Insider threats refer to malicious or unintentional actions taken by employees, contractors, or other insiders within an organization that can compromise sensitive data or disrupt operations. These threats can come in many forms, such as stealing confidential information, causing damage to systems or networks, or introducing malware or other malicious code.
One of the main challenges of detecting, investigating, and responding to insider threats is that these individuals often have legitimate access to sensitive information and systems, making it difficult to distinguish their behavior from normal activities.
This blog post highlights 10 of our latest resources for helping you detect and respond to insider threats.
1. 4 Requirements for Building a Successful Insider Threat Team | Blog
Sometimes, having a security operations center (SOC) isn’t enough to address insider threats. Security operations teams are managing massive amounts of data across billions of events from on-premises and the cloud, but detecting insider threats has special requirements that encompass both searching historical data and seeing evolving credential behavior changes as they happen.
2. How to Build an Insider Threat Program with Exabeam | Webinar
In this webinar, you will learn four common scenarios where you need an insider threat team, how to build a mission statement and tools, four attributes of a successful insider threat program, how behavioral analytics baseline “normal” behavior of users and devices — showing risk faster, and about automated investigation experience that automates manual routines and guides new insider threat teams.
3. Organizational Downsizing and Insider Threats: Detecting the Undetectable to Reduce Risk | Blog
Early in 2022, many organizations went on a hiring spree and now the recent economic downturn has led to an uptick in companies downsizing. Past history has shown that downsizing increases the organizational risk companies face from impacted employees and the data and IP they have access to. CISOs need to educate their organizations on the risk of insider threats all the way to the board level to get buy-in for the programs and necessary budget to address these threats. Learn the challenges of detecting insider threats, how Exabeam helps triage, detect, investigate, and resolve insider threats, and data leak activity to watch for.
4. Holidays and Insider Threats — Exabeam Answers Questions From the Field | Blog
There are many questions at security field events that boiled down to the same themes: Management is doing layoffs — what should we (security) look out for? We did some hiring, and the new people failed our phishing tests. How do we communicate the risks upward? We have a change freeze coming up. Anything you recommend that we do? We have an executive budget to create an insider threat team. Where do we start? In this article, hear some of the best responses to each of these questions.
5. A CISO’s Guide to Adversary Alignment | White Paper
“Are we secure?” Executives and board members always want the answer to be “yes,” but CISOs know it’s irresponsible to make such a blanket statement. An adversary could be any potential threat — whether external or internal, intentional or unintentional. So, the question CISOs should be answering is: “Are we adversary-aligned?” Download this white paper to learn how your people, processes, and tools can be adversary-aligned, and the benefits of doing so.
6. The What and How of Evaluating UEBA Under the Hood | Blog
Why do we bother with UEBA in the first place? 93% of breaches are due to compromised credentials. For such insider threats, there is no other alternative to UEBA. While threat prevention technologies are a necessary component of enterprise security, companies are recognizing that UEBA detection tools are an integral part of security defense. Read the blog to learn about the three dimensions to consider when evaluating UEBA solutions.
7. Are Systems Integrators Pricey? Not If You Consider How They Reduce Costs Long Term | Blog
As a security executive, you are inundated with a daily onslaught of risks and threats to your organization amidst layoffs, organizational budget cuts, geopolitical challenges, and a general shortage of cybersecurity resources. The best technology is critical for addressing these challenges, but perhaps just as importantly, organizations should leverage trusted advisors to help prepare for when something happens, and to avoid hidden costs to the organization in the future. Learn who these trusted advisors are, why this is important for an insider threat program, what we typically consider for the price tag, and what we should consider for the price tag.
8. How Does Exabeam Improve Your Security Environment? | Blog
Information security practitioners know that the real operational risks of insider threats are a result of unpreparedness. There are known unknowns that we do our best to protect against, but there are also unknown unknowns that, when they surface, often result in 2:30 am calls from our CISOs or information security leadership. These alarms create stress and lead to burnout among security analysts and managers. Ideally, awareness and preparation can mitigate many of these risks, but situations on the ground in a security operations center (SOC) are not always ideal. Learn some of the lesser-known benefits of user and entity behavior analytics (UEBA) to defend against insider threats, along with chronologically correlated security vendor events in a timeline.
9. Powerful Behavioral Analytics | Solution Brief
Security operations teams fail due to the limitations of legacy security information and event management (SIEM). Legacy tools don’t provide a complete picture of a threat — they bury analysts with alerts. This demands a shift in investment from legacy on-premises, rule-based detection to cloud-native SIEM platforms designed to identify abnormal behavior. This solution brief will help you understand how Exabeam behavioral analytics can help your organization defend against insider threats.
10. Automated Investigation Experience | Solution Brief
Legacy security tools don’t provide a full picture of a threat and compel slow, ineffective, and manual investigations and fragmented response efforts. Meanwhile, attacks are becoming increasingly sophisticated and hard to detect, and credential-based attacks are multiplying. This solution brief will show you how Exabeam automated investigation experience can help your organization stave off insider threats.
Want to learn more about detecting and preventing insider threats?
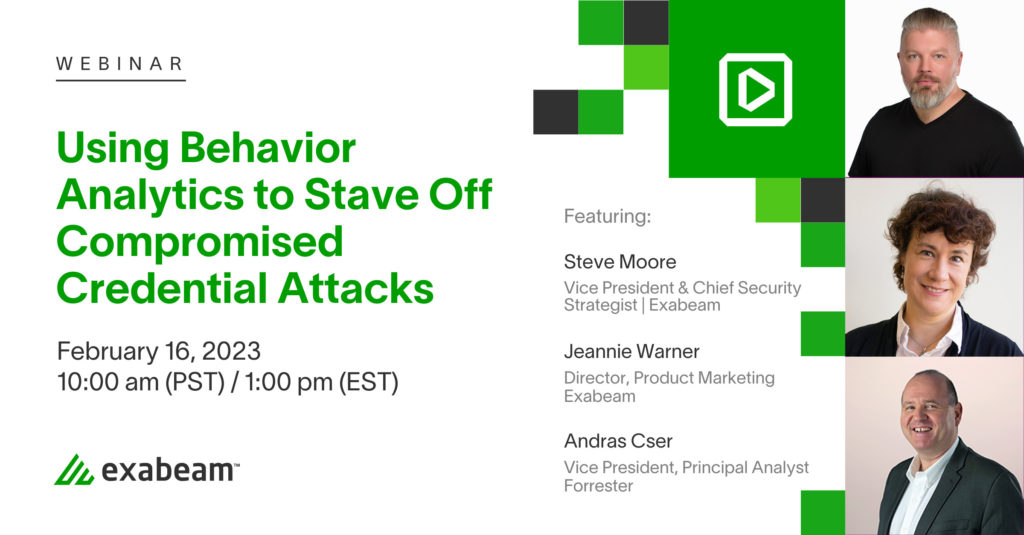
Register for our webinar, Using Behavior Analytics to Stave Off Compromised Credential Attacks.
Millions are spent on security operations centers on tools, processes, and people. Yet, we still have million-dollar problems, often due to an efficacy gap or a lack of adversary alignment.
Compromised credentials are involved in more than 90 percent of breaches (Verizon 2022 DBIR). How can security operations address this? This webinar will address the challenges associated with compromised credentials and discuss some of the steps organizations can take to improve their detection and response.
Come listen to our panel of experts discuss such topics as:
- Why are we seeing so many credential-based attacks and why do we seem to be failing at detection and response?
- How are the IAM and SIEM markets evolving to take these into consideration?
- How can IAM and security operations address these challenges?
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!












