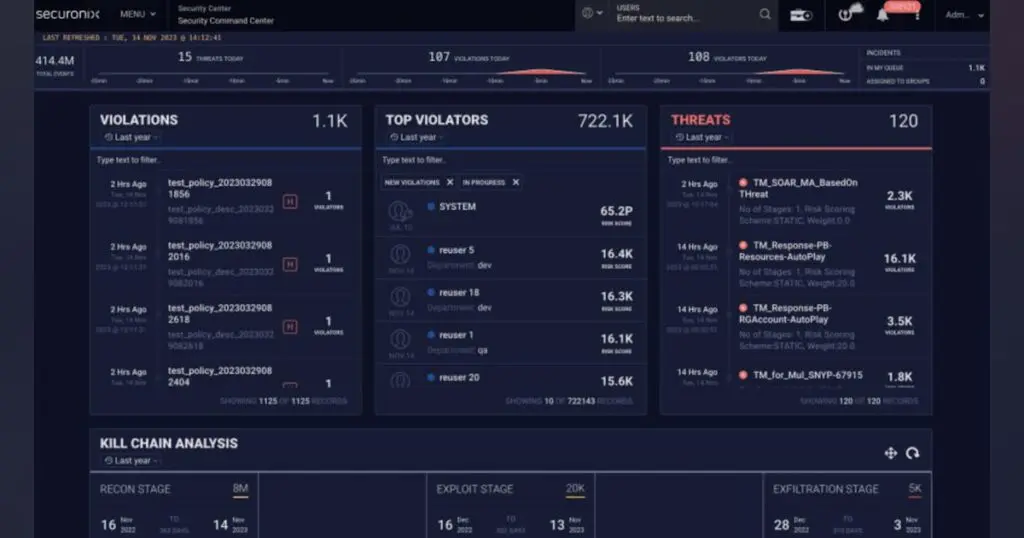
Source: Securonix
Securonix UEBA
Securonix user and entity behavior analytics (UEBA) is a solution to detect anomalous behavior by leveraging machine learning and behavior analysis. It provides visibility into user and entity actions, to potentially identify insider threats and subtle security risks.
Key features of Securonix UEBA include:
- SIEM integration: Deploys on top of an existing SIEM.
- Industry-leading behavior analytics: Uses machine learning algorithms and out-of-the-box use cases for threat detection.
- Cloud visibility: Extends monitoring to cloud environments through built-in APIs for cloud platforms and applications.
- Insider threat monitoring: Detects deviations from normal behavior by combining user context with event data, mitigating the risk of insider threats.

Source: Securonix
Securonix SOAR
Securonix security orchestration, automation, and response (SOAR) is a solution within the Securonix Unified Defense SIEM. Built directly into the platform, Securonix SOAR automates security operations, reducing manual interventions and helping teams respond to threats more efficiently.
Key features of Securonix SOAR include:
- Multi-tenant deployment: Supports multi-tenant environments, enabling centralized actions across multiple tenants from a single console.
- Integrated platform: Combines detection and response into a single workflow.
- Cloud-native SOAR: Built into the SIEM with no additional infrastructure to manage.
- Simplified licensing: Offers a flat pricing model that allows unlimited analyst seats without extra costs.
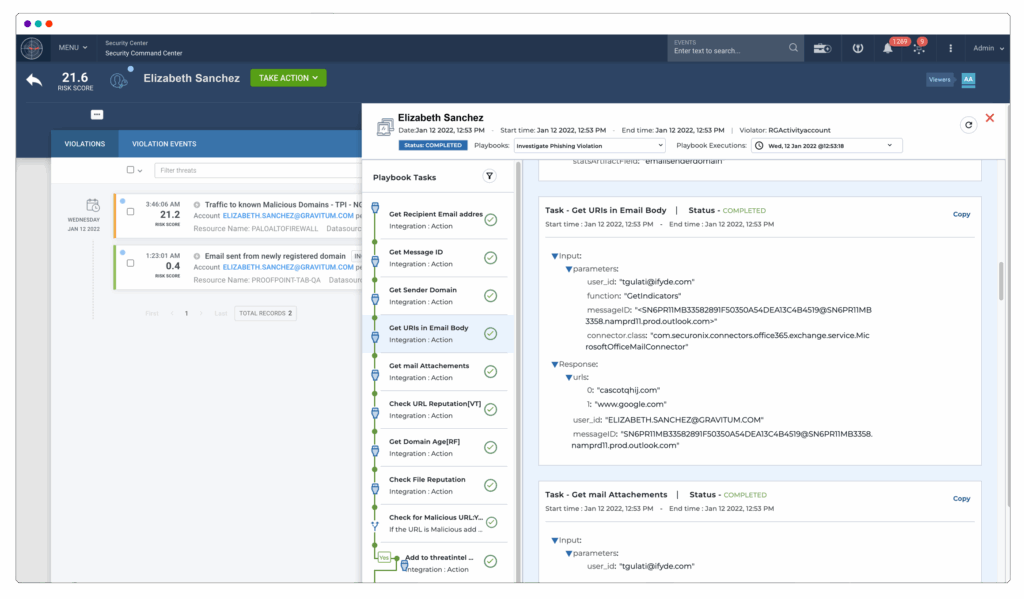
Source: Securonix
Securonix ATS
Securonix autonomous threat sweeper (ATS) automates the detection and response to threats. Supported by threat intelligence from Securonix Threat Labs, ATS performs autonomous sweeps of historical event data, ensuring rapid identification and mitigation of potential risks.
Key features of Securonix ATS include:
- Proactive security: Scans logs and historical data for emerging threats and assesses exposure.
- Curated threat advisories: Provides continuously updated threat intelligence, combining research from Securonix Threat Labs with community-sourced and industry-leading data.
- Multi-vector detection: Uses a blend of indicators of compromise (IOC) and tactics, techniques, and procedures (TTP) detection to trace both known and unknown threats.
- Reporting and alerting: Automates reporting, incident creation, and alerting.
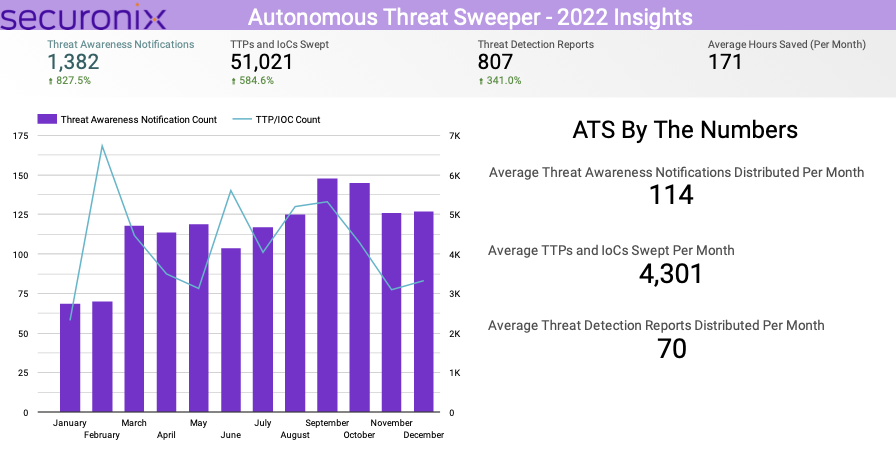
Source: Securonix
Securonix Investigate
Securonix Investigate accelerates the threat investigation process by providing on-demand context enrichment and supporting collaboration among analysts. Integrated directly into the Securonix platform, it allows teams to share insights and knowledge within the investigation workflow without needing external tools like ticketing or messaging systems.
Key features of Securonix Investigate include:
- Single-view context window: Consolidates details into one view.
- On-demand data enrichment: Gathers relevant data from internal and external sources, keeping the investigation context current.
- Integrated AI: Uses AI-driven natural language capabilities to build threat content.
- Workflow annotations: Enables analysts to annotate and document observations within the investigation.
- Dedicated team channels: Enables collaboration through specific communication channels, allowing information sharing across groups like red, blue, or purple teams.
Source: Securonix
Securonix Limitations
While Securonix is a respected solution, it comes with some limitations. The following were reported by users on the G2 platform:
- Complex querying for alerts: Users often find it difficult to write queries for alert searches, which can hinder threat investigation.
- Slow support: Securonix’s support is frequently criticized for slow response times. Some users have reported that support staff lack the expertise to resolve issues, causing delays in addressing technical problems.
- Not suited for smaller organizations: The platform is intended for large organizations, and smaller businesses may not fully benefit from its machine learning capabilities or complex customization options.
- Deployment challenges: Implementing Securonix can be complex, and there are limited connectors for integrating external data sources, which can complicate data ingestion and analysis.
- Vendor lock-in: Due to the platform’s customization requirements and complexity, organizations may experience vendor lock-in, making it difficult to switch providers or adopt other solutions.
- Customization process delays: Although Securonix allows high levels of customization, the process can be slow and unclear, requiring dedicated internal subject matter experts (SMEs) to smooth the implementation and rule creation processes.
Notable Securonix Competitors and Alternatives
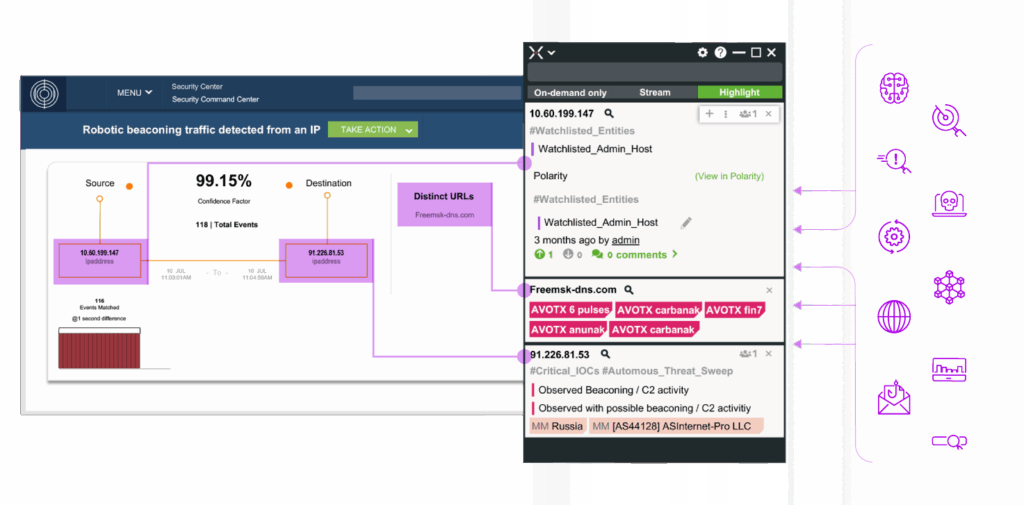
1. Exabeam
Exabeam is a leading provider of security information and event management (SIEM) solutions, combining UEBA, SIEM, SOAR, and TDIR to accelerate security operations. Its Security Operations platforms enables security teams to quickly detect, investigate, and respond to threats while enhancing operational efficiency.
Key Features:
- Scalable log collection and management: The open platform accelerates log onboarding by 70%, eliminating the need for advanced engineering skills while ensuring seamless log aggregation across hybrid environments.
- Behavioral analytics: Uses advanced analytics to baseline normal vs. abnormal behavior, detecting insider threats, lateral movement, and advanced attacks missed by signature-based systems. Customers report that Exabeam helps detect and respond to 90% of attacks before other vendors can catch them.
- Automated threat response: Simplifies security operations by automating incident timelines, reducing manual effort by 30%, and accelerating investigation times by 80%.
- Contextual incident investigation: Since Exabeam automates timeline creation and reduces time spent on menial tasks, it cuts the time to detect and respond to threats by over 50%. Pre-built correlation rules, anomaly detection models, and vendor integrations reduce alerts by 60%, minimizing false positives.
- SaaS and cloud-native options: Flexible deployment options provide scalability for cloud-first and hybrid environments, ensuring rapid time to value for customers. For organizations who can’t, or won’t move their SIEM to the cloud, Exabeam provides a market-leading, full featured, and self-hosted SIEM.
- Network visibility with NetMon: Delivers deep insight beyond firewalls and IDS/IPS, detecting threats like data theft and botnet activity while making investigation easier with flexible searching. Deep Packet Analytics (DPA) also builds on the NetMon Deep Packet Inspection (DPI) engine to interpret key indicators of compromise (IOCs).
Exabeam customers consistently highlight how its real-time visibility, automation, and productivity tools powered by AI, uplevel security talent, transforming overwhelmed analysts into proactive defenders while reducing costs and maintaining industry-leading support.
2. Sumo Logic

Sumo Logic is a cloud-native SIEM solution to unify threat detection, investigation, and response across hybrid and multicloud environments. It enables security teams to monitor and respond to security incidents while simplifying operations through automation and continuous intelligence.
Key features of Sumo Logic include:
- Unified platform: Combines logs, metrics, and security analytics in one platform.
- Cloud-native architecture: Delivers a scalable SIEM that adapts to dynamic environments without on-premises infrastructure.
- Real-time analytics: Provides continuous data ingestion and analytics, enabling immediate threat detection.
- Integrated SOAR capabilities: Automates workflows across investigation and response, helping improve SOC efficiency.
- Threat intelligence integration: Enriches events with threat intelligence feeds, helping analysts to prioritize and contextualize alerts.
- Out-of-the-box content: Offers prebuilt rules, dashboards, and compliance reporting aligned to industry standards like MITRE ATT&CK and NIST.

Source: Sumo Logic
3. Microsoft Sentinel

Microsoft Sentinel (formerly Azure Sentinel) is a cloud-native SIEM platform combined with SOAR capabilities. It provides a solution for detecting, investigating, and responding to cyber threats across cloud and on-premises environments. Built on Azure, it leverages AI, automation, and integrated threat intelligence.
Key features of Microsoft Sentinel include:
- Threat hunting: Provides hunting capabilities with tools built on the MITRE ATT&CK framework, allowing analysts to search for and identify threats.
- Data collection at scale: Gathers data across users, devices, applications, and infrastructure, supporting on-premises and multi-cloud environments.
- Built-in threat detection: Uses Microsoft’s threat intelligence stream and customizable analytics to detect threats.
- AI-enhanced investigation: Automates threat investigations using AI, with interactive graphs to trace and analyze incidents.
- Customizable playbooks: Automates incident response through workflows created with Azure Logic Apps, integrating with third-party tools like ServiceNow.
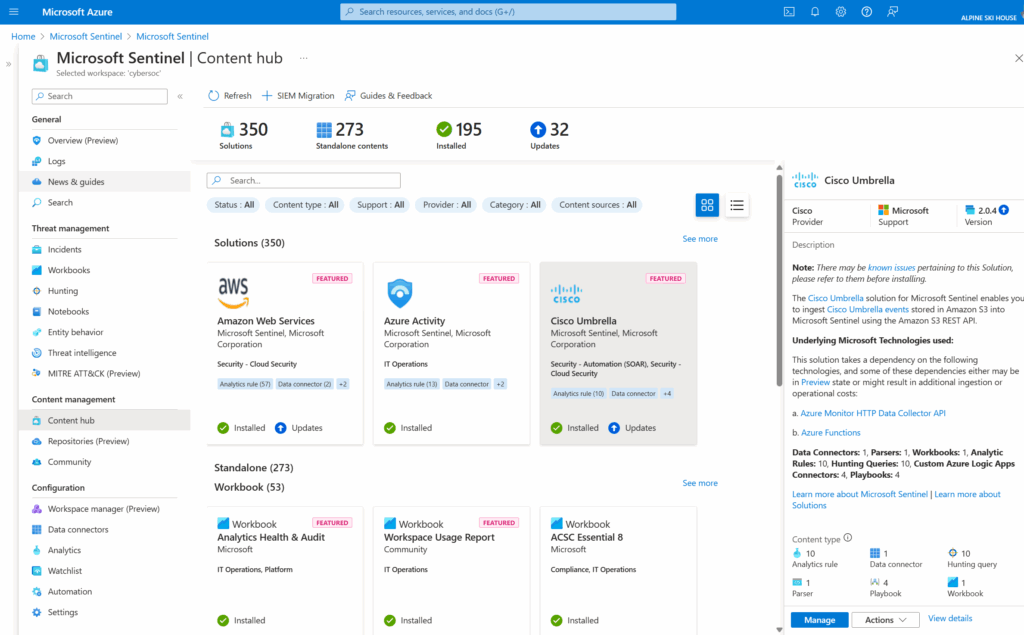
Source: Microsoft
4. Splunk Enterprise Security

Splunk Enterprise Security is a SIEM platform to provide visibility for security teams. It offers scalability and data ingestion capabilities from various sources, improving both operational efficiency and threat response. Splunk Enterprise Security integrates natively with Splunk SOAR, simplifying security operations.
Key features of Splunk Enterprise Security include:
- Automated playbooks: Leverages Splunk SOAR’s automation for incident response.
- Deep visibility: Ingests, normalizes, and analyzes data from various sources.
- Risk-based alerting (RBA): Attempts to focus on high-priority threats through context-driven risk scoring.
- Curated detections: Leverages out-of-the-box detections aligned with standards like MITRE ATT&CK, enabling faster threat identification and remediation.
- Unified TDIR workflows: Integrates detection, investigation, and response workflows through Mission Control.
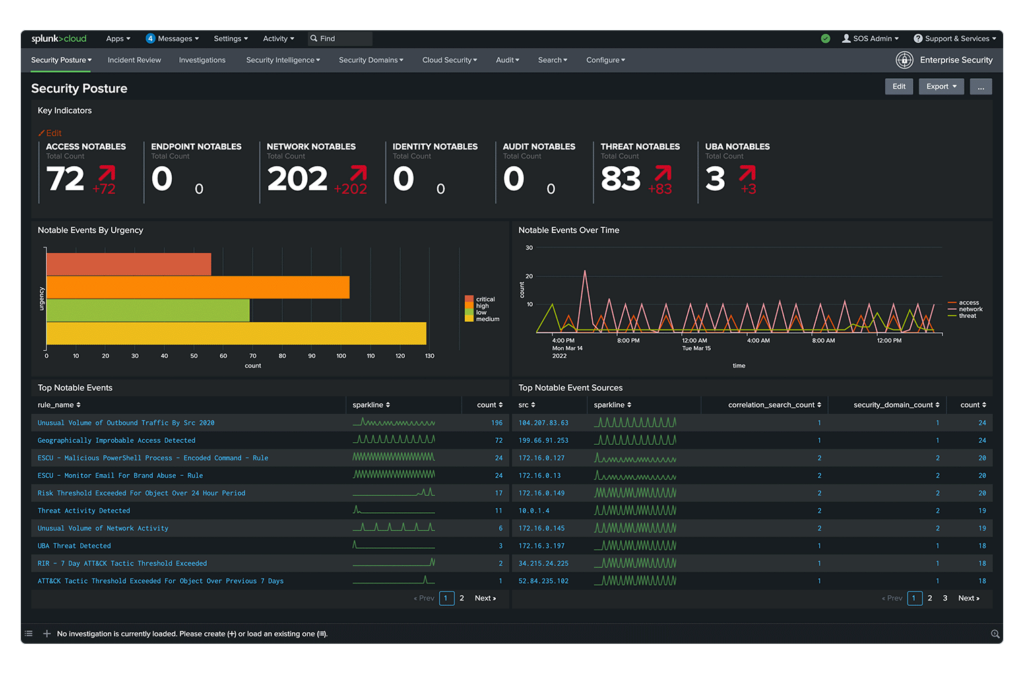
Source: Splunk
5. Rapid7 InsightIDR
Rapid7 InsightIDR is a cloud-native security information and event management platform for hybrid environments. It provides scalable, elastic security management for threat detection and response. It integrates AI-driven behavioral detections, advanced analytics, and threat intelligence.
Key features of Rapid7 InsightIDR include:
- Deception technology: Lures attackers with decoy assets, providing early warning of malicious activity.
- SIEM and EDR integration: Combines security information and event management with endpoint detection and response for visibility and protection.
- User and entity behavior analytics (UEBA): Detect anomalous behavior and identify potential insider threats or compromised accounts.
- Network traffic analysis: Monitors network activity to identify suspicious patterns and improve threat detection.
- Embedded threat intelligence: Leverages an up-to-date library of detections mapped to the MITRE ATT&CK framework.

Source: Rapid7
Conclusion
Securonix offers a comprehensive cybersecurity solution with its cloud-native SIEM, UEBA, and SOAR capabilities, providing threat detection, analysis, and automated response for large-scale organizations. While the platform excels in scalability, AI-driven insights, and behavior analytics, it’s most effective for enterprises that can manage the complexity of deployment and customization.
Learn more about the Exabeam Security Operations Platform
See Additional Guides on Key Information Security Topics
Together with our content partners, we have authored in-depth guides on several other topics that can also be useful as you explore the world of information security.
Cyber Threat Intelligence
Authored by Exabeam
- [Guide] Best Insider Threat Management Software: Top 9 Solutions in 2025
- [Guide] Best Threat Intelligence Tools: Top 8 Providers in 2025
- [Whitepaper] 2024 State of the Security Team Research
- [Product] Exabeam | AI-Driven Security Operations
FortiSIEM
Authored by Exabeam
- [Guide] FortiSIEM: Key Features, Pricing, Limitations & Alternatives
- [Guide] 10 Fortinet Competitors to Know in 2025
- [Blog] How SIEM Helps With Cyber Insurance
- [Product] LogRhythm SIEM | Self-Hosted SIEM for Advanced TDIR
Software Supply Chain Security
Authored by Oligo
- [Product] Oligo ADR | Instant Attack Detection & Supply Chain Security
- [Guide] Ultimate Guide to Software Supply Chain Security in 2025
- [Guide] Supply Chain Attack: How It Works and 5 Recent Examples
- [Blog] ShellTorch: Multiple Critical Vulnerabilities in PyTorch TorchServe Threatens Countless AI Users
Learn More About Exabeam
Learn about the Exabeam platform and expand your knowledge of information security with our collection of white papers, podcasts, webinars, and more.