The Exabeam 2018 Cybersecurity Professionals Salary and Job Report has great news for new college graduates—working in cybersecurity can lead to a career that you really enjoy, with a high salary and job security.
Imagine a job search where there is a huge number of openings. Studies by Cisco, ISACA and Symantec are predicting a cybersecurity labor shortage numbering in the millions. And with millennials wanting “purpose over paycheck,” working as a security analyst who is protecting the good guys, while hunting hackers and finding the bad guys, could be the ideal career for many new graduates.
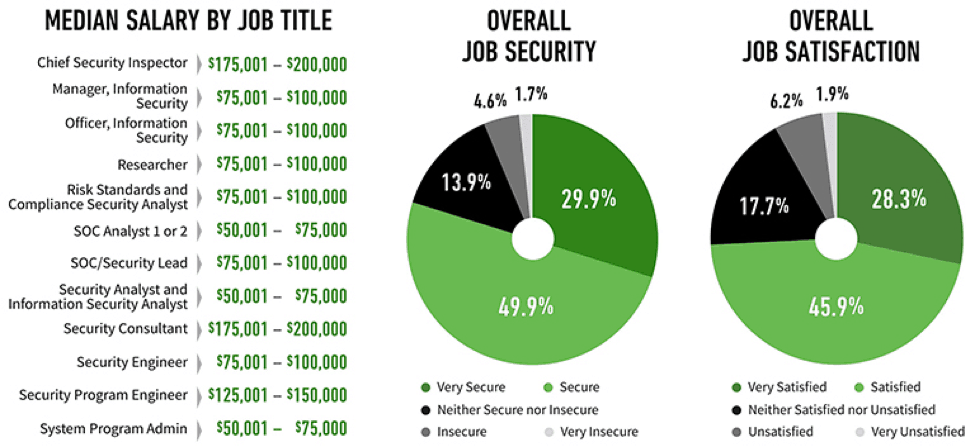
Figure 1- Salaries of cybersecurity pros can surpass $200K, and there’s high job security and satisfaction rates.
So, how do you work in cybersecurity when most colleges and universities don’t offer a major in cybersecurity?
According to Alan Paller, director of research at the SANS Institute (a trusted security training organization), the following three-step process is the best way for grads to get started with their career in cybersecurity.
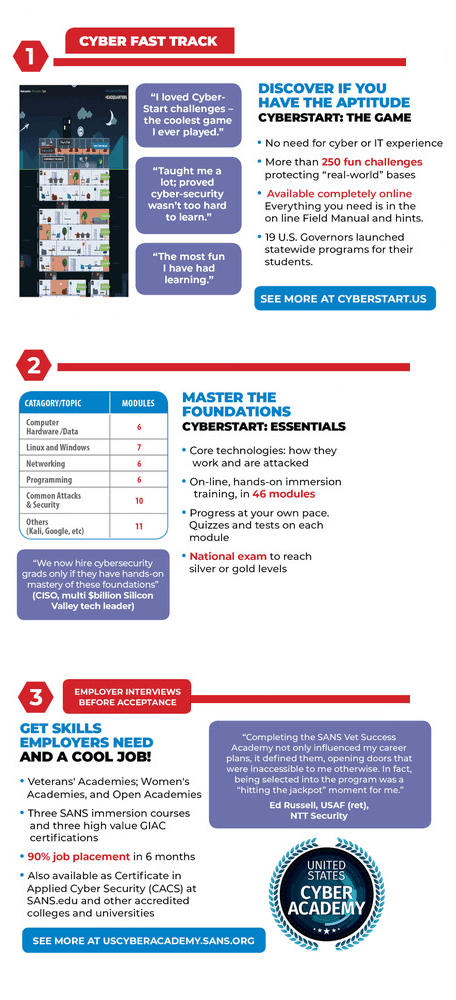
Figure 2 – Three-step process for getting a job in cybersecurity according to the SANS Institute.
Professor Alan Woodward from the University of Surrey explains that careers in cybersecurity can take many forms. “Cybersecurity is inherently a multi-disciplinary field. You will find that the most successful tend to have a particular approach rather than a specific set of technical skills. Most think laterally, out of the box and almost back to front. Although I’m an engineer, I find I enjoy taking things apart to find out how they work rather than necessarily building them—many professionals I come across in cybersecurity have these traits.”
Professor Woodward suggests getting an advanced degree in cybersecurity as well. “You can bolster your information security skills by getting a master’s degree or MSc. For those looking to study in Europe, it’s worth researching programs such as the Surrey Centre for Cybersecurity, which is approved by the GCHQ as an Academic Center of Excellence.”
Figure 3 – Surrey Centre for Cybersecurity has an esteemed cybersecurity program.
Advice for Increasing the Number of Women Working in Cybersecurity
One less than stellar data point from the Exabeam survey is the small percentage of women who work in cybersecurity—at only 10 percent female. That’s even less than the low number of women who work in technology, which is hovering around 26 percent, according to various studies. Unfortunately, the growing number of women with a STEM education are not ending up with careers in Security Operations Centers (SOC).
Turning to several prominent women in cybersecurity who are connected to an organization called Women in CyberSecurity, we found some excellent advice:
Tania Ghods, a security intelligence and operations consultant at IBM Security Services, recommends just jumping in:
“My advice for women is to not be afraid to take the leap. It’s important to remember that you do not need to qualify for every single bullet item in a job description. If you have the majority of the skills, apply. And if you don’t end up getting the position, at least you had practice interviews.”
Ruth Agosto, who works in security and compliance at KPMG, and spent two years working in a SOC, suggests obtaining an inexpensive cybersecurity certification:
“Become certified. One of the most accepted certifications is Security + by CompTIA. The exam is not too expensive. This exam will cover the necessities needed for understanding the concepts used within SOC environments.”
New graduate Kristina Greenshields, who is currently in negotiations to become a cybersecurity administrator (fingers crossed), suggested networking and using online forums to get the interview:
“I find that the more you talk to people—no matter who they are or where they work—you will always find someone who knows someone that is on a SOC team and knows of openings. The key is to ask questions and not be afraid to ask for a referral. Networking will always pay off. You’re not asking for a handout—you still have to prove yourself and you still have to do the work. I attend online job fairs and then follow those I speak with on LinkedIn.”
Lora Vaughn McIntosh, a VP who manages a SOC for Regions Bank had this to say about the importance of workplace culture:
“Organizational culture is important to recruiting and retaining women, but it’s also important for career satisfaction and advancement. Finding a company with an open and supportive culture can ease many of the barriers to success.”
ISSA is a Great Resource for Developing a Career in Cybersecurity
The Information Systems Security Association (ISSA) is s a nonprofit, international organization of information security professionals and practitioners. They provide educational forums, publications, and peer interaction opportunities that will enhance your knowledge, skills and professional growth. There are chapters all over the world with regular meetings.
If you have any questions or advice, reach out to ISSA.
The world certainly needs skilled and passionate cybersecurity professionals, and there’s the educational resources and workforce out there ready to help you get started.
Similar Posts
Recent Posts
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so you can stay ahead of the cybercriminals and defend your organization.
See a world-class SIEM solution in action
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!












