At Exabeam, part of our mission is to help keep security professionals educated and informed on threat detection and incident response topics. In June, we created several resources for you. In case you missed them, here are 17 of our most recent pieces geared toward helping you mature your SOC and enhance your security posture with XDR and next-gen SIEM. Whether you’re a CISO or a security practitioner, there is something on this list for you.
1. Forrester Consulting ROI Calculator | Interactive Model
Do you ever wonder if your Security Information and Event Management (SIEM) solution delivers an ROI? This interactive model is based upon the Forrester Consulting study, The Total Economic Impact of Exabeam Fusion SIEM, commissioned by Exabeam. Try it and calculate the value you can achieve.
2. Improving Threat Detection, Investigation and Response: How SA Power Networks Teamed With Exabeam for Faster, Analytics-driven Cybersecurity Results | Case Study
SA Power Networks is the sole electricity distributor for the state of South Australia, supplying electricity to about 1.7 million South Australians. A year after implementing Exabeam’s Threat Detection and Incident Response (TDIR) analytics software solution, this partnership has streamlined and accelerated SA Power Network’s TDIR function, strengthening security team bonds and collaboration, and cementing the critical link between security and business initiatives.
3. Exabeam Advanced Analytics | Data Sheet
Today’s credential-based threats are complex, often touching many systems, using multiple logins, and spanning a period of several months. These insider threats involve the legitimate credentials and access privileges of real users, making them challenging for legacy security solutions to detect. In order to tackle these insidious threats, organizations need a solution built from the ground up using modern technologies such as machine learning, behavioral analysis, and data science. Learn how Exabeam Advanced Analytics can help.
4. Top Four Cyberthreats Challenging The Banking Industry and How to Address Them | Guide
The banking industry has become a prime target for external threats such as credentials, phishing, and ransomware attacks. With the average data breach costing organizations more than $4 million, this is an issue for which banks can’t afford to be unprepared. In this guide, we will explore some of the most prevalent external cyberthreats facing banks and how you can tackle them head-on.
5. The New CISO Podcast: Management Tools | Blog
In this episode of The New CISO podcast, Jeremy Sneeden, Director of Security Operations and Engineering at Allina Health, discusses the importance of management training to learn how to lead others, how to ask for what you need, how to advocate for your team, how to quantify risks, and advice for the CISO-in-training.
6. The New CISO Podcast: Don’t Be Afraid to Break Things | Podcast
In this episode of The New CISO podcast, David Lingenfelter, VP Information Security at Penn National Gaming, discusses the importance of constantly learning and evolving in the IT security field. After a nearly 30-year-long career in IT with a focus on computer security, he shares his experiences growing and advancing through his work in the industry. Listen to the episode to hear about David’s journey, his advice for beginners in the field, and his thoughts on IT management.
7. The New CISO Podcast: Building The Right Relationships | Podcast
In this episode of The New CISO podcast, Den Jones, Chief Security Officer at Banyan Security, discusses the importance of trustworthy and transparent relationships in the cybersecurity field. He shares how to deal with misleading salespeople and create effective data security strategies. Listen to the episode to hear about Den’s journey, the problems with vendors, and his thoughts on building relationships.
8. The Importance of Automated Cyberthreat Response | Video
In this video interview with Information Security Media Group at RSA Conference 2022, Exabeam CEO, Mike DeCesare, discusses evolving XDR trends. It’s critical to enable companies to not only see what is going on in their IT environments, but to also quickly react; and “sheer manpower” is no longer sufficient to respond to the evolving surge of cyberthreats. “Companies are going to have to allow their cybersecurity products — and especially the easier things to block — to just block those [threats] automatically,” he says.
9. 21 Top Cybersecurity Threats and How Threat Intelligence Can Help | Blog
Cybersecurity threats continue to grow and evolve in frequency, vector, and complexity. Get a quick, up-to-date review of 21 cybersecurity threats and how to gain the information you need to prevent data breaches and bolster your information security.
10. Are You Thinking About Shifting Your SIEM to the Cloud? | Blog
Cloud-delivered SIEM solutions are becoming increasingly popular, and more businesses are looking to move their SIEMs to the cloud to save costs and cut down on operational overhead. While you may have many questions, the big ones should be: How am I using my SIEM now? How can I take advantage of all the benefits of cloud-delivered technologies to achieve even more?
11. The Next Wave of Innovation in SIEM, Security Analytics, and TDIR | Blog
When speaking to customers and prospects about their cybersecurity challenges and the struggles they face using the incumbent set of technologies, it’s a consistent chorus of two main concerns:
- Their SIEM isn’t designed for big data workloads. It can barely keep up with alerts, but they also want to collect all manners of logs and additional context because, without that, they are back to having limited visibility.
- Tools they use for threat detection, investigation, and response (TDIR) are uninspiring; they lack intuition and an understanding of the role of the analyst who spends a significant amount of time using them.
It’s loud and clear: something has to change. Read the article to learn more about Exabeam’s next-generation cybersecurity platform, featuring: cloud-scale data collection and transformation, storage without limits, and powerful visualizations.
12. The Benefits of UEBA Technology with Industry Experts at the Helm | Blog
Best-in-class security technology complements great expertise, and vice versa. To significantly improve your security posture, you need both. User and Entity Behavior Analytics (UEBA) technology is a game-changing development for the cybersecurity industry. These tools allow security policies to evolve beyond the application of static rulesets and detect a far wider range of suspicious activities in the enterprise. Read the article to learn more about behavioral insights enhanced with machine learning and the value of detection and response expertise.
13. Ransomware: Bigger, Better, and Still Going Strong | Blog
It is evident that ransomware attacks are still apparent and on the rise. In 2021, ransomware attacks increased by 13 percent year over year — more than the past five years combined. Organizations are understandably concerned about their ability to not only prevent attacks but to recover should they be targeted. Addressing the problem in its entirety is a common defensive oversight — especially, for example, at the point where ransomware performs reconnaissance on systems before initiating. Empowering oneself with the correct knowledge can help one to begin to understand the likelihood of an emerging threat, and thus allow an organization to take necessary precautionary measures. Read the article to learn about the ransomware landscape, the human element of ransomware, and addressing the emerging ransomware threat.
14. Exabeam in Action: Stopping Lapsus$ in Their Tracks | Blog
What makes Lapsus$ attacks so difficult to detect is that the intrusion appears to be coming from authorized users. When credentials are stolen or purchased, and used to move laterally within an organization, nearly all security teams are unable to detect abnormal behavior associated with legitimate credentials. This is the story of an Exabeam customer that used Fusion SIEM to identify, investigate, and remove the evasive Lapsus$ criminal hacking group from their environment.
15. One Week of Gartner Security & Risk Summit 2022 in 10 Minutes | Blog
Unlike RSA, which seems to have been dominated by cybersecurity vendors’ marketing and product demos, the Gartner Summit was an opportunity for Gartner analysts to share their insights gathered across thousands of customer and vendor interactions, and countless surveys and interviews. There was also an expo floor with many security vendors. This article will cover all the buzzwords-du-jour, such as secure access service edge (SASE), extended detection and response (XDR), zero trust, cybersecurity mesh architecture (CMA), identity threat detection and response (ITDR), and more.
16. What Forrester Consulting is Saying About the ROI From Exabeam SIEM | Webinar
It’s not often you see the four-letter term, SIEM, in the same sentence with the three-letter term, ROI. Well, now you can. Learn how a group of Exabeam Fusion SIEM customers achieved a composite ROI of 245% over three years, with a payback period of less than six months. That’s what the Exabeam Fusion Total Economic Impact(™) (TEI) study by Forrester Consulting revealed. In this webinar, we examine the measurable benefits of Exabeam Fusion SIEM and share how you too can transform your security operations using the Exabeam Fusion Platform.
17. Using a Layered Approach to Improve Ransomware Detection and Response | White Paper
Ransomware cost the world $20 billion in 2021, and it’s here to stay. Entry can come at any time through multiple attack vectors, so what can security leaders do to prevent ransomware’s destructive effects? The Exabeam Security Research Team reviewed the characteristics of four recent ransomware attacks.
Hear what Forrester Consulting is Saying about the ROI from Exabeam SIEM
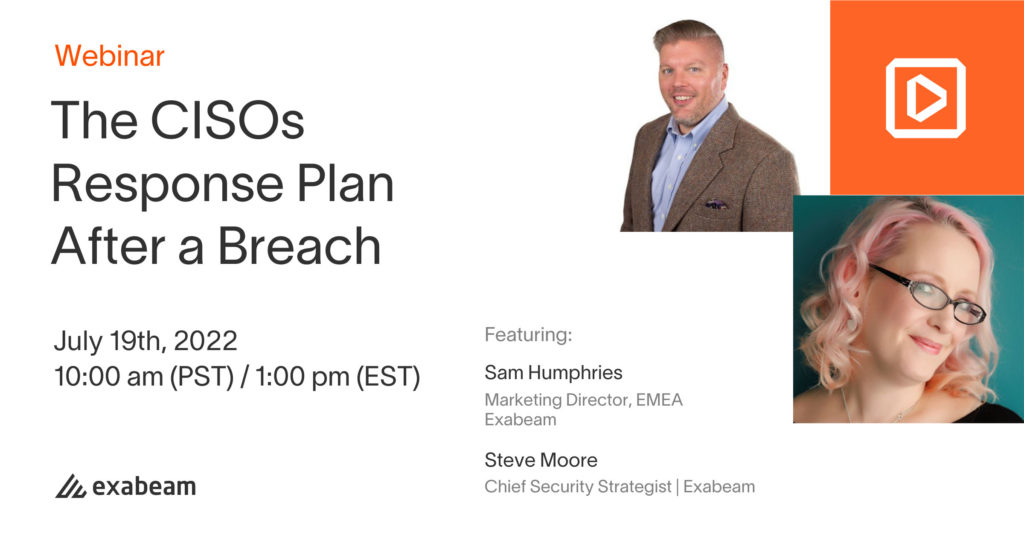
For more insights, register for our webinar, The CISOs Response Plan After a Breach.
You’ll learn about:
- Planning and playing well with others
- SITREPs – what, when, and who needs to know
- When to communicate with and without emotion
- Consistency when communicating (internal and external)
- Containment and remediation — one big event or a journey?
- How to foster a culture of learning, not blame
- Dealing with the aftermath of audits and future scrutiny
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!












