We recently launched Turnkey Playbooks, a new feature for Exabeam Incident Responder as part of i53 to help security teams get faster time to value from their SOAR product. We’re excited to share how this will help customers as part of their journey to adopt automation.
The “magic” of SOAR
Since we launched our security orchestration automation and response (SOAR) product, Incident Responder, we’ve seen the market evolve. As our reps and engineers listened to customers seeking to adopt SOAR solutions — both ours and those of other vendors — they came upon an interesting problem: while many customers had key initiatives to adopt automation and address staffing shortages, many were unsure where to begin. Many heard practically spiritual language about SOAR products that could change their lives with advanced features, hundreds of integrations and complex workflows. Our engineers even joked some thought SOAR software could be programmed to do everything from quarantining an endpoint to “automagically” making your morning coffee.
SOAR promises fall short
However, any security engineer who has experience with implementing a SOAR solution has run into complexity. According to Gartner, SOAR solutions are not “plug-and-play.” Even though solutions have a library of out-of-the-box use cases and integrations, buyers are reporting multiweek professional services engagements are commonly needed to implement their initial use cases, as every organization’s processes and technologies deployed are different.
Through additional research, we came to learn that many customers, regardless of the SOAR vendor they picked, were taking several months to stand up their solutions. Projects stalled as security teams needed to purchase additional licenses to third-party security tools or obtain API keys from other teams (which can take a surprisingly long time in some organizations). The promise of automation started to sour.
Hearing this issue with SOAR adoption, we put on our analyst hats and got to work on a solution.
Phishing for clues
First, recall the problem that many security teams are not quite sure where to start in their automation journey. After talking to a number of our sales engineers as well as companies part of our customer advisory board, we identified phishing investigations as a key activity consuming analysts’ time. Drilling down a bit further to understand the process, we found:
- Security teams face hundreds of phishing emails in a day or week
- Teams often dedicate a junior analyst to manually sift through emails for potentially malicious links or file attachments
- The analyst spends hours — sometimes even all day — copying and pasting links and attachments into threat intelligence services
- Based on the results, the analyst will escalate the incident for further investigation
Even when this process is well defined and used on a daily basis, each email might take the analyst anywhere from 10-20 minutes. Multiply that by the hundreds to potentially thousands of phishing emails received daily in an organization, and the time spent quickly adds up to exceed the number of hours in a day. This means queues from phishing emails grow ever larger as phishing attacks continue to pour in. Ultimately, this puts their organizations at risk.
Turnkey playbooks accelerate automation
While many organizations have attempted to automate this process, many have stalled due to the challenges of acquiring additional third-party licenses and configuration. Exabeam is proud to now offer its customers Turnkey Playbooks to help customers accelerate their automation journey. Turnkey playbooks work out of the box without requiring any configuration or investment in additional third-party products. As a result, security teams can begin to get value from our SOAR solution, Exabeam Incident Responder, on day 1.
The first offering, the Turnkey Playbook for Threat Intelligence, automatically identifies malicious domains, IP addresses, URLs, files, and email addresses with no additional configuration or licenses required. This not only saves analysts time in their day to day in automating portions of their phishing response workflows, but also, the cycles spent configuring and deploying their SOAR tool and other third-party security tools. Analysts will also be able to modify the playbook via its components to customize new workflows specific to their SOC.
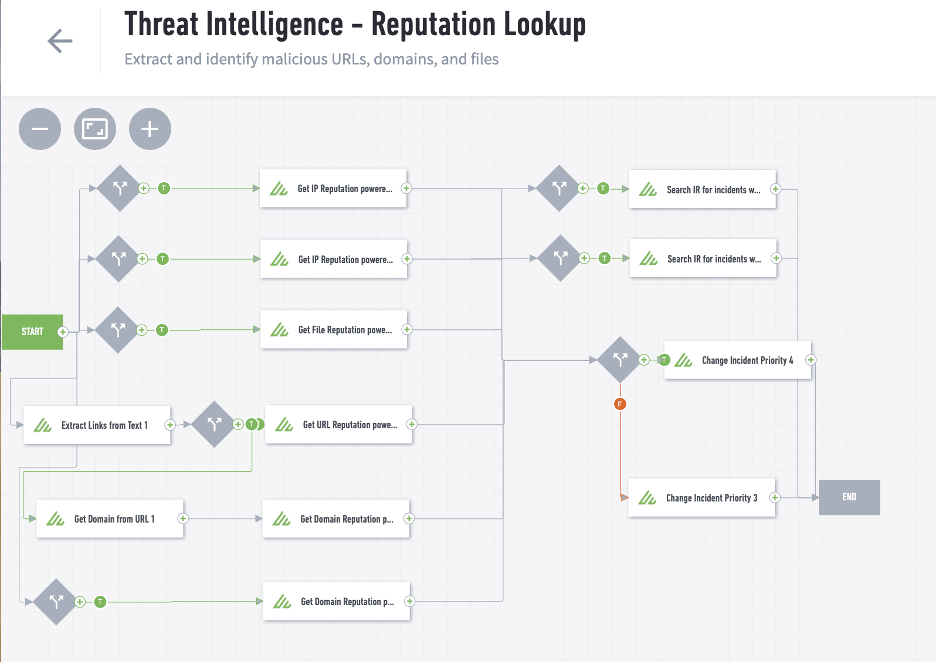
Figure 1: The Exabeam Turnkey Playbook for Threat Intelligence automatically extracts files and links from an email, then obtains the IP, domain, URL, file, and email sender reputation from a threat intelligence service. Using conditional logic, the playbook automatically escalates the incident if it finds anything suspicious.
“Turnkey Playbooks offer unique, easy to adopt SOAR workflows in digestible pieces. SOAR vendors can overwhelm their customers, and here we’re able to offer automation the way it should be: simple.” — Shahar Ben Hador, VP of Product Management and former CISO, Exabeam
To learn more about Incident Responder, feel free to schedule a demo or download our data sheet.
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!













