- Why Exabeam
Customers

r-tec DE
r-tec entscheidet sich für die Exabeam Security Operations Platform zur Unterstützung seiner SOC-, MDR- und Vorfallsreaktions-Services
Read More- Products
Featured Data Sheet

Exabeam Fusion
AI-driven Exabeam Fusion: Bring an end to your SIEM nightmares. It’s time for faster, easier, and more accurate threat detection, investigation, and response (TDIR). Exabeam Fusion applies AI and automation to security operations workflows for a holistic approach to combating cyberthreats, delivering the most effective TDIR. AI-driven detections pinpoint high-risk threats by learning normal behavior... Read more »
Read More- Solutions
Featured Solution Brief

Exabeam Fusion on Google Cloud
As cyberattacks become increasingly frequent, sophisticated, and hard to detect, security operationsteams are struggling with the limitations of legacy security information and event management (SIEM) and traditional perimeter security. Traditional platforms haven’t kept pace with the growth of data, the sophistication of attacks, or the shift to the cloud. Nor can it handle the increasing... Read more »
Read More- Resources
Featured Resource

- Customers
- Partners
Get a DemoCustomers

r-tec DE
r-tec entscheidet sich für die Exabeam Security Operations Platform zur Unterstützung seiner SOC-, MDR- und Vorfallsreaktions-Services
Read More- Company
- Why Exabeam
Customers

r-tec DE
r-tec entscheidet sich für die Exabeam Security Operations Platform zur Unterstützung seiner SOC-, MDR- und Vorfallsreaktions-Services
Read More- Products
Featured Data Sheet

Exabeam Fusion
AI-driven Exabeam Fusion: Bring an end to your SIEM nightmares. It’s time for faster, easier, and more accurate threat detection, investigation, and response (TDIR). Exabeam Fusion applies AI and automation to security operations workflows for a holistic approach to combating cyberthreats, delivering the most effective TDIR. AI-driven detections pinpoint high-risk threats by learning normal behavior... Read more »
Read More- Solutions
Featured Solution Brief

Exabeam Fusion on Google Cloud
As cyberattacks become increasingly frequent, sophisticated, and hard to detect, security operationsteams are struggling with the limitations of legacy security information and event management (SIEM) and traditional perimeter security. Traditional platforms haven’t kept pace with the growth of data, the sophistication of attacks, or the shift to the cloud. Nor can it handle the increasing... Read more »
Read More- Resources
Featured Resource

- Customers
- Partners
Blog Derek Lin
Information Security Blog
Stay ahead with Exabeam’s news, insights, innovations, and best practices covering information security and cyber threat detection and response for the security professional.
Stay Informed
Subscribe today and we'll send our latest blog posts right to your inbox, so can stay ahead of the cybercriminals and defend your organization.


 Load More
Load MoreSee a world-class SIEM solution in action
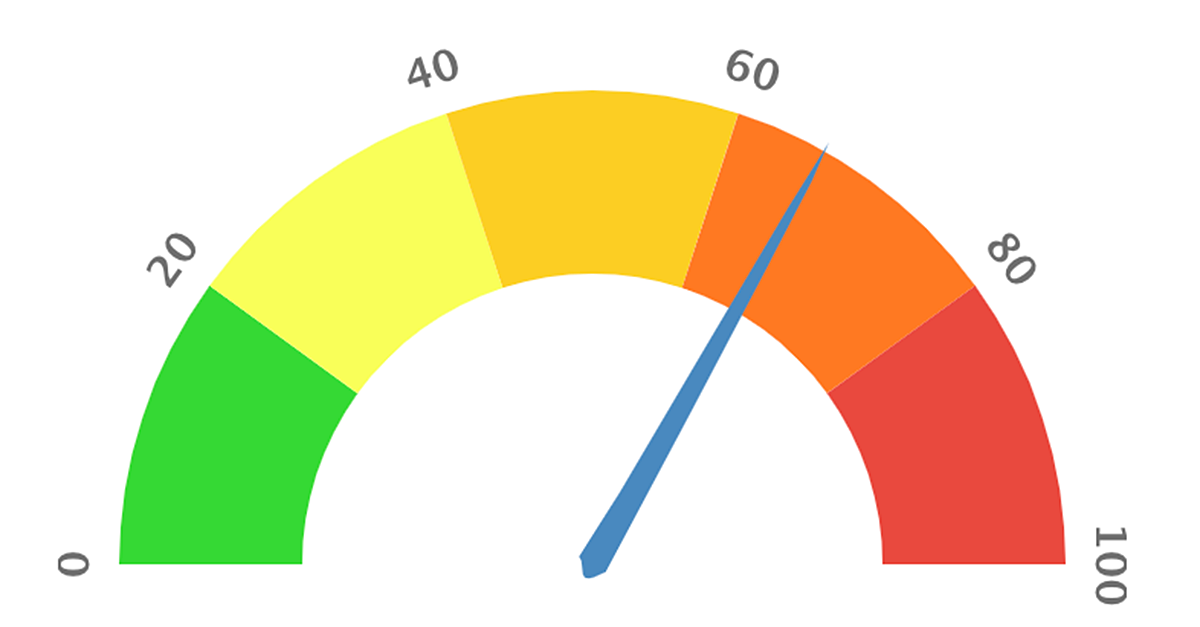
Most reported breaches involved lost or stolen credentials. How can you keep pace?
Exabeam delivers SOC teams industry-leading analytics, patented anomaly detection, and Smart Timelines to help teams pinpoint the actions that lead to exploits.
Whether you need a SIEM replacement, a legacy SIEM modernization with XDR, Exabeam offers advanced, modular, and cloud-delivered TDIR.
Get a demo today!
We use cookies on our website to give you the most relevant experience by remembering your preferences and repeat visits. By clicking “Accept”, you consent to the use of ALL the cookies.Manage consentPrivacy Overview
This website uses cookies to improve your experience while you navigate through the website. Out of these, the cookies that are categorized as necessary are stored on your browser as they are essential for the working of basic functionalities of the website. We also use third-party cookies that help us analyze and understand how you use this website. These cookies will be stored in your browser only with your consent. You also have the option to opt-out of these cookies. But opting out of some of these cookies may affect your browsing experience.Necessary cookies are absolutely essential for the website to function properly. These cookies ensure basic functionalities and security features of the website, anonymously.Cookie Duration Description cookielawinfo-checbox-analytics 11 months This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". cookielawinfo-checbox-functional 11 months The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". cookielawinfo-checbox-others 11 months This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. cookielawinfo-checkbox-necessary 11 months This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". cookielawinfo-checkbox-performance 11 months This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". viewed_cookie_policy 11 months The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. Functional cookies help to perform certain functionalities like sharing the content of the website on social media platforms, collect feedbacks, and other third-party features.Performance cookies are used to understand and analyze the key performance indexes of the website which helps in delivering a better user experience for the visitors.Analytical cookies are used to understand how visitors interact with the website. These cookies help provide information on metrics the number of visitors, bounce rate, traffic source, etc.Advertisement cookies are used to provide visitors with relevant ads and marketing campaigns. These cookies track visitors across websites and collect information to provide customized ads.Other uncategorized cookies are those that are being analyzed and have not been classified into a category as yet. - Products
- Products