At Exabeam, part of our mission is to help keep security professionals educated and informed on threat detection and incident response topics. In January, we created several resources for you. In case you missed them, here are 19 of our most recent pieces geared towards helping you mature your SOC and enhance your security posture with XDR and Next-gen SIEM. Whether you’re a CISO or a security practitioner, there is something on this list for you.
1. Planning Before the Breach: You Can’t Protect What You Can’t See | eBook
Cybercriminals, nation-states, and malicious insiders are actively targeting organizations for financial gain, to steal secrets and intellectual property, disrupt operations, and harvest personally identifiable information. Keeping pace requires a deeper understanding of the risk in your environment — behavioral context — about every user and asset.
This eBook is a guide for organizations looking to better understand their risk, improve their security detection and response capabilities, and level the playing field against sophisticated adversaries.
2. Exabeam Delivers Next-Gen SIEM and XDR for Google Cloud | eBook
Read our eBook to learn how Exabeam’s security solutions are outsmarting cybercriminals by:
- Tackling the blindspots of legacy SIEM
- Augmenting legacy SIEM with Next-gen SIEM and XDR
- Integrating behavioral analytics to detect insider threats and lateral movement
- Automating threat detection, investigation, and response
3. Ransomware, Phishing, and Malware: 4 Ways to Defend and Respond to External Threats | Guide
External threats refer to techniques commonly employed by adversaries to deceive users, gain access to valid credentials, or exploit corporate assets. Attack vectors like phishing or malware provide adversaries ample opportunities to breach a company’s defenses. Even worse, with the global pandemic and shift to remote work, phishing scams disguised as legitimate communications containing critical information are on the rise.
Even though defense against external threats is improving, their quickly evolving nature and daily occurrence means prevention is never guaranteed. SOC teams must be prepared to respond to an active attack at any time.
Read this guide to see how Exabeam can help defend and respond to these external threats.
4. Insider Threats: Malicious Insiders and Compromised Credentials | Checklist
Defending against insider threats is more than just picking the right security solutions. It’s also defining and creating a security program that pulls people, processes, and technology together to effectively defend against these kinds of threats.
An insider threat is malicious activity against an organization that comes from user credentials with legitimate access to an organization’s network, applications, or databases. These credentials can be current employees, former employees, or third parties like partners, contractors, or temporary workers with access to the organization’s physical or digital assets. They can be privileged or service accounts that have automated download functions or normal activities that have been compromised by an identity-based attack. While the term is most commonly used to describe illicit or malicious activity, it can also refer to any user account which causes harm to the business. This checklist is meant to be a guide when defining an insider threat or insider risk defense program.
5. Top 5 Benefits of Augmenting Your SIEM with Exabeam Fusion XDR | Guide
Managing your organization’s security alerts is a full-time job — whether you monitor only Network Security Devices (NSD), Endpoint, Identity, or (ideally) all of the above. Traditional Security Information and Event Management (SIEM) products may be exactly what is required for log management and the requirements of compliance and governance, but they are seldom optimized for threat detection and incident response — and require extensive tuning to build events of interest.
Enter Exabeam Fusion XDR. When combined with a SIEM solution such as Splunk, QRadar, or a data lake, you add threat analysis, entity (user, endpoint, server, etc.) behavior analysis, risk scoring, correlation, and built-in incident response and case handling. All of this is possible without having to rip and replace your SIEM.
Instead of letting your legacy SIEM leave you vulnerable, Exabeam Fusion XDR allows you to add powerful machine learning and automation to help detect and respond to hard-to-find threats such as ransomware, rogue insiders, or attacks involving compromised credentials and lateral movement. Fusion XDR will help your team quickly become outcomes-focused with use case packages and reporting, and an easy interface for building more specific to your needs.
Amplifying your SIEM with the addition of Exabeam Fusion XDR has many benefits — read this guide to learn the top 5 quick wins.
6. External Threats: Ransomware, Phishing, and Malware | Checklist
External threats such as ransomware, phishing, and malware attacks are a daily occurrence for every organization. While defense against these attacks is improving, their quickly evolving nature means prevention is never guaranteed. SOC teams must be prepared to respond to an active attack at any time.
Defending against external threats is more than just choosing the right security solutions. It’s also creating a security program that puts people, processes, and technology together. Download the checklist and use it as a guide when defending and responding to external attacks.
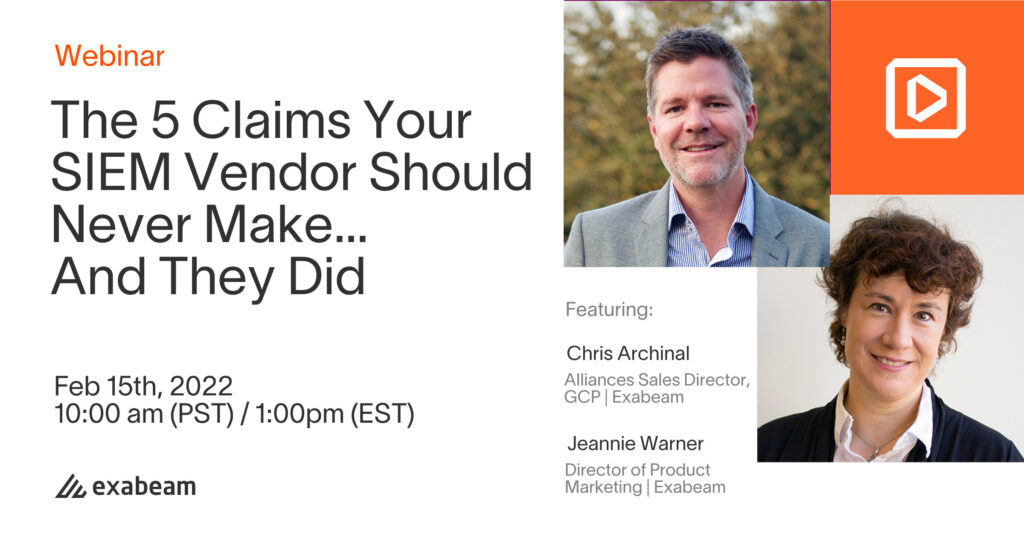
7. The 5 Lies Claims a SIEM Vendor Should Never Make | Guide
A SIEM is a very established technology with a mature set of vendor products but has recently become a victim of scope creep. Over the years, new capabilities, edge requirements, and delivery models have resulted in a product that barely resembles Version 1. The complexity of today’s SIEM is legendary (well-documented, well-understood), a byproduct of this explosion in scope.
While the evolution of the SIEM has resulted in a product that is far more powerful today than at its conception, vendors have overstated, overhyped, and over-promised about its capabilities. Many users have been burned — here are the five claims you need to watch out for.
8. 2022 Predictions from Exabeam Executives | Guide + Video
What does 2022 have in store for cybersecurity? Exabeam’s security experts share what to expect this year in our guide, as well as in this LinkedIn Live video.
9. Rediscover Trust in Cybersecurity: A Women in Cybersecurity Podcast | Podcast
It’s important for employees to be brought into the fold as security’s allies, rather than as its adversaries. For cybersecurity teams that operate with an adversarial mindset appropriate for external threats, it can be challenging to approach internal threats differently. You can’t treat employees the same way you treat nation-state hackers. But employees play a pivotal role in preventing data leaks, making it important to create a company-wide culture of transparency. Transparency feeds trust, which builds a strong foundation for Security Awareness Training to be truly effective.
The CyberWire’s Jennifer Eiben hosts this women in cybersecurity podcast. Kathleen Smith of ClearedJobs.Net moderates the panel. Panelists include Michelle Killian from Sponsor Code 42, Sam Humphries of Exabeam, and Masha Sedova of Elevate Security.
10. Utilizing UEBA for Advanced Insider Threat Detection & Investigation with Exabeam and CrowdStrike | Video
In this hands-on demo you’ll learn how, through the Exabeam and CrowdStrike integration, security teams can detect and investigate advanced insider threats with user and entity behavior analytics (UEBA). See how endpoint telemetry collected from CrowdStrike is streamed, through the Falcon data replicator or FDR, to Exabeam — before Exabeam applies UEBA to help analysts detect, prioritize, and investigate insider threats through behavioral baselining, user attribution, alert prioritization, and timeline creation.
11. Cyber Attack Incident Response: How to Assess the Changing Cyber Crime Landscape | Video
We find ourselves in the post-data breach mindset, where cybersecurity practitioners and vendors alike understand and accept that there is almost a certainty of suffering from any number of cyber attacks. Are we approaching a watershed moment where we’re going to have to start thinking: “Instead of just being prepared for falling victim to almost certain cyber crime, should we be preparing ourselves for a changing threat landscape too?” SentinelOne’s Scott Schefermann answers this, and other infosec questions about where we find ourselves in a post-breach information technology world, from a cybersecurity incident response perspective.
12. Monitoring, Automated Orchestration and Automation with Okta, Netskope, and Exabeam | Video
This video covers the Exabeam/Netskope bi-directional integration. Including ingest support for Data Lake and Advanced Analytics, SOAR support from Incident Responder, and alert and event data flows from Netskope into the Exabeam platform through various transport mechanisms. We also look at how Exabeam stitches the Netskope data into smart timelines for a holistic overview of events.
13. Exabeam and Netskope | Video
Cloud access security broker solutions are essential for detecting risks to an organization’s cloud platform, such as compromised credentials and insider threats. By integrating Netskope with Exabeam, security teams can:
- Monitor cloud-access events to identify unusual activity.
- Analyze data from cloud-based services in conjunction with other security and infrastructure solutions to detect anomalous activity.
- Eliminate manual gathering and assembly of data from multiple, disparate systems.
- Improve productivity by dramatically reducing the time analysts spend investigating incidents.
- Leverage Exabeam Smart Timelines to automate the assembly of incident timelines.
14. Protecting Your Blindspots Against Insider Threats and Other Attacks, Featuring Forrester | On-demand Webinar
Over the past two years, the business world has experienced a major shift to a more open work-from-anywhere model. Corresponding with this shift are the trends of cloud adoption and a new cybersecurity attitude — the “we’ve been breached” mindset.
These changes pose SOC teams a new set of challenges, particularly around insider threats, legitimate users, or compromised users going undetected. Insider threats represent a huge Achilles heel for most organizations because most traditional tools can’t detect abnormal behavior when being perpetrated using valid credentials. The impact: lost IP representing billions in risk, brand reputation resulting in lost customers or soiled reputation, and even weakened National Security. So how can organizations protect themselves from the blindspots posed by these threats, perpetrated by attackers they can’t see?
In this on-demand webinar with guest speaker Joseph Blankenship, VP Research Director, Forrester, we’ll explore the challenges many organizations face with complex threats such as Insider Threats, what companies of all sizes can do to identify the blindspots, and how a SOC platform like Exabeam Fusion SIEM and XDR can help you protect what other tools can’t see.
15. See How Exabeam Protects Your Business From Insider Threats | On-demand Webinar
While protecting your organization from external threats is critical, external threats may not pose the biggest risk to your business. The trusted employee or contractor that breaks bad can cause untold damage to your business, all while operating in plain sight. Your security stack often is oblivious to these actions, giving you a false sense of security while in reality the company jewels are pilfered.
To combat these insider threats, you must baseline, monitor, and analyze behavior of users and assets around the clock, and react fast when something suspicious is identified.
Exabeam helps organizations around the world gain new insights into the inner workings of their environments, while simultaneously rooting out threats hiding in the open.
In this demo, you will learn:
- How easy it is to maintain continuous risk visibility with Exabeam
- The breadth of security, business, and IT products supported by Exabeam
- Learn a different approach to threat investigations
- How automation built into Exabeam makes all the difference
16. Mapping AI to Your Security Posture and Avoiding Overlooked Threats | On-demand Webinar
In this episode of the award winning teissTalk, Jenny and her guests consider:
- How can InfoSec teams test and recognize AI bias?
- What can you do to prevent biased AI models from missing unknown threats?
- How can you avoid creating biased algorithms?
17. How Do You Know if Your SOC is Relevant? | On-demand Webinar
In this episode of the award winning teissTalk, Geoff and his guests consider:
- What are the capabilities and attributes that are universally known as good, and what change do you measure?
- Accelerating investigation and response times in your SOC maturity journey
- Recruitment and retention of high-demand and high-quality SOC analysts in a post-pandemic world
18. A CISO’s Guide to Communicating Risk | Whitepaper
It takes 212 days before a breach is detected. So you have to wonder: How long have we been compromised? What will it take to recover? And above all, how badly will it damage our reputation?
It’s part of a CISO’s job to be aware of the risks and costs associated with a data breach — but what about the rest of the senior leadership team? In some cases, it’s difficult for executives to comprehend both the short-term and long-term ramifications. Given CISOs’ expertise, they have an opportunity to step in to educate key stakeholders and protect the business. It’s important to ensure that the entire C-suite realizes what they could lose in a serious security event.
19. Exabeam/KPMG Joint Special Session After Report | Blog Post
Exabeam and KPMG co-hosted a special online session titled “Manufacturing Industry CISO Roundtable – From ‘Prevention’ to ‘Discovery,’ the Future and Present of Security Monitoring” on October 20, 2021. The session covered trends in security incidents alongside the approaches and concerns of participating companies regarding security monitoring, and an active discussion took place on the future outlook in the field.
In this report, we introduce the presentations and discussions that took place during the seminar.
Watch the Webinar
For more insights, register for our Feb. 15 webinar, “The 5 Claims Your SIEM Vendor Should Never Make…And They Did.” We’ll tell you which questions everyone should be asking their security teams, potential vendors, and management.
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!