In July last year, we released our research report on the Anatomy of a Ransomware attack in which we looked into both the financial model of ransomware and then detection as it unfolds. Due to the recent WannaCry ransomware craze, we think it’s time to revisit.
When we addressed ransomware last year, we made a significant comment about the ever-evolving nature of malicious software. We predicted that in the near future (evidently now) ransomware will move on from being a standalone software with tactical strategy to encrypt endpoints, into a “ransom-worm,” a more sophisticated strain that is able to use exploit kits and zero-day vulnerabilities to infect machines on a global scale, scan hosts on the network, and pivot. This is one of those times that I’m unhappy to say we were right.
WannaCry is the next generation of ransomware, still using all of the common and known techniques of ransomware but with a twist on the infection vector using vulnerabilities (in this case Eternalblue modules and the Doublepulsar backdoor, made famous by the NSA)
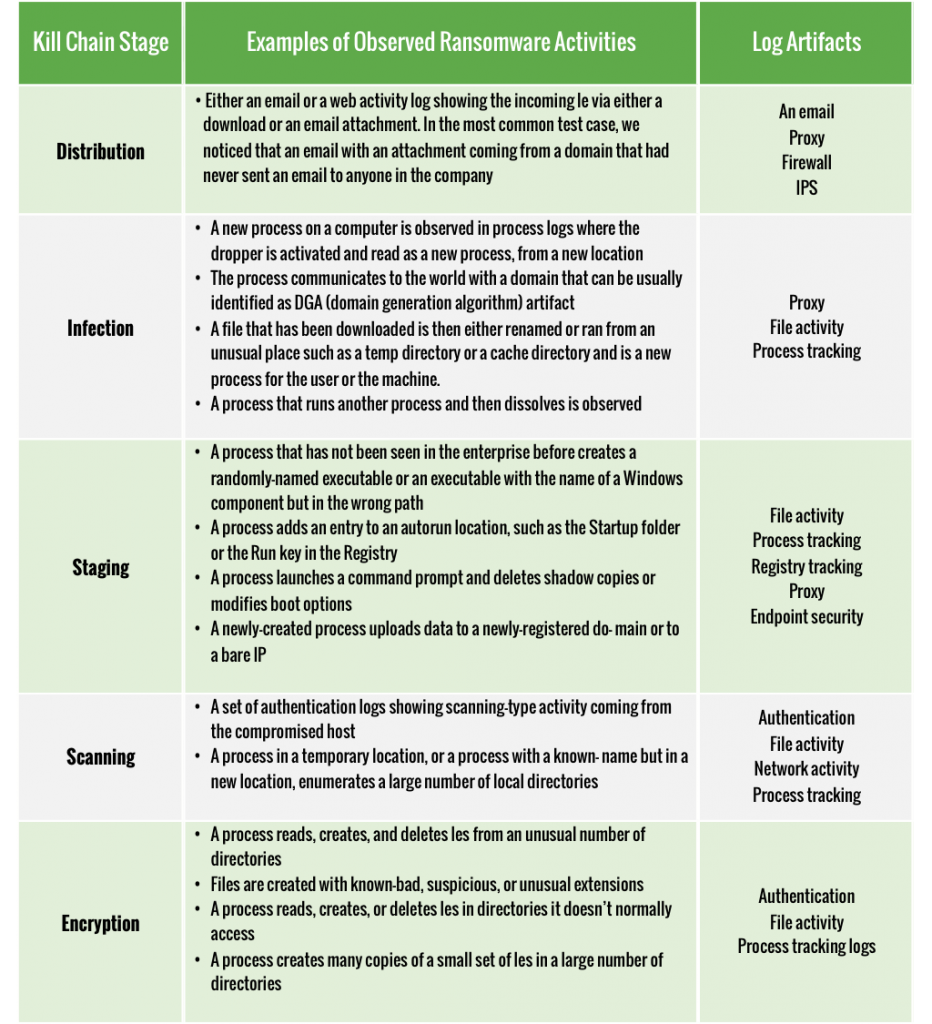
WannaCry behaves no different than other ransomware in that any other aspect, which means the same kill chain we described in our research paper (read for more detail) stands, including the various signals.

How can I learn about WannaCry?
For those who want to learn more about WannaCry, I recommend reading Talos’s WannaCry analysis, here. They have done a fantastic job in analyzing WannaCry and the artifacts/IOCs involved.
In our research paper, there’s a cheat sheet that explores what signals are available throughout the environment that may indicate that a Ransomware attack is unfolding, we recommend handing that to your incident response team to make sure they are on top of it.
Mitigation and prevention recommendations
Companies looking to introduce protective measurements should follow these steps:
- Update all windows based systems with the latest security patches, emphasis on MS17-010 which addresses the infection vector. Once patched, the current strain of WannaCry will not be able to infect those systems
- Ensure detection and blocking of known WannaCry domains as well as TOR traffic, create DNS sinkholes if possible,
- Allow WannaCry domains that are known sinkholes that kill the malware execution (by their design)
- Block Tor-2-Web proxy sites from being accessed
- Audit your firewalls for inbound open ports and block the SMB protocol ports (139,445) for inbound traffic
- On endpoint detection, set a basic alert for when multiple “.wnry” or “.wncry” files are being created, and disable network access of that host in case of an alert trigger
- Notify your users and executives so that the threat is not a mystery, let them know how it looks like when they get infected so that they can act, and let your company know that you are actively working towards protection.
And if I have Exabeam Advanced Analytics ?
Customers that have our Advanced Analytics in place already have the logic to detect ransomware. The attack is detected as it unfolds, giving the security operation center time to respond quickly.
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!












